forked from such-gitea/wownero
Compare commits
67 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
94390f8364 | ||
|
|
5249d14063 | ||
|
|
9713b3f058 | ||
|
|
6f2d52de9e | ||
|
|
949158eb00 | ||
|
|
c749be7f9d | ||
|
|
036cdfadad | ||
|
|
8670b67c9c | ||
|
|
98f2524ecc | ||
|
|
a0b181f4cd | ||
|
|
2ae11e8e4b | ||
|
|
ae9de01824 | ||
|
|
5227b3280c | ||
|
|
ed34ba0774 | ||
|
|
33634f6dfd | ||
|
|
62d746ffeb | ||
|
|
da0c68074e | ||
|
|
8b392ed111 | ||
|
|
7683daa61f | ||
|
|
105fc24be0 | ||
|
|
58aa5ac491 | ||
|
|
c3f0e58191 | ||
|
|
1b96834767 | ||
|
|
73746a016e | ||
|
|
781f7ea3e6 | ||
|
|
ee9419998b | ||
|
|
f3d415f7a0 | ||
|
|
904349a75c | ||
|
|
fdb1f180e4 | ||
|
|
c34c4d2e29 | ||
|
|
e757efb83d | ||
|
|
007032c83b | ||
|
|
29e13fe96a | ||
|
|
3a8d4bbf71 | ||
|
|
5825907680 | ||
|
|
496c4babb6 | ||
|
|
c7b73d31a5 | ||
|
|
3b9a06d5aa | ||
|
|
a1258baf5a | ||
|
|
76de3683ac | ||
|
|
baddb899f7 | ||
|
|
19d4cbefe8 | ||
|
|
af1a741699 | ||
|
|
07e86b1e85 | ||
|
|
72c2f5c3e6 | ||
|
|
8566d1f9a4 | ||
|
|
ae876c7532 | ||
|
|
502f96011e | ||
|
|
17b39ab7bc | ||
|
|
c319796355 | ||
|
|
4dcd3cd0b2 | ||
|
|
eb3a2b298f | ||
|
|
333ea74895 | ||
|
|
e05dac801f | ||
|
|
31f865f8e4 | ||
|
|
612bf0b58a | ||
|
|
c73c7abfcd | ||
|
|
f31438d9a6 | ||
|
|
4abfc23006 | ||
|
|
52c460d5b9 | ||
|
|
6179aa7d35 | ||
|
|
268e2a0c96 | ||
|
|
7af9353936 | ||
|
|
f943a83b71 | ||
|
|
a3c020b4ee | ||
|
|
cc6c013f63 | ||
|
|
a140780405 |
12
.github/FUNDING.yml
vendored
Normal file
12
.github/FUNDING.yml
vendored
Normal file
@@ -0,0 +1,12 @@
|
||||
# These are supported funding model platforms
|
||||
|
||||
github: # Replace with up to 4 GitHub Sponsors-enabled usernames e.g., [user1, user2]
|
||||
patreon: # Replace with a single Patreon username
|
||||
open_collective: # Replace with a single Open Collective username
|
||||
ko_fi: # Replace with a single Ko-fi username
|
||||
tidelift: # Replace with a single Tidelift platform-name/package-name e.g., npm/babel
|
||||
community_bridge: # Replace with a single Community Bridge project-name e.g., cloud-foundry
|
||||
liberapay: # Replace with a single Liberapay username
|
||||
issuehunt: # Replace with a single IssueHunt username
|
||||
otechie: # Replace with a single Otechie username
|
||||
custom: https://dev-funding.webui.wowkira.com
|
||||
3
.gitmodules
vendored
3
.gitmodules
vendored
@@ -12,3 +12,6 @@
|
||||
[submodule "external/trezor-common"]
|
||||
path = external/trezor-common
|
||||
url = https://github.com/trezor/trezor-common.git
|
||||
[submodule "external/randomwow"]
|
||||
path = external/randomwow
|
||||
url = https://github.com/wownero/RandomWOW
|
||||
|
||||
@@ -177,6 +177,15 @@ else()
|
||||
message(STATUS "Building without build tag")
|
||||
endif()
|
||||
|
||||
# Update and init submodules by default
|
||||
if(NOT MANUAL_SUBMODULES)
|
||||
find_package(Git)
|
||||
if(GIT_FOUND)
|
||||
message(STATUS "Initializing submodules")
|
||||
execute_process(COMMAND git "submodule" "update" "--init" "--recursive" WORKING_DIRECTORY ${CMAKE_SOURCE_DIR})
|
||||
endif()
|
||||
endif()
|
||||
|
||||
if(NOT MANUAL_SUBMODULES)
|
||||
find_package(Git)
|
||||
if(GIT_FOUND)
|
||||
@@ -196,6 +205,7 @@ if(NOT MANUAL_SUBMODULES)
|
||||
check_submodule(external/unbound)
|
||||
check_submodule(external/rapidjson)
|
||||
check_submodule(external/trezor-common)
|
||||
check_submodule(external/randomwow)
|
||||
endif()
|
||||
endif()
|
||||
|
||||
@@ -244,7 +254,7 @@ endif()
|
||||
set_property(GLOBAL PROPERTY USE_FOLDERS ON)
|
||||
enable_testing()
|
||||
|
||||
option(BUILD_DOCUMENTATION "Build the Doxygen documentation." ON)
|
||||
option(BUILD_DOCUMENTATION "Build the Doxygen documentation." OFF)
|
||||
option(BUILD_TESTS "Build tests." OFF)
|
||||
|
||||
# Check whether we're on a 32-bit or 64-bit system
|
||||
@@ -488,6 +498,14 @@ ExternalProject_Add(generate_translations_header
|
||||
include_directories("${CMAKE_CURRENT_BINARY_DIR}/translations")
|
||||
add_subdirectory(external)
|
||||
|
||||
# Final setup for miniupnpc
|
||||
if(UPNP_STATIC OR IOS)
|
||||
add_definitions("-DUPNP_STATIC")
|
||||
else()
|
||||
add_definitions("-DUPNP_DYNAMIC")
|
||||
include_directories(${UPNP_INCLUDE})
|
||||
endif()
|
||||
|
||||
# Final setup for libunbound
|
||||
include_directories(${UNBOUND_INCLUDE})
|
||||
link_directories(${UNBOUND_LIBRARY_DIRS})
|
||||
@@ -672,8 +690,11 @@ else()
|
||||
add_cxx_flag_if_supported(-fstack-clash-protection CXX_SECURITY_FLAGS)
|
||||
endif()
|
||||
|
||||
add_c_flag_if_supported(-mmitigate-rop C_SECURITY_FLAGS)
|
||||
add_cxx_flag_if_supported(-mmitigate-rop CXX_SECURITY_FLAGS)
|
||||
# Removed in GCC 9.1 (or before ?), but still accepted, so spams the output
|
||||
if (NOT (CMAKE_C_COMPILER_ID STREQUAL "GNU" AND NOT CMAKE_C_COMPILER_VERSION VERSION_LESS 9.1))
|
||||
add_c_flag_if_supported(-mmitigate-rop C_SECURITY_FLAGS)
|
||||
add_cxx_flag_if_supported(-mmitigate-rop CXX_SECURITY_FLAGS)
|
||||
endif()
|
||||
|
||||
# linker
|
||||
if (NOT WIN32)
|
||||
|
||||
8
Makefile
8
Makefile
@@ -69,7 +69,7 @@ debug-test-trezor:
|
||||
|
||||
debug-all:
|
||||
mkdir -p $(builddir)/debug
|
||||
cd $(builddir)/debug && cmake -D BUILD_TESTS=ON -D BUILD_SHARED_LIBS=OFF -D CMAKE_BUILD_TYPE=Debug $(topdir) && $(MAKE)
|
||||
cd $(builddir)/debug && cmake -D BUILD_TESTS=OFF -D BUILD_SHARED_LIBS=OFF -D CMAKE_BUILD_TYPE=Debug $(topdir) && $(MAKE)
|
||||
|
||||
debug-static-all:
|
||||
mkdir -p $(builddir)/debug
|
||||
@@ -85,7 +85,7 @@ debug-static-win32:
|
||||
|
||||
cmake-release:
|
||||
mkdir -p $(builddir)/release
|
||||
cd $(builddir)/release && cmake -D CMAKE_BUILD_TYPE=Release $(topdir)
|
||||
cd $(builddir)/release && cmake -D BUILD_TESTS=OFF -D CMAKE_BUILD_TYPE=Release $(topdir)
|
||||
|
||||
release: cmake-release
|
||||
cd $(builddir)/release && $(MAKE)
|
||||
@@ -96,11 +96,11 @@ release-test:
|
||||
|
||||
release-all:
|
||||
mkdir -p $(builddir)/release
|
||||
cd $(builddir)/release && cmake -D BUILD_TESTS=ON -D CMAKE_BUILD_TYPE=release $(topdir) && $(MAKE)
|
||||
cd $(builddir)/release && cmake -D BUILD_TESTS=OFF -D CMAKE_BUILD_TYPE=release $(topdir) && $(MAKE)
|
||||
|
||||
release-static:
|
||||
mkdir -p $(builddir)/release
|
||||
cd $(builddir)/release && cmake -D STATIC=ON -D ARCH="x86-64" -D BUILD_64=ON -D CMAKE_BUILD_TYPE=release $(topdir) && $(MAKE)
|
||||
cd $(builddir)/release && cmake -D BUILD_TESTS=OFF -D STATIC=ON -D ARCH="x86-64" -D BUILD_64=ON -D CMAKE_BUILD_TYPE=release $(topdir) && $(MAKE)
|
||||
|
||||
coverage:
|
||||
mkdir -p $(builddir)/debug
|
||||
|
||||
39
PKGBUILD
Normal file
39
PKGBUILD
Normal file
@@ -0,0 +1,39 @@
|
||||
# Maintainer: wowario <wowario at protonmail dot com>
|
||||
# Contributor: wowario <wowario at protonmail dot com>
|
||||
|
||||
pkgbase=('wownero-git')
|
||||
pkgname=('wownero-git')
|
||||
pkgver=0.5.0.2
|
||||
pkgrel=1
|
||||
pkgdesc="a fairly launched privacy-centric meme coin with no premine and a finite supply"
|
||||
license=('custom:Cryptonote')
|
||||
arch=('x86_64')
|
||||
url="http://wownero.org/"
|
||||
depends=('boost-libs' 'zeromq' 'unbound' 'libusb')
|
||||
makedepends=('git' 'cmake' 'boost')
|
||||
provides=('wownero-git')
|
||||
|
||||
source=("${pkgname}"::"git+https://github.com/wownero/wownero")
|
||||
|
||||
sha256sums=('SKIP')
|
||||
|
||||
pkgver() {
|
||||
cd "${srcdir}/${pkgname}"
|
||||
printf "$(echo ${pkgver} | sed 's/\.r.*//').r%s.g%s" \
|
||||
"$(git rev-list --count HEAD)" "$(git rev-parse --short HEAD)"
|
||||
}
|
||||
|
||||
build() {
|
||||
cd "${srcdir}/${pkgname}"
|
||||
git fetch --tags && git checkout tags/v0.5.0.2 -b v0.5.0.2
|
||||
USE_SINGLE_BUILDDIR=1 make
|
||||
}
|
||||
|
||||
package_wownero-git() {
|
||||
install -Dm644 "${srcdir}/${pkgname}/LICENSE" "${pkgdir}/usr/share/licenses/${pkgname}/LICENSE"
|
||||
install -Dm644 "${srcdir}/${pkgname}/utils/conf/wownerod.conf" "${pkgdir}/etc/wownerod.conf"
|
||||
install -Dm644 "${srcdir}/${pkgname}/utils/systemd/wownerod.service" "${pkgdir}/usr/lib/systemd/system/wownerod.service"
|
||||
install -Dm755 "${srcdir}/${pkgname}/build/release/bin/wownerod" "${pkgdir}/usr/bin/wownerod"
|
||||
install -Dm755 "${srcdir}/${pkgname}/build/release/bin/wownero-wallet-cli" "${pkgdir}/usr/bin/wownero-wallet-cli"
|
||||
install -Dm755 "${srcdir}/${pkgname}/build/release/bin/wownero-wallet-rpc" "${pkgdir}/usr/bin/wownero-wallet-rpc"
|
||||
}
|
||||
878
README.md
878
README.md
@@ -1,698 +1,111 @@
|
||||
# Monero
|
||||
# ~~Mo~~Wownero - Such privacy! Many coins! Wow! 🐕
|
||||
|
||||
Copyright (c) 2014-2019 The Monero Project.
|
||||
Portions Copyright (c) 2012-2013 The Cryptonote developers.
|
||||
|
||||
## Table of Contents
|
||||
## Resources
|
||||
|
||||
- [Development resources](#development-resources)
|
||||
- [Vulnerability response](#vulnerability-response)
|
||||
- [Research](#research)
|
||||
- [Announcements](#announcements)
|
||||
- [Translations](#translations)
|
||||
- [Build](#build)
|
||||
- [IMPORTANT](#important)
|
||||
- [Coverage](#coverage)
|
||||
- [Introduction](#introduction)
|
||||
- [About this project](#about-this-project)
|
||||
- [Supporting the project](#supporting-the-project)
|
||||
- [License](#license)
|
||||
- [Contributing](#contributing)
|
||||
- [Scheduled software upgrades](#scheduled-software-upgrades)
|
||||
- [Release staging schedule and protocol](#release-staging-schedule-and-protocol)
|
||||
- [Compiling Monero from source](#compiling-monero-from-source)
|
||||
- [Dependencies](#dependencies)
|
||||
- Web: [wownero.org](http://wownero.org)
|
||||
- Twitter: [@w0wn3r0](https://twitter.com/w0wn3r0)
|
||||
- Discord: [discord.gg/sQt74ep](https://discord.gg/sQt74ep)
|
||||
- Reddit: [/r/wownero](https://www.reddit.com/r/wownero)
|
||||
- Mail: [wownero@protonmail.com](mailto:wownero@protonmail.com)
|
||||
- GitHub: [https://github.com/wownero/wownero](https://github.com/wownero/wownero)
|
||||
- IRC: [#wownero on Freenode](https://kiwiirc.com/client/irc.freenode.net/?nick=suchchatter|?#wownero)
|
||||
- Bitmessage Chan: wownero (`BM-2cSzWtrj2pzLva9GF1Jp2TYsnLjrnJpvba`)
|
||||
- Network stats: [https://freeboard.io/board/c8mM2c](https://freeboard.io/board/c8mM2c)
|
||||
- Wownero Funding System: [https://funding.wownero.com](https://funding.wownero.com)
|
||||
- Keybase Chat Group: [https://keybase.io/team/wownero](https://keybase.io/team/wownero)
|
||||
|
||||
## Development resources
|
||||
Blockchain Explorers
|
||||
- https://explore.wownero.com
|
||||
- https://explorer.wowkira.com
|
||||
- http://explorer.wowne.ro
|
||||
- http://dr4koizzq4ixyxqkz7qagx7bopt4gnrbtrp7cbqcji2fkp4mnve3wrqd.onion
|
||||
- http://wow5eqtzqvsg5jctqzg5g7uk3u62sfqiacj5x6lo4by7bvnj6jkvubyd.onion
|
||||
|
||||
- Web: [getmonero.org](https://getmonero.org)
|
||||
- Forum: [forum.getmonero.org](https://forum.getmonero.org)
|
||||
- Mail: [dev@getmonero.org](mailto:dev@getmonero.org)
|
||||
- GitHub: [https://github.com/monero-project/monero](https://github.com/monero-project/monero)
|
||||
- IRC: [#monero-dev on Freenode](https://webchat.freenode.net/?randomnick=1&channels=%23monero-dev&prompt=1&uio=d4)
|
||||
|
||||
## Vulnerability response
|
||||
|
||||
- Our [Vulnerability Response Process](https://github.com/monero-project/meta/blob/master/VULNERABILITY_RESPONSE_PROCESS.md) encourages responsible disclosure
|
||||
- We are also available via [HackerOne](https://hackerone.com/monero)
|
||||
|
||||
## Research
|
||||
|
||||
The [Monero Research Lab](https://src.getmonero.org/resources/research-lab/) is an open forum where the community coordinates research into Monero cryptography, protocols, fungibility, analysis, and more. We welcome collaboration and contributions from outside researchers! Because not all Lab work and publications are distributed as traditional preprints or articles, they may be easy to miss if you are conducting literature reviews for your own Monero research. You are encouraged to get in touch with our researchers if you have questions, wish to collaborate, or would like guidance to help avoid unnecessarily duplicating earlier or known work.
|
||||
|
||||
Our researchers are available on IRC in [#monero-research-lab on Freenode](https://webchat.freenode.net/?randomnick=1&channels=%23monero-research-lab&prompt=1&uio=d4) or by email:
|
||||
|
||||
- Sarang Noether, Ph.D.: [sarang@getmonero.org](mailto:sarang@getmonero.org) or [sarang.noether@protonmail.com](mailto:sarang.noether@protonmail.com); [research repository](https://github.com/SarangNoether/research-lab)
|
||||
- Surae Noether (Brandon Goodell), Ph.D.: [surae@getmonero.org](mailto:surae@getmonero.org) or [surae.noether@protonmail.com](mailto:surae.noether@protonmail.com); [research repository](https://github.com/b-g-goodell/research-lab)
|
||||
|
||||
## Announcements
|
||||
|
||||
- You can subscribe to an [announcement listserv](https://lists.getmonero.org) to get critical announcements from the Monero core team. The announcement list can be very helpful for knowing when software updates are needed.
|
||||
|
||||
## Translations
|
||||
The CLI wallet is available in different languages. If you want to help translate it, see our self-hosted localization platform, Pootle, on [translate.getmonero.org](https://translate.getmonero.org/projects/CLI/). Every translation *must* be uploaded on the platform, pull requests directly editing the code in this repository will be closed. If you need help with Pootle, you can find a guide with screenshots [here](https://github.com/monero-ecosystem/monero-translations/blob/master/pootle.md).
|
||||
|
||||
|
||||
If you need help/support/info about translations, contact the localization workgroup. You can find the complete list of contacts on the repository of the workgroup: [monero-translations](https://github.com/monero-ecosystem/monero-translations#contacts).
|
||||
|
||||
## Build
|
||||
|
||||
### IMPORTANT
|
||||
|
||||
These builds are of the master branch, which is used for active development and can be either unstable or incompatible with release software. Please compile release branches.
|
||||
|
||||
| Operating System | Processor | Status |
|
||||
| --------------------- | -------- |--------|
|
||||
| Ubuntu 16.04 | i686 | [](https://build.getmonero.org/builders/monero-static-ubuntu-i686)
|
||||
| Ubuntu 16.04 | amd64 | [](https://build.getmonero.org/builders/monero-static-ubuntu-amd64)
|
||||
| Ubuntu 16.04 | armv7 | [](https://build.getmonero.org/builders/monero-static-ubuntu-arm7)
|
||||
| Debian Stable | armv8 | [](https://build.getmonero.org/builders/monero-static-debian-armv8)
|
||||
| macOS 10.11 | amd64 | [](https://build.getmonero.org/builders/monero-static-osx-10.11)
|
||||
| macOS 10.12 | amd64 | [](https://build.getmonero.org/builders/monero-static-osx-10.12)
|
||||
| macOS 10.13 | amd64 | [](https://build.getmonero.org/builders/monero-static-osx-10.13)
|
||||
| FreeBSD 11 | amd64 | [](https://build.getmonero.org/builders/monero-static-freebsd64)
|
||||
| DragonFly BSD 4.6 | amd64 | [](https://build.getmonero.org/builders/monero-static-dragonflybsd-amd64)
|
||||
| Windows (MSYS2/MinGW) | i686 | [](https://build.getmonero.org/builders/monero-static-win32)
|
||||
| Windows (MSYS2/MinGW) | amd64 | [](https://build.getmonero.org/builders/monero-static-win64)
|
||||
|
||||
## Coverage
|
||||
|
||||
| Type | Status |
|
||||
|-----------|--------|
|
||||
| Coverity | [](https://scan.coverity.com/projects/9657/)
|
||||
| Coveralls | [](https://coveralls.io/github/monero-project/monero?branch=master)
|
||||
| License | [](https://opensource.org/licenses/BSD-3-Clause)
|
||||
Public Nodes
|
||||
- node.wowne.ro:34568
|
||||
- wowkira.com:34568
|
||||
- wow.aluisyo.network:34568
|
||||
|
||||
## Introduction
|
||||
|
||||
Monero is a private, secure, untraceable, decentralised digital currency. You are your bank, you control your funds, and nobody can trace your transfers unless you allow them to do so.
|
||||
|
||||
**Privacy:** Monero uses a cryptographically sound system to allow you to send and receive funds without your transactions being easily revealed on the blockchain (the ledger of transactions that everyone has). This ensures that your purchases, receipts, and all transfers remain absolutely private by default.
|
||||
|
||||
**Security:** Using the power of a distributed peer-to-peer consensus network, every transaction on the network is cryptographically secured. Individual wallets have a 25 word mnemonic seed that is only displayed once, and can be written down to backup the wallet. Wallet files are encrypted with a passphrase to ensure they are useless if stolen.
|
||||
|
||||
**Untraceability:** By taking advantage of ring signatures, a special property of a certain type of cryptography, Monero is able to ensure that transactions are not only untraceable, but have an optional measure of ambiguity that ensures that transactions cannot easily be tied back to an individual user or computer.
|
||||
|
||||
**Decentralization:** The utility of monero depends on its decentralised peer-to-peer consensus network - anyone should be able to run the monero software, validate the integrity of the blockchain, and participate in all aspects of the monero network using consumer-grade commodity hardware. Decentralization of the monero network is maintained by software development that minimizes the costs of running the monero software and inhibits the proliferation of specialized, non-commodity hardware.
|
||||
|
||||
## About this project
|
||||
|
||||
This is the core implementation of Monero. It is open source and completely free to use without restrictions, except for those specified in the license agreement below. There are no restrictions on anyone creating an alternative implementation of Monero that uses the protocol and network in a compatible manner.
|
||||
|
||||
As with many development projects, the repository on Github is considered to be the "staging" area for the latest changes. Before changes are merged into that branch on the main repository, they are tested by individual developers in their own branches, submitted as a pull request, and then subsequently tested by contributors who focus on testing and code reviews. That having been said, the repository should be carefully considered before using it in a production environment, unless there is a patch in the repository for a particular show-stopping issue you are experiencing. It is generally a better idea to use a tagged release for stability.
|
||||
|
||||
**Anyone is welcome to contribute to Monero's codebase!** If you have a fix or code change, feel free to submit it as a pull request directly to the "master" branch. In cases where the change is relatively small or does not affect other parts of the codebase it may be merged in immediately by any one of the collaborators. On the other hand, if the change is particularly large or complex, it is expected that it will be discussed at length either well in advance of the pull request being submitted, or even directly on the pull request.
|
||||
|
||||
## Supporting the project
|
||||
|
||||
Monero is a 100% community-sponsored endeavor. If you want to join our efforts, the easiest thing you can do is support the project financially. Both Monero and Bitcoin donations can be made to **donate.getmonero.org** if using a client that supports the [OpenAlias](https://openalias.org) standard. Alternatively you can send XMR to the Monero donation address via the `donate` command (type `help` in the command-line wallet for details).
|
||||
|
||||
The Monero donation address is: `44AFFq5kSiGBoZ4NMDwYtN18obc8AemS33DBLWs3H7otXft3XjrpDtQGv7SqSsaBYBb98uNbr2VBBEt7f2wfn3RVGQBEP3A` (viewkey: `f359631075708155cc3d92a32b75a7d02a5dcf27756707b47a2b31b21c389501`)
|
||||
|
||||
The Bitcoin donation address is: `1KTexdemPdxSBcG55heUuTjDRYqbC5ZL8H`
|
||||
|
||||
Core development funding and/or some supporting services are also graciously provided by sponsors:
|
||||
|
||||
[<img width="80" src="https://static.getmonero.org/images/sponsors/mymonero.png"/>](https://mymonero.com)
|
||||
[<img width="150" src="https://static.getmonero.org/images/sponsors/kitware.png?1"/>](https://kitware.com)
|
||||
[<img width="100" src="https://static.getmonero.org/images/sponsors/dome9.png"/>](https://dome9.com)
|
||||
[<img width="150" src="https://static.getmonero.org/images/sponsors/araxis.png"/>](https://araxis.com)
|
||||
[<img width="150" src="https://static.getmonero.org/images/sponsors/jetbrains.png"/>](https://www.jetbrains.com/)
|
||||
[<img width="150" src="https://static.getmonero.org/images/sponsors/navicat.png"/>](https://www.navicat.com/)
|
||||
[<img width="150" src="https://static.getmonero.org/images/sponsors/symas.png"/>](https://www.symas.com/)
|
||||
|
||||
There are also several mining pools that kindly donate a portion of their fees, [a list of them can be found on our Bitcointalk post](https://bitcointalk.org/index.php?topic=583449.0).
|
||||
|
||||
## License
|
||||
|
||||
See [LICENSE](LICENSE).
|
||||
|
||||
## Contributing
|
||||
|
||||
If you want to help out, see [CONTRIBUTING](CONTRIBUTING.md) for a set of guidelines.
|
||||
Wownero is a privacy-centric memecoin that was fairly launched on April 1, 2018 with no pre-mine, stealth-mine or ICO. Wownero has a maximum supply of around 184 million WOW with a slow and steady emission over 50 years. It is a fork of Monero, but with its own genesis block, so there is no degradation of privacy due to ring signatures using different participants for the same tx outputs on opposing forks.
|
||||
|
||||
## Scheduled software upgrades
|
||||
|
||||
Monero uses a fixed-schedule software upgrade (hard fork) mechanism to implement new features. This means that users of Monero (end users and service providers) should run current versions and upgrade their software on a regular schedule. Software upgrades occur during the months of April and October. The required software for these upgrades will be available prior to the scheduled date. Please check the repository prior to this date for the proper Monero software version. Below is the historical schedule and the projected schedule for the next upgrade.
|
||||
Dates are provided in the format YYYY-MM-DD.
|
||||
Wownero uses a fixed-schedule software upgrade (hard fork) mechanism to implement new features. This means that users of Wownero (end users and service providers) should run current versions and upgrade their software on a regular schedule. The required software for these upgrades will be available prior to the scheduled date. Please check the repository prior to this date for the proper Wownero software version. Below is the historical schedule and the projected schedule for the next upgrade.
|
||||
Dates are provided in the format YYYY-MM-DD.
|
||||
|
||||
|
||||
| Software upgrade block height | Date | Fork version | Minimum Monero version | Recommended Monero version | Details |
|
||||
| Software upgrade block height | Date | Release Name | Minimum Wownero version | Recommended Wownero version | Details |
|
||||
| ------------------------------ | -----------| ----------------- | ---------------------- | -------------------------- | ---------------------------------------------------------------------------------- |
|
||||
| 1009827 | 2016-03-22 | v2 | v0.9.4 | v0.9.4 | Allow only >= ringsize 3, blocktime = 120 seconds, fee-free blocksize 60 kb |
|
||||
| 1141317 | 2016-09-21 | v3 | v0.9.4 | v0.10.0 | Splits coinbase into denominations |
|
||||
| 1220516 | 2017-01-05 | v4 | v0.10.1 | v0.10.2.1 | Allow normal and RingCT transactions |
|
||||
| 1288616 | 2017-04-15 | v5 | v0.10.3.0 | v0.10.3.1 | Adjusted minimum blocksize and fee algorithm |
|
||||
| 1400000 | 2017-09-16 | v6 | v0.11.0.0 | v0.11.0.0 | Allow only RingCT transactions, allow only >= ringsize 5 |
|
||||
| 1546000 | 2018-04-06 | v7 | v0.12.0.0 | v0.12.3.0 | Cryptonight variant 1, ringsize >= 7, sorted inputs
|
||||
| 1685555 | 2018-10-18 | v8 | v0.13.0.0 | v0.13.0.4 | max transaction size at half the penalty free block size, bulletproofs enabled, cryptonight variant 2, fixed ringsize [11](https://youtu.be/KOO5S4vxi0o)
|
||||
| 1686275 | 2018-10-19 | v9 | v0.13.0.0 | v0.13.0.4 | bulletproofs required
|
||||
| 1788000 | 2019-03-09 | v10 | v0.14.0.0 | v0.14.0.2 | New PoW based on Cryptonight-R, new block weight algorithm, slightly more efficient RingCT format
|
||||
| 1788720 | 2019-03-10 | v11 | v0.14.0.0 | v0.14.0.2 | forbid old RingCT transaction format
|
||||
| XXXXXXX | 2019-10-XX | XX | XXXXXXXXX | XXXXXXXXX | X
|
||||
| 1 | 2018-04-01 | Awesome Akita | v0.1.0.0 | v0.1.0.0 | Cryptonight variant 1, ringsize >= 8, sorted inputs
|
||||
| 6969 | 2018-04-24 | Busty Brazzers | v0.2.0.0 | v0.2.0.0 | Bulletproofs, LWMA difficulty algorithm, ringsize >= 10, reduce unlock to 4
|
||||
| 53666 | 2018-10-06 | Cool Cage | v0.3.0.0 | v0.3.1.3 | Cryptonight variant 2, LWMA v2, ringsize = 22, MMS
|
||||
| 63469 | 2018-11-11 | Dank Doge | v0.4.0.0 | v0.4.0.0 | LWMA v4
|
||||
| 81769 | 2019-02-19 | Erotic EggplantEmoji | v0.5.0.0 | v0.5.0.2 | Cryptonight/wow, LWMA v1 with N=144, Updated Bulletproofs, Fee Per Byte, Auto-churn
|
||||
| 114969 | 2019-06-14 | F For Fappening | v0.6.1.0 | v0.6.1.1 | RandomWOW, new block weight algorithm, slightly more efficient RingCT format
|
||||
|
||||
X's indicate that these details have not been determined as of commit date.
|
||||
|
||||
## Release staging schedule and protocol
|
||||
## Release staging and Contributing
|
||||
|
||||
Approximately three months prior to a scheduled software upgrade, a branch from Master will be created with the new release version tag. Pull requests that address bugs should then be made to both Master and the new release branch. Pull requests that require extensive review and testing (generally, optimizations and new features) should *not* be made to the release branch.
|
||||
**Anyone is welcome to contribute to Wownero's codebase!**
|
||||
|
||||
## Compiling Monero from source
|
||||
If you have a fix or code change, feel free to submit it as a pull request. Ahead of a scheduled software upgrade, a development branch will be created with the new release version tag. Pull requests that address bugs should be made to Master. Pull requests that require review and testing (generally, optimizations and new features) should be made to the development branch. All pull requests will be considered safe until the US dollar valuation of 1 Wownero equals $1000. After this valuation has been reached, more research will be needed to introduce experimental cryptography and/or code into the codebase.
|
||||
|
||||
### Dependencies
|
||||
|
||||
The following table summarizes the tools and libraries required to build. A
|
||||
few of the libraries are also included in this repository (marked as
|
||||
"Vendored"). By default, the build uses the library installed on the system,
|
||||
and ignores the vendored sources. However, if no library is found installed on
|
||||
the system, then the vendored source will be built and used. The vendored
|
||||
sources are also used for statically-linked builds because distribution
|
||||
packages often include only shared library binaries (`.so`) but not static
|
||||
library archives (`.a`).
|
||||
|
||||
| Dep | Min. version | Vendored | Debian/Ubuntu pkg | Arch pkg | Fedora | Optional | Purpose |
|
||||
| ------------ | ------------- | -------- | ------------------ | ------------ | ----------------- | -------- | -------------- |
|
||||
| GCC | 4.7.3 | NO | `build-essential` | `base-devel` | `gcc` | NO | |
|
||||
| CMake | 3.5 | NO | `cmake` | `cmake` | `cmake` | NO | |
|
||||
| pkg-config | any | NO | `pkg-config` | `base-devel` | `pkgconf` | NO | |
|
||||
| Boost | 1.58 | NO | `libboost-all-dev` | `boost` | `boost-devel` | NO | C++ libraries |
|
||||
| OpenSSL | basically any | NO | `libssl-dev` | `openssl` | `openssl-devel` | NO | sha256 sum |
|
||||
| libzmq | 3.0.0 | NO | `libzmq3-dev` | `zeromq` | `cppzmq-devel` | NO | ZeroMQ library |
|
||||
| OpenPGM | ? | NO | `libpgm-dev` | `libpgm` | `openpgm-devel` | NO | For ZeroMQ |
|
||||
| libnorm[2] | ? | NO | `libnorm-dev` | | ` | YES | For ZeroMQ |
|
||||
| libunbound | 1.4.16 | YES | `libunbound-dev` | `unbound` | `unbound-devel` | NO | DNS resolver |
|
||||
| libsodium | ? | NO | `libsodium-dev` | `libsodium` | `libsodium-devel` | NO | cryptography |
|
||||
| libunwind | any | NO | `libunwind8-dev` | `libunwind` | `libunwind-devel` | YES | Stack traces |
|
||||
| liblzma | any | NO | `liblzma-dev` | `xz` | `xz-devel` | YES | For libunwind |
|
||||
| libreadline | 6.3.0 | NO | `libreadline6-dev` | `readline` | `readline-devel` | YES | Input editing |
|
||||
| ldns | 1.6.17 | NO | `libldns-dev` | `ldns` | `ldns-devel` | YES | SSL toolkit |
|
||||
| expat | 1.1 | NO | `libexpat1-dev` | `expat` | `expat-devel` | YES | XML parsing |
|
||||
| GTest | 1.5 | YES | `libgtest-dev`[1] | `gtest` | `gtest-devel` | YES | Test suite |
|
||||
| Doxygen | any | NO | `doxygen` | `doxygen` | `doxygen` | YES | Documentation |
|
||||
| Graphviz | any | NO | `graphviz` | `graphviz` | `graphviz` | YES | Documentation |
|
||||
|
||||
|
||||
[1] On Debian/Ubuntu `libgtest-dev` only includes sources and headers. You must
|
||||
build the library binary manually. This can be done with the following command ```sudo apt-get install libgtest-dev && cd /usr/src/gtest && sudo cmake . && sudo make && sudo mv libg* /usr/lib/ ```
|
||||
[2] libnorm-dev is needed if your zmq library was built with libnorm, and not needed otherwise
|
||||
|
||||
Install all dependencies at once on Debian/Ubuntu:
|
||||
|
||||
``` sudo apt update && sudo apt install build-essential cmake pkg-config libboost-all-dev libssl-dev libzmq3-dev libunbound-dev libsodium-dev libunwind8-dev liblzma-dev libreadline6-dev libldns-dev libexpat1-dev doxygen graphviz libpgm-dev```
|
||||
|
||||
Install all dependencies at once on macOS with the provided Brewfile:
|
||||
``` brew update && brew bundle --file=contrib/brew/Brewfile ```
|
||||
|
||||
FreeBSD one liner for required to build dependencies
|
||||
```pkg install git gmake cmake pkgconf boost-libs cppzmq libsodium```
|
||||
|
||||
### Cloning the repository
|
||||
|
||||
Clone recursively to pull-in needed submodule(s):
|
||||
|
||||
`$ git clone --recursive https://github.com/monero-project/monero`
|
||||
|
||||
If you already have a repo cloned, initialize and update:
|
||||
|
||||
`$ cd monero && git submodule init && git submodule update`
|
||||
|
||||
### Build instructions
|
||||
|
||||
Monero uses the CMake build system and a top-level [Makefile](Makefile) that
|
||||
invokes cmake commands as needed.
|
||||
|
||||
#### On Linux and macOS
|
||||
|
||||
* Install the dependencies
|
||||
* Change to the root of the source code directory, change to the most recent release branch, and build:
|
||||
|
||||
```bash
|
||||
cd monero
|
||||
git checkout release-v0.14
|
||||
make
|
||||
```
|
||||
|
||||
*Optional*: If your machine has several cores and enough memory, enable
|
||||
parallel build by running `make -j<number of threads>` instead of `make`. For
|
||||
this to be worthwhile, the machine should have one core and about 2GB of RAM
|
||||
available per thread.
|
||||
|
||||
*Note*: If cmake can not find zmq.hpp file on macOS, installing `zmq.hpp` from
|
||||
https://github.com/zeromq/cppzmq to `/usr/local/include` should fix that error.
|
||||
|
||||
*Note*: The instructions above will compile the most stable release of the
|
||||
Monero software. If you would like to use and test the most recent software,
|
||||
use ```git checkout master```. The master branch may contain updates that are
|
||||
both unstable and incompatible with release software, though testing is always
|
||||
encouraged.
|
||||
|
||||
* The resulting executables can be found in `build/release/bin`
|
||||
|
||||
* Add `PATH="$PATH:$HOME/monero/build/release/bin"` to `.profile`
|
||||
|
||||
* Run Monero with `monerod --detach`
|
||||
|
||||
* **Optional**: build and run the test suite to verify the binaries:
|
||||
|
||||
```bash
|
||||
make release-test
|
||||
```
|
||||
|
||||
*NOTE*: `core_tests` test may take a few hours to complete.
|
||||
|
||||
* **Optional**: to build binaries suitable for debugging:
|
||||
|
||||
```bash
|
||||
make debug
|
||||
```
|
||||
|
||||
* **Optional**: to build statically-linked binaries:
|
||||
|
||||
```bash
|
||||
make release-static
|
||||
```
|
||||
|
||||
Dependencies need to be built with -fPIC. Static libraries usually aren't, so you may have to build them yourself with -fPIC. Refer to their documentation for how to build them.
|
||||
|
||||
* **Optional**: build documentation in `doc/html` (omit `HAVE_DOT=YES` if `graphviz` is not installed):
|
||||
|
||||
```bash
|
||||
HAVE_DOT=YES doxygen Doxyfile
|
||||
```
|
||||
|
||||
#### On the Raspberry Pi
|
||||
|
||||
Tested on a Raspberry Pi Zero with a clean install of minimal Raspbian Stretch (2017-09-07 or later) from https://www.raspberrypi.org/downloads/raspbian/. If you are using Raspian Jessie, [please see note in the following section](#note-for-raspbian-jessie-users).
|
||||
|
||||
* `apt-get update && apt-get upgrade` to install all of the latest software
|
||||
|
||||
* Install the dependencies for Monero from the 'Debian' column in the table above.
|
||||
|
||||
* Increase the system swap size:
|
||||
|
||||
```bash
|
||||
sudo /etc/init.d/dphys-swapfile stop
|
||||
sudo nano /etc/dphys-swapfile
|
||||
CONF_SWAPSIZE=2048
|
||||
sudo /etc/init.d/dphys-swapfile start
|
||||
```
|
||||
|
||||
* If using an external hard disk without an external power supply, ensure it gets enough power to avoid hardware issues when syncing, by adding the line "max_usb_current=1" to /boot/config.txt
|
||||
|
||||
* Clone monero and checkout the most recent release version:
|
||||
|
||||
```bash
|
||||
git clone https://github.com/monero-project/monero.git
|
||||
cd monero
|
||||
git checkout tags/v0.14.1.0
|
||||
```
|
||||
|
||||
* Build:
|
||||
|
||||
```bash
|
||||
make release
|
||||
```
|
||||
|
||||
* Wait 4-6 hours
|
||||
|
||||
* The resulting executables can be found in `build/release/bin`
|
||||
|
||||
* Add `PATH="$PATH:$HOME/monero/build/release/bin"` to `.profile`
|
||||
|
||||
* Run Monero with `monerod --detach`
|
||||
|
||||
* You may wish to reduce the size of the swap file after the build has finished, and delete the boost directory from your home directory
|
||||
|
||||
#### *Note for Raspbian Jessie users:*
|
||||
|
||||
If you are using the older Raspbian Jessie image, compiling Monero is a bit more complicated. The version of Boost available in the Debian Jessie repositories is too old to use with Monero, and thus you must compile a newer version yourself. The following explains the extra steps, and has been tested on a Raspberry Pi 2 with a clean install of minimal Raspbian Jessie.
|
||||
|
||||
* As before, `apt-get update && apt-get upgrade` to install all of the latest software, and increase the system swap size
|
||||
|
||||
```bash
|
||||
sudo /etc/init.d/dphys-swapfile stop
|
||||
sudo nano /etc/dphys-swapfile
|
||||
CONF_SWAPSIZE=2048
|
||||
sudo /etc/init.d/dphys-swapfile start
|
||||
```
|
||||
|
||||
|
||||
* Then, install the dependencies for Monero except `libunwind` and `libboost-all-dev`
|
||||
|
||||
* Install the latest version of boost (this may first require invoking `apt-get remove --purge libboost*` to remove a previous version if you're not using a clean install):
|
||||
|
||||
```bash
|
||||
cd
|
||||
wget https://sourceforge.net/projects/boost/files/boost/1.64.0/boost_1_64_0.tar.bz2
|
||||
tar xvfo boost_1_64_0.tar.bz2
|
||||
cd boost_1_64_0
|
||||
./bootstrap.sh
|
||||
sudo ./b2
|
||||
```
|
||||
|
||||
* Wait ~8 hours
|
||||
|
||||
```bash
|
||||
sudo ./bjam cxxflags=-fPIC cflags=-fPIC -a install
|
||||
```
|
||||
|
||||
* Wait ~4 hours
|
||||
|
||||
* From here, follow the [general Raspberry Pi instructions](#on-the-raspberry-pi) from the "Clone monero and checkout most recent release version" step.
|
||||
|
||||
#### On Windows:
|
||||
|
||||
Binaries for Windows are built on Windows using the MinGW toolchain within
|
||||
[MSYS2 environment](https://www.msys2.org). The MSYS2 environment emulates a
|
||||
POSIX system. The toolchain runs within the environment and *cross-compiles*
|
||||
binaries that can run outside of the environment as a regular Windows
|
||||
application.
|
||||
|
||||
**Preparing the build environment**
|
||||
|
||||
* Download and install the [MSYS2 installer](https://www.msys2.org), either the 64-bit or the 32-bit package, depending on your system.
|
||||
* Open the MSYS shell via the `MSYS2 Shell` shortcut
|
||||
* Update packages using pacman:
|
||||
|
||||
```bash
|
||||
pacman -Syu
|
||||
```
|
||||
|
||||
* Exit the MSYS shell using Alt+F4
|
||||
* Edit the properties for the `MSYS2 Shell` shortcut changing "msys2_shell.bat" to "msys2_shell.cmd -mingw64" for 64-bit builds or "msys2_shell.cmd -mingw32" for 32-bit builds
|
||||
* Restart MSYS shell via modified shortcut and update packages again using pacman:
|
||||
|
||||
```bash
|
||||
pacman -Syu
|
||||
```
|
||||
|
||||
|
||||
* Install dependencies:
|
||||
|
||||
To build for 64-bit Windows:
|
||||
|
||||
```bash
|
||||
pacman -S mingw-w64-x86_64-toolchain make mingw-w64-x86_64-cmake mingw-w64-x86_64-boost mingw-w64-x86_64-openssl mingw-w64-x86_64-zeromq mingw-w64-x86_64-libsodium mingw-w64-x86_64-hidapi
|
||||
```
|
||||
|
||||
To build for 32-bit Windows:
|
||||
|
||||
```bash
|
||||
pacman -S mingw-w64-i686-toolchain make mingw-w64-i686-cmake mingw-w64-i686-boost mingw-w64-i686-openssl mingw-w64-i686-zeromq mingw-w64-i686-libsodium mingw-w64-i686-hidapi
|
||||
```
|
||||
|
||||
* Open the MingW shell via `MinGW-w64-Win64 Shell` shortcut on 64-bit Windows
|
||||
or `MinGW-w64-Win64 Shell` shortcut on 32-bit Windows. Note that if you are
|
||||
running 64-bit Windows, you will have both 64-bit and 32-bit MinGW shells.
|
||||
|
||||
**Cloning**
|
||||
|
||||
* To git clone, run:
|
||||
|
||||
```bash
|
||||
git clone --recursive https://github.com/monero-project/monero.git
|
||||
```
|
||||
|
||||
**Building**
|
||||
|
||||
* Change to the cloned directory, run:
|
||||
|
||||
```bash
|
||||
cd monero
|
||||
```
|
||||
|
||||
* If you would like a specific [version/tag](https://github.com/monero-project/monero/tags), do a git checkout for that version. eg. 'v0.14.1.0'. If you don't care about the version and just want binaries from master, skip this step:
|
||||
|
||||
```bash
|
||||
git checkout v0.14.1.0
|
||||
```
|
||||
|
||||
* If you are on a 64-bit system, run:
|
||||
|
||||
```bash
|
||||
make release-static-win64
|
||||
```
|
||||
|
||||
* If you are on a 32-bit system, run:
|
||||
|
||||
```bash
|
||||
make release-static-win32
|
||||
```
|
||||
|
||||
* The resulting executables can be found in `build/release/bin`
|
||||
|
||||
* **Optional**: to build Windows binaries suitable for debugging on a 64-bit system, run:
|
||||
|
||||
```bash
|
||||
make debug-static-win64
|
||||
```
|
||||
|
||||
* **Optional**: to build Windows binaries suitable for debugging on a 32-bit system, run:
|
||||
|
||||
```bash
|
||||
make debug-static-win32
|
||||
```
|
||||
|
||||
* The resulting executables can be found in `build/debug/bin`
|
||||
|
||||
### On FreeBSD:
|
||||
|
||||
The project can be built from scratch by following instructions for Linux above(but use `gmake` instead of `make`). If you are running monero in a jail you need to add the flag: `allow.sysvipc=1` to your jail configuration, otherwise lmdb will throw the error message: `Failed to open lmdb environment: Function not implemented`.
|
||||
|
||||
We expect to add Monero into the ports tree in the near future, which will aid in managing installations using ports or packages.
|
||||
|
||||
### On OpenBSD:
|
||||
|
||||
#### OpenBSD < 6.2
|
||||
|
||||
This has been tested on OpenBSD 5.8.
|
||||
|
||||
You will need to add a few packages to your system. `pkg_add db cmake gcc gcc-libs g++ gtest`.
|
||||
|
||||
The doxygen and graphviz packages are optional and require the xbase set.
|
||||
|
||||
The Boost package has a bug that will prevent librpc.a from building correctly. In order to fix this, you will have to Build boost yourself from scratch. Follow the directions here (under "Building Boost"):
|
||||
https://github.com/bitcoin/bitcoin/blob/master/doc/build-openbsd.md
|
||||
|
||||
You will have to add the serialization, date_time, and regex modules to Boost when building as they are needed by Monero.
|
||||
|
||||
To build: `env CC=egcc CXX=eg++ CPP=ecpp DEVELOPER_LOCAL_TOOLS=1 BOOST_ROOT=/path/to/the/boost/you/built make release-static-64`
|
||||
|
||||
#### OpenBSD 6.2 and 6.3
|
||||
|
||||
You will need to add a few packages to your system. `pkg_add cmake zeromq libiconv`.
|
||||
|
||||
The doxygen and graphviz packages are optional and require the xbase set.
|
||||
|
||||
|
||||
Build the Boost library using clang. This guide is derived from: https://github.com/bitcoin/bitcoin/blob/master/doc/build-openbsd.md
|
||||
|
||||
We assume you are compiling with a non-root user and you have `doas` enabled.
|
||||
|
||||
Note: do not use the boost package provided by OpenBSD, as we are installing boost to `/usr/local`.
|
||||
|
||||
```bash
|
||||
# Create boost building directory
|
||||
mkdir ~/boost
|
||||
cd ~/boost
|
||||
|
||||
# Fetch boost source
|
||||
ftp -o boost_1_64_0.tar.bz2 https://netcologne.dl.sourceforge.net/project/boost/boost/1.64.0/boost_1_64_0.tar.bz2
|
||||
|
||||
# MUST output: (SHA256) boost_1_64_0.tar.bz2: OK
|
||||
echo "7bcc5caace97baa948931d712ea5f37038dbb1c5d89b43ad4def4ed7cb683332 boost_1_64_0.tar.bz2" | sha256 -c
|
||||
tar xfj boost_1_64_0.tar.bz2
|
||||
|
||||
# Fetch and apply boost patches, required for OpenBSD
|
||||
ftp -o boost_test_impl_execution_monitor_ipp.patch https://raw.githubusercontent.com/openbsd/ports/bee9e6df517077a7269ff0dfd57995f5c6a10379/devel/boost/patches/patch-boost_test_impl_execution_monitor_ipp
|
||||
ftp -o boost_config_platform_bsd_hpp.patch https://raw.githubusercontent.com/openbsd/ports/90658284fb786f5a60dd9d6e8d14500c167bdaa0/devel/boost/patches/patch-boost_config_platform_bsd_hpp
|
||||
|
||||
# MUST output: (SHA256) boost_config_platform_bsd_hpp.patch: OK
|
||||
echo "1f5e59d1154f16ee1e0cc169395f30d5e7d22a5bd9f86358f738b0ccaea5e51d boost_config_platform_bsd_hpp.patch" | sha256 -c
|
||||
# MUST output: (SHA256) boost_test_impl_execution_monitor_ipp.patch: OK
|
||||
echo "30cec182a1437d40c3e0bd9a866ab5ddc1400a56185b7e671bb3782634ed0206 boost_test_impl_execution_monitor_ipp.patch" | sha256 -c
|
||||
|
||||
cd boost_1_64_0
|
||||
patch -p0 < ../boost_test_impl_execution_monitor_ipp.patch
|
||||
patch -p0 < ../boost_config_platform_bsd_hpp.patch
|
||||
|
||||
# Start building boost
|
||||
echo 'using clang : : c++ : <cxxflags>"-fvisibility=hidden -fPIC" <linkflags>"" <archiver>"ar" <striper>"strip" <ranlib>"ranlib" <rc>"" : ;' > user-config.jam
|
||||
./bootstrap.sh --without-icu --with-libraries=chrono,filesystem,program_options,system,thread,test,date_time,regex,serialization,locale --with-toolset=clang
|
||||
./b2 toolset=clang cxxflags="-stdlib=libc++" linkflags="-stdlib=libc++" -sICONV_PATH=/usr/local
|
||||
doas ./b2 -d0 runtime-link=shared threadapi=pthread threading=multi link=static variant=release --layout=tagged --build-type=complete --user-config=user-config.jam -sNO_BZIP2=1 -sICONV_PATH=/usr/local --prefix=/usr/local install
|
||||
```
|
||||
|
||||
Build the cppzmq bindings.
|
||||
|
||||
We assume you are compiling with a non-root user and you have `doas` enabled.
|
||||
|
||||
```bash
|
||||
# Create cppzmq building directory
|
||||
mkdir ~/cppzmq
|
||||
cd ~/cppzmq
|
||||
|
||||
# Fetch cppzmq source
|
||||
ftp -o cppzmq-4.2.3.tar.gz https://github.com/zeromq/cppzmq/archive/v4.2.3.tar.gz
|
||||
|
||||
# MUST output: (SHA256) cppzmq-4.2.3.tar.gz: OK
|
||||
echo "3e6b57bf49115f4ae893b1ff7848ead7267013087dc7be1ab27636a97144d373 cppzmq-4.2.3.tar.gz" | sha256 -c
|
||||
tar xfz cppzmq-4.2.3.tar.gz
|
||||
|
||||
# Start building cppzmq
|
||||
cd cppzmq-4.2.3
|
||||
mkdir build
|
||||
cd build
|
||||
cmake ..
|
||||
doas make install
|
||||
```
|
||||
|
||||
Build monero:
|
||||
```bash
|
||||
env DEVELOPER_LOCAL_TOOLS=1 BOOST_ROOT=/usr/local make release-static
|
||||
```
|
||||
|
||||
#### OpenBSD >= 6.4
|
||||
|
||||
You will need to add a few packages to your system. `pkg_add cmake gmake zeromq cppzmq libiconv boost`.
|
||||
|
||||
The doxygen and graphviz packages are optional and require the xbase set.
|
||||
|
||||
Build monero: `env DEVELOPER_LOCAL_TOOLS=1 BOOST_ROOT=/usr/local gmake release-static`
|
||||
|
||||
Note: you may encounter the following error, when compiling the latest version of monero as a normal user:
|
||||
|
||||
```
|
||||
LLVM ERROR: out of memory
|
||||
c++: error: unable to execute command: Abort trap (core dumped)
|
||||
```
|
||||
|
||||
Then you need to increase the data ulimit size to 2GB and try again: `ulimit -d 2000000`
|
||||
|
||||
### On Solaris:
|
||||
|
||||
The default Solaris linker can't be used, you have to install GNU ld, then run cmake manually with the path to your copy of GNU ld:
|
||||
|
||||
```bash
|
||||
mkdir -p build/release
|
||||
cd build/release
|
||||
cmake -DCMAKE_LINKER=/path/to/ld -D CMAKE_BUILD_TYPE=Release ../..
|
||||
cd ../..
|
||||
```
|
||||
|
||||
Then you can run make as usual.
|
||||
|
||||
### On Linux for Android (using docker):
|
||||
|
||||
```bash
|
||||
# Build image (for ARM 32-bit)
|
||||
docker build -f utils/build_scripts/android32.Dockerfile -t monero-android .
|
||||
# Build image (for ARM 64-bit)
|
||||
docker build -f utils/build_scripts/android64.Dockerfile -t monero-android .
|
||||
# Create container
|
||||
docker create -it --name monero-android monero-android bash
|
||||
# Get binaries
|
||||
docker cp monero-android:/src/build/release/bin .
|
||||
```
|
||||
|
||||
### Building portable statically linked binaries
|
||||
|
||||
By default, in either dynamically or statically linked builds, binaries target the specific host processor on which the build happens and are not portable to other processors. Portable binaries can be built using the following targets:
|
||||
|
||||
* ```make release-static-linux-x86_64``` builds binaries on Linux on x86_64 portable across POSIX systems on x86_64 processors
|
||||
* ```make release-static-linux-i686``` builds binaries on Linux on x86_64 or i686 portable across POSIX systems on i686 processors
|
||||
* ```make release-static-linux-armv8``` builds binaries on Linux portable across POSIX systems on armv8 processors
|
||||
* ```make release-static-linux-armv7``` builds binaries on Linux portable across POSIX systems on armv7 processors
|
||||
* ```make release-static-linux-armv6``` builds binaries on Linux portable across POSIX systems on armv6 processors
|
||||
* ```make release-static-win64``` builds binaries on 64-bit Windows portable across 64-bit Windows systems
|
||||
* ```make release-static-win32``` builds binaries on 64-bit or 32-bit Windows portable across 32-bit Windows systems
|
||||
|
||||
### Cross Compiling
|
||||
|
||||
You can also cross-compile static binaries on Linux for Windows and macOS with the `depends` system.
|
||||
|
||||
* ```make depends target=x86_64-linux-gnu``` for 64-bit linux binaries.
|
||||
* ```make depends target=x86_64-w64-mingw32``` for 64-bit windows binaries.
|
||||
* Requires: `python3 g++-mingw-w64-x86-64 wine1.6 bc`
|
||||
* ```make depends target=x86_64-apple-darwin11``` for macOS binaries.
|
||||
* Requires: `cmake imagemagick libcap-dev librsvg2-bin libz-dev libbz2-dev libtiff-tools python-dev`
|
||||
* ```make depends target=i686-linux-gnu``` for 32-bit linux binaries.
|
||||
* Requires: `g++-multilib bc`
|
||||
* ```make depends target=i686-w64-mingw32``` for 32-bit windows binaries.
|
||||
* Requires: `python3 g++-mingw-w64-i686`
|
||||
* ```make depends target=arm-linux-gnueabihf``` for armv7 binaries.
|
||||
* Requires: `g++-arm-linux-gnueabihf`
|
||||
* ```make depends target=aarch64-linux-gnu``` for armv8 binaries.
|
||||
* Requires: `g++-aarch64-linux-gnu`
|
||||
|
||||
The required packages are the names for each toolchain on apt. Depending on your distro, they may have different names.
|
||||
|
||||
Using `depends` might also be easier to compile Monero on Windows than using MSYS. Activate Windows Subsystem for Linux (WSL) with a distro (for example Ubuntu), install the apt build-essentials and follow the `depends` steps as depicted above.
|
||||
|
||||
The produced binaries still link libc dynamically. If the binary is compiled on a current distribution, it might not run on an older distribution with an older installation of libc. Passing `-DBACKCOMPAT=ON` to cmake will make sure that the binary will run on systems having at least libc version 2.17.
|
||||
|
||||
## Installing Monero from a package
|
||||
|
||||
**DISCLAIMER: These packages are not part of this repository or maintained by this project's contributors, and as such, do not go through the same review process to ensure their trustworthiness and security.**
|
||||
## Installing from a package
|
||||
|
||||
Packages are available for
|
||||
|
||||
* Ubuntu and [snap supported](https://snapcraft.io/docs/core/install) systems, via a community contributed build.
|
||||
* Arch Linux/Manjaro
|
||||
|
||||
```bash
|
||||
snap install monero --beta
|
||||
```
|
||||
yay -S wownero-git
|
||||
|
||||
Installing a snap is very quick. Snaps are secure. They are isolated with all of their dependencies. Snaps also auto update when a new version is released.
|
||||
* NixOS
|
||||
|
||||
* Arch Linux (via [AUR](https://aur.archlinux.org/)):
|
||||
- Stable release: [`monero`](https://aur.archlinux.org/packages/monero)
|
||||
- Bleeding edge: [`monero-git`](https://aur.archlinux.org/packages/monero-git)
|
||||
nix-shell -p altcoins.wownero
|
||||
|
||||
* Void Linux:
|
||||
* Ubuntu 18.04/Ubuntu 16.04/Debian 9/Debian 8 (amd64)
|
||||
|
||||
```bash
|
||||
xbps-install -S monero
|
||||
```
|
||||
|
||||
* GuixSD
|
||||
|
||||
```bash
|
||||
guix package -i monero
|
||||
```
|
||||
|
||||
* Docker
|
||||
|
||||
```bash
|
||||
# Build using all available cores
|
||||
docker build -t monero .
|
||||
|
||||
# or build using a specific number of cores (reduce RAM requirement)
|
||||
docker build --build-arg NPROC=1 -t monero .
|
||||
|
||||
# either run in foreground
|
||||
docker run -it -v /monero/chain:/root/.bitmonero -v /monero/wallet:/wallet -p 18080:18080 monero
|
||||
|
||||
# or in background
|
||||
docker run -it -d -v /monero/chain:/root/.bitmonero -v /monero/wallet:/wallet -p 18080:18080 monero
|
||||
```
|
||||
|
||||
* The build needs 3 GB space.
|
||||
* Wait one hour or more
|
||||
sudo apt-key adv --keyserver keyserver.ubuntu.com --recv-keys B09DF0E4B0C56A94
|
||||
sudo add-apt-repository "deb http://ppa.wownero.com/ bionic main"
|
||||
sudo apt-get update
|
||||
sudo apt-get install wownero
|
||||
|
||||
Packaging for your favorite distribution would be a welcome contribution!
|
||||
|
||||
## Running monerod
|
||||
**DISCLAIMER: These packages are not part of this repository, and as such, do not go through the same review process to ensure their trustworthiness and security.**
|
||||
|
||||
|
||||
## Building from Source
|
||||
|
||||
* Arch Linux/Manjaro
|
||||
|
||||
sudo pacman -Syu && sudo pacman -S base-devel cmake boost openssl zeromq libpgm unbound libsodium git
|
||||
git clone https://github.com/wownero/wownero
|
||||
cd wownero
|
||||
make
|
||||
|
||||
|
||||
* Debian/Ubuntu
|
||||
|
||||
sudo apt update && sudo apt install build-essential cmake pkg-config libboost-all-dev libssl-dev libzmq3-dev libunbound-dev libsodium-dev libpgm-dev git
|
||||
git clone https://github.com/wownero/wownero
|
||||
cd wownero
|
||||
make
|
||||
|
||||
|
||||
## Running Binaries
|
||||
|
||||
The build places the binary in `bin/` sub-directory within the build directory
|
||||
from which cmake was invoked (repository root by default). To run in
|
||||
foreground:
|
||||
|
||||
```bash
|
||||
./bin/monerod
|
||||
```
|
||||
./bin/wownerod
|
||||
|
||||
To list all available options, run `./bin/monerod --help`. Options can be
|
||||
To list all available options, run `./bin/wownerod --help`. Options can be
|
||||
specified either on the command line or in a configuration file passed by the
|
||||
`--config-file` argument. To specify an option in the configuration file, add
|
||||
a line with the syntax `argumentname=value`, where `argumentname` is the name
|
||||
@@ -700,148 +113,55 @@ of the argument without the leading dashes, for example `log-level=1`.
|
||||
|
||||
To run in background:
|
||||
|
||||
```bash
|
||||
./bin/monerod --log-file monerod.log --detach
|
||||
```
|
||||
./bin/wownerod --log-file wownerod.log --detach
|
||||
|
||||
To run as a systemd service, copy
|
||||
[monerod.service](utils/systemd/monerod.service) to `/etc/systemd/system/` and
|
||||
[monerod.conf](utils/conf/monerod.conf) to `/etc/`. The [example
|
||||
service](utils/systemd/monerod.service) assumes that the user `monero` exists
|
||||
[wownerod.service](utils/systemd/wownerod.service) to `/etc/systemd/system/` and
|
||||
[wownerod.conf](utils/conf/wownerod.conf) to `/etc/`. The [example
|
||||
service](utils/systemd/wownerod.service) assumes that the user `wownero` exists
|
||||
and its home is the data directory specified in the [example
|
||||
config](utils/conf/monerod.conf).
|
||||
config](utils/conf/wownerod.conf).
|
||||
|
||||
If you're on Mac, you may need to add the `--max-concurrency 1` option to
|
||||
monero-wallet-cli, and possibly monerod, if you get crashes refreshing.
|
||||
Once node is synced to network, run the CLI wallet by entering:
|
||||
|
||||
## Internationalization
|
||||
./bin/wownero-wallet-cli
|
||||
|
||||
See [README.i18n.md](README.i18n.md).
|
||||
Type `help` in CLI wallet to see standard commands (for advanced options, type `help_advanced`).
|
||||
|
||||
## Using Tor
|
||||
## Tor Anonymity Network
|
||||
|
||||
> There is a new, still experimental, [integration with Tor](ANONYMITY_NETWORKS.md). The
|
||||
> feature allows connecting over IPv4 and Tor simulatenously - IPv4 is used for
|
||||
> relaying blocks and relaying transactions received by peers whereas Tor is
|
||||
> used solely for relaying transactions received over local RPC. This provides
|
||||
> privacy and better protection against surrounding node (sybil) attacks.
|
||||
* Install [Tor Browser](https://www.torproject.org/download/)
|
||||
* Open `torrc` file in a text editor ([installation directory]/Browser/TorBrowser/Data/Tor/torrc) and add hidden service information as follows:
|
||||
|
||||
While Monero isn't made to integrate with Tor, it can be used wrapped with torsocks, by
|
||||
setting the following configuration parameters and environment variables:
|
||||
|
||||
* `--p2p-bind-ip 127.0.0.1` on the command line or `p2p-bind-ip=127.0.0.1` in
|
||||
monerod.conf to disable listening for connections on external interfaces.
|
||||
* `--no-igd` on the command line or `no-igd=1` in monerod.conf to disable IGD
|
||||
(UPnP port forwarding negotiation), which is pointless with Tor.
|
||||
* `DNS_PUBLIC=tcp` or `DNS_PUBLIC=tcp://x.x.x.x` where x.x.x.x is the IP of the
|
||||
desired DNS server, for DNS requests to go over TCP, so that they are routed
|
||||
through Tor. When IP is not specified, monerod uses the default list of
|
||||
servers defined in [src/common/dns_utils.cpp](src/common/dns_utils.cpp).
|
||||
* `TORSOCKS_ALLOW_INBOUND=1` to tell torsocks to allow monerod to bind to interfaces
|
||||
to accept connections from the wallet. On some Linux systems, torsocks
|
||||
allows binding to localhost by default, so setting this variable is only
|
||||
necessary to allow binding to local LAN/VPN interfaces to allow wallets to
|
||||
connect from remote hosts. On other systems, it may be needed for local wallets
|
||||
as well.
|
||||
* Do NOT pass `--detach` when running through torsocks with systemd, (see
|
||||
[utils/systemd/monerod.service](utils/systemd/monerod.service) for details).
|
||||
* If you use the wallet with a Tor daemon via the loopback IP (eg, 127.0.0.1:9050),
|
||||
then use `--untrusted-daemon` unless it is your own hidden service.
|
||||
|
||||
Example command line to start monerod through Tor:
|
||||
|
||||
```bash
|
||||
DNS_PUBLIC=tcp torsocks monerod --p2p-bind-ip 127.0.0.1 --no-igd
|
||||
```
|
||||
|
||||
### Using Tor on Tails
|
||||
|
||||
TAILS ships with a very restrictive set of firewall rules. Therefore, you need
|
||||
to add a rule to allow this connection too, in addition to telling torsocks to
|
||||
allow inbound connections. Full example:
|
||||
|
||||
```bash
|
||||
sudo iptables -I OUTPUT 2 -p tcp -d 127.0.0.1 -m tcp --dport 18081 -j ACCEPT
|
||||
DNS_PUBLIC=tcp torsocks ./monerod --p2p-bind-ip 127.0.0.1 --no-igd --rpc-bind-ip 127.0.0.1 \
|
||||
--data-dir /home/amnesia/Persistent/your/directory/to/the/blockchain
|
||||
HiddenServiceDir [installation directory]/Browser/TorBrowser/Data/Tor/wow_node
|
||||
HiddenServiceVersion 3
|
||||
HiddenServicePort 44469 127.0.0.1:44469
|
||||
```
|
||||
* Save `torrc` file and restart Tor Browser (keep open)
|
||||
* Change directory to the `wow_node` folder, open `hostname` file, and copy your node's ".onion" address
|
||||
* Start wownerod with the following parameters:
|
||||
|
||||
## Debugging
|
||||
|
||||
This section contains general instructions for debugging failed installs or problems encountered with Monero. First, ensure you are running the latest version built from the Github repo.
|
||||
|
||||
### Obtaining stack traces and core dumps on Unix systems
|
||||
|
||||
We generally use the tool `gdb` (GNU debugger) to provide stack trace functionality, and `ulimit` to provide core dumps in builds which crash or segfault.
|
||||
|
||||
* To use `gdb` in order to obtain a stack trace for a build that has stalled:
|
||||
|
||||
Run the build.
|
||||
|
||||
Once it stalls, enter the following command:
|
||||
|
||||
```bash
|
||||
gdb /path/to/monerod `pidof monerod`
|
||||
```
|
||||
|
||||
Type `thread apply all bt` within gdb in order to obtain the stack trace
|
||||
|
||||
* If however the core dumps or segfaults:
|
||||
|
||||
Enter `ulimit -c unlimited` on the command line to enable unlimited filesizes for core dumps
|
||||
|
||||
Enter `echo core | sudo tee /proc/sys/kernel/core_pattern` to stop cores from being hijacked by other tools
|
||||
|
||||
Run the build.
|
||||
|
||||
When it terminates with an output along the lines of "Segmentation fault (core dumped)", there should be a core dump file in the same directory as monerod. It may be named just `core`, or `core.xxxx` with numbers appended.
|
||||
|
||||
You can now analyse this core dump with `gdb` as follows:
|
||||
|
||||
```bash
|
||||
gdb /path/to/monerod /path/to/dumpfile`
|
||||
./wownerod --proxy tor,127.0.0.1:9150,25 --anonymous-inbound YOUR_NODE_ADDRESS.onion,127.0.0.1:44469,25 --add-peer wo5dkrgua62whkitjqmj6wzlp3hnth2w3lau2oj675rmaeexzy2q6cid.onion:44469
|
||||
```
|
||||
For more information, check out [ANONYMITY_NETWORKS](https://github.com/wownero/wownero/blob/master/ANONYMITY_NETWORKS.md).
|
||||
|
||||
Print the stack trace with `bt`
|
||||
## Wownero Graphical Wallets
|
||||
|
||||
#### To run monero within gdb:
|
||||
* [Wownero-Light-Wallet](https://github.com/wownero/Wownero-Light-Wallet)
|
||||
|
||||
Type `gdb /path/to/monerod`
|
||||
* [Wownerujo Android Wallet](https://github.com/wownero/wownerujo)
|
||||
|
||||
Pass command-line options with `--args` followed by the relevant arguments
|
||||
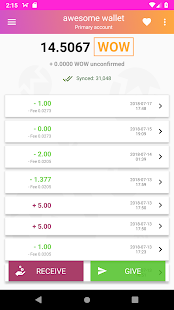
|
||||
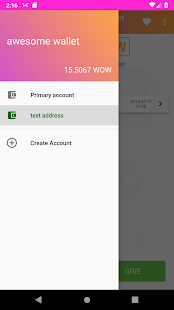
|
||||
|
||||
Type `run` to run monerod
|
||||
## Donating to Wownero Project
|
||||
|
||||
### Analysing memory corruption
|
||||
Developers are volunteers doing this mostly for shits and giggles. If you would like to support our shenanigans and stimulant addictions, please consider donating to [WFS proposals](https://funding.wownero.com/proposals) or the [dev slush fund](https://dev-funding.webui.wowkira.com).
|
||||
|
||||
There are two tools available:
|
||||
Donations may also be sent to:
|
||||
|
||||
#### ASAN
|
||||
XMR: `44SQVPGLufPasUcuUQSZiF5c9BFzjcP8ucDxzzFDgLf1VkCEFaidJ3u2AhSKMhPLKA3jc2iS8wQHFcaigM6fXmo6AnFRn5B`
|
||||
|
||||
Configure Monero with the -D SANITIZE=ON cmake flag, eg:
|
||||
|
||||
```bash
|
||||
cd build/debug && cmake -D SANITIZE=ON -D CMAKE_BUILD_TYPE=Debug ../..
|
||||
```
|
||||
|
||||
You can then run the monero tools normally. Performance will typically halve.
|
||||
|
||||
#### valgrind
|
||||
|
||||
Install valgrind and run as `valgrind /path/to/monerod`. It will be very slow.
|
||||
|
||||
### LMDB
|
||||
|
||||
Instructions for debugging suspected blockchain corruption as per @HYC
|
||||
|
||||
There is an `mdb_stat` command in the LMDB source that can print statistics about the database but it's not routinely built. This can be built with the following command:
|
||||
|
||||
```bash
|
||||
cd ~/monero/external/db_drivers/liblmdb && make
|
||||
```
|
||||
|
||||
The output of `mdb_stat -ea <path to blockchain dir>` will indicate inconsistencies in the blocks, block_heights and block_info table.
|
||||
|
||||
The output of `mdb_dump -s blocks <path to blockchain dir>` and `mdb_dump -s block_info <path to blockchain dir>` is useful for indicating whether blocks and block_info contain the same keys.
|
||||
|
||||
These records are dumped as hex data, where the first line is the key and the second line is the data.
|
||||
BTC: `bc1qcw9zglp3fxyl25zswemw7jczlqryms2lsmu464`
|
||||
|
||||
@@ -29,7 +29,7 @@
|
||||
# Parts of this file are originally copyright (c) 2012-2013 The Cryptonote developers
|
||||
|
||||
# Check what commit we're on
|
||||
execute_process(COMMAND "${GIT}" rev-parse --short HEAD RESULT_VARIABLE RET OUTPUT_VARIABLE COMMIT OUTPUT_STRIP_TRAILING_WHITESPACE)
|
||||
execute_process(COMMAND "${GIT}" rev-parse --short=9 HEAD RESULT_VARIABLE RET OUTPUT_VARIABLE COMMIT OUTPUT_STRIP_TRAILING_WHITESPACE)
|
||||
|
||||
if(RET)
|
||||
# Something went wrong, set the version tag to -unknown
|
||||
@@ -38,6 +38,7 @@ if(RET)
|
||||
set(VERSIONTAG "unknown")
|
||||
configure_file("src/version.cpp.in" "${TO}")
|
||||
else()
|
||||
string(SUBSTRING ${COMMIT} 0 9 COMMIT)
|
||||
message(STATUS "You are currently on commit ${COMMIT}")
|
||||
|
||||
# Get all the tags
|
||||
|
||||
@@ -1,8 +1,8 @@
|
||||
package=openssl
|
||||
$(package)_version=1.0.2q
|
||||
$(package)_version=1.0.2r
|
||||
$(package)_download_path=https://www.openssl.org/source
|
||||
$(package)_file_name=$(package)-$($(package)_version).tar.gz
|
||||
$(package)_sha256_hash=5744cfcbcec2b1b48629f7354203bc1e5e9b5466998bbccc5b5fcde3b18eb684
|
||||
$(package)_sha256_hash=ae51d08bba8a83958e894946f15303ff894d75c2b8bbd44a852b64e3fe11d0d6
|
||||
|
||||
define $(package)_set_vars
|
||||
$(package)_config_env=AR="$($(package)_ar)" RANLIB="$($(package)_ranlib)" CC="$($(package)_cc)"
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
packages:=boost openssl zeromq cppzmq expat ldns cppzmq readline libiconv hidapi protobuf libusb
|
||||
packages:=boost openssl zeromq cppzmq expat ldns readline libiconv hidapi protobuf libusb
|
||||
native_packages := native_ccache native_protobuf
|
||||
|
||||
darwin_native_packages = native_biplist native_ds_store native_mac_alias
|
||||
|
||||
@@ -8,6 +8,7 @@ OPTION(BUILD_TESTS "Build tests." OFF)
|
||||
|
||||
SET(STATIC ON)
|
||||
SET(UNBOUND_STATIC ON)
|
||||
SET(ARCH "default")
|
||||
|
||||
SET(BUILD_TESTS @build_tests@)
|
||||
SET(TREZOR_DEBUG @build_tests@)
|
||||
|
||||
38
contrib/epee/include/net/net_fwd.h
Normal file
38
contrib/epee/include/net/net_fwd.h
Normal file
@@ -0,0 +1,38 @@
|
||||
// Copyright (c) 2019, The Monero Project
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without modification, are
|
||||
// permitted provided that the following conditions are met:
|
||||
//
|
||||
// 1. Redistributions of source code must retain the above copyright notice, this list of
|
||||
// conditions and the following disclaimer.
|
||||
//
|
||||
// 2. Redistributions in binary form must reproduce the above copyright notice, this list
|
||||
// of conditions and the following disclaimer in the documentation and/or other
|
||||
// materials provided with the distribution.
|
||||
//
|
||||
// 3. Neither the name of the copyright holder nor the names of its contributors may be
|
||||
// used to endorse or promote products derived from this software without specific
|
||||
// prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY
|
||||
// EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
|
||||
// MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL
|
||||
// THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL,
|
||||
// SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
|
||||
// PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
|
||||
// INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT,
|
||||
// STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF
|
||||
// THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
#pragma once
|
||||
|
||||
namespace epee
|
||||
{
|
||||
namespace net_utils
|
||||
{
|
||||
struct ssl_authentication_t;
|
||||
class ssl_options_t;
|
||||
}
|
||||
}
|
||||
@@ -193,7 +193,6 @@ namespace net_utils
|
||||
return CONNECT_FAILURE;
|
||||
}
|
||||
}
|
||||
m_ssl_options.support = ssl_support_t::e_ssl_support_enabled;
|
||||
}
|
||||
return CONNECT_SUCCESS;
|
||||
}else
|
||||
@@ -223,7 +222,6 @@ namespace net_utils
|
||||
return false;
|
||||
if (m_ssl_options.support == epee::net_utils::ssl_support_t::e_ssl_support_autodetect)
|
||||
{
|
||||
m_ssl_options.support = epee::net_utils::ssl_support_t::e_ssl_support_enabled;
|
||||
if (try_connect_result == CONNECT_NO_SSL)
|
||||
{
|
||||
MERROR("SSL handshake failed on an autodetect connection, reconnecting without SSL");
|
||||
@@ -396,7 +394,7 @@ namespace net_utils
|
||||
if (!m_connected || !m_ssl_socket->next_layer().is_open())
|
||||
return false;
|
||||
if (ssl)
|
||||
*ssl = m_ssl_options.support == ssl_support_t::e_ssl_support_enabled;
|
||||
*ssl = m_ssl_options.support != ssl_support_t::e_ssl_support_disabled;
|
||||
return true;
|
||||
}
|
||||
|
||||
@@ -651,7 +649,7 @@ namespace net_utils
|
||||
bool write(const void* data, size_t sz, boost::system::error_code& ec)
|
||||
{
|
||||
bool success;
|
||||
if(m_ssl_options.support == ssl_support_t::e_ssl_support_enabled)
|
||||
if(m_ssl_options.support != ssl_support_t::e_ssl_support_disabled)
|
||||
success = boost::asio::write(*m_ssl_socket, boost::asio::buffer(data, sz), ec);
|
||||
else
|
||||
success = boost::asio::write(m_ssl_socket->next_layer(), boost::asio::buffer(data, sz), ec);
|
||||
@@ -660,7 +658,7 @@ namespace net_utils
|
||||
|
||||
void async_write(const void* data, size_t sz, boost::system::error_code& ec)
|
||||
{
|
||||
if(m_ssl_options.support == ssl_support_t::e_ssl_support_enabled)
|
||||
if(m_ssl_options.support != ssl_support_t::e_ssl_support_disabled)
|
||||
boost::asio::async_write(*m_ssl_socket, boost::asio::buffer(data, sz), boost::lambda::var(ec) = boost::lambda::_1);
|
||||
else
|
||||
boost::asio::async_write(m_ssl_socket->next_layer(), boost::asio::buffer(data, sz), boost::lambda::var(ec) = boost::lambda::_1);
|
||||
@@ -668,7 +666,7 @@ namespace net_utils
|
||||
|
||||
void async_read(char* buff, size_t sz, boost::asio::detail::transfer_at_least_t transfer_at_least, handler_obj& hndlr)
|
||||
{
|
||||
if(m_ssl_options.support != ssl_support_t::e_ssl_support_enabled)
|
||||
if(m_ssl_options.support == ssl_support_t::e_ssl_support_disabled)
|
||||
boost::asio::async_read(m_ssl_socket->next_layer(), boost::asio::buffer(buff, sz), transfer_at_least, hndlr);
|
||||
else
|
||||
boost::asio::async_read(*m_ssl_socket, boost::asio::buffer(buff, sz), transfer_at_least, hndlr);
|
||||
|
||||
@@ -294,6 +294,11 @@ namespace net_utils
|
||||
m_max_speed_up(0)
|
||||
{}
|
||||
|
||||
connection_context_base(const connection_context_base& a): connection_context_base()
|
||||
{
|
||||
set_details(a.m_connection_id, a.m_remote_address, a.m_is_income, a.m_ssl);
|
||||
}
|
||||
|
||||
connection_context_base& operator=(const connection_context_base& a)
|
||||
{
|
||||
set_details(a.m_connection_id, a.m_remote_address, a.m_is_income, a.m_ssl);
|
||||
|
||||
@@ -129,6 +129,7 @@ script: |
|
||||
chmod +x ${WRAP_DIR}/${prog}
|
||||
done
|
||||
|
||||
git config --global core.abbrev 9
|
||||
cd monero
|
||||
BASEPREFIX=`pwd`/contrib/depends
|
||||
# Build dependencies for each host
|
||||
@@ -153,7 +154,7 @@ script: |
|
||||
export PATH=${BASEPREFIX}/${i}/native/bin:${ORIGPATH}
|
||||
mkdir build && cd build
|
||||
cmake .. -DCMAKE_TOOLCHAIN_FILE=${BASEPREFIX}/${i}/share/toolchain.cmake -DBACKCOMPAT=ON
|
||||
make
|
||||
make ${MAKEOPTS}
|
||||
DISTNAME=monero-${i}
|
||||
mv bin ${DISTNAME}
|
||||
find ${DISTNAME}/ | sort | tar --no-recursion --mode='u+rw,go+r-w,a+X' --owner=0 --group=0 -c -T - | gzip -9n > ${OUTDIR}/${DISTNAME}.tar.gz
|
||||
|
||||
@@ -77,6 +77,7 @@ script: |
|
||||
create_per-host_faketime_wrappers "2000-01-01 12:00:00"
|
||||
export PATH=${WRAP_DIR}:${PATH}
|
||||
|
||||
git config --global core.abbrev 9
|
||||
cd monero
|
||||
BASEPREFIX=`pwd`/contrib/depends
|
||||
|
||||
@@ -100,7 +101,7 @@ script: |
|
||||
export PATH=${BASEPREFIX}/${i}/native/bin:${ORIGPATH}
|
||||
mkdir build && cd build
|
||||
cmake .. -DCMAKE_TOOLCHAIN_FILE=${BASEPREFIX}/${i}/share/toolchain.cmake
|
||||
make
|
||||
make ${MAKEOPTS}
|
||||
DISTNAME=monero-${i}
|
||||
mv bin ${DISTNAME}
|
||||
find ${DISTNAME}/ | sort | tar --no-recursion --mode='u+rw,go+r-w,a+X' --owner=0 --group=0 -c -T - | gzip -9n > ${OUTDIR}/${DISTNAME}.tar.gz
|
||||
|
||||
@@ -100,6 +100,7 @@ script: |
|
||||
create_per-host_linker_wrapper "2000-01-01 12:00:00"
|
||||
export PATH=${WRAP_DIR}:${PATH}
|
||||
|
||||
git config --global core.abbrev 9
|
||||
cd monero
|
||||
BASEPREFIX=`pwd`/contrib/depends
|
||||
# Build dependencies for each host
|
||||
@@ -125,7 +126,7 @@ script: |
|
||||
export PATH=${BASEPREFIX}/${i}/native/bin:${ORIGPATH}
|
||||
mkdir build && cd build
|
||||
cmake .. -DCMAKE_TOOLCHAIN_FILE=${BASEPREFIX}/${i}/share/toolchain.cmake
|
||||
make
|
||||
make ${MAKEOPTS}
|
||||
DISTNAME=monero-${i}
|
||||
mv bin ${DISTNAME}
|
||||
find ${DISTNAME}/ | sort | zip -X@ ${OUTDIR}/${DISTNAME}.zip
|
||||
|
||||
@@ -1,8 +0,0 @@
|
||||
#!/bin/sh
|
||||
|
||||
if [ ! -d "$SNAP_USER_DATA/etc" ]; then
|
||||
mkdir $SNAP_USER_DATA/etc/
|
||||
cp -R $SNAP/etc/monerod.conf $SNAP_USER_DATA/etc/monerod.conf
|
||||
fi
|
||||
|
||||
exec "$SNAP/bin/monerod" "$@"
|
||||
Binary file not shown.
|
Before Width: | Height: | Size: 1.5 KiB After Width: | Height: | Size: 18 KiB |
@@ -1,31 +1,29 @@
|
||||
name: monero
|
||||
version: 0.11.1.0-1
|
||||
summary: "Monero: the secure, private, untraceable cryptocurrency https://getmonero.org"
|
||||
name: wownero
|
||||
version: 0.5.0.0
|
||||
summary: "Wownero: the secure, private, untraceable cryptocurrency http://wownero.org"
|
||||
description: |
|
||||
Monero is a private, secure, untraceable, decentralised digital currency.
|
||||
You are your bank, you control your funds, and nobody can trace your transfers
|
||||
unless you allow them to do so.
|
||||
Wownero: a fairly launched privacy-centric meme coin with no premine and a finite supply.
|
||||
grade: devel
|
||||
confinement: strict
|
||||
|
||||
apps:
|
||||
monerod:
|
||||
wownerod:
|
||||
daemon: forking
|
||||
command: |
|
||||
monerod-wrapper --detach --data-dir ${SNAP_COMMON} --config-file ${SNAP_USER_DATA}/etc/monerod.conf
|
||||
wownerod-wrapper --detach --data-dir ${SNAP_COMMON} --config-file ${SNAP_USER_DATA}/etc/wownerod.conf
|
||||
plugs:
|
||||
- network
|
||||
- network-bind
|
||||
monero-wallet-rpc:
|
||||
wownero-wallet-rpc:
|
||||
command: |
|
||||
monero-wallet-rpc --log-file ${SNAP_USER_DATA}
|
||||
wownero-wallet-rpc --log-file ${SNAP_USER_DATA}
|
||||
plugs:
|
||||
- home
|
||||
- network
|
||||
- network-bind
|
||||
monero-wallet-cli:
|
||||
wownero-wallet-cli:
|
||||
command: |
|
||||
monero-wallet-cli --log-file ${SNAP_USER_DATA}
|
||||
wownero-wallet-cli --log-file ${SNAP_USER_DATA}
|
||||
plugs:
|
||||
- home
|
||||
- network
|
||||
@@ -71,8 +69,8 @@ parts:
|
||||
plugin: dump
|
||||
source: .
|
||||
organize:
|
||||
contrib/snap/monerod.conf: etc/monerod.conf
|
||||
contrib/snap/monerod-wrapper: bin/monerod-wrapper
|
||||
contrib/snap/wownerod.conf: etc/wownerod.conf
|
||||
contrib/snap/wownerod-wrapper: bin/wownerod-wrapper
|
||||
prime:
|
||||
- etc
|
||||
- bin
|
||||
|
||||
8
contrib/snap/wownerod-wrapper
Executable file
8
contrib/snap/wownerod-wrapper
Executable file
@@ -0,0 +1,8 @@
|
||||
#!/bin/sh
|
||||
|
||||
if [ ! -d "$SNAP_USER_DATA/etc" ]; then
|
||||
mkdir $SNAP_USER_DATA/etc/
|
||||
cp -R $SNAP/etc/wownerod.conf $SNAP_USER_DATA/etc/wownerod.conf
|
||||
fi
|
||||
|
||||
exec "$SNAP/bin/wownerod" "$@"
|
||||
@@ -4,7 +4,7 @@
|
||||
# See 'monerod --help' for all available options.
|
||||
|
||||
# Overridden by snap:
|
||||
# data-dir=/var/lib/monero
|
||||
# log-file=/var/log/monero/monero.log
|
||||
# data-dir=/var/lib/wownero
|
||||
# log-file=/var/log/wownero/wownero.log
|
||||
|
||||
log-level=0
|
||||
49
external/CMakeLists.txt
vendored
49
external/CMakeLists.txt
vendored
@@ -34,22 +34,42 @@
|
||||
# We always compile if we are building statically to reduce static dependency issues...
|
||||
# ...except for FreeBSD, because FreeBSD is a special case that doesn't play well with
|
||||
# others.
|
||||
|
||||
find_package(Miniupnpc REQUIRED)
|
||||
|
||||
message(STATUS "Using in-tree miniupnpc")
|
||||
add_subdirectory(miniupnp/miniupnpc)
|
||||
set_property(TARGET libminiupnpc-static PROPERTY FOLDER "external")
|
||||
if(MSVC)
|
||||
set_property(TARGET libminiupnpc-static APPEND_STRING PROPERTY COMPILE_FLAGS " -wd4244 -wd4267")
|
||||
elseif(NOT MSVC)
|
||||
set_property(TARGET libminiupnpc-static APPEND_STRING PROPERTY COMPILE_FLAGS " -Wno-undef -Wno-unused-result -Wno-unused-value")
|
||||
endif()
|
||||
if(CMAKE_SYSTEM_NAME MATCHES "NetBSD")
|
||||
set_property(TARGET libminiupnpc-static APPEND_STRING PROPERTY COMPILE_FLAGS " -D_NETBSD_SOURCE")
|
||||
if(NOT IOS)
|
||||
find_package(Miniupnpc QUIET)
|
||||
endif()
|
||||
|
||||
set(UPNP_LIBRARIES "libminiupnpc-static" PARENT_SCOPE)
|
||||
# If we have the correct shared version and we're not building static, use it
|
||||
if(STATIC OR IOS)
|
||||
set(USE_SHARED_MINIUPNPC false)
|
||||
elseif(MINIUPNP_FOUND AND MINIUPNPC_VERSION_1_7_OR_HIGHER)
|
||||
set(USE_SHARED_MINIUPNPC true)
|
||||
endif()
|
||||
|
||||
if(USE_SHARED_MINIUPNPC)
|
||||
message(STATUS "Using shared miniupnpc found at ${MINIUPNP_INCLUDE_DIR}")
|
||||
|
||||
set(UPNP_STATIC false PARENT_SCOPE)
|
||||
set(UPNP_INCLUDE ${MINIUPNP_INCLUDE_DIR} PARENT_SCOPE)
|
||||
set(UPNP_LIBRARIES ${MINIUPNP_LIBRARY} PARENT_SCOPE)
|
||||
else()
|
||||
if(STATIC)
|
||||
message(STATUS "Using miniupnpc from local source tree for static build")
|
||||
else()
|
||||
message(STATUS "Using miniupnpc from local source tree (/external/miniupnp/miniupnpc)")
|
||||
endif()
|
||||
|
||||
add_subdirectory(miniupnp/miniupnpc)
|
||||
|
||||
set_property(TARGET libminiupnpc-static PROPERTY FOLDER "external")
|
||||
if(MSVC)
|
||||
set_property(TARGET libminiupnpc-static APPEND_STRING PROPERTY COMPILE_FLAGS " -wd4244 -wd4267")
|
||||
elseif(NOT MSVC)
|
||||
set_property(TARGET libminiupnpc-static APPEND_STRING PROPERTY COMPILE_FLAGS " -Wno-undef -Wno-unused-result -Wno-unused-value")
|
||||
endif()
|
||||
|
||||
set(UPNP_STATIC true PARENT_SCOPE)
|
||||
set(UPNP_LIBRARIES "libminiupnpc-static" PARENT_SCOPE)
|
||||
endif()
|
||||
|
||||
find_package(Unbound)
|
||||
|
||||
@@ -80,3 +100,4 @@ endif()
|
||||
|
||||
add_subdirectory(db_drivers)
|
||||
add_subdirectory(easylogging++)
|
||||
add_subdirectory(randomwow)
|
||||
|
||||
2
external/miniupnp
vendored
2
external/miniupnp
vendored
Submodule external/miniupnp updated: 6b9b73a567...4c700e0952
1
external/randomwow
vendored
Submodule
1
external/randomwow
vendored
Submodule
Submodule external/randomwow added at fd74b8092f
@@ -127,14 +127,14 @@ endif()
|
||||
add_subdirectory(cryptonote_protocol)
|
||||
if(NOT IOS)
|
||||
add_subdirectory(simplewallet)
|
||||
add_subdirectory(gen_multisig)
|
||||
add_subdirectory(daemonizer)
|
||||
add_subdirectory(daemon)
|
||||
add_subdirectory(blockchain_utilities)
|
||||
endif()
|
||||
|
||||
if(CMAKE_BUILD_TYPE STREQUAL Debug)
|
||||
add_subdirectory(debug_utilities)
|
||||
add_subdirectory(blockchain_utilities)
|
||||
add_subdirectory(gen_multisig)
|
||||
endif()
|
||||
|
||||
if(PER_BLOCK_CHECKPOINT)
|
||||
|
||||
@@ -394,582 +394,7 @@ void BlockchainDB::fixup()
|
||||
LOG_PRINT_L1("Database is opened read only - skipping fixup check");
|
||||
return;
|
||||
}
|
||||
|
||||
// There was a bug that would cause key images for transactions without
|
||||
// any outputs to not be added to the spent key image set. There are two
|
||||
// instances of such transactions, in blocks 202612 and 685498.
|
||||
// The key images below are those from the inputs in those transactions.
|
||||
// On testnet, there are no such transactions
|
||||
// See commit 533acc30eda7792c802ea8b6417917fa99b8bc2b for the fix
|
||||
static const char * const mainnet_genesis_hex = "418015bb9ae982a1975da7d79277c2705727a56894ba0fb246adaabb1f4632e3";
|
||||
crypto::hash mainnet_genesis_hash;
|
||||
epee::string_tools::hex_to_pod(mainnet_genesis_hex, mainnet_genesis_hash );
|
||||
set_batch_transactions(true);
|
||||
batch_start();
|
||||
|
||||
if (get_block_hash_from_height(0) == mainnet_genesis_hash)
|
||||
{
|
||||
// block 202612 (511 key images in 511 transactions)
|
||||
static const char * const key_images_202612[] =
|
||||
{
|
||||
"51fc647fb27439fbb3672197d2068e4110391edf80d822f58607bd5757cba7f3",
|
||||
"d8cf1c1bd41f13c4553186e130e6e2c1cd80135ddb418f350088926997a95ca9",
|
||||
"95d2556c8acd1457dce7bfd9c83b1d82b821a55a9c9588b04b7b5cf562a65949",
|
||||
"4b5d987fee1bb563a162d23e41741ad73560c003e26a09b6655f09496538daac",
|
||||
"1d25ea86323d1578579d3894a54b99ea1c3e2dca547c6726c44aef67db958b02",
|
||||
"92e46fb70be5d9df39ca83c4fc6ae26c594118314bb75502a9c9752a781d0b33",
|
||||
"924d0cb9060d429be7e59d164a0f80a4dabc3607d44401b26fb93e7182ab435d",
|
||||
"f63e4a23fec860fd4c3734623891330ac1ff5af251e83a0e6247287818b8a72f",
|
||||
"5b14c5ef13738d015619b61dacefc2ade3660d25b35ef96330a8f4e2afc26526",
|
||||
"d5016b012a2fb6ca23fd56ece544d847962264b4aee15efe1465805fd824a8fb",
|
||||
"0a7f3da1d9dd341cd96829e484b07163099763ac7bd60603b7ee14f7dbcb278d",
|
||||
"d716c03d7447d2b693f6f61b6ad36bd57344033fc1a11feaf60d569f40014530",
|
||||
"23154a812e99ce226f6a87087e0812f419aed51289f1c0c359b0b61303b53a36",
|
||||
"03940341e1a99d5b0c68eacfdf5a20df90d7d0a3d6089d39709cdd964490755c",
|
||||
"ef09648814cfe071f5d8e9cfde57247ad09409265c4b6c84697bbb046809bd7e",
|
||||
"8843ec52b0496ca4e895813cfe00bb18ea777d3618e9bd2e200287e888e2f5c7",
|
||||
"8558bf39baf3df62b5d33cdf97163a365e6c44f4d6deef920730b4982b66449f",
|
||||
"504d9380ce581de0af97d5800d5ca9e61d78df368907151ab1e567eb6445332a",
|
||||
"673797763593c23b3ee07b43bd8760365e2c251a8a60a275528ff34a477110cc",
|
||||
"25178c95e4d402c58d79c160d2c52dd3c45db2c78e6aaa8d24d35c64f19d4957",
|
||||
"407c3a05dcc8bdcb0446b5d562cf05b4536fc7337344765215130d5f1e7ee906",
|
||||
"4e7fa771a5455d8ee8295f01181a360cdc6467cc185c2834c7daf9fbf85b6f1d",
|
||||
"6beb64cb024f9c5c988f942177fc9c1ec5ecfa85b7db0f13a17f9f98e8e46fe7",
|
||||
"6406bfc4e486e64c889ea15577d66e5835c65c6a39ec081af8ac5acdc153b4b5",
|
||||
"1b1da638709f9f85898af70ffaa5b88d5a4c9f2663ca92113c400ab25caf553c",
|
||||
"da49407a9e1ed27abd28076a647177157c42517e2542e9b6a4921fdadf4e8742",
|
||||
"3c3fdba2a792fddaeb033605163991a09933e8f05c6c934d718e50a613b64d69",
|
||||
"82c60429171173739fa67c4807cab359620299e6ed2a9da80139b5b1e23c5456",
|
||||
"0a19e5767e1381ac16f57cfa5aabd8463551d19f069f7f3465c11a8583253f3e",
|
||||
"d0fae6ffdd4818399eae6224978f170f696150eaf699f2f218abc00c68530f96",
|
||||
"0937889aeb3af5c64608d9a9f88229a068e53417448f00f9aa5e28c570cca8f8",
|
||||
"d6072d269753020912524961ce8c6930cf35abe5c4b2bdc7fd678338d20a68fb",
|
||||
"0e8bc9b06fcc842bdaa7df029bfd1f252d5defc014d58a006c10ab678ecf543f",
|
||||
"9d42f90520f02c9258be53b123d69ddbce5f33f92a903d3fb4cf3358ff0e07b5",
|
||||
"1cc05416b12cbe719617158773c3e6173435fc64e1ee44310dc696baecaeaa95",
|
||||
"266b15222913c11ef6403ee15dc42c8c0e16bc5fa2f49110447802236e045797",
|
||||
"791b123af3b71ac9497a010610f72207ff8ec642969b5cf0d2891b21e7eee562",
|
||||
"946d4d7b084dc32495f22b35fc30394144c8e0ba04f3ad6e2c2bfb0173a2266d",
|
||||
"2c015cb990c1583228d08b2d5de9227b950c3f57364fc1033bca5c0fbfd08c58",
|
||||
"13fdc41862fd85507f579c69accb9cc6a40f5971bfa41e3caff598a3dcffd2fc",
|
||||
"64b06d9874a83917c583c9439d1c736083377d67fda2961b623f7124663134c3",
|
||||
"2fa49cd19e0aa02989991a4c3760f44be800fe8fb4d58b23aca382e10dc0d2d6",
|
||||
"377628f265f799772e9fb6065be8b6eee200c329f729fe36c25ee179e4d20df9",
|
||||
"ba94fa79134ce383b6a98b04dc6ad3d1b950e410d50a292bc770f9685e59fe91",
|
||||
"875c924329f0733e31fe8d8aed70dc1906335b8a9984932b6368ea24edb39765",
|
||||
"f31f4abb3f5ee42a5aae86d70b3bd9a9c1934933641893864dd333f89719d608",
|
||||
"2bcd629e125514a780f568d3c2e8b12a2e7fbbee06e652bbeed3e7825508e31c",
|
||||
"918b43581163ca1963de21bb9ac401756e75c3f00ac8dcfafc139f1ad5d7d998",
|
||||
"5730dd57fa52749a0d6502b11c9d802ac495875542431310c674a65655b7c2a3",
|
||||
"03f84b990683e569e2f6143bb963a2a8de411e7c4b7923117b94c7afcb4b43ea",
|
||||
"b298c8510d35bd2be0ff0753ad7d98d480f4c6490bb67fb93cd4632ea726e8a7",
|
||||
"0a771afbf9be104c01b89eaeb57073297d35ac8fbbcc0816820fdb9a29d26625",
|
||||
"713d90d6ca1be1a4e05a5f8441dc528c699caa09eda49c09072f5f8291354c2e",
|
||||
"988827f45c19330d9404309f63d536a447803cca7cb182ef005b074def09ab7d",
|
||||
"9dcaa105b4def895f3faee704c250bdc924316f153cb972f3fb565beec0b7942",
|
||||
"1c06c30afe65b59e9e22d6bb454e4209a03efe53cdbf27b3945d5d75b1b90427",
|
||||
"49e08c13d1da209ec1aea7b7fbe0daa648e30febeb2aa5ffbaaabdd71a278ac2",
|
||||
"e1c2e49ab7b829854c46a64772ded35459908e0f563edbcf5c612913b7767046",
|
||||
"e08bb7d133490ca85a6325d46807170cd07618b6a5f6e1d069e44890cc366fab",
|
||||
"5c73ca0691cde2f35b7933d6db33f0b642ec70d0bd3f2b0ebbd97754ca67e248",
|
||||
"6404399151872a521dae767311712225dba65d810ba2feba209204221b5d772d",
|
||||
"4a0c3aa6cef36f44edf08ad8fb1533d7e1186e317da8a3afb3d81af072043233",
|
||||
"104b3e1af37cf10b663a7ec8452ea882082018c4d5be4cd49e7f532e2fea64e5",
|
||||
"e723a46bf9684b4476c3005eb5c26511c58b7eb3c708ddf7470ee30a40834b32",
|
||||
"18e6f0fa3aa779a73ceefabea27bff3202003fd2c558ec5f5d07920528947d57",
|
||||
"c97e73eb593ff39e63307220796cc64974c0c8adac860a2559ab47c49bc0c860",
|
||||
"13c363a962955b00db6d5a68b8307cd900ae9202d9b2deb357b8d433545244ac",
|
||||
"76a488865151fab977d3639bac6cba4ba9b52aa17d28ac3580775ed0bff393e4",
|
||||
"a14de587c9f4cd50bb470ecffd10026de97b9b5e327168a0a8906891d39d4319",
|
||||
"b1d38ee1c4ca8ae2754a719706e6f71865e8c512310061b8d26438fedf78707e",
|
||||
"772bb8a3f74be96fa84be5fa8f9a8ef355e2df54869c2e8ae6ad2bf54ed5057e",
|
||||
"3083a7011da36be63e3f7cacd70ab52e364dd58783302f1cb07535a66b5735f5",
|
||||
"2b1d892e3002aa3201deb4ffe28c0c43b75b8f30c96b5d43f6d5829049ecbd94",
|
||||
"cb738aabe44c6fb17ade284bf27db0169e309bf8cf9c91c4e4e62856619a4c64",
|
||||
"1707e04b792f4953f460f217b9bb94c84cef60736a749fb01277cfe0eaaa48c7",
|
||||
"ab8b6bac9b8a4f00b78acb4bd50ed2758e0fa100964b6f298d2a943eb2af2b30",
|
||||
"dd317193fef72490f3be01293b29e9c2f94eda10824a76ca74bf39dd7cb40ab2",
|
||||
"4fb3d995b087af7517fcb79e71f43bac0c4fbda64d89417a40ca4a708f2e8bc1",
|
||||
"549ba38c31bf926b2cb7e8f7f15d15df6388dce477a3aff0245caa44606849fc",
|
||||
"7585c14ab9abbffb89d0fa9f00c78ecae9f7c9062e5d4f1fae8453b3951fc60b",
|
||||
"953f855323f72461b7167e3df0f4fd746a06f5a7f98aa42acdce2eef822a0b2f",
|
||||
"0931932d57dde94dcfb017179a5a0954b7d671422149738260a365ca44f50eb8",
|
||||
"a3d179d16a4a275a3bb0f260cee9284db243abad637a9dbe92d02940f1c7ee8c",
|
||||
"959843f1e76ff0785dafe312c2ea66380fdc32b9d6180920f05f874c74599a80",
|
||||
"fbc36b3e1718fe6c338968b04caa01a7adb315d206abc63e56768d69e008a65d",
|
||||
"f054de7eac5e2ea48072e7fb4db93594c5f5d2dfa0afe8266042b6adc80dfdca",
|
||||
"39dfc68dc6ba8c457b2995562c867cef2f2cf994e8d6776a6b20869e25053f70",
|
||||
"19ad7ca7629758c22ac83643605c8a32a6665bae8e35dbc9b4ad90343756ebb3",
|
||||
"e89e80ea5c64cf7840f614f26e35a12c9c3091fa873e63b298835d9eda31a9ea",
|
||||
"572c1b9a83c947f62331b83009cc2ec9e62eab7260b49929388e6500c45cd917",
|
||||
"df0b21f679e6c0bf97f7b874e9f07c93c3467b092f3d9e1484e5646fda6eca5f",
|
||||
"8f3b7c0f4b403af62fe83d3cfac3f1e2572af8afa4cea3f3e2e04291efe84cf6",
|
||||
"aae8b8db243009d021d8c9897d52ee8125a17212f0a8b85f681ad8950ae45f0e",
|
||||
"3d45a4957d27447dea83d9ae2ef392a3a86619bfcf8dda2db405a7b304997797",
|
||||
"a5b0a619a8e3030b691bdba1ed951cd54e4bc2063602eae26d9791fb18e60301",
|
||||
"14650df217dd64a2905cd058114e761502dff37d40e80789200bc53af29b265f",
|
||||
"fd6a245ab5e4e6e18d7ba9b37478ce38248f0ab864e5511d2208ae3d25017e5f",
|
||||
"fbe0be6dd42a11feb5db5ae56fcbbac41041ab04a35f1df075580e960c8eeab0",
|
||||
"72f3f1213d9bec92ba9705b447d99cd0a6a446e37a3c1c50bb8ece1090bfe56e",
|
||||
"20df836554e1534f62b2a6df9ce58e11c1b9b4746ce8ee3c462300a8c01f5e76",
|
||||
"5c3d2a81b7331c86420ad32b6e9a212b73b1c3413724a0f91bf073eba18e2f1f",
|
||||
"63264ddfb29cd36fc18f3ee6614c4101ba7229bc5ac375f912590d3f0df982f4",
|
||||
"5ec4eb637761c1c9dbc6aa6649d4410508ef8d25d61ad6caa40c6ee3236d5515",
|
||||
"270c70940536017915e1cdbc003de7279ec1c94cba1ef6130f4236f7e306e4f0",
|
||||
"c1d1d57a7c03f6ddeeab5230a4910db8355e2143f473dea6e1d57c2f8d882b76",
|
||||
"218c030a7fdc9917e9f87e2921e258d34d7740a68b5bee48a392b8a2acf1f347",
|
||||
"ac47861c01c89ea64abee14cf6e1f317859ed56b69ae66377dc63e6575b7b1eb",
|
||||
"23bf549c8a03f9870983c8098e974308ec362354b0dcf636c242a88f24fc2718",
|
||||
"a3ce8b817e5212c851c6b95e693849a396c79b0d04b2a554de9b78933fbea2b7",
|
||||
"7310120c1cc1961b0d3fce13743c8a7075ae426fe6cccaf83600f24cee106236",
|
||||
"8fa0630f193777dcc4f5eccd1ad9ceacf80acdf65e52e4e01bf3a2b2fdd0dac6",
|
||||
"4a5f5c87f67d573d0673f01abaebc26eaa62e6d04627588549cc9e6c142dc994",
|
||||
"78971cccacc645116f9d380c167f955d54b386a22af112233f7de004fc0c8316",
|
||||
"badc67216868e1de1bbe044bf0e6070e6ee0353d05c13fa0c43b1897db5219a2",
|
||||
"c45b2a168bc51cbb615a79f97432cc4bb6b104da9cdc1fc640c930657452f71b",
|
||||
"c17eda13541d14554c5db542155b08b6bf9cb403d425745b662ebc2b2b9b3a3b",
|
||||
"313210cd9d2efc1603f07859bae7bd5fb5914f4a631b943f2f6ff5927a4e681a",
|
||||
"6ee94ec8af4e6828f9b46c590ea55da640ef50e810a247d3e8cdf4b91c42d2c2",
|
||||
"505b7a4d9f1ba6577aa2a941843f86c205b23b1ea21035925e587022e2f0aeed",
|
||||
"98e6a7cd687e8192e300a8202999ec31ad57bc34f656f2ae90d148607ff6d29f",
|
||||
"1be5db002c0a446cc2c1da363e5d08ae045cd8f5e76c8cccd65d5166393c0bdf",
|
||||
"17c02ac6d390c5c735e1e873c40294220e89071fca08a5da396a131fa1ba8670",
|
||||
"2540507c39ae6fdcd90de826077f0ca390da126166a25c15c048a60606a27367",
|
||||
"5ab9328e525c7a017ef4f591d995ad4595d74cbf8ff4112af33b08c70661a304",
|
||||
"9c105587a96c51d81422f64e46016564d22329760648c95dcac7218f3733f915",
|
||||
"525afb1b94a75f1edc2b55c700071e14a2166acda003370047c30dba8ea80278",
|
||||
"745d4a5d9f95ca4efa6261b6bcd4ecacd504b5b901a2ce1353c522a5c0c15dcc",
|
||||
"5a5a568cd87ba34252ba254e6a320e1a7f52f13e7451bb887efb34ff881785f2",
|
||||
"1ec50a80198cd830b51f4f7a0222015a268d9b40f04e7f838c7b8dc7abf63b01",
|
||||
"68836b662d79349cb42f5cef54e6a066157d398cc87d3b13f29fc04e5cf364a5",
|
||||
"658db317f355a9cbd86f673775cac0c308fe14967428fd283a36e300a6a53b2f",
|
||||
"677d79a8c467dd9db38f0ef45c2787dd368f701a6b47bf7a5f06112c38da643e",
|
||||
"2baa455d4066f5d628f9ecd315cb57deca71069db5d0d112ae0aa18a84b6f0d7",
|
||||
"5e7b0889f351560081360ac2b1429b48b2f7d886227f144e3b198e2f1fa56ed9",
|
||||
"c3d317fbf26e15add8b4f8f93df9de9b22297b8e4945ebab9ee249d4f72f4e45",
|
||||
"3c0b705a5c1e31abc7e46d8ff3c148a033f6875454cfb67f8d2a2b9a57a5ba7e",
|
||||
"a0ab74663561af2adc2d38be3569fbe7aa2454346416ac96e5eb26b1e01b1e2f",
|
||||
"53526cffdb74327670566c1dacacffb7d30a43a7f1862ff8bab87737bfa5edb6",
|
||||
"24c5d36ab98d88f87b2c71afb4ea8562e05c7aa0b50f3bc0f9ed50a4cd52989b",
|
||||
"c3ce4de5f94dff65d11e33a865855a4404259cf45263914c884f79db4f35169d",
|
||||
"f1009b6dcf30030cff872d636fb96ed233eb6ecb8ffed003c7da64e4f5a02f4c",
|
||||
"e3729f58614d3b42450d1599d863983ab7e3e5c29fb57aad7958c8923a2627c4",
|
||||
"31cf4792f7b5ce01b217ec80184edd2a7c49c0b21701f5494ee2c9bac67c28ca",
|
||||
"b42a5c9c92a656c5bb2b759ce160fdfd245243aeb1786338faea63b62e9a60ce",
|
||||
"a1efc8d5d0855933d5ac8fe5960c7acacb92fcb09bfbc929e5002f168251e648",
|
||||
"c4322c7f3682ec94b0dcb42f13b498c36cf575d505aacc8ec8bf67a6a2abf4c9",
|
||||
"684ee5aa3c98357aeaddcc30c6620939b52aeef729e24b4a46ccafc44f24d831",
|
||||
"36180f2ae11d105e0efbfbddb94e6b45b08609a383e4e1a8fa3b06d7a8051de9",
|
||||
"96c2d183eacc87581a0b17b8d07878bc10d436728510715109a7565d9972f8b5",
|
||||
"3068c9d04d561c7e29e3f621280b61a61885de0e9ec35a66a3116ca7a9e09627",
|
||||
"2eb94b9673ad6f8f88288fddfceae4baaeccb37bed88a35611d826ba06a5363b",
|
||||
"fc8cd5fae8b81121001f7767dcd5f185c0fdcc88cce1fbb184ddbcfad697ba54",
|
||||
"51521da1ecedea6d588d774eb155d936b32a14913c2f11d989bcc5116e65bf41",
|
||||
"3d23542e597a83dd6307700d79058b920f281c65f832333734d8a0adec510495",
|
||||
"11d2e01913ff0d4bd21970d709d88e63289492c0bbad7bff99c0d36858a841ca",
|
||||
"de674f1eee3068d2bc8c2f2897d8556e5deb872869652f7d3a4e5dbc6f1063c8",
|
||||
"e722d7f728526110c0921791b417afde4af1e87ae48ccc01911786197843104b",
|
||||
"aaba3a4e2a7d20ab76edfbcccefc27acfd509db3638582c28230e73ffd71d340",
|
||||
"1385a7209dafb9622dd4274179832e40c7fae19445383c34ef79adb0e4de0c98",
|
||||
"108408531fca288d74de4a2c596eab8569e355d9ab2f8380f4d24073a6b3fa95",
|
||||
"294476a86fcd39351ae452cdb8af9584067ec4501ec6182d0062bb154559fed3",
|
||||
"e64b175e0284c5cb69c8db46344ed43b5ced8abfe3cbf0c197103cfd116944cd",
|
||||
"cdd73a0f1fa7c14ed2177ae2163035333718847e49dd5cca6775bd20fc7553ad",
|
||||
"d423d2a374bc66a4587a5e3affa327ca75b8116051320759a3b88a868a7b80d4",
|
||||
"f13ad1e5b1315557d5497b58516eb3b0759d909725ddd0eb8a0dee439c6c0a48",
|
||||
"3a600b547a6061186a54e491344fd50cc7d4f0566a386a40aba6545254773728",
|
||||
"37a6f3f221fe17cc04a65aa544d5135e8297ecaf0853ba784dffacb74feb481b",
|
||||
"0ca42d67d0f84b28861d63e919e6ce5ad527447fdc53a03d8497a0241bee9376",
|
||||
"c7dbda42459e6fadb92c416eaef3e04674fc57915a93f3be4e656634c9654075",
|
||||
"0e34d728ae4fe347a5afecdf886fbd4d48a65c5d0dfab807da6ae95b6b2d7a3a",
|
||||
"f1bc69257ed510db5b2ed370010b037f452a29c49e36337264b3011ce2516216",
|
||||
"33f98f6b8a8e202463955998fba3b790199daa893e5471554826cfd9daa5c02f",
|
||||
"f8a0a37a2c9ebd7022d7cded1ee0318fd363020070b4cdaea800e44dcc1300d2",
|
||||
"6862714daedb908a4d86a3a3f1e65ec2c29ae61501b4ddcaf184243dd095d71b",
|
||||
"555cd19a6d21941c1174129b8bbcc70edcf0d6874262ce9e1e542351990d523d",
|
||||
"2cd6b44326828f23a2aa33699754bfa072c4883f39d53616f6a6b74149b664b6",
|
||||
"127f45d2eacb565c21c1030fe8054fd0a3a75705bc368924712aa145d414fa47",
|
||||
"19225e2dae6e1166f21cdab1290194470ded09df9b66f3faad3c1cc9ebcf340f",
|
||||
"b7b3f53f0539b2b4837b8bb9dae0ccbd200c8d36126d9f50199d68a4293a46d3",
|
||||
"6b6323be01f27d6d759d9670825e8ebb9c4cd8016351702328df91cef36cfec8",
|
||||
"020c31cfdfc5b22b10235745b89b311d271cf82f2ba16d03fdf7a8bc8538694b",
|
||||
"62573218530182b79e40d0113b7d281dace6da33bfcd0f9318558de5e5c76f08",
|
||||
"37d928416b15982f5bb8be40c5b62fae0b664e412c25891f8860c4242927e610",
|
||||
"b07ad11134a5c0542d2b418ef3863e8ea8477de68d9310681818ddd40825fdb0",
|
||||
"4af77cb76bab845b56470c95ce7b8cd84ce49a095984c1f3eed67b0ee344316e",
|
||||
"e3fdd4668d8726ba6adc401ac662c0cf6b5c1872082c488ed7da966d425fb1c0",
|
||||
"3dec71c81c7e78e879abc8da8b30e2446edbe98eeb8df9dafe9201ebb4c6a834",
|
||||
"7105467d9c5e855f1362fbddf820ed5e757997862efc9000317d3830a2f60ef3",
|
||||
"2821df94b021d3e77e8d9c0f3972340210f5ea2c0935cbf125cfc578d4d6722f",
|
||||
"114e5807accc337a22598bded30ebf3e0cfd75877e239f10cb043f829c315ab5",
|
||||
"d658a1c0354628cd7312593ab25d5b9083de8f0def6e8425f188101d256cd136",
|
||||
"4818d3be9b2a38fcc8c85d6c46f69b502943f79cf2462dfb0b6499e761bcc836",
|
||||
"92b8c943cb017b5f2d39264640c069f1ecced1d3ce9b3fd755d6df2fddb99458",
|
||||
"6edbd0fdf064fcbccd4a9e7a8ea520b87cb7faf867f7fe8a5f53625beb575119",
|
||||
"bf3b49c477dafb06af65bf09851c0fbef9dbc3152a7268d31b55a8e7a9a95860",
|
||||
"0e234dbadfda1393be2f068182615dbb83736f84f87710b5c7965bdce9f4a26a",
|
||||
"df5ceae34429e47b92bbd5505ba27666552e0eb619997f359c55699c3252b1ff",
|
||||
"08c1c7d940d699a91a83249bd578772e8958ffe23179e6150f07b96f1b47ce1e",
|
||||
"6f919a429270da0022d70062537bdc1b21c43a8abc552d8e366647e5b719d310",
|
||||
"63c66e5fd5d27f6fda87912ce46fa91a5e5b3634ed147fa2986330fc2696d3fa",
|
||||
"bde070b75296bca3aa494e7f549cd2bd1ff003776712bc98a3164b139b2054ab",
|
||||
"66694196dac5b60cf5e0ae05db8f3894fe04d65910686806551f471a0a0472e9",
|
||||
"0d2e97524b7ce4cf30b54e61b2689df036d099c53d42e2977b1671834bac39e7",
|
||||
"e081af76e923455f408127862be5c9baf7de6b19b952aa2a1da997d4dfe594c0",
|
||||
"121bf6ae1596983b703d62fecf60ea7dd3c3909acf1e0911652e7dadb420ed12",
|
||||
"a25e7b17464df71cd84ad08b17c5268520923bc33fe78c21b756f17353ea39a0",
|
||||
"e985f078fb44dbfdf3f4f34388f0f233a4e413e02297ee9a7dcc3fcceacd44f9",
|
||||
"b9184cf45e6e6b112cd863b1719de1bcab2137eb957e8028edca3a204a9ebb96",
|
||||
"157d177d5e4bcce0040eb4bddb681eacf9e2942e1c542a57ce851b4742a9cc4f",
|
||||
"0823e06635c9a1a69fd8833d1e48df98d711c1c47c06f27bb384932db1bbe9ee",
|
||||
"8beeec1fd1bcdecba235b449cc49abca69b6486ed1c0861a2bfb6a43c970b86f",
|
||||
"349f61a1cfc9112e537522858a0edae732a2f8434cf4780d3d2ec1e96f581cca",
|
||||
"587cdf72b5914d364f7e214a70481cf1131ee4a09e6b43e52428d2e56b000c13",
|
||||
"a6aa0c179316534c7b9ffb5f42a2af98d1d3a166bfb413199579f259c7b5e6df",
|
||||
"f9f3bb1ba8da5899b79186008ecfbd416b49f3b86d94045b91e34a40e41d5cff",
|
||||
"0cdda65a60b7b4d94e794c9397e01f69fb29309ce4fac83e7392dbba6bc497f9",
|
||||
"8fa5fce5ad09d43af7218ea5724cff2c4849a59ff73caf3bbca466e3c8538ba8",
|
||||
"8874ef46008753fcc0b77eb7a4a8560e35966bf5a12bcad4203ad2b4c1f8bfbe",
|
||||
"a8ee9a3aa2d0c08a951439ffb0e6d10315fc4776997b275de1ec19663e88c2c2",
|
||||
"9c184cbbff464ab4d5f6bfa78c39bf0880fb93b1574139306a97acb940d415c9",
|
||||
"5493a38c255c91ca49b958ed417f6c57e5bc444779d8f536f290596a31bc63d3",
|
||||
"3e1e82b96cc599d9fc55ae74330692ccbfb538a4cc923975fd8876efe4b81552",
|
||||
"16aaaf820c24c2726e349b0e49bbab72ca6eef7b3a2835de88d0cececa4da684",
|
||||
"7fa52ba349f7203c3dbc2249f9881101a3318d21869dd59f17abf953d234db65",
|
||||
"713d8018bb9ba3ab55c3a110120b9d7593514111075ef05f0fdb233ff2ceddc8",
|
||||
"56063afb495759a0942f1c33f28a4fb8320c6d376cb3c9513249453e45f24a04",
|
||||
"f9a6bacd9e055749b45174ecf3c3db18b78f3474761948a68adf601f54e59660",
|
||||
"7ddd7c6d41572f93fe07c0300c34e455b6d1f4372204933bf45035241c8b060c",
|
||||
"f81021b893a36b201de71330a2ea050b59dbf7560c62fa9cbea9261ab47a0ba2",
|
||||
"a01fbe4114c18fd534ae1621404d25c08e3b6775a2631ff40279bafd8c9304f4",
|
||||
"350fad8ebc938c6eb508a1483f385f577794a002bc1229db70a1b0131d174b9d",
|
||||
"570cb8bce87f532c5051d8c4c864012408e672a7d492669e660251fb1e066bec",
|
||||
"8cb6efbb129c84eba26d894c4293b476a6e9a1fe969c6ad18b554d2a57885f36",
|
||||
"f384a98467bf7f084ca31bea121a4ec76e530f523d3225c21ed25a18544a9916",
|
||||
"da127ab58ce557c2c95c20d6a291c2e5d880fff09dc28927b7bdfec97b995d72",
|
||||
"a4d95b4f74366ec920d0a0c5d81265688cc18733ffc444cac9b01ae2431568aa",
|
||||
"5ae2a71470570733422468bb733d53c85b1c8a6e7e6df5c05941556bcf342d1a",
|
||||
"65a2d161ff0e095d3afe37584dbbe649f1e9cd440755b5a3c5b2a252d5c0b8bc",
|
||||
"25ef70a8e41bb422ed7996a41160294e33238d6af17a532232f0a50b123431a2",
|
||||
"f1f0f76ee901664a65b97104296babb9c7422370e99bb677ae07c2ee420e7f40",
|
||||
"c3c66dda180b0330e75c8139b9f315a8c6b937f55d87d7be42e172bbac60d71e",
|
||||
"5881786695a9e58e19d79f790c7d9243a847c0269c5770bdd01f5149c2a62a88",
|
||||
"f2f816d3c8ebc7df06ab68d39223181aacc7be04364d1d4e69a56c33949bb983",
|
||||
"80a1c3b6b2778d4846ad9fe0bb2dd5afd99aa897f8231bfaac45fde43d602d9f",
|
||||
"72ad67cb043aa5df0c3dcc2464953a66893259d81c9cc7778c12bca3447fbd58",
|
||||
"ad72420a7963b8d4536d8eba00b4b989992247cd8c01660e242a8e71edaf0e19",
|
||||
"999d603d1cf6068e3bb6abe1bca976fa0ab84c4660b29ea8973de8b5cf5fd283",
|
||||
"e137a5910f02a764c3a3d8f1579ac0c7e3cc34e58933216868efe010332c1e6e",
|
||||
"10e0fa2362f59317626ae989bd1f962c583339d8d74d76c3e585243d152b91e8",
|
||||
"1951c652704962f5c6e33a4d4aadfee5d53ce2253644d1ed542da3e278524a07",
|
||||
"c938bccb7ba6c0217d8ba35ed91502aee051c8ae5bff05e88aab3b322aec936f",
|
||||
"4d6386c689785edd5beb55911a3a9fc8914838c8192184199589beef8b6ddf9f",
|
||||
"26f6f45a6468bc4b1f085fd28d63c264ee17564f9e247fc03ee179a0b579dcda",
|
||||
"235b7bb82b72c61acd5979ca5f2ca740aee805a780ba22e11aae5cd34f6ec760",
|
||||
"c027ffb585a1e4844b4907490b621b08c7e40a5e6f93e97bd4bb1b615bba9908",
|
||||
"aa77fc8053d139b998577319de29457b78b1cc8b35a5f3526c0621eaa42ce6e8",
|
||||
"afd0af9a11c5ae2a7c4a4571ce39ad57d8df70ef146ed83ad8eaff97b2387fb8",
|
||||
"a1f8fee9f1da9a2b306489d00edf754187b55e97f4fe6f249432fe6c7f44d6be",
|
||||
"4f12e8a123465a862060efb656299e6bef732e5954b02194308817b243e84d32",
|
||||
"6a1ca62f7d6952ad2eba1c64035260319baf03deabf856ca860744fc886b3d3a",
|
||||
"c72dd1fe890d6e4c1f7325a4f224e85aef6cdca8bf9441d228efaf126e02ba63",
|
||||
"2f6ddcea18d891ef4252e657989de68adcc43c2175d49c0c059c5e49b9dd5aed",
|
||||
"24efac0f240ed183c30398ee40307623f52113598f66c5864c90fc62643a2aec",
|
||||
"6ba3ebc935e7cf7fbb446e7f5c12b19c4455e6894412b0eedee4fc945e429e9a",
|
||||
"3519d6e5bc9649f97d07a07ef5471a553ffce35c7619f4f63e91a2ba38cbb729",
|
||||
"65e073df352fa9917e5c2475167e6c523b68c1406e1b6e81109e2d4cc87c740d",
|
||||
"d73bf816c3648a7d53d34be938c454e515efb0c974d5a225f33635540b2db90d",
|
||||
"bce167790fc86a273db011757d09e2d1148521ce242c2ded58f26cc49993aacb",
|
||||
"2d4286ed4039916f29602e86f47ea4c5b05998c0198509ca7799fcadfb337e8d",
|
||||
"9837c495b1af4f76b09177514a0f3e1dceb509c52b91712f3c7d29dc1b91d09b",
|
||||
"5c848b8291f39759903ce77f151acf40f3ab5afa2d4a45af62b320371c29a697",
|
||||
"b92df5016ee947ce6a21365d3361977f7f2f6c14025a983c44e13d3e8cc72152",
|
||||
"71d2f57222a39b1a7ed2df5e6fb23a964439b5a8e7d49b49d87e5cd5354baa75",
|
||||
"88b44d0198fb15b0c20a97f87e021c744606bfd35eae2874f35c447aa4ac3cd4",
|
||||
"29bb4c2557714119cd684da2867e689e37e3ca9c912db83ab84746816f6092ab",
|
||||
"b1836d98a288752675b133b9018fa1edf174f311921d01926c1e1a5900c21029",
|
||||
"a00645e090c7d96f3155ffbcfc41e526a763b0f53a98151ac4a7d4a5b14066b6",
|
||||
"78aab09919d17773b0d62799b37bd2e2970f72f5d1eb6472489c367b6135374f",
|
||||
"eb6123aeb28608f1c97b2bf62ef69f977cd0658a0ab491deebb1e972caa938c5",
|
||||
"8dd7ef1650b1b30cdf7814ae4d61a237eb0acc3ec3ce0f72b1c25780329c2d7d",
|
||||
"b1998419be3172858b990eea84fe10bb24b76c219cde277cb4305955fc7e0b65",
|
||||
"1b10560016c4bc506eef9056dedc2943a17179081e6eaf85b48d37dc20eac3cc",
|
||||
"1fb1d9d4d408a6734234910f554d272739a0d6fa401918d79b57be62c3f23ba2",
|
||||
"dec878f54ce36788289b61d32de0d9539032aba22cd15522752f729659c7cc5c",
|
||||
"fdbfd0773f5a66637b093dabf812197940d1134619a7e60a931b19915b7dab0a",
|
||||
"21bd2c9aae052a1c187947d2964f2be4afa7b30248409c41a75522e88a4e7977",
|
||||
"59326adab03416ec1d36699c18e5e4fa13ca1f2212d48c23bfdecb0be7263616",
|
||||
"bcf263d39457c0aef8ef42fd98f8131198ec4fb203155dd5bcd759e499a9ca5c",
|
||||
"f1ad083bcd8c7630eef93336d8a971ae8ae37166a6a00ac39684420c5f9afef8",
|
||||
"d82ee2ac41b36e3c1787a01835bf054070486dc20f6565efedbbc37cd3bf5fa5",
|
||||
"eba91a0dcbd3986299b0a3e66c116f77bd3421829291fd769522f01da26f107b",
|
||||
"11016558b7e8c6386c6a3e862691dcba47e33e257f0e7df38901ea7c0eba894c",
|
||||
"04f02795e34a0030e5186c8e700da8a46b1aa6bc0abed6b35c9c1cd6a73776b9",
|
||||
"2628dc8ad7fb731d59456b2755a99c6701467125fa69816c21bfccabc31edf6b",
|
||||
"9b7ca249ee5b45cd264492f30df09f708a7d9caed7beb9a5c6292f22e4c31f85",
|
||||
"5c42e7caedf382092faaf392174792b3cf5f2fe29cb586387ee55611af0617c9",
|
||||
"373f2fd5940a01feb79659c8b9099477f6d3e7b570ebb749c2ac336ea4be583d",
|
||||
"fea22887147adc3a659a14902080b03e86b4b8b16985fdf0bbacaed00d812422",
|
||||
"6a3e51a1443cff62af9fa12fafc8ea78ae74dac7792c9ae0f436f570ab33eb71",
|
||||
"796be21e213d6d0cd6fbe2de1555fb73d1cf9edc041a9f1ff1ad583c4ca92460",
|
||||
"03fcbcb31d3fd17f0eedb45ac5a51678c7c8b2b8498225d05f74e2892f017f72",
|
||||
"d28da07c6c22daf9ae987b3033c33d3140e5a56fa1ffd7dc5c7853d55a45bcc7",
|
||||
"fbb0ce02f50018741a12fc08eea80a18067d7bb0fcd96153d40bb8c808473aae",
|
||||
"2bf7c05a0209b4ea31314f04bd754cd01c58102d7cde8c496c655b6494924354",
|
||||
"1968a9e6e14ae86a1e02e6078fc4631851fce5dbac6aa34f860defd1ccfd0ded",
|
||||
"d886181329c9e06462a1407f547d77b38ff2c868b86d8976aa478e1cbb3d66d4",
|
||||
"0d465e02ff2f8eb0b5fb2fa9a38579c5d66337d4a16b58f8ed28d2d89fc02392",
|
||||
"3196419015289807880ef24b6781734822d654dc260c0560d00bac65eacd5219",
|
||||
"fa08390ddc333a2a12248d5ec3e51fff9b782227069fe5a0afbd8eba967ae8d1",
|
||||
"49ae36a791cb84516688d59a1ed3e5112851d65f265078aa2d433b45fa984c8a",
|
||||
"35daa428e12c59da6730760979aca3444d8b31149c6febd99fbfefa4b2372082",
|
||||
"5ef1d697beba612ff31d1dc139817c313a4e2ad3977775943b635c141ef0f2a1",
|
||||
"674256037ec00edb66b9355fb1d33a30a47a5d1f4bce2dd5475d89f1ea6502db",
|
||||
"7b6f017bc550933af91eec32a79464f540c5e0c208703e175843ee4e9ffc0a50",
|
||||
"bf0eb91da1d18dbb18fd9ff36c837387887ba142961176a44889718b2becb9dc",
|
||||
"3e5ac43a05164b074a2ff6353e9882917c5a3dbe168c2695de895f7decf1a56c",
|
||||
"35e8f004965347c2b18a000a83dd3a8084b8a4bf00522061ed1179aa1107c413",
|
||||
"fccb0fff3a24e555ec96f702ec11d420338910d148fc7b039d67568ad3a0e032",
|
||||
"5cab231048032dbf921b4fafa1951dd2da93bc3740667f31d5a1d5665b141261",
|
||||
"ffedb24be73441fbcd069f7785ebb865870e0f3ed228190732e4ffd5962bb82d",
|
||||
"a4fcfec18adf92f4ed822f64d2da9f5ae630885a1bfa626530f641db99aa7a30",
|
||||
"f98bcee41b0e3deafa1efaa1863750dbfd9bd7430b82529b670867d852230b5d",
|
||||
"8ab8d5fca047a52364a737c1af57bf656c9ad5049f08ef4c5aa252e61aa72123",
|
||||
"91318b39ad94c1d58143586b6d90dd6092a9d7487e321f4976967b6ac445ff43",
|
||||
"fabfbd4569ab018e12d5ffa9b1a40ca8eb2ca60a685817351d90eaa770d5eccb",
|
||||
"bbc5ef34428d980e2401942ceecfe07cdf21bfb1acae0596ea1d43fccf504f69",
|
||||
"26943e4201ea407a5667103fe07ca6e08ef76940f274349b0e2e776bcfb0acb6",
|
||||
"e3b305ffe33e72841f8e2a8688cc5cc27d42aee7624b33b7b6399b42db392437",
|
||||
"17c5a763dd57e6bcc7c4cf2db0eb5cf3e97116b67fe0dd519c97e4a4d55d5a62",
|
||||
"bbd260216879ce86af8318ffcf73c9e063ca76dd8bc35d3b6be45b2b4184888b",
|
||||
"41285591d0595bc42ab663051b410d51af39fe1720592e27acb1a8af72360a76",
|
||||
"f29acd6068ce494d0c0fe294cad91bb8968e3fff3f595a113227ab545c3ca3e6",
|
||||
"ec9013c6394528e7dd788ce7cc085ca79fcdfbb37565999d5b4b5a4e39452ecc",
|
||||
"27829bd7f1a8fcddcad0cc34a3b3fc67d62a2f3e09f8e75d35035c2281e83afd",
|
||||
"666bea9db4e15087204d076294d221d4cf5864f5d94de38f29132b1934a17ace",
|
||||
"a3a30924cad3dbda3446e5a6324e0a1390c70f795d5ecfe17ee5c70b14f7d87d",
|
||||
"19567fe5fdb10711d60aa4d9843e1c49c2a6d2fd1b5cf662e2105606bb7815d3",
|
||||
"b139f1c3a2f15596b9320334e37e4184d5d584c4a81e72d821a7edcad3aa62d5",
|
||||
"08f1531e0e3e8f8bae313b2c60a72d5601bf8b60d7a4d2f60e8481650340d250",
|
||||
"c5895669e1ff182bf1dd6c00dc955265e08ded0952b8ca62a1c63ba11c99f4ca",
|
||||
"84d1c28153f66c1a4eb5fa0df695e936d83294df31a08d8d8e2d4798d19d8ce0",
|
||||
"b8699f6af853fdbe897848feb46a05d733363f304eac4c8c1932e6ea4bc062cb",
|
||||
"10eb3f6c1d0661468d9ed83593e5e9c0b43c6feec6a5405a498194905ea6ed48",
|
||||
"509e215a600d9cadcbf5d62632ba321d7314764218db00ce8c907e425fccc445",
|
||||
"e62119b7be84c8eaad41ba7f4a35da403f4ed96b967a3134e89ee8b78f8792c2",
|
||||
"f790754a95d59ea5ffe6b9b5cc386c600a9e19e8bec997c192764365f1d05376",
|
||||
"990121b5aa4d6badfb7154db4cdbb4512124bc2f442bebac71ea90b5cc86f203",
|
||||
"b6983dedaa891eb14c964d84461e5cd37ed27b61771c64978ba83e3ecea194fa",
|
||||
"00fba1ceaa6aa1e378cd5b22a771d6070250ac37f4e17d7bf1a70b3139e9a860",
|
||||
"429854e7738abf2ecf46909454039e2fc5a080eb9a3c0c5ea13b07426dac3ad9",
|
||||
"ceb3e017944b0dd787be219d8629930b3f2e20e22b12dc88fd838488ebb896f3",
|
||||
"eb9e5d14424c63e675fe771b73ca865f7d38cf334d65e2426e12a0b88c1a2236",
|
||||
"556ee713449e6e59ac4b8b2e8310180c8f6280484e9db23456526cceb9216168",
|
||||
"bc89c3aa889e0144ac526a1f861227430dde7e439cc6a7e9b25c9a049c3ca7b3",
|
||||
"56d070c62ea99be66fff741a8e45fafda5f9ff783e84d5395b251f356ce4e16f",
|
||||
"ace15859c399e5ecd13b1420d3c3703c6a88dfb4a084f7225e7ba40a4b444fc8",
|
||||
"f03f1261ab6eb879fe9c5b0028cd400b3ffdfac4344e4c75f6cde3c05ded1f26",
|
||||
"955b2fda8d0068226f89270028b316b5adac871f1c1c85435479aba14a381b0f",
|
||||
"422509a98d7461a6b8ec87cbb173b2486577b59ea9b269e01c20567b38b3b3b2",
|
||||
"007d4de62ad89a4f5985f0cd9b76a7293acf383b4e9e734e813b9df1d57f986f",
|
||||
"13a04e32948225b7e22aa0137341ebbb811e0743032fac16be9d691a652db2eb",
|
||||
"8244b11d880a52f9f9e1830a822e6eeeaf0b12fc759f8261bc2f490cb0794f3b",
|
||||
"27d3415f8f8fd3048a1ee0d9487256dd1b0f9e31be663778efa5b3add63868ec",
|
||||
"0053f888db916a8905320e253fe2f0666355e6fb6de36f897231920a3edfe39f",
|
||||
"0bc5c0a2ea47fa3bb8be107e3b9d6b7226b1c8bd16ca1bab8f51b8e1de08aa8b",
|
||||
"4ca13aaa161c79025b5cd6c9a8ac33554f5ceb479fe293d9a342c865cd9c9948",
|
||||
"333afbe82e2a3df38bd1ef998f39c5feef2554697aa21b5410c0e95ef9156249",
|
||||
"587c4fcabd18ff890064171fce3d5be0c4aa1bba46893fb6a827a85ab54d20f3",
|
||||
"964328e4d51d67c4e2f1fd102a66b861d98199f81d18d660b1b4b52504cd772a",
|
||||
"196aad5594651efd679d30b9feb0f0d172cf977b4f89aa670ec741a8bf21e669",
|
||||
"9137bfd66bbf47bfa0bfcbb9f6e71b6eb3fd9776530e9fd30d3dab19e182f35d",
|
||||
"8217392c4ed2313188f295d94148a027a7f43824a5f5fba33a0b8c1045d509b4",
|
||||
"be9e12761519a4836e73015544163254877e1c4912fcea67a10e7026421dde75",
|
||||
"7b5220421a520b876cc6cdba0d3895104d7fac914dca5b93f9fe8b226566b71e",
|
||||
"5c83fccfeb4bf0eb8a94d43ebc84a81639a32f26c7ef77d0a2b626b7de7befdb",
|
||||
"132fd6c92cf176f975efdb5ded53470b462a48a2815c6f54a93ce4f935784cc7",
|
||||
"46a3dba364022d11aa616a2bc20e3be5c4390f38b9446edfa464d90d9af5d48f",
|
||||
"34b3f3fd8a83905a37762060f51d0b116377b4820b031b8e668e16f46c5b0285",
|
||||
"f0e397e033dabec859a4b9a9043c5f1fb0dba504764d6bcf2fe9bf2ffd318474",
|
||||
"85ecf59c7dd3b24ad17f591bc4737f32f1384c370a7a6f2add06a811dc824b6c",
|
||||
"4d03cdb1e6ad8e066a83654626d8c221433e8d4fd901c671300af37e000177f2",
|
||||
"61cb9c651893e6401b25f2bdf79c9f3ddc9ffe69cf6c791c420462bd73e347e1",
|
||||
"85f2686a42158cd5ad327781ecccd1bdcd346941dd4b4edc45f717de6a011800",
|
||||
"92de2ab82cac528e6d4ccd61e5b7c79591dcad9909c8ad3c8276ece6d48c0f08",
|
||||
"23a878a06bb94bff33083349149f3c860f2b00bc3fb28f04cbaf717c08af19a3",
|
||||
"1b1cce18ff0323566b192885d7ced30f9a9531a2580240f2c593a7d5b8580974",
|
||||
"08fcdec7ea1376d84f3b13a47a4b73c7781c9c7890bb28f712b58af4fd3f24fe",
|
||||
"03cc08fc4ece807c6495272c412be23b045622cc6b786ed8d5c94156ae678a0e",
|
||||
"c4d8a61dc3f5dcf4b83f27a90cbc37e816cf4754e12309626ec5679c99087c46",
|
||||
"b29d00681e29001cdd63c4bc50e5e25715faef692aeebb678c8050e1c095e888",
|
||||
"ac154617e93f2bb1afa232675f2135437a9cc9700c14c51c40084946596ba11a",
|
||||
"ce9549de8e68ae89f424dd9e1cde8a4eea2069da667cfcfbe837691d37366668",
|
||||
"426c45a98e2af35cc9708149f6c086ff5a3972e77d62c627d5e20de5d731cad8",
|
||||
"7e21bfe240a3d9b77a129c734a1d428dbc890379fbaf862853f48b2f7470b2b0",
|
||||
"fa090a71f77223a7210de6db18d9aa809e89fb15253aea28131df6c5a7639140",
|
||||
"7094ad044c5ab025e088b43aa0b947601fabe58ed700a412fd96e4b917ced0c8",
|
||||
"936d5cdc4f081b6fe36c356af4378d472cd7990303f2ea44da645afd7d5d7f9c",
|
||||
"05342037d3b69349dce7b95529d4b2a63ceb9d9393217a68f7cc8c958a96c3ea",
|
||||
"ff9e1c414ef27b1178b1de296526f50520b7ddb06286bf9c47792bfb449e40b6",
|
||||
"2f2b7bedb34d2854b17ccb702cddd8bc0157e39721d58be0b2ad54ee291fc9f1",
|
||||
"0d8db1f34140bbf7eb809137018a74af08cb3345b8a3e368cdda8521dab45791",
|
||||
"b109e4bfabcfe4a1c38be1156d9ca851c75e6aa2e57c0869e40cd9056f571e07",
|
||||
"5cb363547ca077c806fc69bc8c2006831ab89e72fd778ac1a48fa810934e350e",
|
||||
"85ee928bb110fd64eae54a91fc8548883e7fc4c60a3c61b505c31cea2d295c86",
|
||||
"1ec3df7d10ee6fd5f0532ad4fe771e6befc28b0bed0250bf523695d6d49a8246",
|
||||
"de9db2fc07c866bd7b885fb41522b63d550d0ce2e8ac5e14464a41733c2319e6",
|
||||
"9a27136422a8f56768db29ba172a7ba26c3c7aa910324e78e5ab3a3268ac3674",
|
||||
"60213c315119bf9005cb533d1a5b403b4a13c59982fe7773d30fdd8f519f4205",
|
||||
"40eb61ef1812eb8a4d389599bf449fc86653b2c4986061b952f46fc049de53f4",
|
||||
"658ef0d8140162b5f04591be13b47456245f531208bbca3260b857ca09b803c5",
|
||||
"02270fa66255048d724894e2206b4e773cc6a7b6d17ca090cdc25f317d5f53b9",
|
||||
"2ec6a0147f419161f7198d05be5f93152d9ccc10672db0ea47ff1687c0f0dd15",
|
||||
"4be1d8ceb96eb80ef7ce30079ded31163272aeccff5c18fe3aaa32ea2f5bed9d",
|
||||
"04ecaf48f44de87243b17b4c71ebff00020738639336010fa57435a54b623798",
|
||||
"e313a9feb7cfd1d56ec87b1f1062ff9a80da498f7b761af4bef0cecd1b4c385b",
|
||||
"ede3748f971f22341f7f5844dc60fc03cdb30c7cc720ebe13ae588c17a78aa94",
|
||||
"d90c0faa70e39b7c0a8c55457ed6e6478a4e4bf3707b08104326a1ee8377c3ab",
|
||||
"c79ffd0bbc8d004cc542e212990df6498abddd3deb50fd00ed00a2ff690974d6",
|
||||
"35c37d88cf73a89c4124b0ee537347c37fdb47156c8b0ecc509efc58236ed3f0",
|
||||
"a99182f343ccf05e557ffa6df71f03688b2afcf314c59daa774fe78db6f47add",
|
||||
"01115397a78af8a4ae2727ca7a01843235b626bd3db80888d3dfd0020d4135e2",
|
||||
"4a55aced578470d2f7280096d7fe8095f294095fba4778d1977d6db9270472f0",
|
||||
"4624adf8a5633f65b213b8ca46b55cb0ee36c41495f39b1ae70cbd545779b1a0",
|
||||
"d72bcd5b57a9c47e7bd5e9a1103657d10beb7b6c6d41f2b2985bc3bd3cc74860",
|
||||
"48baadb9a46293c92f29e7617846171356a42c3b5d18d49a05a7e173993785f7",
|
||||
"3da927737af8cb0e1c77097e35c54158d18aabfb3051c45bcc7ddfe00b157b1f",
|
||||
"b4a24bfdb2cb802c8d48a3a18fbfe18622a767fe7eddfca57d4555550ccd1643",
|
||||
"c58f82ac7c49dcba1721a88358f07636c9df60d3fd383e5789b808dc57a1dc9d",
|
||||
"5e1f756eff5155df073d30f4452bdafc4adaf4f35960771bf2c1e30137fd7a79",
|
||||
"be4a332f289338d67bd4834eae3128c488a61d255e972da484b6252b67a46b89",
|
||||
"d496e4a36238d03a83d8b45cf33d9388aa7568a279b034d1cdd87b457356cc5b",
|
||||
"a1c5212730ccda34de393210e276bbd44720dda777bcfd602315a3eee582f7dc",
|
||||
"08914ec63f6ef7fe1d678937dc0f6178883440b26b4aca29fce79068947e8397",
|
||||
"49e2cd2bd9b974074d9814f93eed371620bd4ea5fbf97a625065704e8fb382d7",
|
||||
"047c194111818b48ce93a4b006e4a09b9a2650757a87357111796e11e847bf23",
|
||||
"5955b0baa8265341f35a6f24fdc79066ba3ca9c5354c69b6b37a9ef3a26be556",
|
||||
"d7c962f3ea1938c5267cca4072548acf3afcce4d438ed62027caa211a5f98e8b",
|
||||
"c8cfba67cb4ce7e291b35154a50476d9a5c6bbb5d6cbaaa5d2408547fea7b02b",
|
||||
"de8a940d8a69a64ce264d2ab7320662aef2e391c587cb2aae22a86718d5dffbb",
|
||||
"94176f1310b26e54d4de48f87b74aa0b60532f184a2268508dece86dd7f85d36",
|
||||
"9ce6ee3fca56c9256a69df404782301300a6e5e7f5a25a1f6d68c0e9e42584c9",
|
||||
"7c423c4a220c6ff43ab6432f92b166323c58ee77f8c096ba0b00d52d7bd507e8",
|
||||
"0b62b9c1ae4d4988720e8d41d980b334458189de0a3dd01699338d7b07c3894e",
|
||||
"64f45f6f75110624506c53716f2fc1d5fe5f88f82a5bc6a7459ce70eae56dbb3",
|
||||
"12ffbeb8e52fed161af4d8a015d1a5c45dcb8240e5c8933ce3a88ba2c58f97e8",
|
||||
"2ee6b7b96043c8ded9fb52f87cdd0d0580ca6f8cef183c8a656394a11c0aa393",
|
||||
"aaef26b1f5726258bf9ce305a3e54bca65cf68779f90f9d24287245c27362e27",
|
||||
"ef59588dce57c35d010bea4d209f44c62f0b7c7e65bc0226c0e4971934da9435",
|
||||
"0e606c2f6f8dcd579faf4739312bd7327ac7796fa44a81780fe0d66fc7761fb9",
|
||||
"2f307198afdbde5f95989a17e06ce1bb9ff36c441cf3b2248431534fe13bb9fe",
|
||||
"51418e6df23d450aaacc74ef2df53a6b1693727b70bda9ebc43acfc23d8fb5ea",
|
||||
"6e9e3ac46705ed80520695b924435b00d2b3079598bf7faca7fd1524be777e5e",
|
||||
"1e96241e2876aad29ce64f5d7e7fbb8db7265449df816c0d30a96633778c5cb6",
|
||||
"81788f00eb72696d811f946e65d2c96528c45590874a1defdd46651e9b79a3a1",
|
||||
"d9aa5a9f1df50e933d7105a5d72b5fe96bfbb9fd4b5b0eaa5e80af12e72d497a",
|
||||
"e1b6976a732d27fc5d6a96b6d3d0d1d5eaa6ec46bae4665f17e7a43aefc75280",
|
||||
"9151c75edcec1cc90aa2d2c240ff657b0eef3f5f1ec37418c8854b2493114f1d",
|
||||
"3e7c12d0132421f08ea0a390cfa325e422a6b35120fb2eb650f108a165237934",
|
||||
"1ee0e85c7d8a91089c03f37318cdc9127026bf789e3ce4b75046eaa3eebd3458",
|
||||
"4ae64a3ef66cad847409ce175bd5365c9097fd21647a05730ac6b45841add3c8",
|
||||
"f0ea0f334cf1d64678a6dab08c07e2f94f339e8389bd17ebc882b5c8b736cbf2",
|
||||
"da904db96060546ff69e28993ce8183766da9402ac10fae9fc1f1d67ebd83c90",
|
||||
"db11820615f7b5e47778c45d2e083e77f49b608b587dc09ec26f077aba07a242",
|
||||
"ff5c726a83bd785484de75bb03b421f9e8e382bf2740120a2fcf72326aa01c75",
|
||||
"f8643a7efd6304980db323303ab73a6fd4f4ee1047520d39d571580395b97f21",
|
||||
"8facf9737d07838aedf6030593bfb247d8c29fe8d9b18b2913408627a4424d7e",
|
||||
"f0672964aa6e4c7dd4768e18827023787386927f4db89fd661444979afb43c18",
|
||||
"6fd3649c8401f2704ed2be18518b870eb6bf2b9a6689d1b336f05bd8b49017f6",
|
||||
"ed172dac7de827493e0c0fdd8d3299333acb678e72ed499e0224b389cc1e0fba",
|
||||
"7f9a8a8cc8e34add11934a1a5882be5978a6d28405cb0a053ec5699a502b1cef",
|
||||
"6ca829ebd2a0a40994f68c1db7978ec274b45c46e9b351df869a2bfe0630bbd4",
|
||||
"0bbb017c437573a55db88258a9d9a01188bdd23bb6b26903b137814871661f47",
|
||||
"9a6358d2541f46b6d05b80fe25a2cb025fbe9e4b227a6275908d5ee31c948569",
|
||||
"a75d26c6d4ce944024f10e6d23e8b5b888d680120e15dc0e4fee8d8833ee0c6a",
|
||||
"1d43d33556699b42c124b46e41243abf48727fe488428056fdd174a3861c1e3c",
|
||||
"7b5bd3fecbaa093f005c4f806ea67846c0df6b04df7729925cb14724f6a8b582",
|
||||
"6bdf2b54f2f5ab90191261d33dee80fede75896994016422b28db8ba62327d82",
|
||||
"1a16181b250085a91ccecc118473fa2ab98515e894a7b63b347c24b5be560c7a",
|
||||
"22d24891755910b48ad632358c26245bdcc375abc41f7e2c9fb3c7773dbf4e22",
|
||||
"5b70c5d4a373d541619c944fcc3b61259550b0e9fba3eca16f0879e5845b43b9",
|
||||
"b78f9098c9d76987b7409e63426a8d49972bb4e75289576c680cf96513d44b6d",
|
||||
"916b53b8e85eb7e0a2a76d6fc8d2163430e7183ccb103d6705f54af4bb070907",
|
||||
"dc3d78f43110d2aa9df83c5485ec33663ad5452b8cdeb1aeeac9d6b1487fb781",
|
||||
"3975539ed5402cb9f5ab503584524dd141cc4296b666ec66d807f94f62b1c026",
|
||||
"bd1f97fd89183643423073f22733880616456ca41960699f18e868cb9ac35508",
|
||||
"90b468ff0f83460c3dd8cfe778c39d32c6bb1eeff9ac5de7804a4050d3b8073e",
|
||||
"0e886d49d88b82c9f8dbdd2f38a535992f35ab16629724d746394db3898235fa",
|
||||
"76c22e965242d1ca5614e829d9028dcad9c4b09393bcbdd318b0365557335fb9",
|
||||
"59b168488ec8629f820a1efd8fc5a0c2adec4253e61d6a2945a68a9a43be9035",
|
||||
"ff172b42854eaf2865caa985d2fb6283c5ab19574126623ffd615a761a5bce72",
|
||||
"cb46ac9ccc024ee74c96e3cf1c13a6949a432e855dfa881b6a307c0e6daac59e",
|
||||
"9971574924c0f413bf4c0f96bb9c2fbdfea8f475e33a8fb6f15fa40903b63444",
|
||||
"1a95567deb0f45a8941e2248f33286485984a5e9d86d16c37d42169ad864dc36",
|
||||
"205fc7f7ec7a83f0bc22d5269c91762cd00adc7428456d799be5a0cd76f08b0f",
|
||||
"849dd41ef59a722901b7a0deb2c1fd3c110a91a726120a0a119cb7a15cf98438",
|
||||
"a32880917c714612101af95e5c8d8eb5fb046fdcc68bae76c05b829b3fa73c2e",
|
||||
"70b38d6d510d13b359dffa910329952c620a4bce4ee7a8552b9bb3a14572394d",
|
||||
"ef257ab2f4226faa6ba288a6793f026609068effb866c18496a847e8b60b102d",
|
||||
"e5196ab42ff53c8352288bde6b6b7312cd6f39f7d21b556b0db178d8470d5790",
|
||||
"ca98f128bf085f2b718f2b3c12da7c4d98887cc94251a2b1705b637611bd83bb",
|
||||
"79508f0b93a49ec19c5cb05906ca1ba3d3db8ed4f9c6884873d0d7e3e985ea51",
|
||||
"9088be3f47f9debc63e928739f7163182b49eab044518b151f0b89f6b6aefdd0",
|
||||
"46b2782fd669b6288a4d7348cf6671360277ba4864cc69bce3497369ac2ec31e",
|
||||
"0fa5131557db67b430d516530be939ff25882adf68a076602f3dfad8c77c963a",
|
||||
"3404302cc097d5457244453a4c9990804201ee8161188df811bcb32404998c71",
|
||||
"856939710dbb90a8eeda875a31f9a52af759bd932b88e7b08df35414c54d4721",
|
||||
"72569573b9b41d0ac5ce17764a139c6b8b36ef3ca6d92cec625dbcdae758ba22",
|
||||
"9746da344e435a008d6acb4847211bb676376ecc76c825b5d44a28b89ceeb40e",
|
||||
"3eafded1595516f032e33ec975f4c9c3a1055d13aa5575cf8a801d6103fdbeb4",
|
||||
"e88a6d2daa863c0787cc523a2cab45c546fad788951b10d75e2b0954db24cca7",
|
||||
"38f531e67f88f66de44d3357c8e8f2db456160ca31dd2024c9562f6afd260278",
|
||||
};
|
||||
// block 685498 (13 key images in one transaction)
|
||||
static const char * const key_images_685498[] =
|
||||
{
|
||||
"749b7277aa21c70c417f255fb181c3a30b44277edf657eaaebf28a2709dd2a90",
|
||||
"5a9b3e1a87332d735cedaa2b5623a6a5e99d99f5a2887c8fc84293577e8bf25c",
|
||||
"bea438768445eb3650cf619bf6758e94035abfe0ccda91d4a58c582df143d835",
|
||||
"376e237ff4da5e5cbd6e1bba4b01412fa751f2959c0c57006589f382413df429",
|
||||
"14ac2f2e044f8635a3a42ecb46c575424073c1f6e5ed5e905f516d57f63184b5",
|
||||
"2d1d2ecb77b69a2901de00897d0509c1b7855a3b2f8eb1afe419008fc03cd15a",
|
||||
"ea01658f0972b77ae9112d525ec073e3ec5c3b98d5ad912d95ab2636354b70b6",
|
||||
"d3934864a46101d8c242415282e7fc9ee73ad16cd40355535d226ab45ecdb61a",
|
||||
"ee379b05c5d02432330ebd4ea9c4f1c87d14c388568d526a0f8a22649a14e453",
|
||||
"aeb7b842b410b13ca4af7a5ffd5ae6caddc8bfec653df1b945e478839a2e0057",
|
||||
"451806929d9f5c3a7f365472703871abadc25b2a5a2d75472a45e86cd76c610b",
|
||||
"272d9b9fcc9e253c08da9caf8233471150019582eaefef461c1f9ceff7e2c337",
|
||||
"633cdedeb3b96ec4f234c670254c6f721e0b368d00b48c6b26759db7d62cf52d",
|
||||
};
|
||||
|
||||
if (height() > 202612)
|
||||
{
|
||||
for (const auto &kis: key_images_202612)
|
||||
{
|
||||
crypto::key_image ki;
|
||||
epee::string_tools::hex_to_pod(kis, ki);
|
||||
if (!has_key_image(ki))
|
||||
{
|
||||
LOG_PRINT_L1("Fixup: adding missing spent key " << ki);
|
||||
add_spent_key(ki);
|
||||
}
|
||||
}
|
||||
}
|
||||
if (height() > 685498)
|
||||
{
|
||||
for (const auto &kis: key_images_685498)
|
||||
{
|
||||
crypto::key_image ki;
|
||||
epee::string_tools::hex_to_pod(kis, ki);
|
||||
if (!has_key_image(ki))
|
||||
{
|
||||
LOG_PRINT_L1("Fixup: adding missing spent key " << ki);
|
||||
add_spent_key(ki);
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
batch_stop();
|
||||
}
|
||||
|
||||
} // namespace cryptonote
|
||||
|
||||
@@ -129,6 +129,15 @@ struct tx_data_t
|
||||
};
|
||||
#pragma pack(pop)
|
||||
|
||||
struct alt_block_data_t
|
||||
{
|
||||
uint64_t height;
|
||||
uint64_t cumulative_weight;
|
||||
uint64_t cumulative_difficulty_low;
|
||||
uint64_t cumulative_difficulty_high;
|
||||
uint64_t already_generated_coins;
|
||||
};
|
||||
|
||||
/**
|
||||
* @brief a struct containing txpool per transaction metadata
|
||||
*/
|
||||
@@ -753,6 +762,21 @@ public:
|
||||
*/
|
||||
virtual void batch_stop() = 0;
|
||||
|
||||
/**
|
||||
* @brief aborts a batch transaction
|
||||
*
|
||||
* If the subclass implements batching, this function should abort the
|
||||
* batch it is currently on.
|
||||
*
|
||||
* If no batch is in-progress, this function should throw a DB_ERROR.
|
||||
* This exception may change in the future if it is deemed necessary to
|
||||
* have a more granular exception type for this scenario.
|
||||
*
|
||||
* If any of this cannot be done, the subclass should throw the corresponding
|
||||
* subclass of DB_EXCEPTION
|
||||
*/
|
||||
virtual void batch_abort() = 0;
|
||||
|
||||
/**
|
||||
* @brief sets whether or not to batch transactions
|
||||
*
|
||||
@@ -1528,8 +1552,45 @@ public:
|
||||
*
|
||||
* @param: sz the block size
|
||||
*/
|
||||
|
||||
virtual void add_max_block_size(uint64_t sz) = 0;
|
||||
|
||||
/**
|
||||
* @brief add a new alternative block
|
||||
*
|
||||
* @param: blkid the block hash
|
||||
* @param: data: the metadata for the block
|
||||
* @param: blob: the block's blob
|
||||
*/
|
||||
virtual void add_alt_block(const crypto::hash &blkid, const cryptonote::alt_block_data_t &data, const cryptonote::blobdata &blob) = 0;
|
||||
|
||||
/**
|
||||
* @brief get an alternative block by hash
|
||||
*
|
||||
* @param: blkid the block hash
|
||||
* @param: data: the metadata for the block
|
||||
* @param: blob: the block's blob
|
||||
*
|
||||
* @return true if the block was found in the alternative blocks list, false otherwise
|
||||
*/
|
||||
virtual bool get_alt_block(const crypto::hash &blkid, alt_block_data_t *data, cryptonote::blobdata *blob) = 0;
|
||||
|
||||
/**
|
||||
* @brief remove an alternative block
|
||||
*
|
||||
* @param: blkid the block hash
|
||||
*/
|
||||
virtual void remove_alt_block(const crypto::hash &blkid) = 0;
|
||||
|
||||
/**
|
||||
* @brief get the number of alternative blocks stored
|
||||
*/
|
||||
virtual uint64_t get_alt_block_count() = 0;
|
||||
|
||||
/**
|
||||
* @brief drop all alternative blocks
|
||||
*/
|
||||
virtual void drop_alt_blocks() = 0;
|
||||
|
||||
/**
|
||||
* @brief runs a function over all txpool transactions
|
||||
*
|
||||
@@ -1619,6 +1680,23 @@ public:
|
||||
virtual bool for_all_outputs(std::function<bool(uint64_t amount, const crypto::hash &tx_hash, uint64_t height, size_t tx_idx)> f) const = 0;
|
||||
virtual bool for_all_outputs(uint64_t amount, const std::function<bool(uint64_t height)> &f) const = 0;
|
||||
|
||||
/**
|
||||
* @brief runs a function over all alternative blocks stored
|
||||
*
|
||||
* The subclass should run the passed function for each alt block it has
|
||||
* stored, passing (blkid, data, blob) as its parameters.
|
||||
*
|
||||
* If any call to the function returns false, the subclass should return
|
||||
* false. Otherwise, the subclass returns true.
|
||||
*
|
||||
* The subclass should throw DB_ERROR if any of the expected values are
|
||||
* not found. Current implementations simply return false.
|
||||
*
|
||||
* @param std::function f the function to run
|
||||
*
|
||||
* @return false if the function returns false for any output, otherwise true
|
||||
*/
|
||||
virtual bool for_all_alt_blocks(std::function<bool(const crypto::hash &blkid, const alt_block_data_t &data, const cryptonote::blobdata *blob)> f, bool include_blob = false) const = 0;
|
||||
|
||||
|
||||
//
|
||||
|
||||
@@ -194,6 +194,8 @@ namespace
|
||||
* txpool_meta txn hash txn metadata
|
||||
* txpool_blob txn hash txn blob
|
||||
*
|
||||
* alt_blocks block hash {block data, block blob}
|
||||
*
|
||||
* Note: where the data items are of uniform size, DUPFIXED tables have
|
||||
* been used to save space. In most of these cases, a dummy "zerokval"
|
||||
* key is used when accessing the table; the Key listed above will be
|
||||
@@ -221,6 +223,8 @@ const char* const LMDB_SPENT_KEYS = "spent_keys";
|
||||
const char* const LMDB_TXPOOL_META = "txpool_meta";
|
||||
const char* const LMDB_TXPOOL_BLOB = "txpool_blob";
|
||||
|
||||
const char* const LMDB_ALT_BLOCKS = "alt_blocks";
|
||||
|
||||
const char* const LMDB_HF_STARTING_HEIGHTS = "hf_starting_heights";
|
||||
const char* const LMDB_HF_VERSIONS = "hf_versions";
|
||||
|
||||
@@ -774,7 +778,7 @@ void BlockchainLMDB::add_block(const block& blk, size_t block_weight, uint64_t l
|
||||
bi.bi_diff_lo = (cumulative_difficulty & 0xffffffffffffffff).convert_to<uint64_t>();
|
||||
bi.bi_hash = blk_hash;
|
||||
bi.bi_cum_rct = num_rct_outs;
|
||||
if (blk.major_version >= 4)
|
||||
if (m_height > 0 && blk.major_version >= 4)
|
||||
{
|
||||
uint64_t last_height = m_height-1;
|
||||
MDB_val_set(h, last_height);
|
||||
@@ -1311,7 +1315,7 @@ void BlockchainLMDB::open(const std::string& filename, const int db_flags)
|
||||
if (is_hdd_result)
|
||||
{
|
||||
if (is_hdd_result.value())
|
||||
MCLOG_RED(el::Level::Warning, "global", "The blockchain is on a rotating drive: this will be very slow, use an SSD if possible");
|
||||
MCLOG_RED(el::Level::Debug, "global", "The blockchain is on a rotating drive: this will be very slow, use an SSD if possible");
|
||||
}
|
||||
|
||||
m_folder = filename;
|
||||
@@ -1400,6 +1404,8 @@ void BlockchainLMDB::open(const std::string& filename, const int db_flags)
|
||||
lmdb_db_open(txn, LMDB_TXPOOL_META, MDB_CREATE, m_txpool_meta, "Failed to open db handle for m_txpool_meta");
|
||||
lmdb_db_open(txn, LMDB_TXPOOL_BLOB, MDB_CREATE, m_txpool_blob, "Failed to open db handle for m_txpool_blob");
|
||||
|
||||
lmdb_db_open(txn, LMDB_ALT_BLOCKS, MDB_CREATE, m_alt_blocks, "Failed to open db handle for m_alt_blocks");
|
||||
|
||||
// this subdb is dropped on sight, so it may not be present when we open the DB.
|
||||
// Since we use MDB_CREATE, we'll get an exception if we open read-only and it does not exist.
|
||||
// So we don't open for read-only, and also not drop below. It is not used elsewhere.
|
||||
@@ -1423,6 +1429,7 @@ void BlockchainLMDB::open(const std::string& filename, const int db_flags)
|
||||
|
||||
mdb_set_compare(txn, m_txpool_meta, compare_hash32);
|
||||
mdb_set_compare(txn, m_txpool_blob, compare_hash32);
|
||||
mdb_set_compare(txn, m_alt_blocks, compare_hash32);
|
||||
mdb_set_compare(txn, m_properties, compare_string);
|
||||
|
||||
if (!(mdb_flags & MDB_RDONLY))
|
||||
@@ -2241,6 +2248,50 @@ bool BlockchainLMDB::for_all_txpool_txes(std::function<bool(const crypto::hash&,
|
||||
return ret;
|
||||
}
|
||||
|
||||
bool BlockchainLMDB::for_all_alt_blocks(std::function<bool(const crypto::hash&, const alt_block_data_t&, const cryptonote::blobdata*)> f, bool include_blob) const
|
||||
{
|
||||
LOG_PRINT_L3("BlockchainLMDB::" << __func__);
|
||||
check_open();
|
||||
|
||||
TXN_PREFIX_RDONLY();
|
||||
RCURSOR(alt_blocks);
|
||||
|
||||
MDB_val k;
|
||||
MDB_val v;
|
||||
bool ret = true;
|
||||
|
||||
MDB_cursor_op op = MDB_FIRST;
|
||||
while (1)
|
||||
{
|
||||
int result = mdb_cursor_get(m_cur_alt_blocks, &k, &v, op);
|
||||
op = MDB_NEXT;
|
||||
if (result == MDB_NOTFOUND)
|
||||
break;
|
||||
if (result)
|
||||
throw0(DB_ERROR(lmdb_error("Failed to enumerate alt blocks: ", result).c_str()));
|
||||
const crypto::hash &blkid = *(const crypto::hash*)k.mv_data;
|
||||
if (v.mv_size < sizeof(alt_block_data_t))
|
||||
throw0(DB_ERROR("alt_blocks record is too small"));
|
||||
const alt_block_data_t *data = (const alt_block_data_t*)v.mv_data;
|
||||
const cryptonote::blobdata *passed_bd = NULL;
|
||||
cryptonote::blobdata bd;
|
||||
if (include_blob)
|
||||
{
|
||||
bd.assign(reinterpret_cast<const char*>(v.mv_data) + sizeof(alt_block_data_t), v.mv_size - sizeof(alt_block_data_t));
|
||||
passed_bd = &bd;
|
||||
}
|
||||
|
||||
if (!f(blkid, *data, passed_bd)) {
|
||||
ret = false;
|
||||
break;
|
||||
}
|
||||
}
|
||||
|
||||
TXN_POSTFIX_RDONLY();
|
||||
|
||||
return ret;
|
||||
}
|
||||
|
||||
bool BlockchainLMDB::block_exists(const crypto::hash& h, uint64_t *height) const
|
||||
{
|
||||
LOG_PRINT_L3("BlockchainLMDB::" << __func__);
|
||||
@@ -4062,6 +4113,110 @@ uint8_t BlockchainLMDB::get_hard_fork_version(uint64_t height) const
|
||||
return ret;
|
||||
}
|
||||
|
||||
void BlockchainLMDB::add_alt_block(const crypto::hash &blkid, const cryptonote::alt_block_data_t &data, const cryptonote::blobdata &blob)
|
||||
{
|
||||
LOG_PRINT_L3("BlockchainLMDB::" << __func__);
|
||||
check_open();
|
||||
mdb_txn_cursors *m_cursors = &m_wcursors;
|
||||
|
||||
CURSOR(alt_blocks)
|
||||
|
||||
MDB_val k = {sizeof(blkid), (void *)&blkid};
|
||||
const size_t val_size = sizeof(alt_block_data_t) + blob.size();
|
||||
std::unique_ptr<char[]> val(new char[val_size]);
|
||||
memcpy(val.get(), &data, sizeof(alt_block_data_t));
|
||||
memcpy(val.get() + sizeof(alt_block_data_t), blob.data(), blob.size());
|
||||
MDB_val v = {val_size, (void *)val.get()};
|
||||
if (auto result = mdb_cursor_put(m_cur_alt_blocks, &k, &v, MDB_NODUPDATA)) {
|
||||
if (result == MDB_KEYEXIST)
|
||||
throw1(DB_ERROR("Attempting to add alternate block that's already in the db"));
|
||||
else
|
||||
throw1(DB_ERROR(lmdb_error("Error adding alternate block to db transaction: ", result).c_str()));
|
||||
}
|
||||
}
|
||||
|
||||
bool BlockchainLMDB::get_alt_block(const crypto::hash &blkid, alt_block_data_t *data, cryptonote::blobdata *blob)
|
||||
{
|
||||
LOG_PRINT_L3("BlockchainLMDB:: " << __func__);
|
||||
check_open();
|
||||
|
||||
TXN_PREFIX_RDONLY();
|
||||
RCURSOR(alt_blocks);
|
||||
|
||||
MDB_val_set(k, blkid);
|
||||
MDB_val v;
|
||||
int result = mdb_cursor_get(m_cur_alt_blocks, &k, &v, MDB_SET);
|
||||
if (result == MDB_NOTFOUND)
|
||||
return false;
|
||||
|
||||
if (result)
|
||||
throw0(DB_ERROR(lmdb_error("Error attempting to retrieve alternate block " + epee::string_tools::pod_to_hex(blkid) + " from the db: ", result).c_str()));
|
||||
if (v.mv_size < sizeof(alt_block_data_t))
|
||||
throw0(DB_ERROR("Record size is less than expected"));
|
||||
|
||||
const alt_block_data_t *ptr = (const alt_block_data_t*)v.mv_data;
|
||||
if (data)
|
||||
*data = *ptr;
|
||||
if (blob)
|
||||
blob->assign((const char*)(ptr + 1), v.mv_size - sizeof(alt_block_data_t));
|
||||
|
||||
TXN_POSTFIX_RDONLY();
|
||||
return true;
|
||||
}
|
||||
|
||||
void BlockchainLMDB::remove_alt_block(const crypto::hash &blkid)
|
||||
{
|
||||
LOG_PRINT_L3("BlockchainLMDB::" << __func__);
|
||||
check_open();
|
||||
mdb_txn_cursors *m_cursors = &m_wcursors;
|
||||
|
||||
CURSOR(alt_blocks)
|
||||
|
||||
MDB_val k = {sizeof(blkid), (void *)&blkid};
|
||||
MDB_val v;
|
||||
int result = mdb_cursor_get(m_cur_alt_blocks, &k, &v, MDB_SET);
|
||||
if (result)
|
||||
throw0(DB_ERROR(lmdb_error("Error locating alternate block " + epee::string_tools::pod_to_hex(blkid) + " in the db: ", result).c_str()));
|
||||
result = mdb_cursor_del(m_cur_alt_blocks, 0);
|
||||
if (result)
|
||||
throw0(DB_ERROR(lmdb_error("Error deleting alternate block " + epee::string_tools::pod_to_hex(blkid) + " from the db: ", result).c_str()));
|
||||
}
|
||||
|
||||
uint64_t BlockchainLMDB::get_alt_block_count()
|
||||
{
|
||||
LOG_PRINT_L3("BlockchainLMDB:: " << __func__);
|
||||
check_open();
|
||||
|
||||
TXN_PREFIX_RDONLY();
|
||||
RCURSOR(alt_blocks);
|
||||
|
||||
MDB_stat db_stats;
|
||||
int result = mdb_stat(m_txn, m_alt_blocks, &db_stats);
|
||||
uint64_t count = 0;
|
||||
if (result != MDB_NOTFOUND)
|
||||
{
|
||||
if (result)
|
||||
throw0(DB_ERROR(lmdb_error("Failed to query m_alt_blocks: ", result).c_str()));
|
||||
count = db_stats.ms_entries;
|
||||
}
|
||||
TXN_POSTFIX_RDONLY();
|
||||
return count;
|
||||
}
|
||||
|
||||
void BlockchainLMDB::drop_alt_blocks()
|
||||
{
|
||||
LOG_PRINT_L3("BlockchainLMDB::" << __func__);
|
||||
check_open();
|
||||
|
||||
TXN_PREFIX(0);
|
||||
|
||||
auto result = mdb_drop(*txn_ptr, m_alt_blocks, 0);
|
||||
if (result)
|
||||
throw1(DB_ERROR(lmdb_error("Error dropping alternative blocks: ", result).c_str()));
|
||||
|
||||
TXN_POSTFIX_SUCCESS();
|
||||
}
|
||||
|
||||
bool BlockchainLMDB::is_read_only() const
|
||||
{
|
||||
unsigned int flags;
|
||||
|
||||
@@ -67,6 +67,8 @@ typedef struct mdb_txn_cursors
|
||||
MDB_cursor *m_txc_txpool_meta;
|
||||
MDB_cursor *m_txc_txpool_blob;
|
||||
|
||||
MDB_cursor *m_txc_alt_blocks;
|
||||
|
||||
MDB_cursor *m_txc_hf_versions;
|
||||
|
||||
MDB_cursor *m_txc_properties;
|
||||
@@ -87,6 +89,7 @@ typedef struct mdb_txn_cursors
|
||||
#define m_cur_spent_keys m_cursors->m_txc_spent_keys
|
||||
#define m_cur_txpool_meta m_cursors->m_txc_txpool_meta
|
||||
#define m_cur_txpool_blob m_cursors->m_txc_txpool_blob
|
||||
#define m_cur_alt_blocks m_cursors->m_txc_alt_blocks
|
||||
#define m_cur_hf_versions m_cursors->m_txc_hf_versions
|
||||
#define m_cur_properties m_cursors->m_txc_properties
|
||||
|
||||
@@ -108,6 +111,7 @@ typedef struct mdb_rflags
|
||||
bool m_rf_spent_keys;
|
||||
bool m_rf_txpool_meta;
|
||||
bool m_rf_txpool_blob;
|
||||
bool m_rf_alt_blocks;
|
||||
bool m_rf_hf_versions;
|
||||
bool m_rf_properties;
|
||||
} mdb_rflags;
|
||||
@@ -288,6 +292,12 @@ public:
|
||||
virtual bool update_pruning();
|
||||
virtual bool check_pruning();
|
||||
|
||||
virtual void add_alt_block(const crypto::hash &blkid, const cryptonote::alt_block_data_t &data, const cryptonote::blobdata &blob);
|
||||
virtual bool get_alt_block(const crypto::hash &blkid, alt_block_data_t *data, cryptonote::blobdata *blob);
|
||||
virtual void remove_alt_block(const crypto::hash &blkid);
|
||||
virtual uint64_t get_alt_block_count();
|
||||
virtual void drop_alt_blocks();
|
||||
|
||||
virtual bool for_all_txpool_txes(std::function<bool(const crypto::hash&, const txpool_tx_meta_t&, const cryptonote::blobdata*)> f, bool include_blob = false, bool include_unrelayed_txes = true) const;
|
||||
|
||||
virtual bool for_all_key_images(std::function<bool(const crypto::key_image&)>) const;
|
||||
@@ -295,6 +305,7 @@ public:
|
||||
virtual bool for_all_transactions(std::function<bool(const crypto::hash&, const cryptonote::transaction&)>, bool pruned) const;
|
||||
virtual bool for_all_outputs(std::function<bool(uint64_t amount, const crypto::hash &tx_hash, uint64_t height, size_t tx_idx)> f) const;
|
||||
virtual bool for_all_outputs(uint64_t amount, const std::function<bool(uint64_t height)> &f) const;
|
||||
virtual bool for_all_alt_blocks(std::function<bool(const crypto::hash &blkid, const alt_block_data_t &data, const cryptonote::blobdata *blob)> f, bool include_blob = false) const;
|
||||
|
||||
virtual uint64_t add_block( const std::pair<block, blobdata>& blk
|
||||
, size_t block_weight
|
||||
@@ -452,6 +463,8 @@ private:
|
||||
MDB_dbi m_txpool_meta;
|
||||
MDB_dbi m_txpool_blob;
|
||||
|
||||
MDB_dbi m_alt_blocks;
|
||||
|
||||
MDB_dbi m_hf_starting_heights;
|
||||
MDB_dbi m_hf_versions;
|
||||
|
||||
|
||||
@@ -54,6 +54,7 @@ public:
|
||||
virtual void unlock() override { }
|
||||
virtual bool batch_start(uint64_t batch_num_blocks=0, uint64_t batch_bytes=0) override { return true; }
|
||||
virtual void batch_stop() override {}
|
||||
virtual void batch_abort() override {}
|
||||
virtual void set_batch_transactions(bool) override {}
|
||||
virtual void block_wtxn_start() override {}
|
||||
virtual void block_wtxn_stop() override {}
|
||||
@@ -155,6 +156,13 @@ public:
|
||||
|
||||
virtual uint64_t get_max_block_size() override { return 100000000; }
|
||||
virtual void add_max_block_size(uint64_t sz) override { }
|
||||
|
||||
virtual void add_alt_block(const crypto::hash &blkid, const cryptonote::alt_block_data_t &data, const cryptonote::blobdata &blob) override {}
|
||||
virtual bool get_alt_block(const crypto::hash &blkid, alt_block_data_t *data, cryptonote::blobdata *blob) override { return false; }
|
||||
virtual void remove_alt_block(const crypto::hash &blkid) override {}
|
||||
virtual uint64_t get_alt_block_count() override { return 0; }
|
||||
virtual void drop_alt_blocks() override {}
|
||||
virtual bool for_all_alt_blocks(std::function<bool(const crypto::hash &blkid, const alt_block_data_t &data, const cryptonote::blobdata *blob)> f, bool include_blob = false) const override { return true; }
|
||||
};
|
||||
|
||||
}
|
||||
|
||||
@@ -157,7 +157,7 @@ endif()
|
||||
|
||||
set_property(TARGET blockchain_import
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-blockchain-import")
|
||||
OUTPUT_NAME "wownero-blockchain-import")
|
||||
install(TARGETS blockchain_import DESTINATION bin)
|
||||
|
||||
monero_add_executable(blockchain_export
|
||||
@@ -178,7 +178,7 @@ target_link_libraries(blockchain_export
|
||||
|
||||
set_property(TARGET blockchain_export
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-blockchain-export")
|
||||
OUTPUT_NAME "wownero-blockchain-export")
|
||||
install(TARGETS blockchain_export DESTINATION bin)
|
||||
|
||||
monero_add_executable(blockchain_blackball
|
||||
@@ -200,7 +200,7 @@ target_link_libraries(blockchain_blackball
|
||||
|
||||
set_property(TARGET blockchain_blackball
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-blockchain-mark-spent-outputs")
|
||||
OUTPUT_NAME "wownero-blockchain-mark-spent-outputs")
|
||||
install(TARGETS blockchain_blackball DESTINATION bin)
|
||||
|
||||
|
||||
@@ -222,7 +222,7 @@ target_link_libraries(blockchain_usage
|
||||
|
||||
set_property(TARGET blockchain_usage
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-blockchain-usage")
|
||||
OUTPUT_NAME "wownero-blockchain-usage")
|
||||
install(TARGETS blockchain_usage DESTINATION bin)
|
||||
|
||||
monero_add_executable(blockchain_ancestry
|
||||
@@ -243,7 +243,7 @@ target_link_libraries(blockchain_ancestry
|
||||
|
||||
set_property(TARGET blockchain_ancestry
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-blockchain-ancestry")
|
||||
OUTPUT_NAME "wownero-blockchain-ancestry")
|
||||
install(TARGETS blockchain_ancestry DESTINATION bin)
|
||||
|
||||
monero_add_executable(blockchain_depth
|
||||
@@ -264,7 +264,7 @@ target_link_libraries(blockchain_depth
|
||||
|
||||
set_property(TARGET blockchain_depth
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-blockchain-depth")
|
||||
OUTPUT_NAME "wownero-blockchain-depth")
|
||||
install(TARGETS blockchain_depth DESTINATION bin)
|
||||
|
||||
monero_add_executable(blockchain_stats
|
||||
@@ -285,7 +285,7 @@ target_link_libraries(blockchain_stats
|
||||
|
||||
set_property(TARGET blockchain_stats
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-blockchain-stats")
|
||||
OUTPUT_NAME "wownero-blockchain-stats")
|
||||
install(TARGETS blockchain_stats DESTINATION bin)
|
||||
|
||||
monero_add_executable(blockchain_prune_known_spent_data
|
||||
@@ -307,7 +307,7 @@ target_link_libraries(blockchain_prune_known_spent_data
|
||||
|
||||
set_property(TARGET blockchain_prune_known_spent_data
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-blockchain-prune-known-spent-data")
|
||||
OUTPUT_NAME "wownero-blockchain-prune-known-spent-data")
|
||||
install(TARGETS blockchain_prune_known_spent_data DESTINATION bin)
|
||||
|
||||
monero_add_executable(blockchain_prune
|
||||
@@ -316,7 +316,7 @@ monero_add_executable(blockchain_prune
|
||||
|
||||
set_property(TARGET blockchain_prune
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-blockchain-prune")
|
||||
OUTPUT_NAME "wownero-blockchain-prune")
|
||||
install(TARGETS blockchain_prune DESTINATION bin)
|
||||
|
||||
target_link_libraries(blockchain_prune
|
||||
|
||||
@@ -395,12 +395,12 @@ int main(int argc, char* argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << desc_options << std::endl;
|
||||
return 1;
|
||||
}
|
||||
|
||||
mlog_configure(mlog_get_default_log_path("monero-blockchain-ancestry.log"), true);
|
||||
mlog_configure(mlog_get_default_log_path("wownero-blockchain-ancestry.log"), true);
|
||||
if (!command_line::is_arg_defaulted(vm, arg_log_level))
|
||||
mlog_set_log(command_line::get_arg(vm, arg_log_level).c_str());
|
||||
else
|
||||
|
||||
@@ -1084,7 +1084,7 @@ int main(int argc, char* argv[])
|
||||
const command_line::arg_descriptor<bool> arg_rct_only = {"rct-only", "Only work on ringCT outputs", false};
|
||||
const command_line::arg_descriptor<bool> arg_check_subsets = {"check-subsets", "Check ring subsets (very expensive)", false};
|
||||
const command_line::arg_descriptor<bool> arg_verbose = {"verbose", "Verbose output)", false};
|
||||
const command_line::arg_descriptor<std::vector<std::string> > arg_inputs = {"inputs", "Path to Monero DB, and path to any fork DBs"};
|
||||
const command_line::arg_descriptor<std::vector<std::string> > arg_inputs = {"inputs", "Path to Wownero DB, and path to any fork DBs"};
|
||||
const command_line::arg_descriptor<std::string> arg_db_sync_mode = {
|
||||
"db-sync-mode"
|
||||
, "Specify sync option, using format [safe|fast|fastest]:[nrecords_per_sync]."
|
||||
@@ -1126,12 +1126,12 @@ int main(int argc, char* argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << desc_options << std::endl;
|
||||
return 1;
|
||||
}
|
||||
|
||||
mlog_configure(mlog_get_default_log_path("monero-blockchain-mark-spent-outputs.log"), true);
|
||||
mlog_configure(mlog_get_default_log_path("wownero-blockchain-mark-spent-outputs.log"), true);
|
||||
if (!command_line::is_arg_defaulted(vm, arg_log_level))
|
||||
mlog_set_log(command_line::get_arg(vm, arg_log_level).c_str());
|
||||
else
|
||||
|
||||
@@ -97,12 +97,12 @@ int main(int argc, char* argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << desc_options << std::endl;
|
||||
return 1;
|
||||
}
|
||||
|
||||
mlog_configure(mlog_get_default_log_path("monero-blockchain-depth.log"), true);
|
||||
mlog_configure(mlog_get_default_log_path("wownero-blockchain-depth.log"), true);
|
||||
if (!command_line::is_arg_defaulted(vm, arg_log_level))
|
||||
mlog_set_log(command_line::get_arg(vm, arg_log_level).c_str());
|
||||
else
|
||||
|
||||
@@ -97,12 +97,12 @@ int main(int argc, char* argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << desc_options << std::endl;
|
||||
return 1;
|
||||
}
|
||||
|
||||
mlog_configure(mlog_get_default_log_path("monero-blockchain-export.log"), true);
|
||||
mlog_configure(mlog_get_default_log_path("wownero-blockchain-export.log"), true);
|
||||
if (!command_line::is_arg_defaulted(vm, arg_log_level))
|
||||
mlog_set_log(command_line::get_arg(vm, arg_log_level).c_str());
|
||||
else
|
||||
|
||||
@@ -673,7 +673,7 @@ int main(int argc, char* argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << desc_options << std::endl;
|
||||
return 1;
|
||||
}
|
||||
@@ -711,7 +711,7 @@ int main(int argc, char* argv[])
|
||||
m_config_folder = command_line::get_arg(vm, cryptonote::arg_data_dir);
|
||||
db_arg_str = command_line::get_arg(vm, arg_database);
|
||||
|
||||
mlog_configure(mlog_get_default_log_path("monero-blockchain-import.log"), true);
|
||||
mlog_configure(mlog_get_default_log_path("wownero-blockchain-import.log"), true);
|
||||
if (!command_line::is_arg_defaulted(vm, arg_log_level))
|
||||
mlog_set_log(command_line::get_arg(vm, arg_log_level).c_str());
|
||||
else
|
||||
|
||||
@@ -490,12 +490,12 @@ int main(int argc, char* argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << desc_options << std::endl;
|
||||
return 1;
|
||||
}
|
||||
|
||||
mlog_configure(mlog_get_default_log_path("monero-blockchain-prune.log"), true);
|
||||
mlog_configure(mlog_get_default_log_path("wownero-blockchain-prune.log"), true);
|
||||
if (!command_line::is_arg_defaulted(vm, arg_log_level))
|
||||
mlog_set_log(command_line::get_arg(vm, arg_log_level).c_str());
|
||||
else
|
||||
|
||||
@@ -147,12 +147,12 @@ int main(int argc, char* argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << desc_options << std::endl;
|
||||
return 1;
|
||||
}
|
||||
|
||||
mlog_configure(mlog_get_default_log_path("monero-blockchain-prune-known-spent-data.log"), true);
|
||||
mlog_configure(mlog_get_default_log_path("wownero-blockchain-prune-known-spent-data.log"), true);
|
||||
if (!command_line::is_arg_defaulted(vm, arg_log_level))
|
||||
mlog_set_log(command_line::get_arg(vm, arg_log_level).c_str());
|
||||
else
|
||||
|
||||
@@ -107,12 +107,12 @@ int main(int argc, char* argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << desc_options << std::endl;
|
||||
return 1;
|
||||
}
|
||||
|
||||
mlog_configure(mlog_get_default_log_path("monero-blockchain-stats.log"), true);
|
||||
mlog_configure(mlog_get_default_log_path("wownero-blockchain-stats.log"), true);
|
||||
if (!command_line::is_arg_defaulted(vm, arg_log_level))
|
||||
mlog_set_log(command_line::get_arg(vm, arg_log_level).c_str());
|
||||
else
|
||||
|
||||
@@ -129,12 +129,12 @@ int main(int argc, char* argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << desc_options << std::endl;
|
||||
return 1;
|
||||
}
|
||||
|
||||
mlog_configure(mlog_get_default_log_path("monero-blockchain-usage.log"), true);
|
||||
mlog_configure(mlog_get_default_log_path("wownero-blockchain-usage.log"), true);
|
||||
if (!command_line::is_arg_defaulted(vm, arg_log_level))
|
||||
mlog_set_log(command_line::get_arg(vm, arg_log_level).c_str());
|
||||
else
|
||||
|
||||
Binary file not shown.
@@ -161,54 +161,65 @@ namespace cryptonote
|
||||
{
|
||||
if (nettype == TESTNET)
|
||||
{
|
||||
ADD_CHECKPOINT(0, "48ca7cd3c8de5b6a4d53d2861fbdaedca141553559f9be9520068053cda8430b");
|
||||
ADD_CHECKPOINT(1000000, "46b690b710a07ea051bc4a6b6842ac37be691089c0f7758cfeec4d5fc0b4a258");
|
||||
ADD_CHECKPOINT(1058600, "12904f6b4d9e60fd875674e07147d2c83d6716253f046af7b894c3e81da7e1bd");
|
||||
return true;
|
||||
}
|
||||
if (nettype == STAGENET)
|
||||
{
|
||||
ADD_CHECKPOINT(0, "76ee3cc98646292206cd3e86f74d88b4dcc1d937088645e9b0cbca84b7ce74eb");
|
||||
ADD_CHECKPOINT(10000, "1f8b0ce313f8b9ba9a46108bfd285c45ad7c2176871fd41c3a690d4830ce2fd5");
|
||||
return true;
|
||||
}
|
||||
ADD_CHECKPOINT(1, "771fbcd656ec1464d3a02ead5e18644030007a0fc664c0a964d30922821a8148");
|
||||
ADD_CHECKPOINT(10, "c0e3b387e47042f72d8ccdca88071ff96bff1ac7cde09ae113dbb7ad3fe92381");
|
||||
ADD_CHECKPOINT(100, "ac3e11ca545e57c49fca2b4e8c48c03c23be047c43e471e1394528b1f9f80b2d");
|
||||
ADD_CHECKPOINT(1000, "5acfc45acffd2b2e7345caf42fa02308c5793f15ec33946e969e829f40b03876");
|
||||
ADD_CHECKPOINT(10000, "c758b7c81f928be3295d45e230646de8b852ec96a821eac3fea4daf3fcac0ca2");
|
||||
ADD_CHECKPOINT(22231, "7cb10e29d67e1c069e6e11b17d30b809724255fee2f6868dc14cfc6ed44dfb25");
|
||||
ADD_CHECKPOINT(29556, "53c484a8ed91e4da621bb2fa88106dbde426fe90d7ef07b9c1e5127fb6f3a7f6");
|
||||
ADD_CHECKPOINT(50000, "0fe8758ab06a8b9cb35b7328fd4f757af530a5d37759f9d3e421023231f7b31c");
|
||||
ADD_CHECKPOINT(80000, "a62dcd7b536f22e003ebae8726e9e7276f63d594e264b6f0cd7aab27b66e75e3");
|
||||
ADD_CHECKPOINT(202612, "bbd604d2ba11ba27935e006ed39c9bfdd99b76bf4a50654bc1e1e61217962698");
|
||||
ADD_CHECKPOINT(202613, "e2aa337e78df1f98f462b3b1e560c6b914dec47b610698b7b7d1e3e86b6197c2");
|
||||
ADD_CHECKPOINT(202614, "c29e3dc37d8da3e72e506e31a213a58771b24450144305bcba9e70fa4d6ea6fb");
|
||||
ADD_CHECKPOINT(205000, "5d3d7a26e6dc7535e34f03def711daa8c263785f73ec1fadef8a45880fde8063");
|
||||
ADD_CHECKPOINT(220000, "9613f455933c00e3e33ac315cc6b455ee8aa0c567163836858c2d9caff111553");
|
||||
ADD_CHECKPOINT(230300, "bae7a80c46859db355556e3a9204a337ae8f24309926a1312323fdecf1920e61");
|
||||
ADD_CHECKPOINT(230700, "93e631240ceac831da1aebfc5dac8f722c430463024763ebafa888796ceaeedf");
|
||||
ADD_CHECKPOINT(231350, "b5add137199b820e1ea26640e5c3e121fd85faa86a1e39cf7e6cc097bdeb1131");
|
||||
ADD_CHECKPOINT(232150, "955de8e6b6508af2c24f7334f97beeea651d78e9ade3ab18fec3763be3201aa8");
|
||||
ADD_CHECKPOINT(249380, "654fb0a81ce3e5caf7e3264a70f447d4bd07586c08fa50f6638cc54da0a52b2d");
|
||||
ADD_CHECKPOINT(460000, "75037a7aed3e765db96c75bcf908f59d690a5f3390baebb9edeafd336a1c4831");
|
||||
ADD_CHECKPOINT(500000, "2428f0dbe49796be05ed81b347f53e1f7f44aed0abf641446ec2b94cae066b02");
|
||||
ADD_CHECKPOINT(600000, "f5828ebf7d7d1cb61762c4dfe3ccf4ecab2e1aad23e8113668d981713b7a54c5");
|
||||
ADD_CHECKPOINT(700000, "12be9b3d210b93f574d2526abb9c1ab2a881b479131fd0d4f7dac93875f503cd");
|
||||
ADD_CHECKPOINT(825000, "56503f9ad766774b575be3aff73245e9d159be88132c93d1754764f28da2ff60");
|
||||
ADD_CHECKPOINT(900000, "d9958d0e7dcf91a5a7b11de225927bf7efc6eb26240315ce12372be902cc1337");
|
||||
ADD_CHECKPOINT(913193, "5292d5d56f6ba4de33a58d9a34d263e2cb3c6fee0aed2286fd4ac7f36d53c85f");
|
||||
ADD_CHECKPOINT(1000000, "a886ef5149902d8342475fee9bb296341b891ac67c4842f47a833f23c00ed721");
|
||||
ADD_CHECKPOINT(1100000, "3fd720c5c8b3072fc1ccda922dec1ef25f9ed88a1e6ad4103d0fe00b180a5903");
|
||||
ADD_CHECKPOINT(1150000, "1dd16f626d18e1e988490dfd06de5920e22629c972c58b4d8daddea0038627b2");
|
||||
ADD_CHECKPOINT(1200000, "fa7d13a90850882060479d100141ff84286599ae39c3277c8ea784393f882d1f");
|
||||
ADD_CHECKPOINT(1300000, "31b34272343a44a9f4ac7de7a8fcf3b7d8a3124d7d6870affd510d2f37e74cd0");
|
||||
ADD_CHECKPOINT(1390000, "a8f5649dd4ded60eedab475f2bec8c934681c07e3cf640e9be0617554f13ff6c");
|
||||
ADD_CHECKPOINT(1450000, "ac94e8860093bc7c83e4e91215cba1d663421ecf4067a0ae609c3a8b52bcfac2");
|
||||
ADD_CHECKPOINT(1530000, "01759bce497ec38e63c78b1038892169203bb78f87e488172f6b854fcd63ba7e");
|
||||
ADD_CHECKPOINT(1579000, "7d0d7a2346373afd41ed1e744a939fc5d474a7dbaa257be5c6fff4009e789241");
|
||||
ADD_CHECKPOINT(1668900, "ac2dcaf3d2f58ffcf8391639f0f1ebafcb8eac43c49479c7c37f611868d07568");
|
||||
ADD_CHECKPOINT(1775600, "1c6e01c661dc22cab939e79ec6a5272190624ce8356d2f7b958e4f9a57fdb05e");
|
||||
ADD_CHECKPOINT(1, "97f4ce4d7879b3bea54dcec738cd2ebb7952b4e9bb9743262310cd5fec749340");
|
||||
ADD_CHECKPOINT(10, "305472c87ff86d8afb3ec42634828462b0ed3d929fc05fa1ae668c3bee04837a");
|
||||
ADD_CHECKPOINT(100, "a92b9deae26e19322041cbc2f850fa905748ae1e5bf69b35ca90b247c5cbfc04");
|
||||
ADD_CHECKPOINT(1000, "62921e13030b29264439cafaf8320cf8aa039ee6ba7ba29c72f11b50a079269a");
|
||||
ADD_CHECKPOINT(2000, "b3e1d73e3d0243239481aa76cb075cf2428556f5dc4f2e30428ea2ba36693e97");
|
||||
ADD_CHECKPOINT(3000, "83a6e1ab394e80b8442b7b70b0e4c3a9fa0143e0ca51a33e829537ef5dd1bf13");
|
||||
ADD_CHECKPOINT(4000, "7c70722d8cb8106b4bec67e1790614cc6e98db7afd0843b96cdff6960a0e0073");
|
||||
ADD_CHECKPOINT(5000, "331ee74008e174e5fd1956f64c52793961b321a1366f7c6f7d324e8265df34f6");
|
||||
ADD_CHECKPOINT(6969, "aa7b66e8c461065139b55c29538a39c33ceda93e587f84d490ed573d80511c87"); //Hard fork to v8
|
||||
ADD_CHECKPOINT(7000, "2711bd33b107f744ad8bf98c1acefa18658780079496bd2f3a36f2e20b261f8e");
|
||||
ADD_CHECKPOINT(7500, "5975967c4624f13f058acafe7adf9355e03e8e802eeadc84ccb22ea588bc0762");
|
||||
ADD_CHECKPOINT(7900, "d9bc18cb35feb6b26bc5a19bbdbf7c852d9cc02883acb5bbce2e87d8b2c86069");
|
||||
ADD_CHECKPOINT(10000, "bc5bfbf1b26c8f976d1d792ece4c6a7e93064bec62b72f1d5beae74c3f273b3b");
|
||||
ADD_CHECKPOINT(20000, "52cc7edcb49eb02f28a653b824089a726f4050eb210263ee6f4180d388a1e5cc");
|
||||
ADD_CHECKPOINT(30000, "d22fde5dd240ade16d3250eb0aa5d1c16dc7cb51c20484e05eb274911032b3fa");
|
||||
ADD_CHECKPOINT(40000, "aee0d642322542ba069cb1c58ab2acd3560f108d4682c3dc3cb15a54d442d91f");
|
||||
ADD_CHECKPOINT(50000, "5286ac2a0f39b3aefcba363cd71f2760bd1e0d763cbc81026ebdc3f80a86541f");
|
||||
ADD_CHECKPOINT(53666, "3f43f56f66ef0c43cf2fd14d0d28fa2aae0ef8f40716773511345750770f1255"); //Hard fork to v9
|
||||
ADD_CHECKPOINT(54500, "8ed3078b389c2b44add007803d741b58d3fbed2e1ba4139bda702152d8773c9b");
|
||||
ADD_CHECKPOINT(55000, "4b662ceccefc3247edb4d654dd610b8fb496e85b88a5de43cc2bdd28171b15ff");
|
||||
ADD_CHECKPOINT(57000, "08a79f09f12bb5d230b63963356a760d51618e526cfc636047a6f3798217c177");
|
||||
ADD_CHECKPOINT(59000, "180b51ee2c5fbcd4362eb7a29df9422481310dd77d10bccdf8930724c31e007e");
|
||||
ADD_CHECKPOINT(59900, "18cc0653ef39cb304c68045dba5eb6b885f936281cd939dea04d0e6c9cd4ae2e");
|
||||
ADD_CHECKPOINT(60000, "0f02aa57a63f79f63dafed9063abe228a37cb19f00430dc3168b8a8f4ae8016c");
|
||||
ADD_CHECKPOINT(61000, "509aca8c54eb5fe44623768757b6e890ae39d512478c75f614cbff3d91809350");
|
||||
ADD_CHECKPOINT(62000, "7fe91ad256c08dbd961e04738968be22fb481093fbfa7959bde7796ccceba0e2");
|
||||
ADD_CHECKPOINT(62150, "1a7c75f8ebeda0e20eb5877181eafd7db0fc887e3fed43e0b27ab2e7bccafd10");
|
||||
ADD_CHECKPOINT(62269, "4969555d60742afb93925fd96d83ac28f45e6e3c0e583c9fb3c92d9b2100d38f");
|
||||
ADD_CHECKPOINT(62405, "4d0ae890cf9f875f231c7069508ad28dc429d14814b52db114dfab7519a27584");
|
||||
ADD_CHECKPOINT(62419, "bd8bf5ac4c4fb07ab4d0d492bd1699def5c095ab6943ad3b63a89d1d8b1ce748");
|
||||
ADD_CHECKPOINT(62425, "41a922dba6f3906871b2ccaf31ec9c91033470c503959093dae796deda8940ea");
|
||||
ADD_CHECKPOINT(62479, "a2e8ff4205ba2980eb70921b0b21b5fc656ee273664ea94b860c68ca069b60dd");
|
||||
ADD_CHECKPOINT(62503, "25fa115962988b4b8f8cfd22744a3e653b22ead8c8468e64caf334fc75a97d08");
|
||||
ADD_CHECKPOINT(62550, "bde522a8a81c392c98c979434aa1dd9d20b4ca52230ba6ae0362872757808a48");
|
||||
ADD_CHECKPOINT(62629, "8368e1ce1d421f1fc969364558433e2b2363d0ffcb5f2d946633095e3e6734f5");
|
||||
ADD_CHECKPOINT(62720, "f871cddd75951e2fe24c282d2bd28396fc922ea519b354ace992a0162cb333ff");
|
||||
ADD_CHECKPOINT(62733, "8331dbeeaf23173d2235a062373a437befadb6492cceb7640127bf18653a9e61");
|
||||
ADD_CHECKPOINT(62877, "62d44adc05d7d4fd9d15239c5575612207beab0bcf2da49158bf89e365441ca1");
|
||||
ADD_CHECKPOINT(63469, "4e33a9343fc5b86661ec0affaeb5b5a065290602c02d817337e4a979fe5747d8"); //Hard fork to v10
|
||||
ADD_CHECKPOINT(69800, "5c65428a664738bc083d1ccd6a1b5ff4305f98e7633f44033816801429b33ce1");
|
||||
ADD_CHECKPOINT(75000, "e93492f79b5344e7edb31537ee65b3e908bf71110cff8188c0c62fefc015d342");
|
||||
ADD_CHECKPOINT(79500, "9bbfd6f2257ce9084de30179944b7695c9b918c9c03a8a63306ab6c5828ff857");
|
||||
ADD_CHECKPOINT(80920, "8fca818344f97ea3912557cbd8be659cf6a5bc1203514c27338e234251d72dfb");
|
||||
ADD_CHECKPOINT(81769, "41db9fef8d0ccfa78b570ee9525d4f55de77b510c3ae4b08a1d51b9aec9ade1d"); //Hard fork to v11
|
||||
ADD_CHECKPOINT(82069, "fdea800d23d0b2eea19dec8af31e453e883e8315c97e25c8bb3e88ca164f8369"); //Hard fork to v12
|
||||
ADD_CHECKPOINT(85000, "31d62ab75470b15aedee6674b78767b53f10951786e991c26035743c267b247a");
|
||||
ADD_CHECKPOINT(87000, "a788e5a7233ca2198ad6446ddc454b05d578e72253ed2bbca969527230f6eec2");
|
||||
ADD_CHECKPOINT(88200, "50bb43d5d563524d6b9f308a2483b80934bab2ab5250757558318834476f1cfb");
|
||||
ADD_CHECKPOINT(100000, "0c1f3bec32fe4ac9bd4b6ce1f4dfc52824f0947d756c9a1a453252c9423071f5");
|
||||
ADD_CHECKPOINT(111450, "d6eadc95607765b36afd8b9148eac20eb101632021348cd34371fc1d8b67f6b6");
|
||||
ADD_CHECKPOINT(114969, "b48245956b87f243048fd61021f4b3e5443e57eee7ff8ba4762d18926e80b80c"); //Hard fork to v13
|
||||
ADD_CHECKPOINT(114980, "3a96963b93154889bd7d59c8a60cf8005e864b930627616e51a4ad11cd9a3d50");
|
||||
|
||||
return true;
|
||||
}
|
||||
|
||||
@@ -253,22 +264,13 @@ namespace cryptonote
|
||||
std::vector<std::string> records;
|
||||
|
||||
// All four MoneroPulse domains have DNSSEC on and valid
|
||||
static const std::vector<std::string> dns_urls = { "checkpoints.moneropulse.se"
|
||||
, "checkpoints.moneropulse.org"
|
||||
, "checkpoints.moneropulse.net"
|
||||
, "checkpoints.moneropulse.co"
|
||||
static const std::vector<std::string> dns_urls = {
|
||||
};
|
||||
|
||||
static const std::vector<std::string> testnet_dns_urls = { "testpoints.moneropulse.se"
|
||||
, "testpoints.moneropulse.org"
|
||||
, "testpoints.moneropulse.net"
|
||||
, "testpoints.moneropulse.co"
|
||||
static const std::vector<std::string> testnet_dns_urls = {
|
||||
};
|
||||
|
||||
static const std::vector<std::string> stagenet_dns_urls = { "stagenetpoints.moneropulse.se"
|
||||
, "stagenetpoints.moneropulse.org"
|
||||
, "stagenetpoints.moneropulse.net"
|
||||
, "stagenetpoints.moneropulse.co"
|
||||
static const std::vector<std::string> stagenet_dns_urls = {
|
||||
};
|
||||
|
||||
if (!tools::dns_utils::load_txt_records_from_dns(records, nettype == TESTNET ? testnet_dns_urls : nettype == STAGENET ? stagenet_dns_urls : dns_urls))
|
||||
|
||||
@@ -102,8 +102,6 @@ get_builtin_ds(void)
|
||||
{
|
||||
static const char * const ds[] =
|
||||
{
|
||||
". IN DS 19036 8 2 49AAC11D7B6F6446702E54A1607371607A1A41855200FD2CE1CDDE32F24E8FB5\n",
|
||||
". IN DS 20326 8 2 E06D44B80B8F1D39A95C0B0D7C65D08458E880409BBC683457104237C7F8EC8D\n",
|
||||
NULL
|
||||
};
|
||||
return ds;
|
||||
|
||||
@@ -36,6 +36,7 @@
|
||||
#include "storages/http_abstract_invoke.h"
|
||||
#include "net/http_auth.h"
|
||||
#include "net/http_client.h"
|
||||
#include "net/net_ssl.h"
|
||||
#include "string_tools.h"
|
||||
|
||||
namespace tools
|
||||
@@ -49,11 +50,12 @@ namespace tools
|
||||
uint32_t ip
|
||||
, uint16_t port
|
||||
, boost::optional<epee::net_utils::http::login> user
|
||||
, epee::net_utils::ssl_options_t ssl_options
|
||||
)
|
||||
: m_http_client{}
|
||||
{
|
||||
m_http_client.set_server(
|
||||
epee::string_tools::get_ip_string_from_int32(ip), std::to_string(port), std::move(user)
|
||||
epee::string_tools::get_ip_string_from_int32(ip), std::to_string(port), std::move(user), std::move(ssl_options)
|
||||
);
|
||||
}
|
||||
|
||||
|
||||
@@ -46,10 +46,6 @@ namespace tools
|
||||
|
||||
// All four MoneroPulse domains have DNSSEC on and valid
|
||||
static const std::vector<std::string> dns_urls = {
|
||||
"updates.moneropulse.org",
|
||||
"updates.moneropulse.net",
|
||||
"updates.moneropulse.co",
|
||||
"updates.moneropulse.se"
|
||||
};
|
||||
|
||||
if (!tools::dns_utils::load_txt_records_from_dns(records, dns_urls))
|
||||
@@ -99,7 +95,7 @@ namespace tools
|
||||
|
||||
std::string get_update_url(const std::string &software, const std::string &subdir, const std::string &buildtag, const std::string &version, bool user)
|
||||
{
|
||||
const char *base = user ? "https://downloads.getmonero.org/" : "https://updates.getmonero.org/";
|
||||
const char *base = user ? "" : "";
|
||||
#ifdef _WIN32
|
||||
static const char *extension = strncmp(buildtag.c_str(), "install-", 8) ? ".zip" : ".exe";
|
||||
#else
|
||||
|
||||
@@ -46,6 +46,7 @@ set(crypto_sources
|
||||
random.c
|
||||
skein.c
|
||||
slow-hash.c
|
||||
rx-slow-hash.c
|
||||
CryptonightR_JIT.c
|
||||
tree-hash.c)
|
||||
|
||||
@@ -53,6 +54,8 @@ if(ARCH_ID STREQUAL "i386" OR ARCH_ID STREQUAL "x86_64" OR ARCH_ID STREQUAL "x86
|
||||
list(APPEND crypto_sources CryptonightR_template.S)
|
||||
endif()
|
||||
|
||||
include_directories(${RANDOMX_INCLUDE})
|
||||
|
||||
set(crypto_headers)
|
||||
|
||||
set(crypto_private_headers
|
||||
@@ -86,6 +89,7 @@ monero_add_library(cncrypto
|
||||
target_link_libraries(cncrypto
|
||||
PUBLIC
|
||||
epee
|
||||
randomx
|
||||
${Boost_SYSTEM_LIBRARY}
|
||||
${SODIUM_LIBRARY}
|
||||
PRIVATE
|
||||
|
||||
56
src/crypto/c_threads.h
Normal file
56
src/crypto/c_threads.h
Normal file
@@ -0,0 +1,56 @@
|
||||
// Copyright (c) 2019, The Monero Project
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without modification, are
|
||||
// permitted provided that the following conditions are met:
|
||||
//
|
||||
// 1. Redistributions of source code must retain the above copyright notice, this list of
|
||||
// conditions and the following disclaimer.
|
||||
//
|
||||
// 2. Redistributions in binary form must reproduce the above copyright notice, this list
|
||||
// of conditions and the following disclaimer in the documentation and/or other
|
||||
// materials provided with the distribution.
|
||||
//
|
||||
// 3. Neither the name of the copyright holder nor the names of its contributors may be
|
||||
// used to endorse or promote products derived from this software without specific
|
||||
// prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY
|
||||
// EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
|
||||
// MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL
|
||||
// THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL,
|
||||
// SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
|
||||
// PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
|
||||
// INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT,
|
||||
// STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF
|
||||
// THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
/* Brain-dead simple portability wrapper over thread APIs for C */
|
||||
#pragma once
|
||||
|
||||
#ifdef _WIN32
|
||||
#include <windows.h>
|
||||
#define CTHR_MUTEX_TYPE HANDLE
|
||||
#define CTHR_MUTEX_INIT NULL
|
||||
#define CTHR_MUTEX_LOCK(x) do { if (x == NULL) { \
|
||||
HANDLE p = CreateMutex(NULL, FALSE, NULL); \
|
||||
if (InterlockedCompareExchangePointer((PVOID*)&x, (PVOID)p, NULL) != NULL) \
|
||||
CloseHandle(p); \
|
||||
} WaitForSingleObject(x, INFINITE) == WAIT_FAILED; } while(0)
|
||||
#define CTHR_MUTEX_UNLOCK(x) (ReleaseMutex(x) == 0)
|
||||
#define CTHR_THREAD_TYPE HANDLE
|
||||
#define CTHR_THREAD_RTYPE void
|
||||
#define CTHR_THREAD_CREATE(thr, func, arg) thr = _beginthread(func, 0, arg)
|
||||
#define CTHR_THREAD_JOIN(thr) WaitForSingleObject(thr, INFINITE)
|
||||
#else
|
||||
#include <pthread.h>
|
||||
#define CTHR_MUTEX_TYPE pthread_mutex_t
|
||||
#define CTHR_MUTEX_INIT PTHREAD_MUTEX_INITIALIZER
|
||||
#define CTHR_MUTEX_LOCK(x) pthread_mutex_lock(&x)
|
||||
#define CTHR_MUTEX_UNLOCK(x) pthread_mutex_unlock(&x)
|
||||
#define CTHR_THREAD_TYPE pthread_t
|
||||
#define CTHR_THREAD_RTYPE void *
|
||||
#define CTHR_THREAD_CREATE(thr, func, arg) pthread_create(&thr, NULL, func, arg)
|
||||
#define CTHR_THREAD_JOIN(thr) pthread_join(thr, NULL)
|
||||
#endif
|
||||
@@ -87,3 +87,14 @@ void hash_extra_jh(const void *data, size_t length, char *hash);
|
||||
void hash_extra_skein(const void *data, size_t length, char *hash);
|
||||
|
||||
void tree_hash(const char (*hashes)[HASH_SIZE], size_t count, char *root_hash);
|
||||
|
||||
#define RX_BLOCK_VERSION 13
|
||||
void rx_slow_hash_allocate_state(void);
|
||||
void rx_slow_hash_free_state(void);
|
||||
uint64_t rx_seedheight(const uint64_t height);
|
||||
void rx_seedheights(const uint64_t height, uint64_t *seed_height, uint64_t *next_height);
|
||||
bool rx_needhash(const uint64_t height, uint64_t *seedheight);
|
||||
void rx_seedhash(const uint64_t seedheight, const char *hash, const int miners);
|
||||
void rx_slow_hash(const void *data, size_t length, char *hash, const int miners);
|
||||
void rx_alt_slowhash(const uint64_t mainheight, const uint64_t seedheight, const char *seedhash, const void *data, size_t length, char *hash);
|
||||
void rx_reorg(const uint64_t split_height);
|
||||
|
||||
349
src/crypto/rx-slow-hash.c
Normal file
349
src/crypto/rx-slow-hash.c
Normal file
@@ -0,0 +1,349 @@
|
||||
// Copyright (c) 2019, The Monero Project
|
||||
//
|
||||
// All rights reserved.
|
||||
//
|
||||
// Redistribution and use in source and binary forms, with or without modification, are
|
||||
// permitted provided that the following conditions are met:
|
||||
//
|
||||
// 1. Redistributions of source code must retain the above copyright notice, this list of
|
||||
// conditions and the following disclaimer.
|
||||
//
|
||||
// 2. Redistributions in binary form must reproduce the above copyright notice, this list
|
||||
// of conditions and the following disclaimer in the documentation and/or other
|
||||
// materials provided with the distribution.
|
||||
//
|
||||
// 3. Neither the name of the copyright holder nor the names of its contributors may be
|
||||
// used to endorse or promote products derived from this software without specific
|
||||
// prior written permission.
|
||||
//
|
||||
// THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY
|
||||
// EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
|
||||
// MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL
|
||||
// THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL,
|
||||
// SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
|
||||
// PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
|
||||
// INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT,
|
||||
// STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF
|
||||
// THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
|
||||
|
||||
#include <assert.h>
|
||||
#include <stddef.h>
|
||||
#include <stdint.h>
|
||||
#include <stdbool.h>
|
||||
#include <string.h>
|
||||
#include <stdio.h>
|
||||
#include <stdlib.h>
|
||||
#include <unistd.h>
|
||||
|
||||
#include "randomx.h"
|
||||
#include "c_threads.h"
|
||||
#include "hash-ops.h"
|
||||
|
||||
#if defined(_MSC_VER)
|
||||
#define THREADV __declspec(thread)
|
||||
#else
|
||||
#define THREADV __thread
|
||||
#endif
|
||||
|
||||
static CTHR_MUTEX_TYPE rx_mutex = CTHR_MUTEX_INIT;
|
||||
|
||||
typedef struct rx_state {
|
||||
volatile uint64_t rs_height;
|
||||
randomx_cache *rs_cache;
|
||||
} rx_state;
|
||||
|
||||
static rx_state rx_s[2];
|
||||
|
||||
static randomx_dataset *rx_dataset;
|
||||
THREADV int rx_s_toggle;
|
||||
THREADV randomx_vm *rx_vm = NULL;
|
||||
|
||||
static void local_abort(const char *msg)
|
||||
{
|
||||
fprintf(stderr, "%s\n", msg);
|
||||
#ifdef NDEBUG
|
||||
_exit(1);
|
||||
#else
|
||||
abort();
|
||||
#endif
|
||||
}
|
||||
|
||||
/**
|
||||
* @brief uses cpuid to determine if the CPU supports the AES instructions
|
||||
* @return true if the CPU supports AES, false otherwise
|
||||
*/
|
||||
|
||||
static inline int force_software_aes(void)
|
||||
{
|
||||
static int use = -1;
|
||||
|
||||
if (use != -1)
|
||||
return use;
|
||||
|
||||
const char *env = getenv("MONERO_USE_SOFTWARE_AES");
|
||||
if (!env) {
|
||||
use = 0;
|
||||
}
|
||||
else if (!strcmp(env, "0") || !strcmp(env, "no")) {
|
||||
use = 0;
|
||||
}
|
||||
else {
|
||||
use = 1;
|
||||
}
|
||||
return use;
|
||||
}
|
||||
|
||||
static void cpuid(int CPUInfo[4], int InfoType)
|
||||
{
|
||||
#if defined(__x86_64__)
|
||||
__asm __volatile__
|
||||
(
|
||||
"cpuid":
|
||||
"=a" (CPUInfo[0]),
|
||||
"=b" (CPUInfo[1]),
|
||||
"=c" (CPUInfo[2]),
|
||||
"=d" (CPUInfo[3]) :
|
||||
"a" (InfoType), "c" (0)
|
||||
);
|
||||
#endif
|
||||
}
|
||||
static inline int check_aes_hw(void)
|
||||
{
|
||||
#if defined(__x86_64__)
|
||||
int cpuid_results[4];
|
||||
static int supported = -1;
|
||||
|
||||
if(supported >= 0)
|
||||
return supported;
|
||||
|
||||
cpuid(cpuid_results,1);
|
||||
return supported = cpuid_results[2] & (1 << 25);
|
||||
#else
|
||||
return 0;
|
||||
#endif
|
||||
}
|
||||
|
||||
static volatile int use_rx_jit_flag = -1;
|
||||
|
||||
static inline int use_rx_jit(void)
|
||||
{
|
||||
#if defined(__x86_64__)
|
||||
|
||||
if (use_rx_jit_flag != -1)
|
||||
return use_rx_jit_flag;
|
||||
|
||||
const char *env = getenv("MONERO_USE_RX_JIT");
|
||||
if (!env) {
|
||||
use_rx_jit_flag = 1;
|
||||
}
|
||||
else if (!strcmp(env, "0") || !strcmp(env, "no")) {
|
||||
use_rx_jit_flag = 0;
|
||||
}
|
||||
else {
|
||||
use_rx_jit_flag = 1;
|
||||
}
|
||||
return use_rx_jit_flag;
|
||||
#else
|
||||
return 0;
|
||||
#endif
|
||||
}
|
||||
|
||||
#define SEEDHASH_EPOCH_BLOCKS 2048 /* Must be same as BLOCKS_SYNCHRONIZING_MAX_COUNT in cryptonote_config.h */
|
||||
#define SEEDHASH_EPOCH_LAG 64
|
||||
|
||||
void rx_reorg(const uint64_t split_height) {
|
||||
int i;
|
||||
CTHR_MUTEX_LOCK(rx_mutex);
|
||||
for (i=0; i<2; i++) {
|
||||
if (split_height < rx_s[i].rs_height)
|
||||
rx_s[i].rs_height = 1; /* set to an invalid seed height */
|
||||
}
|
||||
CTHR_MUTEX_UNLOCK(rx_mutex);
|
||||
}
|
||||
|
||||
uint64_t rx_seedheight(const uint64_t height) {
|
||||
uint64_t s_height = (height <= SEEDHASH_EPOCH_BLOCKS+SEEDHASH_EPOCH_LAG) ? 0 :
|
||||
(height - SEEDHASH_EPOCH_LAG - 1) & ~(SEEDHASH_EPOCH_BLOCKS-1);
|
||||
return s_height;
|
||||
}
|
||||
|
||||
void rx_seedheights(const uint64_t height, uint64_t *seedheight, uint64_t *nextheight) {
|
||||
*seedheight = rx_seedheight(height);
|
||||
*nextheight = rx_seedheight(height + SEEDHASH_EPOCH_LAG);
|
||||
}
|
||||
|
||||
bool rx_needhash(const uint64_t height, uint64_t *seedheight) {
|
||||
rx_state *rx_sp;
|
||||
uint64_t s_height = rx_seedheight(height);
|
||||
int toggle = (s_height & SEEDHASH_EPOCH_BLOCKS) != 0;
|
||||
bool ret;
|
||||
bool changed = (toggle != rx_s_toggle);
|
||||
*seedheight = s_height;
|
||||
rx_s_toggle = toggle;
|
||||
rx_sp = &rx_s[rx_s_toggle];
|
||||
ret = (rx_sp->rs_cache == NULL) || (rx_sp->rs_height != s_height);
|
||||
/* if cache is ok but we've flipped caches, reset vm */
|
||||
if (!ret && changed && rx_vm != NULL)
|
||||
randomx_vm_set_cache(rx_vm, rx_sp->rs_cache);
|
||||
return ret;
|
||||
}
|
||||
|
||||
typedef struct seedinfo {
|
||||
randomx_cache *si_cache;
|
||||
unsigned long si_start;
|
||||
unsigned long si_count;
|
||||
} seedinfo;
|
||||
|
||||
static CTHR_THREAD_RTYPE rx_seedthread(void *arg) {
|
||||
seedinfo *si = arg;
|
||||
randomx_init_dataset(rx_dataset, si->si_cache, si->si_start, si->si_count);
|
||||
return NULL;
|
||||
}
|
||||
|
||||
static void rx_initdata(randomx_cache *rs_cache, const int miners) {
|
||||
if (miners > 1) {
|
||||
unsigned long delta = randomx_dataset_item_count() / miners;
|
||||
unsigned long start = 0;
|
||||
int i;
|
||||
seedinfo *si;
|
||||
CTHR_THREAD_TYPE *st;
|
||||
si = malloc(miners * sizeof(seedinfo));
|
||||
if (si == NULL)
|
||||
local_abort("Couldn't allocate RandomWOW mining threadinfo");
|
||||
st = malloc(miners * sizeof(CTHR_THREAD_TYPE));
|
||||
if (st == NULL) {
|
||||
free(si);
|
||||
local_abort("Couldn't allocate RandomWOW mining threadlist");
|
||||
}
|
||||
for (i=0; i<miners-1; i++) {
|
||||
si[i].si_cache = rs_cache;
|
||||
si[i].si_start = start;
|
||||
si[i].si_count = delta;
|
||||
start += delta;
|
||||
}
|
||||
si[i].si_cache = rs_cache;
|
||||
si[i].si_start = start;
|
||||
si[i].si_count = randomx_dataset_item_count() - start;
|
||||
for (i=1; i<miners; i++) {
|
||||
CTHR_THREAD_CREATE(st[i], rx_seedthread, &si[i]);
|
||||
}
|
||||
randomx_init_dataset(rx_dataset, rs_cache, 0, si[0].si_count);
|
||||
for (i=1; i<miners; i++) {
|
||||
CTHR_THREAD_JOIN(st[i]);
|
||||
}
|
||||
free(st);
|
||||
free(si);
|
||||
} else {
|
||||
randomx_init_dataset(rx_dataset, rs_cache, 0, randomx_dataset_item_count());
|
||||
}
|
||||
}
|
||||
|
||||
static void rx_seedhash_int(rx_state *rx_sp, const uint64_t height, const char *hash, const int miners) {
|
||||
randomx_flags flags = RANDOMX_FLAG_DEFAULT;
|
||||
randomx_cache *cache;
|
||||
CTHR_MUTEX_LOCK(rx_mutex);
|
||||
cache = rx_sp->rs_cache;
|
||||
if (rx_sp->rs_height != height || cache == NULL) {
|
||||
if (use_rx_jit())
|
||||
flags |= RANDOMX_FLAG_JIT;
|
||||
if (cache == NULL) {
|
||||
cache = randomx_alloc_cache(flags | RANDOMX_FLAG_LARGE_PAGES);
|
||||
if (cache == NULL)
|
||||
cache = randomx_alloc_cache(flags);
|
||||
if (cache == NULL)
|
||||
local_abort("Couldn't allocate RandomWOW cache");
|
||||
}
|
||||
randomx_init_cache(cache, hash, 32);
|
||||
if (miners && rx_dataset != NULL)
|
||||
rx_initdata(cache, miners);
|
||||
rx_sp->rs_height = height;
|
||||
if (rx_sp->rs_cache == NULL)
|
||||
rx_sp->rs_cache = cache;
|
||||
}
|
||||
CTHR_MUTEX_UNLOCK(rx_mutex);
|
||||
if (rx_vm != NULL)
|
||||
randomx_vm_set_cache(rx_vm, rx_sp->rs_cache);
|
||||
}
|
||||
|
||||
void rx_seedhash(const uint64_t height, const char *hash, const int miners) {
|
||||
rx_state *rx_sp = &rx_s[rx_s_toggle];
|
||||
rx_seedhash_int(rx_sp, height, hash, miners);
|
||||
}
|
||||
|
||||
static char rx_althash[32]; // seedhash for alternate blocks
|
||||
|
||||
void rx_alt_slowhash(const uint64_t mainheight, const uint64_t seedheight, const char *seedhash, const void *data, size_t length, char *hash) {
|
||||
uint64_t s_height = rx_seedheight(mainheight);
|
||||
int alt_toggle = (s_height & SEEDHASH_EPOCH_BLOCKS) == 0;
|
||||
rx_state *rx_sp = &rx_s[alt_toggle];
|
||||
if (rx_sp->rs_height != seedheight || rx_sp->rs_cache == NULL || memcmp(hash, rx_althash, sizeof(rx_althash))) {
|
||||
memcpy(rx_althash, seedhash, sizeof(rx_althash));
|
||||
rx_sp->rs_height = 1;
|
||||
rx_seedhash_int(rx_sp, seedheight, seedhash, 0);
|
||||
}
|
||||
if (rx_vm == NULL) {
|
||||
randomx_flags flags = RANDOMX_FLAG_DEFAULT;
|
||||
if (use_rx_jit())
|
||||
flags |= RANDOMX_FLAG_JIT;
|
||||
if(!force_software_aes() && check_aes_hw())
|
||||
flags |= RANDOMX_FLAG_HARD_AES;
|
||||
rx_vm = randomx_create_vm(flags | RANDOMX_FLAG_LARGE_PAGES, rx_sp->rs_cache, NULL);
|
||||
if(rx_vm == NULL) //large pages failed
|
||||
rx_vm = randomx_create_vm(flags, rx_sp->rs_cache, NULL);
|
||||
if(rx_vm == NULL) {//fallback if everything fails
|
||||
flags = RANDOMX_FLAG_DEFAULT;
|
||||
rx_vm = randomx_create_vm(flags, rx_sp->rs_cache, NULL);
|
||||
}
|
||||
if (rx_vm == NULL)
|
||||
local_abort("Couldn't allocate RandomWOW VM");
|
||||
}
|
||||
randomx_calculate_hash(rx_vm, data, length, hash);
|
||||
}
|
||||
|
||||
void rx_slow_hash(const void *data, size_t length, char *hash, int miners) {
|
||||
if (rx_vm == NULL) {
|
||||
rx_state *rx_sp = &rx_s[rx_s_toggle];
|
||||
randomx_flags flags = RANDOMX_FLAG_DEFAULT;
|
||||
if (use_rx_jit())
|
||||
flags |= RANDOMX_FLAG_JIT;
|
||||
if(!force_software_aes() && check_aes_hw())
|
||||
flags |= RANDOMX_FLAG_HARD_AES;
|
||||
if (miners) {
|
||||
if (rx_dataset == NULL) {
|
||||
CTHR_MUTEX_LOCK(rx_mutex);
|
||||
if (rx_dataset == NULL) {
|
||||
rx_dataset = randomx_alloc_dataset(RANDOMX_FLAG_LARGE_PAGES);
|
||||
if (rx_dataset == NULL)
|
||||
rx_dataset = randomx_alloc_dataset(RANDOMX_FLAG_DEFAULT);
|
||||
if (rx_dataset != NULL)
|
||||
rx_initdata(rx_sp->rs_cache, miners);
|
||||
}
|
||||
CTHR_MUTEX_UNLOCK(rx_mutex);
|
||||
}
|
||||
if (rx_dataset != NULL)
|
||||
flags |= RANDOMX_FLAG_FULL_MEM;
|
||||
else
|
||||
miners = 0;
|
||||
}
|
||||
rx_vm = randomx_create_vm(flags | RANDOMX_FLAG_LARGE_PAGES, rx_sp->rs_cache, rx_dataset);
|
||||
if(rx_vm == NULL) //large pages failed
|
||||
rx_vm = randomx_create_vm(flags, rx_sp->rs_cache, rx_dataset);
|
||||
if(rx_vm == NULL) {//fallback if everything fails
|
||||
flags = RANDOMX_FLAG_DEFAULT | (miners ? RANDOMX_FLAG_FULL_MEM : 0);
|
||||
rx_vm = randomx_create_vm(flags, rx_sp->rs_cache, rx_dataset);
|
||||
}
|
||||
if (rx_vm == NULL)
|
||||
local_abort("Couldn't allocate RandomWOW VM");
|
||||
}
|
||||
randomx_calculate_hash(rx_vm, data, length, hash);
|
||||
}
|
||||
|
||||
void rx_slow_hash_allocate_state(void) {
|
||||
}
|
||||
|
||||
void rx_slow_hash_free_state(void) {
|
||||
if (rx_vm != NULL) {
|
||||
randomx_destroy_vm(rx_vm);
|
||||
rx_vm = NULL;
|
||||
}
|
||||
}
|
||||
@@ -40,10 +40,6 @@
|
||||
#include "oaes_lib.h"
|
||||
#include "variant2_int_sqrt.h"
|
||||
#include "variant4_random_math.h"
|
||||
#include "CryptonightR_JIT.h"
|
||||
|
||||
#include <errno.h>
|
||||
#include <string.h>
|
||||
|
||||
#define MEMORY (1 << 21) // 2MB scratchpad
|
||||
#define ITER (1 << 20)
|
||||
@@ -55,41 +51,6 @@
|
||||
extern void aesb_single_round(const uint8_t *in, uint8_t *out, const uint8_t *expandedKey);
|
||||
extern void aesb_pseudo_round(const uint8_t *in, uint8_t *out, const uint8_t *expandedKey);
|
||||
|
||||
static void local_abort(const char *msg)
|
||||
{
|
||||
fprintf(stderr, "%s\n", msg);
|
||||
#ifdef NDEBUG
|
||||
_exit(1);
|
||||
#else
|
||||
abort();
|
||||
#endif
|
||||
}
|
||||
|
||||
volatile int use_v4_jit_flag = -1;
|
||||
|
||||
static inline int use_v4_jit(void)
|
||||
{
|
||||
#if defined(__x86_64__)
|
||||
|
||||
if (use_v4_jit_flag != -1)
|
||||
return use_v4_jit_flag;
|
||||
|
||||
const char *env = getenv("MONERO_USE_CNV4_JIT");
|
||||
if (!env) {
|
||||
use_v4_jit_flag = 1;
|
||||
}
|
||||
else if (!strcmp(env, "0") || !strcmp(env, "no")) {
|
||||
use_v4_jit_flag = 0;
|
||||
}
|
||||
else {
|
||||
use_v4_jit_flag = 1;
|
||||
}
|
||||
return use_v4_jit_flag;
|
||||
#else
|
||||
return 0;
|
||||
#endif
|
||||
}
|
||||
|
||||
#define VARIANT1_1(p) \
|
||||
do if (variant == 1) \
|
||||
{ \
|
||||
@@ -156,74 +117,48 @@ static inline int use_v4_jit(void)
|
||||
#define VARIANT2_SHUFFLE_ADD_SSE2(base_ptr, offset) \
|
||||
do if (variant >= 2) \
|
||||
{ \
|
||||
__m128i chunk1 = _mm_load_si128((__m128i *)((base_ptr) + ((offset) ^ 0x10))); \
|
||||
const __m128i chunk1 = _mm_load_si128((__m128i *)((base_ptr) + ((offset) ^ 0x10))); \
|
||||
const __m128i chunk2 = _mm_load_si128((__m128i *)((base_ptr) + ((offset) ^ 0x20))); \
|
||||
const __m128i chunk3 = _mm_load_si128((__m128i *)((base_ptr) + ((offset) ^ 0x30))); \
|
||||
_mm_store_si128((__m128i *)((base_ptr) + ((offset) ^ 0x10)), _mm_add_epi64(chunk3, _b1)); \
|
||||
_mm_store_si128((__m128i *)((base_ptr) + ((offset) ^ 0x20)), _mm_add_epi64(chunk1, _b)); \
|
||||
_mm_store_si128((__m128i *)((base_ptr) + ((offset) ^ 0x30)), _mm_add_epi64(chunk2, _a)); \
|
||||
if (variant >= 4) \
|
||||
{ \
|
||||
chunk1 = _mm_xor_si128(chunk1, chunk2); \
|
||||
_c = _mm_xor_si128(_c, chunk3); \
|
||||
_c = _mm_xor_si128(_c, chunk1); \
|
||||
} \
|
||||
} while (0)
|
||||
|
||||
#define VARIANT2_SHUFFLE_ADD_NEON(base_ptr, offset) \
|
||||
do if (variant >= 2) \
|
||||
{ \
|
||||
uint64x2_t chunk1 = vld1q_u64(U64((base_ptr) + ((offset) ^ 0x10))); \
|
||||
const uint64x2_t chunk1 = vld1q_u64(U64((base_ptr) + ((offset) ^ 0x10))); \
|
||||
const uint64x2_t chunk2 = vld1q_u64(U64((base_ptr) + ((offset) ^ 0x20))); \
|
||||
const uint64x2_t chunk3 = vld1q_u64(U64((base_ptr) + ((offset) ^ 0x30))); \
|
||||
vst1q_u64(U64((base_ptr) + ((offset) ^ 0x10)), vaddq_u64(chunk3, vreinterpretq_u64_u8(_b1))); \
|
||||
vst1q_u64(U64((base_ptr) + ((offset) ^ 0x20)), vaddq_u64(chunk1, vreinterpretq_u64_u8(_b))); \
|
||||
vst1q_u64(U64((base_ptr) + ((offset) ^ 0x30)), vaddq_u64(chunk2, vreinterpretq_u64_u8(_a))); \
|
||||
if (variant >= 4) \
|
||||
{ \
|
||||
chunk1 = veorq_u64(chunk1, chunk2); \
|
||||
_c = vreinterpretq_u8_u64(veorq_u64(vreinterpretq_u64_u8(_c), chunk3)); \
|
||||
_c = vreinterpretq_u8_u64(veorq_u64(vreinterpretq_u64_u8(_c), chunk1)); \
|
||||
} \
|
||||
} while (0)
|
||||
|
||||
#define VARIANT2_PORTABLE_SHUFFLE_ADD(out, a_, base_ptr, offset) \
|
||||
#define VARIANT2_PORTABLE_SHUFFLE_ADD(base_ptr, offset) \
|
||||
do if (variant >= 2) \
|
||||
{ \
|
||||
uint64_t* chunk1 = U64((base_ptr) + ((offset) ^ 0x10)); \
|
||||
uint64_t* chunk2 = U64((base_ptr) + ((offset) ^ 0x20)); \
|
||||
uint64_t* chunk3 = U64((base_ptr) + ((offset) ^ 0x30)); \
|
||||
\
|
||||
uint64_t chunk1_old[2] = { SWAP64LE(chunk1[0]), SWAP64LE(chunk1[1]) }; \
|
||||
const uint64_t chunk2_old[2] = { SWAP64LE(chunk2[0]), SWAP64LE(chunk2[1]) }; \
|
||||
const uint64_t chunk3_old[2] = { SWAP64LE(chunk3[0]), SWAP64LE(chunk3[1]) }; \
|
||||
const uint64_t chunk1_old[2] = { chunk1[0], chunk1[1] }; \
|
||||
\
|
||||
uint64_t b1[2]; \
|
||||
memcpy_swap64le(b1, b + 16, 2); \
|
||||
chunk1[0] = SWAP64LE(chunk3_old[0] + b1[0]); \
|
||||
chunk1[1] = SWAP64LE(chunk3_old[1] + b1[1]); \
|
||||
chunk1[0] = SWAP64LE(SWAP64LE(chunk3[0]) + b1[0]); \
|
||||
chunk1[1] = SWAP64LE(SWAP64LE(chunk3[1]) + b1[1]); \
|
||||
\
|
||||
uint64_t a0[2]; \
|
||||
memcpy_swap64le(a0, a_, 2); \
|
||||
chunk3[0] = SWAP64LE(chunk2_old[0] + a0[0]); \
|
||||
chunk3[1] = SWAP64LE(chunk2_old[1] + a0[1]); \
|
||||
memcpy_swap64le(a0, a, 2); \
|
||||
chunk3[0] = SWAP64LE(SWAP64LE(chunk2[0]) + a0[0]); \
|
||||
chunk3[1] = SWAP64LE(SWAP64LE(chunk2[1]) + a0[1]); \
|
||||
\
|
||||
uint64_t b0[2]; \
|
||||
memcpy_swap64le(b0, b, 2); \
|
||||
chunk2[0] = SWAP64LE(chunk1_old[0] + b0[0]); \
|
||||
chunk2[0] = SWAP64LE(SWAP64LE(chunk1_old[0]) + b0[0]); \
|
||||
chunk2[1] = SWAP64LE(SWAP64LE(chunk1_old[1]) + b0[1]); \
|
||||
if (variant >= 4) \
|
||||
{ \
|
||||
uint64_t out_copy[2]; \
|
||||
memcpy_swap64le(out_copy, out, 2); \
|
||||
chunk1_old[0] ^= chunk2_old[0]; \
|
||||
chunk1_old[1] ^= chunk2_old[1]; \
|
||||
out_copy[0] ^= chunk3_old[0]; \
|
||||
out_copy[1] ^= chunk3_old[1]; \
|
||||
out_copy[0] ^= chunk1_old[0]; \
|
||||
out_copy[1] ^= chunk1_old[1]; \
|
||||
memcpy_swap64le(out, out_copy, 2); \
|
||||
} \
|
||||
} while (0)
|
||||
|
||||
#define VARIANT2_INTEGER_MATH_DIVISION_STEP(b, ptr) \
|
||||
@@ -266,18 +201,18 @@ static inline int use_v4_jit(void)
|
||||
#endif
|
||||
|
||||
#define VARIANT2_2_PORTABLE() \
|
||||
if (variant == 2 || variant == 3) { \
|
||||
if (variant >= 2) { \
|
||||
xor_blocks(long_state + (j ^ 0x10), d); \
|
||||
xor_blocks(d, long_state + (j ^ 0x20)); \
|
||||
}
|
||||
|
||||
#define VARIANT2_2() \
|
||||
do if (variant == 2 || variant == 3) \
|
||||
do if (variant >= 2) \
|
||||
{ \
|
||||
*U64(local_hp_state + (j ^ 0x10)) ^= SWAP64LE(hi); \
|
||||
*(U64(local_hp_state + (j ^ 0x10)) + 1) ^= SWAP64LE(lo); \
|
||||
hi ^= SWAP64LE(*U64(local_hp_state + (j ^ 0x20))); \
|
||||
lo ^= SWAP64LE(*(U64(local_hp_state + (j ^ 0x20)) + 1)); \
|
||||
*U64(hp_state + (j ^ 0x10)) ^= SWAP64LE(hi); \
|
||||
*(U64(hp_state + (j ^ 0x10)) + 1) ^= SWAP64LE(lo); \
|
||||
hi ^= SWAP64LE(*U64(hp_state + (j ^ 0x20))); \
|
||||
lo ^= SWAP64LE(*(U64(hp_state + (j ^ 0x20)) + 1)); \
|
||||
} while (0)
|
||||
|
||||
#define V4_REG_LOAD(dst, src) \
|
||||
@@ -290,56 +225,34 @@ static inline int use_v4_jit(void)
|
||||
} while (0)
|
||||
|
||||
#define VARIANT4_RANDOM_MATH_INIT() \
|
||||
v4_reg r[9]; \
|
||||
struct V4_Instruction code[NUM_INSTRUCTIONS_MAX + 1]; \
|
||||
int jit = use_v4_jit(); \
|
||||
v4_reg r[8]; \
|
||||
struct V4_Instruction code[TOTAL_LATENCY * ALU_COUNT + 1]; \
|
||||
do if (variant >= 4) \
|
||||
{ \
|
||||
for (int i = 0; i < 4; ++i) \
|
||||
V4_REG_LOAD(r + i, (uint8_t*)(state.hs.w + 12) + sizeof(v4_reg) * i); \
|
||||
v4_random_math_init(code, height); \
|
||||
if (jit) \
|
||||
{ \
|
||||
int ret = v4_generate_JIT_code(code, hp_jitfunc, 4096); \
|
||||
if (ret < 0) \
|
||||
local_abort("Error generating CryptonightR code"); \
|
||||
} \
|
||||
} while (0)
|
||||
|
||||
#define VARIANT4_RANDOM_MATH(a, b, r, _b, _b1) \
|
||||
do if (variant >= 4) \
|
||||
{ \
|
||||
uint64_t t[2]; \
|
||||
memcpy(t, b, sizeof(uint64_t)); \
|
||||
uint64_t t; \
|
||||
memcpy(&t, b, sizeof(uint64_t)); \
|
||||
\
|
||||
if (sizeof(v4_reg) == sizeof(uint32_t)) \
|
||||
t[0] ^= SWAP64LE((r[0] + r[1]) | ((uint64_t)(r[2] + r[3]) << 32)); \
|
||||
t ^= SWAP64LE((r[0] + r[1]) | ((uint64_t)(r[2] + r[3]) << 32)); \
|
||||
else \
|
||||
t[0] ^= SWAP64LE((r[0] + r[1]) ^ (r[2] + r[3])); \
|
||||
t ^= SWAP64LE((r[0] + r[1]) ^ (r[2] + r[3])); \
|
||||
\
|
||||
memcpy(b, t, sizeof(uint64_t)); \
|
||||
memcpy(b, &t, sizeof(uint64_t)); \
|
||||
\
|
||||
V4_REG_LOAD(r + 4, a); \
|
||||
V4_REG_LOAD(r + 5, (uint64_t*)(a) + 1); \
|
||||
V4_REG_LOAD(r + 6, _b); \
|
||||
V4_REG_LOAD(r + 7, _b1); \
|
||||
V4_REG_LOAD(r + 8, (uint64_t*)(_b1) + 1); \
|
||||
\
|
||||
if (jit) \
|
||||
(*hp_jitfunc)(r); \
|
||||
else \
|
||||
v4_random_math(code, r); \
|
||||
\
|
||||
memcpy(t, a, sizeof(uint64_t) * 2); \
|
||||
\
|
||||
if (sizeof(v4_reg) == sizeof(uint32_t)) { \
|
||||
t[0] ^= SWAP64LE(r[2] | ((uint64_t)(r[3]) << 32)); \
|
||||
t[1] ^= SWAP64LE(r[0] | ((uint64_t)(r[1]) << 32)); \
|
||||
} else { \
|
||||
t[0] ^= SWAP64LE(r[2] ^ r[3]); \
|
||||
t[1] ^= SWAP64LE(r[0] ^ r[1]); \
|
||||
} \
|
||||
memcpy(a, t, sizeof(uint64_t) * 2); \
|
||||
v4_random_math(code, r); \
|
||||
} while (0)
|
||||
|
||||
|
||||
@@ -405,7 +318,7 @@ static inline int use_v4_jit(void)
|
||||
|
||||
#define pre_aes() \
|
||||
j = state_index(a); \
|
||||
_c = _mm_load_si128(R128(&local_hp_state[j])); \
|
||||
_c = _mm_load_si128(R128(&hp_state[j])); \
|
||||
_a = _mm_load_si128(R128(a)); \
|
||||
|
||||
/*
|
||||
@@ -418,20 +331,20 @@ static inline int use_v4_jit(void)
|
||||
* This code is based upon an optimized implementation by dga.
|
||||
*/
|
||||
#define post_aes() \
|
||||
VARIANT2_SHUFFLE_ADD_SSE2(local_hp_state, j); \
|
||||
VARIANT2_SHUFFLE_ADD_SSE2(hp_state, j); \
|
||||
_mm_store_si128(R128(c), _c); \
|
||||
_mm_store_si128(R128(&local_hp_state[j]), _mm_xor_si128(_b, _c)); \
|
||||
VARIANT1_1(&local_hp_state[j]); \
|
||||
_mm_store_si128(R128(&hp_state[j]), _mm_xor_si128(_b, _c)); \
|
||||
VARIANT1_1(&hp_state[j]); \
|
||||
j = state_index(c); \
|
||||
p = U64(&local_hp_state[j]); \
|
||||
p = U64(&hp_state[j]); \
|
||||
b[0] = p[0]; b[1] = p[1]; \
|
||||
VARIANT2_INTEGER_MATH_SSE2(b, c); \
|
||||
VARIANT4_RANDOM_MATH(a, b, r, &_b, &_b1); \
|
||||
__mul(); \
|
||||
VARIANT2_2(); \
|
||||
VARIANT2_SHUFFLE_ADD_SSE2(local_hp_state, j); \
|
||||
VARIANT2_SHUFFLE_ADD_SSE2(hp_state, j); \
|
||||
a[0] += hi; a[1] += lo; \
|
||||
p = U64(&local_hp_state[j]); \
|
||||
p = U64(&hp_state[j]); \
|
||||
p[0] = a[0]; p[1] = a[1]; \
|
||||
a[0] ^= b[0]; a[1] ^= b[1]; \
|
||||
VARIANT1_2(p + 1); \
|
||||
@@ -458,9 +371,6 @@ union cn_slow_hash_state
|
||||
|
||||
THREADV uint8_t *hp_state = NULL;
|
||||
THREADV int hp_allocated = 0;
|
||||
THREADV v4_random_math_JIT_func hp_jitfunc = NULL;
|
||||
THREADV uint8_t *hp_jitfunc_memory = NULL;
|
||||
THREADV int hp_jitfunc_allocated = 0;
|
||||
|
||||
#if defined(_MSC_VER)
|
||||
#define cpuid(info,x) __cpuidex(info,x,0)
|
||||
@@ -743,7 +653,7 @@ BOOL SetLockPagesPrivilege(HANDLE hProcess, BOOL bEnable)
|
||||
* the allocated buffer.
|
||||
*/
|
||||
|
||||
void slow_hash_allocate_state(void)
|
||||
void cn_slow_hash_allocate_state(void)
|
||||
{
|
||||
if(hp_state != NULL)
|
||||
return;
|
||||
@@ -756,10 +666,10 @@ void slow_hash_allocate_state(void)
|
||||
#if defined(__APPLE__) || defined(__FreeBSD__) || defined(__OpenBSD__) || \
|
||||
defined(__DragonFly__) || defined(__NetBSD__)
|
||||
hp_state = mmap(0, MEMORY, PROT_READ | PROT_WRITE,
|
||||
MAP_PRIVATE | MAP_ANON, -1, 0);
|
||||
MAP_PRIVATE | MAP_ANON, 0, 0);
|
||||
#else
|
||||
hp_state = mmap(0, MEMORY, PROT_READ | PROT_WRITE,
|
||||
MAP_PRIVATE | MAP_ANONYMOUS | MAP_HUGETLB, -1, 0);
|
||||
MAP_PRIVATE | MAP_ANONYMOUS | MAP_HUGETLB, 0, 0);
|
||||
#endif
|
||||
if(hp_state == MAP_FAILED)
|
||||
hp_state = NULL;
|
||||
@@ -770,42 +680,13 @@ void slow_hash_allocate_state(void)
|
||||
hp_allocated = 0;
|
||||
hp_state = (uint8_t *) malloc(MEMORY);
|
||||
}
|
||||
|
||||
|
||||
#if defined(_MSC_VER) || defined(__MINGW32__)
|
||||
hp_jitfunc_memory = (uint8_t *) VirtualAlloc(hp_jitfunc_memory, 4096 + 4095,
|
||||
MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE);
|
||||
#else
|
||||
#if defined(__APPLE__) || defined(__FreeBSD__) || defined(__OpenBSD__) || \
|
||||
defined(__DragonFly__) || defined(__NetBSD__)
|
||||
#ifdef __NetBSD__
|
||||
#define RESERVED_FLAGS PROT_MPROTECT(PROT_EXEC)
|
||||
#else
|
||||
#define RESERVED_FLAGS 0
|
||||
#endif
|
||||
hp_jitfunc_memory = mmap(0, 4096 + 4096, PROT_READ | PROT_WRITE | RESERVED_FLAGS,
|
||||
MAP_PRIVATE | MAP_ANON, -1, 0);
|
||||
#else
|
||||
hp_jitfunc_memory = mmap(0, 4096 + 4096, PROT_READ | PROT_WRITE | PROT_EXEC,
|
||||
MAP_PRIVATE | MAP_ANONYMOUS, -1, 0);
|
||||
#endif
|
||||
if(hp_jitfunc_memory == MAP_FAILED)
|
||||
hp_jitfunc_memory = NULL;
|
||||
#endif
|
||||
hp_jitfunc_allocated = 1;
|
||||
if (hp_jitfunc_memory == NULL)
|
||||
{
|
||||
hp_jitfunc_allocated = 0;
|
||||
hp_jitfunc_memory = malloc(4096 + 4095);
|
||||
}
|
||||
hp_jitfunc = (v4_random_math_JIT_func)((size_t)(hp_jitfunc_memory + 4095) & ~4095);
|
||||
}
|
||||
|
||||
/**
|
||||
*@brief frees the state allocated by slow_hash_allocate_state
|
||||
*/
|
||||
|
||||
void slow_hash_free_state(void)
|
||||
void cn_slow_hash_free_state(void)
|
||||
{
|
||||
if(hp_state == NULL)
|
||||
return;
|
||||
@@ -821,22 +702,8 @@ void slow_hash_free_state(void)
|
||||
#endif
|
||||
}
|
||||
|
||||
if(!hp_jitfunc_allocated)
|
||||
free(hp_jitfunc_memory);
|
||||
else
|
||||
{
|
||||
#if defined(_MSC_VER) || defined(__MINGW32__)
|
||||
VirtualFree(hp_jitfunc_memory, 0, MEM_RELEASE);
|
||||
#else
|
||||
munmap(hp_jitfunc_memory, 4096 + 4095);
|
||||
#endif
|
||||
}
|
||||
|
||||
hp_state = NULL;
|
||||
hp_allocated = 0;
|
||||
hp_jitfunc = NULL;
|
||||
hp_jitfunc_memory = NULL;
|
||||
hp_jitfunc_allocated = 0;
|
||||
}
|
||||
|
||||
/**
|
||||
@@ -893,11 +760,7 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
|
||||
// this isn't supposed to happen, but guard against it for now.
|
||||
if(hp_state == NULL)
|
||||
slow_hash_allocate_state();
|
||||
|
||||
// locals to avoid constant TLS dereferencing
|
||||
uint8_t *local_hp_state = hp_state;
|
||||
v4_random_math_JIT_func local_hp_jitfunc = hp_jitfunc;
|
||||
cn_slow_hash_allocate_state();
|
||||
|
||||
/* CryptoNight Step 1: Use Keccak1600 to initialize the 'state' (and 'text') buffers from the data. */
|
||||
if (prehashed) {
|
||||
@@ -921,7 +784,7 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
for(i = 0; i < MEMORY / INIT_SIZE_BYTE; i++)
|
||||
{
|
||||
aes_pseudo_round(text, text, expandedKey, INIT_SIZE_BLK);
|
||||
memcpy(&local_hp_state[i * INIT_SIZE_BYTE], text, INIT_SIZE_BYTE);
|
||||
memcpy(&hp_state[i * INIT_SIZE_BYTE], text, INIT_SIZE_BYTE);
|
||||
}
|
||||
}
|
||||
else
|
||||
@@ -933,7 +796,7 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
for(j = 0; j < INIT_SIZE_BLK; j++)
|
||||
aesb_pseudo_round(&text[AES_BLOCK_SIZE * j], &text[AES_BLOCK_SIZE * j], aes_ctx->key->exp_data);
|
||||
|
||||
memcpy(&local_hp_state[i * INIT_SIZE_BYTE], text, INIT_SIZE_BYTE);
|
||||
memcpy(&hp_state[i * INIT_SIZE_BYTE], text, INIT_SIZE_BYTE);
|
||||
}
|
||||
}
|
||||
|
||||
@@ -981,7 +844,7 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
for(i = 0; i < MEMORY / INIT_SIZE_BYTE; i++)
|
||||
{
|
||||
// add the xor to the pseudo round
|
||||
aes_pseudo_round_xor(text, text, expandedKey, &local_hp_state[i * INIT_SIZE_BYTE], INIT_SIZE_BLK);
|
||||
aes_pseudo_round_xor(text, text, expandedKey, &hp_state[i * INIT_SIZE_BYTE], INIT_SIZE_BLK);
|
||||
}
|
||||
}
|
||||
else
|
||||
@@ -991,7 +854,7 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
{
|
||||
for(j = 0; j < INIT_SIZE_BLK; j++)
|
||||
{
|
||||
xor_blocks(&text[j * AES_BLOCK_SIZE], &local_hp_state[i * INIT_SIZE_BYTE + j * AES_BLOCK_SIZE]);
|
||||
xor_blocks(&text[j * AES_BLOCK_SIZE], &hp_state[i * INIT_SIZE_BYTE + j * AES_BLOCK_SIZE]);
|
||||
aesb_pseudo_round(&text[AES_BLOCK_SIZE * j], &text[AES_BLOCK_SIZE * j], aes_ctx->key->exp_data);
|
||||
}
|
||||
}
|
||||
@@ -1011,13 +874,13 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
}
|
||||
|
||||
#elif !defined NO_AES && (defined(__arm__) || defined(__aarch64__))
|
||||
void slow_hash_allocate_state(void)
|
||||
void cn_slow_hash_allocate_state(void)
|
||||
{
|
||||
// Do nothing, this is just to maintain compatibility with the upgraded slow-hash.c
|
||||
return;
|
||||
}
|
||||
|
||||
void slow_hash_free_state(void)
|
||||
void cn_slow_hash_free_state(void)
|
||||
{
|
||||
// As above
|
||||
return;
|
||||
@@ -1035,8 +898,6 @@ void slow_hash_free_state(void)
|
||||
|
||||
#define U64(x) ((uint64_t *) (x))
|
||||
|
||||
#define hp_jitfunc ((v4_random_math_JIT_func)NULL)
|
||||
|
||||
STATIC INLINE void xor64(uint64_t *a, const uint64_t b)
|
||||
{
|
||||
*a ^= b;
|
||||
@@ -1071,24 +932,24 @@ union cn_slow_hash_state
|
||||
|
||||
#define pre_aes() \
|
||||
j = state_index(a); \
|
||||
_c = vld1q_u8(&local_hp_state[j]); \
|
||||
_c = vld1q_u8(&hp_state[j]); \
|
||||
_a = vld1q_u8((const uint8_t *)a); \
|
||||
|
||||
#define post_aes() \
|
||||
VARIANT2_SHUFFLE_ADD_NEON(local_hp_state, j); \
|
||||
VARIANT2_SHUFFLE_ADD_NEON(hp_state, j); \
|
||||
vst1q_u8((uint8_t *)c, _c); \
|
||||
vst1q_u8(&local_hp_state[j], veorq_u8(_b, _c)); \
|
||||
VARIANT1_1(&local_hp_state[j]); \
|
||||
vst1q_u8(&hp_state[j], veorq_u8(_b, _c)); \
|
||||
VARIANT1_1(&hp_state[j]); \
|
||||
j = state_index(c); \
|
||||
p = U64(&local_hp_state[j]); \
|
||||
p = U64(&hp_state[j]); \
|
||||
b[0] = p[0]; b[1] = p[1]; \
|
||||
VARIANT2_PORTABLE_INTEGER_MATH(b, c); \
|
||||
VARIANT4_RANDOM_MATH(a, b, r, &_b, &_b1); \
|
||||
__mul(); \
|
||||
VARIANT2_2(); \
|
||||
VARIANT2_SHUFFLE_ADD_NEON(local_hp_state, j); \
|
||||
VARIANT2_SHUFFLE_ADD_NEON(hp_state, j); \
|
||||
a[0] += hi; a[1] += lo; \
|
||||
p = U64(&local_hp_state[j]); \
|
||||
p = U64(&hp_state[j]); \
|
||||
p[0] = a[0]; p[1] = a[1]; \
|
||||
a[0] ^= b[0]; a[1] ^= b[1]; \
|
||||
VARIANT1_2(p + 1); \
|
||||
@@ -1102,47 +963,47 @@ union cn_slow_hash_state
|
||||
*/
|
||||
static void aes_expand_key(const uint8_t *key, uint8_t *expandedKey) {
|
||||
static const int rcon[] = {
|
||||
0x01,0x01,0x01,0x01,
|
||||
0x0c0f0e0d,0x0c0f0e0d,0x0c0f0e0d,0x0c0f0e0d, // rotate-n-splat
|
||||
0x1b,0x1b,0x1b,0x1b };
|
||||
0x01,0x01,0x01,0x01,
|
||||
0x0c0f0e0d,0x0c0f0e0d,0x0c0f0e0d,0x0c0f0e0d, // rotate-n-splat
|
||||
0x1b,0x1b,0x1b,0x1b };
|
||||
__asm__(
|
||||
" eor v0.16b,v0.16b,v0.16b\n"
|
||||
" ld1 {v3.16b},[%0],#16\n"
|
||||
" ld1 {v1.4s,v2.4s},[%2],#32\n"
|
||||
" ld1 {v4.16b},[%0]\n"
|
||||
" mov w2,#5\n"
|
||||
" st1 {v3.4s},[%1],#16\n"
|
||||
" eor v0.16b,v0.16b,v0.16b\n"
|
||||
" ld1 {v3.16b},[%0],#16\n"
|
||||
" ld1 {v1.4s,v2.4s},[%2],#32\n"
|
||||
" ld1 {v4.16b},[%0]\n"
|
||||
" mov w2,#5\n"
|
||||
" st1 {v3.4s},[%1],#16\n"
|
||||
"\n"
|
||||
"1:\n"
|
||||
" tbl v6.16b,{v4.16b},v2.16b\n"
|
||||
" ext v5.16b,v0.16b,v3.16b,#12\n"
|
||||
" st1 {v4.4s},[%1],#16\n"
|
||||
" aese v6.16b,v0.16b\n"
|
||||
" subs w2,w2,#1\n"
|
||||
" tbl v6.16b,{v4.16b},v2.16b\n"
|
||||
" ext v5.16b,v0.16b,v3.16b,#12\n"
|
||||
" st1 {v4.4s},[%1],#16\n"
|
||||
" aese v6.16b,v0.16b\n"
|
||||
" subs w2,w2,#1\n"
|
||||
"\n"
|
||||
" eor v3.16b,v3.16b,v5.16b\n"
|
||||
" ext v5.16b,v0.16b,v5.16b,#12\n"
|
||||
" eor v3.16b,v3.16b,v5.16b\n"
|
||||
" ext v5.16b,v0.16b,v5.16b,#12\n"
|
||||
" eor v6.16b,v6.16b,v1.16b\n"
|
||||
" eor v3.16b,v3.16b,v5.16b\n"
|
||||
" shl v1.16b,v1.16b,#1\n"
|
||||
" eor v3.16b,v3.16b,v6.16b\n"
|
||||
" st1 {v3.4s},[%1],#16\n"
|
||||
" b.eq 2f\n"
|
||||
" eor v3.16b,v3.16b,v5.16b\n"
|
||||
" ext v5.16b,v0.16b,v5.16b,#12\n"
|
||||
" eor v3.16b,v3.16b,v5.16b\n"
|
||||
" ext v5.16b,v0.16b,v5.16b,#12\n"
|
||||
" eor v6.16b,v6.16b,v1.16b\n"
|
||||
" eor v3.16b,v3.16b,v5.16b\n"
|
||||
" shl v1.16b,v1.16b,#1\n"
|
||||
" eor v3.16b,v3.16b,v6.16b\n"
|
||||
" st1 {v3.4s},[%1],#16\n"
|
||||
" b.eq 2f\n"
|
||||
"\n"
|
||||
" dup v6.4s,v3.s[3] // just splat\n"
|
||||
" ext v5.16b,v0.16b,v4.16b,#12\n"
|
||||
" aese v6.16b,v0.16b\n"
|
||||
" dup v6.4s,v3.s[3] // just splat\n"
|
||||
" ext v5.16b,v0.16b,v4.16b,#12\n"
|
||||
" aese v6.16b,v0.16b\n"
|
||||
"\n"
|
||||
" eor v4.16b,v4.16b,v5.16b\n"
|
||||
" ext v5.16b,v0.16b,v5.16b,#12\n"
|
||||
" eor v4.16b,v4.16b,v5.16b\n"
|
||||
" ext v5.16b,v0.16b,v5.16b,#12\n"
|
||||
" eor v4.16b,v4.16b,v5.16b\n"
|
||||
" eor v4.16b,v4.16b,v5.16b\n"
|
||||
" ext v5.16b,v0.16b,v5.16b,#12\n"
|
||||
" eor v4.16b,v4.16b,v5.16b\n"
|
||||
" ext v5.16b,v0.16b,v5.16b,#12\n"
|
||||
" eor v4.16b,v4.16b,v5.16b\n"
|
||||
"\n"
|
||||
" eor v4.16b,v4.16b,v6.16b\n"
|
||||
" b 1b\n"
|
||||
" eor v4.16b,v4.16b,v6.16b\n"
|
||||
" b 1b\n"
|
||||
"\n"
|
||||
"2:\n" : : "r"(key), "r"(expandedKey), "r"(rcon));
|
||||
}
|
||||
@@ -1157,71 +1018,71 @@ __asm__(
|
||||
*/
|
||||
STATIC INLINE void aes_pseudo_round(const uint8_t *in, uint8_t *out, const uint8_t *expandedKey, int nblocks)
|
||||
{
|
||||
const uint8x16_t *k = (const uint8x16_t *)expandedKey, zero = {0};
|
||||
uint8x16_t tmp;
|
||||
int i;
|
||||
const uint8x16_t *k = (const uint8x16_t *)expandedKey, zero = {0};
|
||||
uint8x16_t tmp;
|
||||
int i;
|
||||
|
||||
for (i=0; i<nblocks; i++)
|
||||
{
|
||||
uint8x16_t tmp = vld1q_u8(in + i * AES_BLOCK_SIZE);
|
||||
tmp = vaeseq_u8(tmp, zero);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[0]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[1]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[2]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[3]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[4]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[5]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[6]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[7]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[8]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = veorq_u8(tmp, k[9]);
|
||||
vst1q_u8(out + i * AES_BLOCK_SIZE, tmp);
|
||||
}
|
||||
for (i=0; i<nblocks; i++)
|
||||
{
|
||||
uint8x16_t tmp = vld1q_u8(in + i * AES_BLOCK_SIZE);
|
||||
tmp = vaeseq_u8(tmp, zero);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[0]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[1]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[2]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[3]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[4]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[5]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[6]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[7]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[8]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = veorq_u8(tmp, k[9]);
|
||||
vst1q_u8(out + i * AES_BLOCK_SIZE, tmp);
|
||||
}
|
||||
}
|
||||
|
||||
STATIC INLINE void aes_pseudo_round_xor(const uint8_t *in, uint8_t *out, const uint8_t *expandedKey, const uint8_t *xor, int nblocks)
|
||||
{
|
||||
const uint8x16_t *k = (const uint8x16_t *)expandedKey;
|
||||
const uint8x16_t *x = (const uint8x16_t *)xor;
|
||||
uint8x16_t tmp;
|
||||
int i;
|
||||
const uint8x16_t *k = (const uint8x16_t *)expandedKey;
|
||||
const uint8x16_t *x = (const uint8x16_t *)xor;
|
||||
uint8x16_t tmp;
|
||||
int i;
|
||||
|
||||
for (i=0; i<nblocks; i++)
|
||||
{
|
||||
uint8x16_t tmp = vld1q_u8(in + i * AES_BLOCK_SIZE);
|
||||
tmp = vaeseq_u8(tmp, x[i]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[0]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[1]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[2]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[3]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[4]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[5]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[6]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[7]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[8]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = veorq_u8(tmp, k[9]);
|
||||
vst1q_u8(out + i * AES_BLOCK_SIZE, tmp);
|
||||
}
|
||||
for (i=0; i<nblocks; i++)
|
||||
{
|
||||
uint8x16_t tmp = vld1q_u8(in + i * AES_BLOCK_SIZE);
|
||||
tmp = vaeseq_u8(tmp, x[i]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[0]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[1]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[2]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[3]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[4]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[5]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[6]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[7]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = vaeseq_u8(tmp, k[8]);
|
||||
tmp = vaesmcq_u8(tmp);
|
||||
tmp = veorq_u8(tmp, k[9]);
|
||||
vst1q_u8(out + i * AES_BLOCK_SIZE, tmp);
|
||||
}
|
||||
}
|
||||
|
||||
#ifdef FORCE_USE_HEAP
|
||||
@@ -1251,9 +1112,9 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
RDATA_ALIGN16 uint8_t expandedKey[240];
|
||||
|
||||
#ifndef FORCE_USE_HEAP
|
||||
RDATA_ALIGN16 uint8_t local_hp_state[MEMORY];
|
||||
RDATA_ALIGN16 uint8_t hp_state[MEMORY];
|
||||
#else
|
||||
uint8_t *local_hp_state = (uint8_t *)aligned_malloc(MEMORY,16);
|
||||
uint8_t *hp_state = (uint8_t *)aligned_malloc(MEMORY,16);
|
||||
#endif
|
||||
|
||||
uint8_t text[INIT_SIZE_BYTE];
|
||||
@@ -1293,7 +1154,7 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
for(i = 0; i < MEMORY / INIT_SIZE_BYTE; i++)
|
||||
{
|
||||
aes_pseudo_round(text, text, expandedKey, INIT_SIZE_BLK);
|
||||
memcpy(&local_hp_state[i * INIT_SIZE_BYTE], text, INIT_SIZE_BYTE);
|
||||
memcpy(&hp_state[i * INIT_SIZE_BYTE], text, INIT_SIZE_BYTE);
|
||||
}
|
||||
|
||||
U64(a)[0] = U64(&state.k[0])[0] ^ U64(&state.k[32])[0];
|
||||
@@ -1328,7 +1189,7 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
for(i = 0; i < MEMORY / INIT_SIZE_BYTE; i++)
|
||||
{
|
||||
// add the xor to the pseudo round
|
||||
aes_pseudo_round_xor(text, text, expandedKey, &local_hp_state[i * INIT_SIZE_BYTE], INIT_SIZE_BLK);
|
||||
aes_pseudo_round_xor(text, text, expandedKey, &hp_state[i * INIT_SIZE_BYTE], INIT_SIZE_BLK);
|
||||
}
|
||||
|
||||
/* CryptoNight Step 5: Apply Keccak to the state again, and then
|
||||
@@ -1343,7 +1204,7 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
extra_hashes[state.hs.b[0] & 3](&state, 200, hash);
|
||||
|
||||
#ifdef FORCE_USE_HEAP
|
||||
aligned_free(local_hp_state);
|
||||
aligned_free(hp_state);
|
||||
#endif
|
||||
}
|
||||
#else /* aarch64 && crypto */
|
||||
@@ -1387,7 +1248,7 @@ void mul(const uint8_t *ca, const uint8_t *cb, uint8_t *cres) {
|
||||
#else // !NO_OPTIMIZED_MULTIPLY_ON_ARM
|
||||
|
||||
#ifdef __aarch64__ /* ARM64, no crypto */
|
||||
#define mul(a, b, c) cn_mul128((const uint64_t *)a, (const uint64_t *)b, (uint64_t *)c)
|
||||
#define mul(a, b, c) cn_mul128((const uint64_t *)a, (const uint64_t *)b, (uint64_t *)c)
|
||||
STATIC void cn_mul128(const uint64_t *a, const uint64_t *b, uint64_t *r)
|
||||
{
|
||||
uint64_t lo, hi;
|
||||
@@ -1397,7 +1258,7 @@ STATIC void cn_mul128(const uint64_t *a, const uint64_t *b, uint64_t *r)
|
||||
r[1] = lo;
|
||||
}
|
||||
#else /* ARM32 */
|
||||
#define mul(a, b, c) cn_mul128((const uint32_t *)a, (const uint32_t *)b, (uint32_t *)c)
|
||||
#define mul(a, b, c) cn_mul128((const uint32_t *)a, (const uint32_t *)b, (uint32_t *)c)
|
||||
STATIC void cn_mul128(const uint32_t *aa, const uint32_t *bb, uint32_t *r)
|
||||
{
|
||||
uint32_t t0, t1, t2=0, t3=0;
|
||||
@@ -1466,7 +1327,6 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
{
|
||||
uint8_t text[INIT_SIZE_BYTE];
|
||||
uint8_t a[AES_BLOCK_SIZE];
|
||||
uint8_t a1[AES_BLOCK_SIZE];
|
||||
uint8_t b[AES_BLOCK_SIZE * 2];
|
||||
uint8_t c[AES_BLOCK_SIZE];
|
||||
uint8_t c1[AES_BLOCK_SIZE];
|
||||
@@ -1526,10 +1386,10 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
// Iteration 1
|
||||
j = state_index(a);
|
||||
p = &long_state[j];
|
||||
aesb_single_round(p, c1, a);
|
||||
aesb_single_round(p, p, a);
|
||||
copy_block(c1, p);
|
||||
|
||||
VARIANT2_PORTABLE_SHUFFLE_ADD(c1, a, long_state, j);
|
||||
copy_block(p, c1);
|
||||
VARIANT2_PORTABLE_SHUFFLE_ADD(long_state, j);
|
||||
xor_blocks(p, b);
|
||||
VARIANT1_1(p);
|
||||
|
||||
@@ -1538,15 +1398,14 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
p = &long_state[j];
|
||||
copy_block(c, p);
|
||||
|
||||
copy_block(a1, a);
|
||||
VARIANT2_PORTABLE_INTEGER_MATH(c, c1);
|
||||
VARIANT4_RANDOM_MATH(a1, c, r, b, b + AES_BLOCK_SIZE);
|
||||
VARIANT4_RANDOM_MATH(a, c, r, b, b + AES_BLOCK_SIZE);
|
||||
mul(c1, c, d);
|
||||
VARIANT2_2_PORTABLE();
|
||||
VARIANT2_PORTABLE_SHUFFLE_ADD(c1, a, long_state, j);
|
||||
sum_half_blocks(a1, d);
|
||||
swap_blocks(a1, c);
|
||||
xor_blocks(a1, c);
|
||||
VARIANT2_PORTABLE_SHUFFLE_ADD(long_state, j);
|
||||
sum_half_blocks(a, d);
|
||||
swap_blocks(a, c);
|
||||
xor_blocks(a, c);
|
||||
VARIANT1_2(U64(c) + 1);
|
||||
copy_block(p, c);
|
||||
|
||||
@@ -1554,7 +1413,6 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
copy_block(b + AES_BLOCK_SIZE, b);
|
||||
}
|
||||
copy_block(b, c1);
|
||||
copy_block(a, a1);
|
||||
}
|
||||
|
||||
memcpy(text, state.init, INIT_SIZE_BYTE);
|
||||
@@ -1584,13 +1442,13 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
|
||||
#define hp_jitfunc ((v4_random_math_JIT_func)NULL)
|
||||
|
||||
void slow_hash_allocate_state(void)
|
||||
void cn_slow_hash_allocate_state(void)
|
||||
{
|
||||
// Do nothing, this is just to maintain compatibility with the upgraded slow-hash.c
|
||||
return;
|
||||
}
|
||||
|
||||
void slow_hash_free_state(void)
|
||||
void cn_slow_hash_free_state(void)
|
||||
{
|
||||
// As above
|
||||
return;
|
||||
@@ -1677,7 +1535,6 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
union cn_slow_hash_state state;
|
||||
uint8_t text[INIT_SIZE_BYTE];
|
||||
uint8_t a[AES_BLOCK_SIZE];
|
||||
uint8_t a1[AES_BLOCK_SIZE];
|
||||
uint8_t b[AES_BLOCK_SIZE * 2];
|
||||
uint8_t c1[AES_BLOCK_SIZE];
|
||||
uint8_t c2[AES_BLOCK_SIZE];
|
||||
@@ -1721,7 +1578,7 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
j = e2i(a, MEMORY / AES_BLOCK_SIZE) * AES_BLOCK_SIZE;
|
||||
copy_block(c1, &long_state[j]);
|
||||
aesb_single_round(c1, c1, a);
|
||||
VARIANT2_PORTABLE_SHUFFLE_ADD(c1, a, long_state, j);
|
||||
VARIANT2_PORTABLE_SHUFFLE_ADD(long_state, j);
|
||||
copy_block(&long_state[j], c1);
|
||||
xor_blocks(&long_state[j], b);
|
||||
assert(j == e2i(a, MEMORY / AES_BLOCK_SIZE) * AES_BLOCK_SIZE);
|
||||
@@ -1729,22 +1586,23 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
/* Iteration 2 */
|
||||
j = e2i(c1, MEMORY / AES_BLOCK_SIZE) * AES_BLOCK_SIZE;
|
||||
copy_block(c2, &long_state[j]);
|
||||
copy_block(a1, a);
|
||||
VARIANT2_PORTABLE_INTEGER_MATH(c2, c1);
|
||||
VARIANT4_RANDOM_MATH(a1, c2, r, b, b + AES_BLOCK_SIZE);
|
||||
VARIANT4_RANDOM_MATH(a, c2, r, b, b + AES_BLOCK_SIZE);
|
||||
mul(c1, c2, d);
|
||||
VARIANT2_2_PORTABLE();
|
||||
VARIANT2_PORTABLE_SHUFFLE_ADD(c1, a, long_state, j);
|
||||
sum_half_blocks(a1, d);
|
||||
swap_blocks(a1, c2);
|
||||
xor_blocks(a1, c2);
|
||||
VARIANT2_PORTABLE_SHUFFLE_ADD(long_state, j);
|
||||
swap_blocks(a, c1);
|
||||
sum_half_blocks(c1, d);
|
||||
swap_blocks(c1, c2);
|
||||
xor_blocks(c1, c2);
|
||||
VARIANT1_2(c2 + 8);
|
||||
copy_block(&long_state[j], c2);
|
||||
assert(j == e2i(a, MEMORY / AES_BLOCK_SIZE) * AES_BLOCK_SIZE);
|
||||
if (variant >= 2) {
|
||||
copy_block(b + AES_BLOCK_SIZE, b);
|
||||
}
|
||||
copy_block(b, c1);
|
||||
copy_block(a, a1);
|
||||
copy_block(b, a);
|
||||
copy_block(a, c1);
|
||||
}
|
||||
|
||||
memcpy(text, state.init, INIT_SIZE_BYTE);
|
||||
@@ -1767,3 +1625,15 @@ void cn_slow_hash(const void *data, size_t length, char *hash, int variant, int
|
||||
}
|
||||
|
||||
#endif
|
||||
|
||||
void slow_hash_allocate_state(void)
|
||||
{
|
||||
cn_slow_hash_allocate_state();
|
||||
rx_slow_hash_allocate_state();
|
||||
}
|
||||
|
||||
void slow_hash_free_state(void)
|
||||
{
|
||||
cn_slow_hash_free_state();
|
||||
rx_slow_hash_free_state();
|
||||
}
|
||||
|
||||
@@ -10,11 +10,8 @@ enum V4_Settings
|
||||
TOTAL_LATENCY = 15 * 3,
|
||||
|
||||
// Always generate at least 60 instructions
|
||||
NUM_INSTRUCTIONS_MIN = 60,
|
||||
|
||||
// Never generate more than 70 instructions (final RET instruction doesn't count here)
|
||||
NUM_INSTRUCTIONS_MAX = 70,
|
||||
|
||||
NUM_INSTRUCTIONS = 60,
|
||||
|
||||
// Available ALUs for MUL
|
||||
// Modern CPUs typically have only 1 ALU which can do multiplications
|
||||
ALU_COUNT_MUL = 1,
|
||||
@@ -39,9 +36,10 @@ enum V4_InstructionList
|
||||
// V4_InstructionDefinition is used to generate code from random data
|
||||
// Every random sequence of bytes is a valid code
|
||||
//
|
||||
// There are 9 registers in total:
|
||||
// There are 8 registers in total:
|
||||
// - 4 variable registers
|
||||
// - 5 constant registers initialized from loop variables
|
||||
// - 4 constant registers initialized from loop variables
|
||||
//
|
||||
// This is why dst_index is 2 bits
|
||||
enum V4_InstructionDefinition
|
||||
{
|
||||
@@ -59,9 +57,9 @@ struct V4_Instruction
|
||||
};
|
||||
|
||||
#ifndef FORCEINLINE
|
||||
#if defined(__GNUC__)
|
||||
#ifdef __GNUC__
|
||||
#define FORCEINLINE __attribute__((always_inline)) inline
|
||||
#elif defined(_MSC_VER)
|
||||
#elif _MSC_VER
|
||||
#define FORCEINLINE __forceinline
|
||||
#else
|
||||
#define FORCEINLINE inline
|
||||
@@ -69,9 +67,9 @@ struct V4_Instruction
|
||||
#endif
|
||||
|
||||
#ifndef UNREACHABLE_CODE
|
||||
#if defined(__GNUC__)
|
||||
#ifdef __GNUC__
|
||||
#define UNREACHABLE_CODE __builtin_unreachable()
|
||||
#elif defined(_MSC_VER)
|
||||
#elif _MSC_VER
|
||||
#define UNREACHABLE_CODE __assume(false)
|
||||
#else
|
||||
#define UNREACHABLE_CODE
|
||||
@@ -143,16 +141,16 @@ static FORCEINLINE void v4_random_math(const struct V4_Instruction* code, v4_reg
|
||||
// Generated program can have 60 + a few more (usually 2-3) instructions to achieve required latency
|
||||
// I've checked all block heights < 10,000,000 and here is the distribution of program sizes:
|
||||
//
|
||||
// 60 27960
|
||||
// 61 105054
|
||||
// 62 2452759
|
||||
// 63 5115997
|
||||
// 64 1022269
|
||||
// 65 1109635
|
||||
// 66 153145
|
||||
// 67 8550
|
||||
// 68 4529
|
||||
// 69 102
|
||||
// 60 28495
|
||||
// 61 106077
|
||||
// 62 2455855
|
||||
// 63 5114930
|
||||
// 64 1020868
|
||||
// 65 1109026
|
||||
// 66 151756
|
||||
// 67 8429
|
||||
// 68 4477
|
||||
// 69 87
|
||||
|
||||
// Unroll 70 instructions here
|
||||
V4_EXEC_10(0); // instructions 0-9
|
||||
@@ -178,7 +176,6 @@ static FORCEINLINE void check_data(size_t* data_index, const size_t bytes_needed
|
||||
}
|
||||
|
||||
// Generates as many random math operations as possible with given latency and ALU restrictions
|
||||
// "code" array must have space for NUM_INSTRUCTIONS_MAX+1 instructions
|
||||
static inline int v4_random_math_init(struct V4_Instruction* code, const uint64_t height)
|
||||
{
|
||||
// MUL is 3 cycles, 3-way addition and rotations are 2 cycles, SUB/XOR are 1 cycle
|
||||
@@ -200,7 +197,6 @@ static inline int v4_random_math_init(struct V4_Instruction* code, const uint64_
|
||||
memset(data, 0, sizeof(data));
|
||||
uint64_t tmp = SWAP64LE(height);
|
||||
memcpy(data, &tmp, sizeof(uint64_t));
|
||||
data[20] = -38; // change seed
|
||||
|
||||
// Set data_index past the last byte in data
|
||||
// to trigger full data update with blake hash
|
||||
@@ -208,22 +204,18 @@ static inline int v4_random_math_init(struct V4_Instruction* code, const uint64_
|
||||
size_t data_index = sizeof(data);
|
||||
|
||||
int code_size;
|
||||
|
||||
// There is a small chance (1.8%) that register R8 won't be used in the generated program
|
||||
// So we keep track of it and try again if it's not used
|
||||
bool r8_used;
|
||||
do {
|
||||
int latency[9];
|
||||
int asic_latency[9];
|
||||
int latency[8];
|
||||
int asic_latency[8];
|
||||
|
||||
// Tracks previous instruction and value of the source operand for registers R0-R3 throughout code execution
|
||||
// byte 0: current value of the destination register
|
||||
// byte 1: instruction opcode
|
||||
// byte 2: current value of the source register
|
||||
//
|
||||
// Registers R4-R8 are constant and are treated as having the same value because when we do
|
||||
// Registers R4-R7 are constant and are treated as having the same value because when we do
|
||||
// the same operation twice with two constant source registers, it can be optimized into a single operation
|
||||
uint32_t inst_data[9] = { 0, 1, 2, 3, 0xFFFFFF, 0xFFFFFF, 0xFFFFFF, 0xFFFFFF, 0xFFFFFF };
|
||||
uint32_t inst_data[8] = { 0, 1, 2, 3, 0xFFFFFF, 0xFFFFFF, 0xFFFFFF, 0xFFFFFF };
|
||||
|
||||
bool alu_busy[TOTAL_LATENCY + 1][ALU_COUNT];
|
||||
bool is_rotation[V4_INSTRUCTION_COUNT];
|
||||
@@ -242,7 +234,6 @@ static inline int v4_random_math_init(struct V4_Instruction* code, const uint64_
|
||||
code_size = 0;
|
||||
|
||||
int total_iterations = 0;
|
||||
r8_used = false;
|
||||
|
||||
// Generate random code to achieve minimal required latency for our abstract CPU
|
||||
// Try to get this latency for all 4 registers
|
||||
@@ -286,9 +277,9 @@ static inline int v4_random_math_init(struct V4_Instruction* code, const uint64_
|
||||
// Don't do ADD/SUB/XOR with the same register
|
||||
if (((opcode == ADD) || (opcode == SUB) || (opcode == XOR)) && (a == b))
|
||||
{
|
||||
// Use register R8 as source instead
|
||||
b = 8;
|
||||
src_index = 8;
|
||||
// a is always < 4, so we don't need to check bounds here
|
||||
b = a + 4;
|
||||
src_index = b;
|
||||
}
|
||||
|
||||
// Don't do rotation with the same destination twice because it's equal to a single rotation
|
||||
@@ -368,11 +359,6 @@ static inline int v4_random_math_init(struct V4_Instruction* code, const uint64_
|
||||
code[code_size].src_index = src_index;
|
||||
code[code_size].C = 0;
|
||||
|
||||
if (src_index == 8)
|
||||
{
|
||||
r8_used = true;
|
||||
}
|
||||
|
||||
if (opcode == ADD)
|
||||
{
|
||||
// ADD instruction is implemented as two 1-cycle instructions on a real CPU, so mark ALU as busy for the next cycle too
|
||||
@@ -387,7 +373,7 @@ static inline int v4_random_math_init(struct V4_Instruction* code, const uint64_
|
||||
}
|
||||
|
||||
++code_size;
|
||||
if (code_size >= NUM_INSTRUCTIONS_MIN)
|
||||
if (code_size >= NUM_INSTRUCTIONS)
|
||||
{
|
||||
break;
|
||||
}
|
||||
@@ -402,7 +388,7 @@ static inline int v4_random_math_init(struct V4_Instruction* code, const uint64_
|
||||
// We need to add a few more MUL and ROR instructions to achieve minimal required latency for ASIC
|
||||
// Get this latency for at least 1 of the 4 registers
|
||||
const int prev_code_size = code_size;
|
||||
while ((code_size < NUM_INSTRUCTIONS_MAX) && (asic_latency[0] < TOTAL_LATENCY) && (asic_latency[1] < TOTAL_LATENCY) && (asic_latency[2] < TOTAL_LATENCY) && (asic_latency[3] < TOTAL_LATENCY))
|
||||
while ((asic_latency[0] < TOTAL_LATENCY) && (asic_latency[1] < TOTAL_LATENCY) && (asic_latency[2] < TOTAL_LATENCY) && (asic_latency[3] < TOTAL_LATENCY))
|
||||
{
|
||||
int min_idx = 0;
|
||||
int max_idx = 0;
|
||||
@@ -424,11 +410,9 @@ static inline int v4_random_math_init(struct V4_Instruction* code, const uint64_
|
||||
++code_size;
|
||||
}
|
||||
|
||||
// There is ~98.15% chance that loop condition is false, so this loop will execute only 1 iteration most of the time
|
||||
// It never does more than 4 iterations for all block heights < 10,000,000
|
||||
} while (!r8_used || (code_size < NUM_INSTRUCTIONS_MIN) || (code_size > NUM_INSTRUCTIONS_MAX));
|
||||
// There is ~99.8% chance that code_size >= NUM_INSTRUCTIONS here, so second iteration is required rarely
|
||||
} while (code_size < NUM_INSTRUCTIONS);
|
||||
|
||||
// It's guaranteed that NUM_INSTRUCTIONS_MIN <= code_size <= NUM_INSTRUCTIONS_MAX here
|
||||
// Add final instruction to stop the interpreter
|
||||
code[code_size].opcode = RET;
|
||||
code[code_size].dst_index = 0;
|
||||
|
||||
@@ -88,7 +88,7 @@ namespace cryptonote {
|
||||
const int emission_speed_factor = EMISSION_SPEED_FACTOR_PER_MINUTE - (target_minutes-1);
|
||||
|
||||
uint64_t base_reward = (MONEY_SUPPLY - already_generated_coins) >> emission_speed_factor;
|
||||
if (base_reward < FINAL_SUBSIDY_PER_MINUTE*target_minutes)
|
||||
if (base_reward <= FINAL_SUBSIDY_PER_MINUTE*target_minutes)
|
||||
{
|
||||
base_reward = FINAL_SUBSIDY_PER_MINUTE*target_minutes;
|
||||
}
|
||||
|
||||
@@ -295,7 +295,7 @@ namespace boost
|
||||
a & x.type;
|
||||
if (x.type == rct::RCTTypeNull)
|
||||
return;
|
||||
if (x.type != rct::RCTTypeFull && x.type != rct::RCTTypeSimple && x.type != rct::RCTTypeBulletproof && x.type != rct::RCTTypeBulletproof2)
|
||||
if (x.type != rct::RCTTypeFull && x.type != rct::RCTTypeSimple && x.type != rct::RCTTypeBulletproof && x.type != rct::RCTTypeBulletproof2 && x.type != rct::RCTTypeFullBulletproof && x.type != rct::RCTTypeSimpleBulletproof)
|
||||
throw boost::archive::archive_exception(boost::archive::archive_exception::other_exception, "Unsupported rct type");
|
||||
// a & x.message; message is not serialized, as it can be reconstructed from the tx data
|
||||
// a & x.mixRing; mixRing is not serialized, as it can be reconstructed from the offsets
|
||||
@@ -323,7 +323,7 @@ namespace boost
|
||||
a & x.type;
|
||||
if (x.type == rct::RCTTypeNull)
|
||||
return;
|
||||
if (x.type != rct::RCTTypeFull && x.type != rct::RCTTypeSimple && x.type != rct::RCTTypeBulletproof && x.type != rct::RCTTypeBulletproof2)
|
||||
if (x.type != rct::RCTTypeFull && x.type != rct::RCTTypeSimple && x.type != rct::RCTTypeBulletproof && x.type != rct::RCTTypeBulletproof2 && x.type != rct::RCTTypeFullBulletproof && x.type != rct::RCTTypeSimpleBulletproof)
|
||||
throw boost::archive::archive_exception(boost::archive::archive_exception::other_exception, "Unsupported rct type");
|
||||
// a & x.message; message is not serialized, as it can be reconstructed from the tx data
|
||||
// a & x.mixRing; mixRing is not serialized, as it can be reconstructed from the offsets
|
||||
@@ -337,7 +337,7 @@ namespace boost
|
||||
if (x.p.rangeSigs.empty())
|
||||
a & x.p.bulletproofs;
|
||||
a & x.p.MGs;
|
||||
if (x.type == rct::RCTTypeBulletproof || x.type == rct::RCTTypeBulletproof2)
|
||||
if (x.type == rct::RCTTypeBulletproof || x.type == rct::RCTTypeBulletproof2 || x.type == rct::RCTTypeSimpleBulletproof)
|
||||
a & x.p.pseudoOuts;
|
||||
}
|
||||
|
||||
|
||||
@@ -146,7 +146,7 @@ namespace cryptonote
|
||||
if (!base_only)
|
||||
{
|
||||
const bool bulletproof = rct::is_rct_bulletproof(rv.type);
|
||||
if (bulletproof)
|
||||
if (rct::is_rct_new_bulletproof(rv.type))
|
||||
{
|
||||
if (rv.p.bulletproofs.size() != 1)
|
||||
{
|
||||
@@ -159,7 +159,7 @@ namespace cryptonote
|
||||
return false;
|
||||
}
|
||||
const size_t max_outputs = 1 << (rv.p.bulletproofs[0].L.size() - 6);
|
||||
if (max_outputs < tx.vout.size())
|
||||
if (max_outputs < tx.vout.size() && rv.type == rct::RCTTypeBulletproof)
|
||||
{
|
||||
LOG_PRINT_L1("Failed to parse transaction from blob, bad bulletproofs max outputs in tx " << get_transaction_hash(tx));
|
||||
return false;
|
||||
@@ -170,6 +170,26 @@ namespace cryptonote
|
||||
for (size_t i = 0; i < n_amounts; ++i)
|
||||
rv.p.bulletproofs[0].V[i] = rct::scalarmultKey(rv.outPk[i].mask, rct::INV_EIGHT);
|
||||
}
|
||||
else if (bulletproof)
|
||||
{
|
||||
if (rct::n_bulletproof_v1_amounts(rv.p.bulletproofs) != tx.vout.size())
|
||||
{
|
||||
LOG_PRINT_L1("Failed to parse transaction from blob, bad bulletproofs size in tx " << get_transaction_hash(tx));
|
||||
return false;
|
||||
}
|
||||
size_t idx = 0;
|
||||
for (size_t n = 0; n < rv.outPk.size(); ++n)
|
||||
{
|
||||
//rv.p.bulletproofs[n].V.resize(1);
|
||||
//rv.p.bulletproofs[n].V[0] = rv.outPk[n].mask;
|
||||
CHECK_AND_ASSERT_MES(rv.p.bulletproofs[n].L.size() >= 6, false, "Bad bulletproofs L size"); // at least 64 bits
|
||||
const size_t n_amounts = rct::n_bulletproof_v1_amounts(rv.p.bulletproofs[n]);
|
||||
CHECK_AND_ASSERT_MES(idx + n_amounts <= rv.outPk.size(), false, "Internal error filling out V");
|
||||
rv.p.bulletproofs[n].V.resize(n_amounts);
|
||||
for (size_t i = 0; i < n_amounts; ++i)
|
||||
rv.p.bulletproofs[n].V[i] = rv.outPk[idx++].mask;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
return true;
|
||||
@@ -395,6 +415,8 @@ namespace cryptonote
|
||||
const size_t n_outputs = tx.vout.size();
|
||||
if (n_outputs <= 2)
|
||||
return blob_size;
|
||||
if (rct::is_rct_old_bulletproof(rv.type))
|
||||
return blob_size;
|
||||
const uint64_t bp_base = 368;
|
||||
const size_t n_padded_outputs = rct::n_bulletproof_max_amounts(rv.p.bulletproofs);
|
||||
size_t nlr = 0;
|
||||
@@ -905,7 +927,7 @@ namespace cryptonote
|
||||
{
|
||||
switch (decimal_point)
|
||||
{
|
||||
case 12:
|
||||
case 11:
|
||||
case 9:
|
||||
case 6:
|
||||
case 3:
|
||||
@@ -928,8 +950,8 @@ namespace cryptonote
|
||||
decimal_point = default_decimal_point;
|
||||
switch (decimal_point)
|
||||
{
|
||||
case 12:
|
||||
return "monero";
|
||||
case 11:
|
||||
return "wownero";
|
||||
case 9:
|
||||
return "millinero";
|
||||
case 6:
|
||||
@@ -1150,45 +1172,7 @@ namespace cryptonote
|
||||
//---------------------------------------------------------------
|
||||
bool calculate_block_hash(const block& b, crypto::hash& res, const blobdata *blob)
|
||||
{
|
||||
blobdata bd;
|
||||
if (!blob)
|
||||
{
|
||||
bd = block_to_blob(b);
|
||||
blob = &bd;
|
||||
}
|
||||
|
||||
bool hash_result = get_object_hash(get_block_hashing_blob(b), res);
|
||||
if (!hash_result)
|
||||
return false;
|
||||
|
||||
if (b.miner_tx.vin.size() == 1 && b.miner_tx.vin[0].type() == typeid(cryptonote::txin_gen))
|
||||
{
|
||||
const cryptonote::txin_gen &txin_gen = boost::get<cryptonote::txin_gen>(b.miner_tx.vin[0]);
|
||||
if (txin_gen.height != 202612)
|
||||
return true;
|
||||
}
|
||||
|
||||
// EXCEPTION FOR BLOCK 202612
|
||||
const std::string correct_blob_hash_202612 = "3a8a2b3a29b50fc86ff73dd087ea43c6f0d6b8f936c849194d5c84c737903966";
|
||||
const std::string existing_block_id_202612 = "bbd604d2ba11ba27935e006ed39c9bfdd99b76bf4a50654bc1e1e61217962698";
|
||||
crypto::hash block_blob_hash = get_blob_hash(*blob);
|
||||
|
||||
if (string_tools::pod_to_hex(block_blob_hash) == correct_blob_hash_202612)
|
||||
{
|
||||
string_tools::hex_to_pod(existing_block_id_202612, res);
|
||||
return true;
|
||||
}
|
||||
|
||||
{
|
||||
// make sure that we aren't looking at a block with the 202612 block id but not the correct blobdata
|
||||
if (string_tools::pod_to_hex(res) == existing_block_id_202612)
|
||||
{
|
||||
LOG_ERROR("Block with block id for 202612 but incorrect block blob hash found!");
|
||||
res = null_hash;
|
||||
return false;
|
||||
}
|
||||
}
|
||||
return hash_result;
|
||||
return get_object_hash(get_block_hashing_blob(b), res);
|
||||
}
|
||||
//---------------------------------------------------------------
|
||||
bool get_block_hash(const block& b, crypto::hash& res)
|
||||
@@ -1218,21 +1202,6 @@ namespace cryptonote
|
||||
return p;
|
||||
}
|
||||
//---------------------------------------------------------------
|
||||
bool get_block_longhash(const block& b, crypto::hash& res, uint64_t height)
|
||||
{
|
||||
// block 202612 bug workaround
|
||||
if (height == 202612)
|
||||
{
|
||||
static const std::string longhash_202612 = "84f64766475d51837ac9efbef1926486e58563c95a19fef4aec3254f03000000";
|
||||
string_tools::hex_to_pod(longhash_202612, res);
|
||||
return true;
|
||||
}
|
||||
blobdata bd = get_block_hashing_blob(b);
|
||||
const int cn_variant = b.major_version >= 7 ? b.major_version - 6 : 0;
|
||||
crypto::cn_slow_hash(bd.data(), bd.size(), res, cn_variant, height);
|
||||
return true;
|
||||
}
|
||||
//---------------------------------------------------------------
|
||||
std::vector<uint64_t> relative_output_offsets_to_absolute(const std::vector<uint64_t>& off)
|
||||
{
|
||||
std::vector<uint64_t> res = off;
|
||||
@@ -1253,13 +1222,6 @@ namespace cryptonote
|
||||
return res;
|
||||
}
|
||||
//---------------------------------------------------------------
|
||||
crypto::hash get_block_longhash(const block& b, uint64_t height)
|
||||
{
|
||||
crypto::hash p = null_hash;
|
||||
get_block_longhash(b, p, height);
|
||||
return p;
|
||||
}
|
||||
//---------------------------------------------------------------
|
||||
bool parse_and_validate_block_from_blob(const blobdata& b_blob, block& b, crypto::hash *block_hash)
|
||||
{
|
||||
std::stringstream ss;
|
||||
|
||||
@@ -117,8 +117,6 @@ namespace cryptonote
|
||||
bool calculate_block_hash(const block& b, crypto::hash& res, const blobdata *blob = NULL);
|
||||
bool get_block_hash(const block& b, crypto::hash& res);
|
||||
crypto::hash get_block_hash(const block& b);
|
||||
bool get_block_longhash(const block& b, crypto::hash& res, uint64_t height);
|
||||
crypto::hash get_block_longhash(const block& b, uint64_t height);
|
||||
bool parse_and_validate_block_from_blob(const blobdata& b_blob, block& b, crypto::hash *block_hash);
|
||||
bool parse_and_validate_block_from_blob(const blobdata& b_blob, block& b);
|
||||
bool parse_and_validate_block_from_blob(const blobdata& b_blob, block& b, crypto::hash &block_hash);
|
||||
|
||||
@@ -33,6 +33,7 @@
|
||||
#include <cstddef>
|
||||
#include <cstdint>
|
||||
#include <vector>
|
||||
#include <boost/math/special_functions/round.hpp>
|
||||
|
||||
#include "int-util.h"
|
||||
#include "crypto/hash.h"
|
||||
@@ -254,4 +255,146 @@ namespace cryptonote {
|
||||
return "0x" + s;
|
||||
}
|
||||
|
||||
// LWMA difficulty algorithm
|
||||
// Background: https://github.com/zawy12/difficulty-algorithms/issues/3
|
||||
// Copyright (c) 2017-2018 Zawy
|
||||
difficulty_type next_difficulty_v2(std::vector<std::uint64_t> timestamps, std::vector<difficulty_type> cumulative_difficulties, size_t target_seconds) {
|
||||
|
||||
const int64_t T = static_cast<int64_t>(target_seconds);
|
||||
size_t N = DIFFICULTY_WINDOW_V2;
|
||||
if (timestamps.size() < 4) {
|
||||
return 1;
|
||||
} else if ( timestamps.size() < N+1 ) {
|
||||
N = timestamps.size() - 1;
|
||||
} else {
|
||||
timestamps.resize(N+1);
|
||||
cumulative_difficulties.resize(N+1);
|
||||
}
|
||||
const double adjust = 0.998;
|
||||
const double k = N * (N + 1) / 2;
|
||||
double LWMA(0), sum_inverse_D(0), harmonic_mean_D(0), nextDifficulty(0);
|
||||
int64_t solveTime(0);
|
||||
uint64_t difficulty(0), next_difficulty(0);
|
||||
for (size_t i = 1; i <= N; i++) {
|
||||
solveTime = static_cast<int64_t>(timestamps[i]) - static_cast<int64_t>(timestamps[i - 1]);
|
||||
solveTime = std::min<int64_t>((T * 7), std::max<int64_t>(solveTime, (-7 * T)));
|
||||
difficulty = static_cast<uint64_t>(cumulative_difficulties[i] - cumulative_difficulties[i - 1]);
|
||||
LWMA += (int64_t)(solveTime * i) / k;
|
||||
sum_inverse_D += 1 / static_cast<double>(difficulty);
|
||||
}
|
||||
harmonic_mean_D = N / sum_inverse_D;
|
||||
if (static_cast<int64_t>(boost::math::round(LWMA)) < T / 20)
|
||||
LWMA = static_cast<double>(T / 20);
|
||||
|
||||
nextDifficulty = harmonic_mean_D * T / LWMA * adjust;
|
||||
next_difficulty = static_cast<uint64_t>(nextDifficulty);
|
||||
return next_difficulty;
|
||||
}
|
||||
|
||||
// LWMA-2
|
||||
difficulty_type next_difficulty_v3(std::vector<uint64_t> timestamps, std::vector<difficulty_type> cumulative_difficulties) {
|
||||
|
||||
int64_t T = DIFFICULTY_TARGET_V2;
|
||||
int64_t N = DIFFICULTY_WINDOW_V2;
|
||||
int64_t L(0), ST, sum_3_ST(0), next_D, prev_D;
|
||||
assert(timestamps.size() == cumulative_difficulties.size() && timestamps.size() <= static_cast<uint64_t>(N+1) );
|
||||
for ( int64_t i = 1; i <= N; i++ ) {
|
||||
ST = static_cast<int64_t>(timestamps[i]) - static_cast<int64_t>(timestamps[i-1]);
|
||||
ST = std::max(-4*T, std::min(ST, 6*T));
|
||||
L += ST * i ;
|
||||
if ( i > N-3 ) {
|
||||
sum_3_ST += ST;
|
||||
}
|
||||
}
|
||||
next_D = (static_cast<int64_t>(cumulative_difficulties[N] - cumulative_difficulties[0])*T*(N+1)*99)/(100*2*L);
|
||||
prev_D = static_cast<int64_t>(cumulative_difficulties[N] - cumulative_difficulties[N-1]);
|
||||
next_D = std::max((prev_D*67)/100, std::min(next_D, (prev_D*150)/100));
|
||||
if ( sum_3_ST < (8*T)/10) {
|
||||
next_D = std::max(next_D,(prev_D*108)/100);
|
||||
}
|
||||
return static_cast<uint64_t>(next_D);
|
||||
}
|
||||
|
||||
// LWMA-4
|
||||
difficulty_type next_difficulty_v4(std::vector<uint64_t> timestamps, std::vector<difficulty_type> cumulative_difficulties, size_t height) {
|
||||
|
||||
uint64_t T = DIFFICULTY_TARGET_V2;
|
||||
uint64_t N = DIFFICULTY_WINDOW_V2;
|
||||
uint64_t L(0), ST(0), next_D, prev_D, avg_D, i;
|
||||
assert(timestamps.size() == cumulative_difficulties.size() && timestamps.size() <= N+1 );
|
||||
if ( height <= 63469 + 1 ) { return 100000069; }
|
||||
std::vector<uint64_t>TS(N+1);
|
||||
TS[0] = timestamps[0];
|
||||
for ( i = 1; i <= N; i++) {
|
||||
if ( timestamps[i] > TS[i-1] ) { TS[i] = timestamps[i]; }
|
||||
else { TS[i] = TS[i-1]; }
|
||||
}
|
||||
for ( i = 1; i <= N; i++) {
|
||||
if ( i > 4 && TS[i]-TS[i-1] > 5*T && TS[i-1] - TS[i-4] < (14*T)/10 ) { ST = 2*T; }
|
||||
else if ( i > 7 && TS[i]-TS[i-1] > 5*T && TS[i-1] - TS[i-7] < 4*T ) { ST = 2*T; }
|
||||
else {
|
||||
ST = std::min(5*T ,TS[i] - TS[i-1]);
|
||||
}
|
||||
L += ST * i ;
|
||||
}
|
||||
if (L < N*N*T/20 ) { L = N*N*T/20; }
|
||||
avg_D = static_cast<uint64_t>(( cumulative_difficulties[N] - cumulative_difficulties[0] )/ N);
|
||||
if (avg_D > 2000000*N*N*T) {
|
||||
next_D = (avg_D/(200*L))*(N*(N+1)*T*97);
|
||||
}
|
||||
else { next_D = (avg_D*N*(N+1)*T*97)/(200*L); }
|
||||
prev_D = static_cast<uint64_t>(cumulative_difficulties[N] - cumulative_difficulties[N-1]);
|
||||
if ( ( TS[N] - TS[N-1] < (2*T)/10 ) ||
|
||||
( TS[N] - TS[N-2] < (5*T)/10 ) ||
|
||||
( TS[N] - TS[N-3] < (8*T)/10 ) )
|
||||
{
|
||||
next_D = std::max( next_D, std::min( (prev_D*110)/100, (105*avg_D)/100 ) );
|
||||
}
|
||||
i = 1000000000;
|
||||
while (i > 1) {
|
||||
if ( next_D > i*100 ) { next_D = ((next_D+i/2)/i)*i; break; }
|
||||
else { i /= 10; }
|
||||
}
|
||||
if ( next_D > 100000 ) {
|
||||
next_D = ((next_D+500)/1000)*1000 + std::min(static_cast<uint64_t>(999), (TS[N]-TS[N-10])/10);
|
||||
}
|
||||
return static_cast<uint64_t>(next_D);
|
||||
}
|
||||
|
||||
// LWMA-1 difficulty algorithm
|
||||
// Copyright (c) 2017-2019 Zawy, MIT License
|
||||
// https://github.com/zawy12/difficulty-algorithms/issues/3
|
||||
difficulty_type next_difficulty_v5(std::vector<std::uint64_t> timestamps, std::vector<difficulty_type> cumulative_difficulties, uint64_t T, uint64_t N, uint64_t HEIGHT, uint64_t FORK_HEIGHT, uint64_t difficulty_guess) {
|
||||
assert(timestamps.size() == cumulative_difficulties.size() && timestamps.size() <= N+1 );
|
||||
|
||||
if (HEIGHT >= FORK_HEIGHT && HEIGHT < FORK_HEIGHT + N) { return difficulty_guess; }
|
||||
assert(timestamps.size() == N+1);
|
||||
|
||||
uint64_t L(0), next_D, i, this_timestamp(0), previous_timestamp(0), avg_D;
|
||||
|
||||
previous_timestamp = timestamps[0]-T;
|
||||
for ( i = 1; i <= N; i++) {
|
||||
// Safely prevent out-of-sequence timestamps
|
||||
if ( timestamps[i] > previous_timestamp ) { this_timestamp = timestamps[i]; }
|
||||
else { this_timestamp = previous_timestamp+1; }
|
||||
L += i*std::min(6*T ,this_timestamp - previous_timestamp);
|
||||
previous_timestamp = this_timestamp;
|
||||
}
|
||||
if (L < N*N*T/20 ) { L = N*N*T/20; }
|
||||
avg_D = static_cast<uint64_t>(( cumulative_difficulties[N] - cumulative_difficulties[0] )/ N);
|
||||
|
||||
// Prevent round off error for small D and overflow for large D.
|
||||
if (avg_D > 2000000*N*N*T) {
|
||||
next_D = (avg_D/(200*L))*(N*(N+1)*T*99);
|
||||
}
|
||||
else { next_D = (avg_D*N*(N+1)*T*99)/(200*L); }
|
||||
|
||||
// Make all insignificant digits zero for easy reading.
|
||||
i = 1000000000;
|
||||
while (i > 1) {
|
||||
if ( next_D > i*100 ) { next_D = ((next_D+i/2)/i)*i; break; }
|
||||
else { i /= 10; }
|
||||
}
|
||||
return next_D;
|
||||
}
|
||||
}
|
||||
|
||||
@@ -59,6 +59,10 @@ namespace cryptonote
|
||||
bool check_hash_128(const crypto::hash &hash, difficulty_type difficulty);
|
||||
bool check_hash(const crypto::hash &hash, difficulty_type difficulty);
|
||||
difficulty_type next_difficulty(std::vector<std::uint64_t> timestamps, std::vector<difficulty_type> cumulative_difficulties, size_t target_seconds);
|
||||
difficulty_type next_difficulty_v2(std::vector<std::uint64_t> timestamps, std::vector<difficulty_type> cumulative_difficulties, size_t target_seconds);
|
||||
difficulty_type next_difficulty_v3(std::vector<std::uint64_t> timestamps, std::vector<difficulty_type> cumulative_difficulties);
|
||||
difficulty_type next_difficulty_v4(std::vector<std::uint64_t> timestamps, std::vector<difficulty_type> cumulative_difficulties, size_t height);
|
||||
difficulty_type next_difficulty_v5(std::vector<std::uint64_t> timestamps, std::vector<difficulty_type> cumulative_difficulties, uint64_t T, uint64_t N, uint64_t HEIGHT, uint64_t FORK_HEIGHT, uint64_t difficulty_guess);
|
||||
|
||||
std::string hex(difficulty_type v);
|
||||
}
|
||||
|
||||
@@ -37,8 +37,10 @@
|
||||
#include "syncobj.h"
|
||||
#include "cryptonote_basic_impl.h"
|
||||
#include "cryptonote_format_utils.h"
|
||||
#include "cryptonote_core/cryptonote_tx_utils.h"
|
||||
#include "file_io_utils.h"
|
||||
#include "common/command_line.h"
|
||||
#include "common/util.h"
|
||||
#include "string_coding.h"
|
||||
#include "string_tools.h"
|
||||
#include "storages/portable_storage_template_helper.h"
|
||||
@@ -99,12 +101,13 @@ namespace cryptonote
|
||||
}
|
||||
|
||||
|
||||
miner::miner(i_miner_handler* phandler):m_stop(1),
|
||||
miner::miner(i_miner_handler* phandler, Blockchain* pbc):m_stop(1),
|
||||
m_template(boost::value_initialized<block>()),
|
||||
m_template_no(0),
|
||||
m_diffic(0),
|
||||
m_thread_index(0),
|
||||
m_phandler(phandler),
|
||||
m_pbc(pbc),
|
||||
m_height(0),
|
||||
m_threads_active(0),
|
||||
m_pausers_count(0),
|
||||
@@ -123,7 +126,7 @@ namespace cryptonote
|
||||
m_miner_extra_sleep(BACKGROUND_MINING_DEFAULT_MINER_EXTRA_SLEEP_MILLIS),
|
||||
m_block_reward(0)
|
||||
{
|
||||
|
||||
m_attrs.set_stack_size(THREAD_STACK_SIZE);
|
||||
}
|
||||
//-----------------------------------------------------------------------------------------------------
|
||||
miner::~miner()
|
||||
@@ -360,7 +363,7 @@ namespace cryptonote
|
||||
return m_threads_total;
|
||||
}
|
||||
//-----------------------------------------------------------------------------------------------------
|
||||
bool miner::start(const account_public_address& adr, size_t threads_count, const boost::thread::attributes& attrs, bool do_background, bool ignore_battery)
|
||||
bool miner::start(const account_public_address& adr, size_t threads_count, bool do_background, bool ignore_battery)
|
||||
{
|
||||
m_block_reward = 0;
|
||||
m_mine_address = adr;
|
||||
@@ -371,7 +374,6 @@ namespace cryptonote
|
||||
m_threads_autodetect.push_back({epee::misc_utils::get_ns_count(), m_total_hashes});
|
||||
m_threads_total = 1;
|
||||
}
|
||||
m_attrs = attrs;
|
||||
m_starter_nonce = crypto::rand<uint32_t>();
|
||||
CRITICAL_REGION_LOCAL(m_threads_lock);
|
||||
if(is_mining())
|
||||
@@ -395,7 +397,7 @@ namespace cryptonote
|
||||
|
||||
for(size_t i = 0; i != m_threads_total; i++)
|
||||
{
|
||||
m_threads.push_back(boost::thread(attrs, boost::bind(&miner::worker_thread, this)));
|
||||
m_threads.push_back(boost::thread(m_attrs, boost::bind(&miner::worker_thread, this)));
|
||||
}
|
||||
|
||||
if (threads_count == 0)
|
||||
@@ -405,7 +407,7 @@ namespace cryptonote
|
||||
|
||||
if( get_is_background_mining_enabled() )
|
||||
{
|
||||
m_background_mining_thread = boost::thread(attrs, boost::bind(&miner::background_worker_thread, this));
|
||||
m_background_mining_thread = boost::thread(m_attrs, boost::bind(&miner::background_worker_thread, this));
|
||||
LOG_PRINT_L0("Background mining controller thread started" );
|
||||
}
|
||||
|
||||
@@ -466,12 +468,12 @@ namespace cryptonote
|
||||
return true;
|
||||
}
|
||||
//-----------------------------------------------------------------------------------------------------
|
||||
bool miner::find_nonce_for_given_block(block& bl, const difficulty_type& diffic, uint64_t height)
|
||||
bool miner::find_nonce_for_given_block(const Blockchain *pbc, block& bl, const difficulty_type& diffic, uint64_t height)
|
||||
{
|
||||
for(; bl.nonce != std::numeric_limits<uint32_t>::max(); bl.nonce++)
|
||||
{
|
||||
crypto::hash h;
|
||||
get_block_longhash(bl, h, height);
|
||||
get_block_longhash(pbc, bl, h, height, tools::get_max_concurrency());
|
||||
|
||||
if(check_hash(h, diffic))
|
||||
{
|
||||
@@ -487,10 +489,7 @@ namespace cryptonote
|
||||
{
|
||||
if(m_do_mining)
|
||||
{
|
||||
boost::thread::attributes attrs;
|
||||
attrs.set_stack_size(THREAD_STACK_SIZE);
|
||||
|
||||
start(m_mine_address, m_threads_total, attrs, get_is_background_mining_enabled(), get_ignore_battery());
|
||||
start(m_mine_address, m_threads_total, get_is_background_mining_enabled(), get_ignore_battery());
|
||||
}
|
||||
}
|
||||
//-----------------------------------------------------------------------------------------------------
|
||||
@@ -570,7 +569,7 @@ namespace cryptonote
|
||||
|
||||
b.nonce = nonce;
|
||||
crypto::hash h;
|
||||
get_block_longhash(b, h, height);
|
||||
get_block_longhash(m_pbc, b, h, height, tools::get_max_concurrency());
|
||||
|
||||
if(check_hash(h, local_diff))
|
||||
{
|
||||
|
||||
@@ -52,19 +52,21 @@ namespace cryptonote
|
||||
~i_miner_handler(){};
|
||||
};
|
||||
|
||||
class Blockchain;
|
||||
|
||||
/************************************************************************/
|
||||
/* */
|
||||
/************************************************************************/
|
||||
class miner
|
||||
{
|
||||
public:
|
||||
miner(i_miner_handler* phandler);
|
||||
miner(i_miner_handler* phandler, Blockchain* pbc);
|
||||
~miner();
|
||||
bool init(const boost::program_options::variables_map& vm, network_type nettype);
|
||||
static void init_options(boost::program_options::options_description& desc);
|
||||
bool set_block_template(const block& bl, const difficulty_type& diffic, uint64_t height, uint64_t block_reward);
|
||||
bool on_block_chain_update();
|
||||
bool start(const account_public_address& adr, size_t threads_count, const boost::thread::attributes& attrs, bool do_background = false, bool ignore_battery = false);
|
||||
bool start(const account_public_address& adr, size_t threads_count, bool do_background = false, bool ignore_battery = false);
|
||||
uint64_t get_speed() const;
|
||||
uint32_t get_threads_count() const;
|
||||
void send_stop_signal();
|
||||
@@ -74,7 +76,7 @@ namespace cryptonote
|
||||
bool on_idle();
|
||||
void on_synchronized();
|
||||
//synchronous analog (for fast calls)
|
||||
static bool find_nonce_for_given_block(block& bl, const difficulty_type& diffic, uint64_t height);
|
||||
static bool find_nonce_for_given_block(const Blockchain *pbc, block& bl, const difficulty_type& diffic, uint64_t height);
|
||||
void pause();
|
||||
void resume();
|
||||
void do_print_hashrate(bool do_hr);
|
||||
@@ -133,6 +135,7 @@ namespace cryptonote
|
||||
std::list<boost::thread> m_threads;
|
||||
epee::critical_section m_threads_lock;
|
||||
i_miner_handler* m_phandler;
|
||||
Blockchain* m_pbc;
|
||||
account_public_address m_mine_address;
|
||||
epee::math_helper::once_a_time_seconds<5> m_update_block_template_interval;
|
||||
epee::math_helper::once_a_time_seconds<2> m_update_merge_hr_interval;
|
||||
|
||||
@@ -43,17 +43,19 @@
|
||||
#define CRYPTONOTE_PUBLIC_ADDRESS_TEXTBLOB_VER 0
|
||||
#define CRYPTONOTE_MINED_MONEY_UNLOCK_WINDOW 60
|
||||
#define CURRENT_TRANSACTION_VERSION 2
|
||||
#define CURRENT_BLOCK_MAJOR_VERSION 1
|
||||
#define CURRENT_BLOCK_MINOR_VERSION 0
|
||||
#define CURRENT_BLOCK_MAJOR_VERSION 7
|
||||
#define CURRENT_BLOCK_MINOR_VERSION 7
|
||||
#define CRYPTONOTE_BLOCK_FUTURE_TIME_LIMIT_V2 300*2
|
||||
#define CRYPTONOTE_BLOCK_FUTURE_TIME_LIMIT 60*60*2
|
||||
#define CRYPTONOTE_DEFAULT_TX_SPENDABLE_AGE 10
|
||||
#define CRYPTONOTE_DEFAULT_TX_SPENDABLE_AGE 4
|
||||
|
||||
#define BLOCKCHAIN_TIMESTAMP_CHECK_WINDOW_V2 11
|
||||
#define BLOCKCHAIN_TIMESTAMP_CHECK_WINDOW 60
|
||||
|
||||
// MONEY_SUPPLY - total number coins to be generated
|
||||
#define MONEY_SUPPLY ((uint64_t)(-1))
|
||||
#define EMISSION_SPEED_FACTOR_PER_MINUTE (20)
|
||||
#define FINAL_SUBSIDY_PER_MINUTE ((uint64_t)300000000000) // 3 * pow(10, 11)
|
||||
#define EMISSION_SPEED_FACTOR_PER_MINUTE (24)
|
||||
#define FINAL_SUBSIDY_PER_MINUTE ((uint64_t)(0))
|
||||
|
||||
#define CRYPTONOTE_REWARD_BLOCKS_WINDOW 100
|
||||
#define CRYPTONOTE_BLOCK_GRANTED_FULL_REWARD_ZONE_V2 60000 //size of block (bytes) after which reward for block calculated using block size
|
||||
@@ -62,9 +64,9 @@
|
||||
#define CRYPTONOTE_LONG_TERM_BLOCK_WEIGHT_WINDOW_SIZE 100000 // size in blocks of the long term block weight median window
|
||||
#define CRYPTONOTE_SHORT_TERM_BLOCK_WEIGHT_SURGE_FACTOR 50
|
||||
#define CRYPTONOTE_COINBASE_BLOB_RESERVED_SIZE 600
|
||||
#define CRYPTONOTE_DISPLAY_DECIMAL_POINT 12
|
||||
#define CRYPTONOTE_DISPLAY_DECIMAL_POINT 11
|
||||
// COIN - number of smallest units in one coin
|
||||
#define COIN ((uint64_t)1000000000000) // pow(10, 12)
|
||||
#define COIN ((uint64_t)100000000000) // pow(10, 11)
|
||||
|
||||
#define FEE_PER_KB_OLD ((uint64_t)10000000000) // pow(10, 10)
|
||||
#define FEE_PER_KB ((uint64_t)2000000000) // 2 * pow(10, 9)
|
||||
@@ -77,13 +79,18 @@
|
||||
#define ORPHANED_BLOCKS_MAX_COUNT 100
|
||||
|
||||
|
||||
#define DIFFICULTY_TARGET_V2 120 // seconds
|
||||
#define DIFFICULTY_TARGET_V1 60 // seconds - before first fork
|
||||
#define DIFFICULTY_TARGET_V2 300
|
||||
#define DIFFICULTY_TARGET_V1 300
|
||||
#define DIFFICULTY_WINDOW_V3 144
|
||||
#define DIFFICULTY_WINDOW_V2 60
|
||||
#define DIFFICULTY_WINDOW 720 // blocks
|
||||
#define DIFFICULTY_LAG 15 // !!!
|
||||
#define DIFFICULTY_CUT 60 // timestamps to cut after sorting
|
||||
#define DIFFICULTY_BLOCKS_COUNT_V3 DIFFICULTY_WINDOW_V3 + 1 // added +1 to make N=N
|
||||
#define DIFFICULTY_BLOCKS_COUNT_V2 DIFFICULTY_WINDOW_V2 + 1 // added +1 to make N=N
|
||||
#define DIFFICULTY_BLOCKS_COUNT DIFFICULTY_WINDOW + DIFFICULTY_LAG
|
||||
|
||||
#define DIFFICULTY_FORK_HEIGHT 81769 // ~14 February 2019
|
||||
#define DIFFICULTY_RESET 10000000 // 10 million
|
||||
|
||||
#define CRYPTONOTE_LOCKED_TX_ALLOWED_DELTA_SECONDS_V1 DIFFICULTY_TARGET_V1 * CRYPTONOTE_LOCKED_TX_ALLOWED_DELTA_BLOCKS
|
||||
#define CRYPTONOTE_LOCKED_TX_ALLOWED_DELTA_SECONDS_V2 DIFFICULTY_TARGET_V2 * CRYPTONOTE_LOCKED_TX_ALLOWED_DELTA_BLOCKS
|
||||
@@ -96,6 +103,7 @@
|
||||
#define BLOCKS_IDS_SYNCHRONIZING_DEFAULT_COUNT 10000 //by default, blocks ids count in synchronizing
|
||||
#define BLOCKS_SYNCHRONIZING_DEFAULT_COUNT_PRE_V4 100 //by default, blocks count in blocks downloading
|
||||
#define BLOCKS_SYNCHRONIZING_DEFAULT_COUNT 20 //by default, blocks count in blocks downloading
|
||||
#define BLOCKS_SYNCHRONIZING_MAX_COUNT 2048 //must be a power of 2, greater than 128, equal to SEEDHASH_EPOCH_BLOCKS
|
||||
|
||||
#define CRYPTONOTE_MEMPOOL_TX_LIVETIME (86400*3) //seconds, three days
|
||||
#define CRYPTONOTE_MEMPOOL_TX_FROM_ALT_BLOCK_LIVETIME 604800 //seconds, one week
|
||||
@@ -130,7 +138,7 @@
|
||||
|
||||
#define ALLOW_DEBUG_COMMANDS
|
||||
|
||||
#define CRYPTONOTE_NAME "bitmonero"
|
||||
#define CRYPTONOTE_NAME "wownero"
|
||||
#define CRYPTONOTE_POOLDATA_FILENAME "poolstate.bin"
|
||||
#define CRYPTONOTE_BLOCKCHAINDATA_FILENAME "data.mdb"
|
||||
#define CRYPTONOTE_BLOCKCHAINDATA_LOCK_FILENAME "lock.mdb"
|
||||
@@ -141,12 +149,12 @@
|
||||
|
||||
#define HF_VERSION_DYNAMIC_FEE 4
|
||||
#define HF_VERSION_MIN_MIXIN_4 6
|
||||
#define HF_VERSION_MIN_MIXIN_6 7
|
||||
#define HF_VERSION_MIN_MIXIN_10 8
|
||||
#define HF_VERSION_MIN_MIXIN_7 7
|
||||
#define HF_VERSION_MIN_MIXIN_21 9
|
||||
#define HF_VERSION_ENFORCE_RCT 6
|
||||
#define HF_VERSION_PER_BYTE_FEE 8
|
||||
#define HF_VERSION_SMALLER_BP 10
|
||||
#define HF_VERSION_LONG_TERM_BLOCK_WEIGHT 10
|
||||
#define HF_VERSION_PER_BYTE_FEE 12
|
||||
#define HF_VERSION_LONG_TERM_BLOCK_WEIGHT 13
|
||||
#define HF_VERSION_SMALLER_BP 13
|
||||
|
||||
#define PER_KB_FEE_QUANTIZATION_DECIMALS 8
|
||||
|
||||
@@ -170,31 +178,31 @@ namespace config
|
||||
uint64_t const BASE_REWARD_CLAMP_THRESHOLD = ((uint64_t)100000000); // pow(10, 8)
|
||||
std::string const P2P_REMOTE_DEBUG_TRUSTED_PUB_KEY = "0000000000000000000000000000000000000000000000000000000000000000";
|
||||
|
||||
uint64_t const CRYPTONOTE_PUBLIC_ADDRESS_BASE58_PREFIX = 18;
|
||||
uint64_t const CRYPTONOTE_PUBLIC_INTEGRATED_ADDRESS_BASE58_PREFIX = 19;
|
||||
uint64_t const CRYPTONOTE_PUBLIC_SUBADDRESS_BASE58_PREFIX = 42;
|
||||
uint16_t const P2P_DEFAULT_PORT = 18080;
|
||||
uint16_t const RPC_DEFAULT_PORT = 18081;
|
||||
uint16_t const ZMQ_RPC_DEFAULT_PORT = 18082;
|
||||
uint64_t const CRYPTONOTE_PUBLIC_ADDRESS_BASE58_PREFIX = 4146;
|
||||
uint64_t const CRYPTONOTE_PUBLIC_INTEGRATED_ADDRESS_BASE58_PREFIX = 6810;
|
||||
uint64_t const CRYPTONOTE_PUBLIC_SUBADDRESS_BASE58_PREFIX = 12208;
|
||||
uint16_t const P2P_DEFAULT_PORT = 34567;
|
||||
uint16_t const RPC_DEFAULT_PORT = 34568;
|
||||
uint16_t const ZMQ_RPC_DEFAULT_PORT = 34569;
|
||||
boost::uuids::uuid const NETWORK_ID = { {
|
||||
0x12 ,0x30, 0xF1, 0x71 , 0x61, 0x04 , 0x41, 0x61, 0x17, 0x31, 0x00, 0x82, 0x16, 0xA1, 0xA1, 0x10
|
||||
0x11, 0x33, 0xFF, 0x77 , 0x61, 0x04 , 0x41, 0x61, 0x17, 0x31, 0x00, 0x82, 0x16, 0xA1, 0xA1, 0x10
|
||||
} }; // Bender's nightmare
|
||||
std::string const GENESIS_TX = "013c01ff0001ffffffffffff03029b2e4c0281c0b02e7c53291a94d1d0cbff8883f8024f5142ee494ffbbd08807121017767aafcde9be00dcfd098715ebcf7f410daebc582fda69d24a28e9d0bc890d1";
|
||||
uint32_t const GENESIS_NONCE = 10000;
|
||||
std::string const GENESIS_TX = "013c01ff0001ffffffffff1f029b2e4c0281c0b02e7c53291a94d1d0cbff8883f8024f5142ee494ffbbd08807121012a1a936be5d91c01ee876e38c13fab0ee11cbe86011a2bf7740fb5ebd39d267d";
|
||||
uint32_t const GENESIS_NONCE = 70;
|
||||
|
||||
namespace testnet
|
||||
{
|
||||
uint64_t const CRYPTONOTE_PUBLIC_ADDRESS_BASE58_PREFIX = 53;
|
||||
uint64_t const CRYPTONOTE_PUBLIC_INTEGRATED_ADDRESS_BASE58_PREFIX = 54;
|
||||
uint64_t const CRYPTONOTE_PUBLIC_SUBADDRESS_BASE58_PREFIX = 63;
|
||||
uint16_t const P2P_DEFAULT_PORT = 28080;
|
||||
uint16_t const RPC_DEFAULT_PORT = 28081;
|
||||
uint16_t const ZMQ_RPC_DEFAULT_PORT = 28082;
|
||||
uint16_t const P2P_DEFAULT_PORT = 11180;
|
||||
uint16_t const RPC_DEFAULT_PORT = 11181;
|
||||
uint16_t const ZMQ_RPC_DEFAULT_PORT = 11182;
|
||||
boost::uuids::uuid const NETWORK_ID = { {
|
||||
0x12 ,0x30, 0xF1, 0x71 , 0x61, 0x04 , 0x41, 0x61, 0x17, 0x31, 0x00, 0x82, 0x16, 0xA1, 0xA1, 0x11
|
||||
0x11, 0x33, 0xFF, 0x77 , 0x61, 0x04 , 0x41, 0x61, 0x17, 0x31, 0x00, 0x82, 0x16, 0xA1, 0xA1, 0x11
|
||||
} }; // Bender's daydream
|
||||
std::string const GENESIS_TX = "013c01ff0001ffffffffffff03029b2e4c0281c0b02e7c53291a94d1d0cbff8883f8024f5142ee494ffbbd08807121017767aafcde9be00dcfd098715ebcf7f410daebc582fda69d24a28e9d0bc890d1";
|
||||
uint32_t const GENESIS_NONCE = 10001;
|
||||
std::string const GENESIS_TX = "013c01ff0001ffffffffff1f029b2e4c0281c0b02e7c53291a94d1d0cbff8883f8024f5142ee494ffbbd088071210160eb755f618a2336055dee60f307fe0ded81c5b37b53d310175ca9ee69b0c8ad";
|
||||
uint32_t const GENESIS_NONCE = 70;
|
||||
}
|
||||
|
||||
namespace stagenet
|
||||
|
||||
File diff suppressed because it is too large
Load Diff
@@ -91,17 +91,6 @@ namespace cryptonote
|
||||
class Blockchain
|
||||
{
|
||||
public:
|
||||
/**
|
||||
* @brief Now-defunct (TODO: remove) struct from in-memory blockchain
|
||||
*/
|
||||
struct transaction_chain_entry
|
||||
{
|
||||
transaction tx;
|
||||
uint64_t m_keeper_block_height;
|
||||
size_t m_blob_size;
|
||||
std::vector<uint64_t> m_global_output_indexes;
|
||||
};
|
||||
|
||||
/**
|
||||
* @brief container for passing a block and metadata about it on the blockchain
|
||||
*/
|
||||
@@ -109,7 +98,7 @@ namespace cryptonote
|
||||
{
|
||||
block bl; //!< the block
|
||||
uint64_t height; //!< the height of the block in the blockchain
|
||||
size_t block_cumulative_weight; //!< the weight of the block
|
||||
uint64_t block_cumulative_weight; //!< the weight of the block
|
||||
difficulty_type cumulative_difficulty; //!< the accumulated difficulty after that block
|
||||
uint64_t already_generated_coins; //!< the total coins minted after that block
|
||||
};
|
||||
@@ -216,6 +205,18 @@ namespace cryptonote
|
||||
*/
|
||||
crypto::hash get_block_id_by_height(uint64_t height) const;
|
||||
|
||||
/**
|
||||
* @brief gets a block's hash given a height
|
||||
*
|
||||
* Used only by prepare_handle_incoming_blocks. Will look in the list of incoming blocks
|
||||
* if the height is contained there.
|
||||
*
|
||||
* @param height the height of the block
|
||||
*
|
||||
* @return the hash of the block at the requested height, or a zeroed hash if there is no such block
|
||||
*/
|
||||
crypto::hash get_pending_block_id_by_height(uint64_t height) const;
|
||||
|
||||
/**
|
||||
* @brief gets the block with a given hash
|
||||
*
|
||||
@@ -1011,20 +1012,12 @@ namespace cryptonote
|
||||
#endif
|
||||
|
||||
// TODO: evaluate whether or not each of these typedefs are left over from blockchain_storage
|
||||
typedef std::unordered_map<crypto::hash, size_t> blocks_by_id_index;
|
||||
|
||||
typedef std::unordered_map<crypto::hash, transaction_chain_entry> transactions_container;
|
||||
|
||||
typedef std::unordered_set<crypto::key_image> key_images_container;
|
||||
|
||||
typedef std::vector<block_extended_info> blocks_container;
|
||||
|
||||
typedef std::unordered_map<crypto::hash, block_extended_info> blocks_ext_by_hash;
|
||||
|
||||
typedef std::unordered_map<crypto::hash, block> blocks_by_hash;
|
||||
|
||||
typedef std::map<uint64_t, std::vector<std::pair<crypto::hash, size_t>>> outputs_container; //crypto::hash - tx hash, size_t - index of out in transaction
|
||||
|
||||
|
||||
BlockchainDB* m_db;
|
||||
|
||||
@@ -1033,7 +1026,6 @@ namespace cryptonote
|
||||
mutable epee::critical_section m_blockchain_lock; // TODO: add here reader/writer lock
|
||||
|
||||
// main chain
|
||||
transactions_container m_transactions;
|
||||
size_t m_current_block_cumul_weight_limit;
|
||||
size_t m_current_block_cumul_weight_median;
|
||||
|
||||
@@ -1074,9 +1066,6 @@ namespace cryptonote
|
||||
boost::thread_group m_async_pool;
|
||||
std::unique_ptr<boost::asio::io_service::work> m_async_work_idle;
|
||||
|
||||
// all alternative chains
|
||||
blocks_ext_by_hash m_alternative_chains; // crypto::hash -> block_extended_info
|
||||
|
||||
// some invalid blocks
|
||||
blocks_ext_by_hash m_invalid_blocks; // crypto::hash -> block_extended_info
|
||||
|
||||
@@ -1102,9 +1091,17 @@ namespace cryptonote
|
||||
uint64_t m_btc_expected_reward;
|
||||
bool m_btc_valid;
|
||||
|
||||
|
||||
bool m_batch_success;
|
||||
|
||||
std::shared_ptr<tools::Notify> m_block_notify;
|
||||
std::shared_ptr<tools::Notify> m_reorg_notify;
|
||||
|
||||
// for prepare_handle_incoming_blocks
|
||||
uint64_t m_prepare_height;
|
||||
uint64_t m_prepare_nblocks;
|
||||
std::vector<block> *m_prepare_blocks;
|
||||
|
||||
/**
|
||||
* @brief collects the keys for all outputs being "spent" as an input
|
||||
*
|
||||
@@ -1183,7 +1180,7 @@ namespace cryptonote
|
||||
*
|
||||
* @return false if the reorganization fails, otherwise true
|
||||
*/
|
||||
bool switch_to_alternative_blockchain(std::list<blocks_ext_by_hash::const_iterator>& alt_chain, bool discard_disconnected_chain);
|
||||
bool switch_to_alternative_blockchain(std::list<block_extended_info>& alt_chain, bool discard_disconnected_chain);
|
||||
|
||||
/**
|
||||
* @brief removes the most recent block from the blockchain
|
||||
@@ -1246,7 +1243,7 @@ namespace cryptonote
|
||||
*
|
||||
* @return true on success, false otherwise
|
||||
*/
|
||||
bool build_alt_chain(const crypto::hash &prev_id, std::list<blocks_ext_by_hash::const_iterator>& alt_chain, std::vector<uint64_t> ×tamps, block_verification_context& bvc) const;
|
||||
bool build_alt_chain(const crypto::hash &prev_id, std::list<block_extended_info>& alt_chain, std::vector<uint64_t> ×tamps, block_verification_context& bvc) const;
|
||||
|
||||
/**
|
||||
* @brief gets the difficulty requirement for a new block on an alternate chain
|
||||
@@ -1256,7 +1253,7 @@ namespace cryptonote
|
||||
*
|
||||
* @return the difficulty requirement
|
||||
*/
|
||||
difficulty_type get_next_difficulty_for_alternative_chain(const std::list<blocks_ext_by_hash::const_iterator>& alt_chain, block_extended_info& bei) const;
|
||||
difficulty_type get_next_difficulty_for_alternative_chain(const std::list<block_extended_info>& alt_chain, block_extended_info& bei) const;
|
||||
|
||||
/**
|
||||
* @brief sanity checks a miner transaction before validating an entire block
|
||||
|
||||
@@ -208,12 +208,17 @@ namespace cryptonote
|
||||
"is acted upon."
|
||||
, ""
|
||||
};
|
||||
static const command_line::arg_descriptor<bool> arg_keep_alt_blocks = {
|
||||
"keep-alt-blocks"
|
||||
, "Keep alternative blocks on restart"
|
||||
, false
|
||||
};
|
||||
|
||||
//-----------------------------------------------------------------------------------------------
|
||||
core::core(i_cryptonote_protocol* pprotocol):
|
||||
m_mempool(m_blockchain_storage),
|
||||
m_blockchain_storage(m_mempool),
|
||||
m_miner(this),
|
||||
m_miner(this, &m_blockchain_storage),
|
||||
m_miner_address(boost::value_initialized<account_public_address>()),
|
||||
m_starter_message_showed(false),
|
||||
m_target_blockchain_height(0),
|
||||
@@ -325,6 +330,7 @@ namespace cryptonote
|
||||
command_line::add_arg(desc, arg_prune_blockchain);
|
||||
command_line::add_arg(desc, arg_reorg_notify);
|
||||
command_line::add_arg(desc, arg_block_rate_notify);
|
||||
command_line::add_arg(desc, arg_keep_alt_blocks);
|
||||
|
||||
miner::init_options(desc);
|
||||
BlockchainDB::init_options(desc);
|
||||
@@ -456,6 +462,7 @@ namespace cryptonote
|
||||
std::string check_updates_string = command_line::get_arg(vm, arg_check_updates);
|
||||
size_t max_txpool_weight = command_line::get_arg(vm, arg_max_txpool_weight);
|
||||
bool prune_blockchain = command_line::get_arg(vm, arg_prune_blockchain);
|
||||
bool keep_alt_blocks = command_line::get_arg(vm, arg_keep_alt_blocks);
|
||||
|
||||
boost::filesystem::path folder(m_config_folder);
|
||||
if (m_nettype == FAKECHAIN)
|
||||
@@ -472,8 +479,8 @@ namespace cryptonote
|
||||
if (boost::filesystem::exists(old_files / "blockchain.bin"))
|
||||
{
|
||||
MWARNING("Found old-style blockchain.bin in " << old_files.string());
|
||||
MWARNING("Monero now uses a new format. You can either remove blockchain.bin to start syncing");
|
||||
MWARNING("the blockchain anew, or use monero-blockchain-export and monero-blockchain-import to");
|
||||
MWARNING("Wownero now uses a new format. You can either remove blockchain.bin to start syncing");
|
||||
MWARNING("the blockchain anew, or use wownero-blockchain-export and wownero-blockchain-import to");
|
||||
MWARNING("convert your existing blockchain.bin to the new format. See README.md for instructions.");
|
||||
return false;
|
||||
}
|
||||
@@ -647,6 +654,8 @@ namespace cryptonote
|
||||
CHECK_AND_ASSERT_MES(r, false, "Failed to initialize blockchain storage");
|
||||
|
||||
block_sync_size = command_line::get_arg(vm, arg_block_sync_size);
|
||||
if (block_sync_size > BLOCKS_SYNCHRONIZING_MAX_COUNT)
|
||||
MERROR("Error --dblock-sync-size cannot be greater than " << BLOCKS_SYNCHRONIZING_MAX_COUNT);
|
||||
|
||||
MGINFO("Loading checkpoints");
|
||||
|
||||
@@ -671,12 +680,21 @@ namespace cryptonote
|
||||
r = m_miner.init(vm, m_nettype);
|
||||
CHECK_AND_ASSERT_MES(r, false, "Failed to initialize miner instance");
|
||||
|
||||
if (!keep_alt_blocks && !m_blockchain_storage.get_db().is_read_only())
|
||||
m_blockchain_storage.get_db().drop_alt_blocks();
|
||||
|
||||
if (prune_blockchain)
|
||||
{
|
||||
// display a message if the blockchain is not pruned yet
|
||||
if (m_blockchain_storage.get_current_blockchain_height() > 1 && !m_blockchain_storage.get_blockchain_pruning_seed())
|
||||
{
|
||||
MGINFO("Pruning blockchain...");
|
||||
CHECK_AND_ASSERT_MES(m_blockchain_storage.prune_blockchain(), false, "Failed to prune blockchain");
|
||||
CHECK_AND_ASSERT_MES(m_blockchain_storage.prune_blockchain(), false, "Failed to prune blockchain");
|
||||
}
|
||||
else
|
||||
{
|
||||
CHECK_AND_ASSERT_MES(m_blockchain_storage.update_blockchain_pruning(), false, "Failed to update blockchain pruning");
|
||||
}
|
||||
}
|
||||
|
||||
return load_state_data();
|
||||
@@ -783,6 +801,44 @@ namespace cryptonote
|
||||
return false;
|
||||
}
|
||||
|
||||
// resolve outPk references in rct txes
|
||||
// outPk aren't the only thing that need resolving for a fully resolved tx,
|
||||
// but outPk (1) are needed now to check range proof semantics, and
|
||||
// (2) do not need access to the blockchain to find data
|
||||
if (tx.version >= 2)
|
||||
{
|
||||
rct::rctSig &rv = tx.rct_signatures;
|
||||
if (!rct::is_rct_new_bulletproof(rv.type)){
|
||||
if (rv.outPk.size() != tx.vout.size())
|
||||
{
|
||||
LOG_PRINT_L1("WRONG TRANSACTION BLOB, Bad outPk size in tx " << tx_hash << ", rejected");
|
||||
tvc.m_verifivation_failed = true;
|
||||
return false;
|
||||
}
|
||||
for (size_t n = 0; n < tx.rct_signatures.outPk.size(); ++n)
|
||||
rv.outPk[n].dest = rct::pk2rct(boost::get<txout_to_key>(tx.vout[n].target).key);
|
||||
const bool bulletproof = rct::is_rct_bulletproof(rv.type);
|
||||
if (bulletproof)
|
||||
{
|
||||
if (rct::n_bulletproof_v1_amounts(rv.p.bulletproofs) != tx.vout.size())
|
||||
{
|
||||
LOG_PRINT_L1("WRONG TRANSACTION BLOB, Bad bulletproofs size in tx " << tx_hash << ", rejected");
|
||||
tvc.m_verifivation_failed = true;
|
||||
return false;
|
||||
}
|
||||
size_t idx = 0;
|
||||
for (size_t n = 0; n < rv.p.bulletproofs.size(); ++n)
|
||||
{
|
||||
CHECK_AND_ASSERT_MES(rv.p.bulletproofs[n].L.size() >= 6, false, "Bad bulletproofs L size"); // at least 64 bits
|
||||
const size_t n_amounts = rct::n_bulletproof_v1_amounts(rv.p.bulletproofs[n]);
|
||||
CHECK_AND_ASSERT_MES(idx + n_amounts <= rv.outPk.size(), false, "Internal error filling out V");
|
||||
rv.p.bulletproofs[n].V.clear();
|
||||
for (size_t i = 0; i < n_amounts; ++i)
|
||||
rv.p.bulletproofs[n].V.push_back(rv.outPk[idx++].mask);
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
return true;
|
||||
}
|
||||
//-----------------------------------------------------------------------------------------------
|
||||
@@ -841,6 +897,7 @@ namespace cryptonote
|
||||
tx_info[n].result = false;
|
||||
break;
|
||||
case rct::RCTTypeSimple:
|
||||
case rct::RCTTypeSimpleBulletproof:
|
||||
if (!rct::verRctSemanticsSimple(rv))
|
||||
{
|
||||
MERROR_VER("rct signature semantics check failed");
|
||||
@@ -851,6 +908,7 @@ namespace cryptonote
|
||||
}
|
||||
break;
|
||||
case rct::RCTTypeFull:
|
||||
case rct::RCTTypeFullBulletproof:
|
||||
if (!rct::verRct(rv, true))
|
||||
{
|
||||
MERROR_VER("rct signature semantics check failed");
|
||||
@@ -1115,7 +1173,7 @@ namespace cryptonote
|
||||
//-----------------------------------------------------------------------------------------------
|
||||
size_t core::get_block_sync_size(uint64_t height) const
|
||||
{
|
||||
static const uint64_t quick_height = m_nettype == TESTNET ? 801219 : m_nettype == MAINNET ? 1220516 : 0;
|
||||
static const uint64_t quick_height = m_nettype == TESTNET ? 801219 : m_nettype == MAINNET ? 53666 : 0;
|
||||
if (block_sync_size > 0)
|
||||
return block_sync_size;
|
||||
if (height >= quick_height)
|
||||
@@ -1584,14 +1642,47 @@ namespace cryptonote
|
||||
main_message = "The daemon is running offline and will not attempt to sync to the Monero network.";
|
||||
else
|
||||
main_message = "The daemon will start synchronizing with the network. This may take a long time to complete.";
|
||||
MGINFO_RED(ENDL <<
|
||||
"\n \n"
|
||||
" .::::. \n"
|
||||
" .::::::::. \n"
|
||||
" ::::::::::: \n"
|
||||
" ':::::::::::.. \n"
|
||||
" :::::::::::::::' \n"
|
||||
" ':::::::::::. \n"
|
||||
" .::::::::::::::' \n"
|
||||
" .:::::::::::... \n"
|
||||
" ::::::::::::::'' \n"
|
||||
" .:::. '::::::::'':::: \n"
|
||||
" .::::::::. ':::::' ':::: \n"
|
||||
" .::::':::::::. ::::: '::::. \n"
|
||||
" .:::::' ':::::::::. ::::: ':::. \n"
|
||||
" .:::::' ':::::::::.::::: '::. \n"
|
||||
" .::::'' ':::::::::::::: '::. \n"
|
||||
" .::'' ':::::::::::: :::... \n"
|
||||
" ..:::: ':::::::::' .:' '''' \n"
|
||||
" ..''''':' ':::::.' \n"
|
||||
" ______ ______ ______ _ \n"
|
||||
" | ____| | ____| | ____| (_) \n"
|
||||
" | |__ | |__ ___ _ __ | |__ __ _ _ __ _ __ ___ _ __ _ _ __ __ _ \n"
|
||||
" | __| | __/ _ || '__| | __/ _` | '_ || '_ | / _ | '_ || | '_ | / _` | \n"
|
||||
" | | | | | (_) | | | | | (_| | |_) | |_) | __/ | | | | | | | (_| | \n"
|
||||
" |_| |_| |___/|_| |_| |__,_| .__/| .__/|____|_| |_|_|_| |_||__, | \n"
|
||||
" | | | | __/ | \n"
|
||||
" |_| |_| |___/ \n"
|
||||
"\n \n" << ENDL);
|
||||
MGINFO_YELLOW(ENDL << "**********************************************************************" << ENDL
|
||||
<< main_message << ENDL
|
||||
<< ENDL
|
||||
<< "Caution: Wownero is highly experimental software compiled by a ragtag team of stoners with as much" << ENDL
|
||||
<< "skill as Verge developers. Storing your life savings in WOW is probably not a good idea." << ENDL
|
||||
<< ENDL
|
||||
<< "You can set the level of process detailization through \"set_log <level|categories>\" command," << ENDL
|
||||
<< "where <level> is between 0 (no details) and 4 (very verbose), or custom category based levels (eg, *:WARNING)." << ENDL
|
||||
<< ENDL
|
||||
<< "Use the \"help\" command to see the list of available commands." << ENDL
|
||||
<< "Use \"help <command>\" to see a command's documentation." << ENDL
|
||||
<< "Use the \"help\" command to see a simplified list of available commands." << ENDL
|
||||
<< "Use the \"help_advanced\" command to see an advanced list of available commands." << ENDL
|
||||
<< "Use \"help_advanced <command>\" to see a command's documentation." << ENDL
|
||||
<< "**********************************************************************" << ENDL);
|
||||
m_starter_message_showed = true;
|
||||
}
|
||||
@@ -1848,7 +1939,7 @@ namespace cryptonote
|
||||
MDEBUG("blocks in the last " << seconds[n] / 60 << " minutes: " << b << " (probability " << p << ")");
|
||||
if (p < threshold)
|
||||
{
|
||||
MWARNING("There were " << b << " blocks in the last " << seconds[n] / 60 << " minutes, there might be large hash rate changes, or we might be partitioned, cut off from the Monero network or under attack. Or it could be just sheer bad luck.");
|
||||
MDEBUG("There were " << b << " blocks in the last " << seconds[n] / 60 << " minutes, there might be large hash rate changes, or we might be partitioned, cut off from the Wownero network or under attack. Or it could be just sheer bad luck.");
|
||||
|
||||
std::shared_ptr<tools::Notify> block_rate_notify = m_block_rate_notify;
|
||||
if (block_rate_notify)
|
||||
|
||||
@@ -37,6 +37,7 @@ using namespace epee;
|
||||
#include "common/apply_permutation.h"
|
||||
#include "cryptonote_tx_utils.h"
|
||||
#include "cryptonote_config.h"
|
||||
#include "blockchain.h"
|
||||
#include "cryptonote_basic/miner.h"
|
||||
#include "cryptonote_basic/tx_extra.h"
|
||||
#include "crypto/crypto.h"
|
||||
@@ -591,7 +592,9 @@ namespace cryptonote
|
||||
crypto::hash tx_prefix_hash;
|
||||
get_transaction_prefix_hash(tx, tx_prefix_hash);
|
||||
rct::ctkeyV outSk;
|
||||
if (use_simple_rct)
|
||||
if (rct_config.range_proof_type != rct::RangeProofPaddedBulletproof && use_simple_rct)
|
||||
tx.rct_signatures = rct::genRctSimple_old(rct::hash2rct(tx_prefix_hash), inSk, destinations, inamounts, outamounts, amount_in - amount_out, mixRing, amount_keys, msout ? &kLRki : NULL, msout, index, outSk, rct_config, hwdev);
|
||||
else if (use_simple_rct && rct_config.range_proof_type == rct::RangeProofPaddedBulletproof)
|
||||
tx.rct_signatures = rct::genRctSimple(rct::hash2rct(tx_prefix_hash), inSk, destinations, inamounts, outamounts, amount_in - amount_out, mixRing, amount_keys, msout ? &kLRki : NULL, msout, index, outSk, rct_config, hwdev);
|
||||
else
|
||||
tx.rct_signatures = rct::genRct(rct::hash2rct(tx_prefix_hash), inSk, destinations, outamounts, mixRing, amount_keys, msout ? &kLRki[0] : NULL, msout, sources[0].real_output, outSk, rct_config, hwdev); // same index assumption
|
||||
@@ -658,9 +661,47 @@ namespace cryptonote
|
||||
bl.minor_version = CURRENT_BLOCK_MINOR_VERSION;
|
||||
bl.timestamp = 0;
|
||||
bl.nonce = nonce;
|
||||
miner::find_nonce_for_given_block(bl, 1, 0);
|
||||
miner::find_nonce_for_given_block(NULL, bl, 1, 0);
|
||||
bl.invalidate_hashes();
|
||||
return true;
|
||||
}
|
||||
//---------------------------------------------------------------
|
||||
void get_altblock_longhash(const block& b, crypto::hash& res, const uint64_t main_height, const uint64_t height, const uint64_t seed_height, const crypto::hash& seed_hash)
|
||||
{
|
||||
blobdata bd = get_block_hashing_blob(b);
|
||||
rx_alt_slowhash(main_height, seed_height, seed_hash.data, bd.data(), bd.size(), res.data);
|
||||
}
|
||||
|
||||
bool get_block_longhash(const Blockchain *pbc, const block& b, crypto::hash& res, const uint64_t height, const int miners)
|
||||
{
|
||||
blobdata bd = get_block_hashing_blob(b);
|
||||
const int pow_variant = b.major_version >= 13 ? 6 : b.major_version >= 11 && b.major_version <= 12 ? 4 : 2;
|
||||
if (pow_variant >= 6) {
|
||||
uint64_t seed_height;
|
||||
if (rx_needhash(height, &seed_height)) {
|
||||
crypto::hash hash;
|
||||
if (pbc != NULL)
|
||||
hash = pbc->get_pending_block_id_by_height(seed_height);
|
||||
else
|
||||
memset(&hash, 0, sizeof(hash)); // only happens when generating genesis block
|
||||
rx_seedhash(seed_height, hash.data, miners);
|
||||
}
|
||||
rx_slow_hash(bd.data(), bd.size(), res.data, miners);
|
||||
} else {
|
||||
crypto::cn_slow_hash(bd.data(), bd.size(), res, pow_variant, height);
|
||||
}
|
||||
return true;
|
||||
}
|
||||
|
||||
crypto::hash get_block_longhash(const Blockchain *pbc, const block& b, const uint64_t height, const int miners)
|
||||
{
|
||||
crypto::hash p = crypto::null_hash;
|
||||
get_block_longhash(pbc, b, p, height, miners);
|
||||
return p;
|
||||
}
|
||||
|
||||
void get_block_longhash_reorg(const uint64_t split_height)
|
||||
{
|
||||
rx_reorg(split_height);
|
||||
}
|
||||
}
|
||||
|
||||
@@ -117,6 +117,13 @@ namespace cryptonote
|
||||
, uint32_t nonce
|
||||
);
|
||||
|
||||
class Blockchain;
|
||||
bool get_block_longhash(const Blockchain *pb, const block& b, crypto::hash& res, const uint64_t height, const int miners);
|
||||
void get_altblock_longhash(const block& b, crypto::hash& res, const uint64_t main_height, const uint64_t height,
|
||||
const uint64_t seed_height, const crypto::hash& seed_hash);
|
||||
crypto::hash get_block_longhash(const Blockchain *pb, const block& b, const uint64_t height, const int miners);
|
||||
void get_block_longhash_reorg(const uint64_t split_height);
|
||||
|
||||
}
|
||||
|
||||
BOOST_CLASS_VERSION(cryptonote::tx_source_entry, 1)
|
||||
|
||||
@@ -82,8 +82,8 @@ namespace cryptonote
|
||||
|
||||
uint64_t get_transaction_weight_limit(uint8_t version)
|
||||
{
|
||||
// from v8, limit a tx to 50% of the minimum block weight
|
||||
if (version >= 8)
|
||||
// from v12, limit a tx to 50% of the minimum block weight
|
||||
if (version >= 12)
|
||||
return get_min_block_weight(version) / 2 - CRYPTONOTE_COINBASE_BLOB_RESERVED_SIZE;
|
||||
else
|
||||
return get_min_block_weight(version) - CRYPTONOTE_COINBASE_BLOB_RESERVED_SIZE;
|
||||
@@ -95,13 +95,17 @@ namespace cryptonote
|
||||
// the whole prepare/handle/cleanup incoming block sequence.
|
||||
class LockedTXN {
|
||||
public:
|
||||
LockedTXN(Blockchain &b): m_blockchain(b), m_batch(false) {
|
||||
LockedTXN(Blockchain &b): m_blockchain(b), m_batch(false), m_active(false) {
|
||||
m_batch = m_blockchain.get_db().batch_start();
|
||||
m_active = true;
|
||||
}
|
||||
~LockedTXN() { try { if (m_batch) { m_blockchain.get_db().batch_stop(); } } catch (const std::exception &e) { MWARNING("LockedTXN dtor filtering exception: " << e.what()); } }
|
||||
void commit() { try { if (m_batch && m_active) { m_blockchain.get_db().batch_stop(); m_active = false; } } catch (const std::exception &e) { MWARNING("LockedTXN::commit filtering exception: " << e.what()); } }
|
||||
void abort() { try { if (m_batch && m_active) { m_blockchain.get_db().batch_abort(); m_active = false; } } catch (const std::exception &e) { MWARNING("LockedTXN::abort filtering exception: " << e.what()); } }
|
||||
~LockedTXN() { abort(); }
|
||||
private:
|
||||
Blockchain &m_blockchain;
|
||||
bool m_batch;
|
||||
bool m_active;
|
||||
};
|
||||
}
|
||||
//---------------------------------------------------------------------------------
|
||||
@@ -255,6 +259,7 @@ namespace cryptonote
|
||||
if (!insert_key_images(tx, id, kept_by_block))
|
||||
return false;
|
||||
m_txs_by_fee_and_receive_time.emplace(std::pair<double, std::time_t>(fee / (double)tx_weight, receive_time), id);
|
||||
lock.commit();
|
||||
}
|
||||
catch (const std::exception &e)
|
||||
{
|
||||
@@ -299,6 +304,7 @@ namespace cryptonote
|
||||
if (!insert_key_images(tx, id, kept_by_block))
|
||||
return false;
|
||||
m_txs_by_fee_and_receive_time.emplace(std::pair<double, std::time_t>(fee / (double)tx_weight, receive_time), id);
|
||||
lock.commit();
|
||||
}
|
||||
catch (const std::exception &e)
|
||||
{
|
||||
@@ -398,6 +404,7 @@ namespace cryptonote
|
||||
return;
|
||||
}
|
||||
}
|
||||
lock.commit();
|
||||
if (changed)
|
||||
++m_cookie;
|
||||
if (m_txpool_weight > bytes)
|
||||
@@ -494,6 +501,7 @@ namespace cryptonote
|
||||
m_blockchain.remove_txpool_tx(id);
|
||||
m_txpool_weight -= tx_weight;
|
||||
remove_transaction_keyimages(tx, id);
|
||||
lock.commit();
|
||||
}
|
||||
catch (const std::exception &e)
|
||||
{
|
||||
@@ -578,6 +586,7 @@ namespace cryptonote
|
||||
// ignore error
|
||||
}
|
||||
}
|
||||
lock.commit();
|
||||
++m_cookie;
|
||||
}
|
||||
return true;
|
||||
@@ -641,6 +650,7 @@ namespace cryptonote
|
||||
// continue
|
||||
}
|
||||
}
|
||||
lock.commit();
|
||||
}
|
||||
//---------------------------------------------------------------------------------
|
||||
size_t tx_memory_pool::get_transactions_count(bool include_unrelayed_txes) const
|
||||
@@ -1119,6 +1129,7 @@ namespace cryptonote
|
||||
}
|
||||
}
|
||||
}
|
||||
lock.commit();
|
||||
if (changed)
|
||||
++m_cookie;
|
||||
}
|
||||
@@ -1271,6 +1282,7 @@ namespace cryptonote
|
||||
append_key_images(k_images, tx);
|
||||
LOG_PRINT_L2(" added, new block weight " << total_weight << "/" << max_total_weight << ", coinbase " << print_money(best_coinbase));
|
||||
}
|
||||
lock.commit();
|
||||
|
||||
expected_reward = best_coinbase;
|
||||
LOG_PRINT_L2("Block template filled with " << bl.tx_hashes.size() << " txes, weight "
|
||||
@@ -1336,6 +1348,7 @@ namespace cryptonote
|
||||
// continue
|
||||
}
|
||||
}
|
||||
lock.commit();
|
||||
}
|
||||
if (n_removed > 0)
|
||||
++m_cookie;
|
||||
@@ -1395,6 +1408,7 @@ namespace cryptonote
|
||||
// ignore error
|
||||
}
|
||||
}
|
||||
lock.commit();
|
||||
}
|
||||
|
||||
m_cookie = 0;
|
||||
|
||||
@@ -362,7 +362,7 @@ namespace cryptonote
|
||||
int64_t diff = static_cast<int64_t>(hshd.current_height) - static_cast<int64_t>(m_core.get_current_blockchain_height());
|
||||
uint64_t abs_diff = std::abs(diff);
|
||||
uint64_t max_block_height = std::max(hshd.current_height,m_core.get_current_blockchain_height());
|
||||
uint64_t last_block_v1 = m_core.get_nettype() == TESTNET ? 624633 : m_core.get_nettype() == MAINNET ? 1009826 : (uint64_t)-1;
|
||||
uint64_t last_block_v1 = m_core.get_nettype() == TESTNET ? 0 : m_core.get_nettype() == MAINNET ? 0 : (uint64_t)-1;
|
||||
uint64_t diff_v2 = max_block_height > last_block_v1 ? std::min(abs_diff, max_block_height - last_block_v1) : 0;
|
||||
MCLOG(is_inital ? el::Level::Info : el::Level::Debug, "global", context << "Sync data returned a new top block candidate: " << m_core.get_current_blockchain_height() << " -> " << hshd.current_height
|
||||
<< " [Your node is " << abs_diff << " blocks (" << ((abs_diff - diff_v2) / (24 * 60 * 60 / DIFFICULTY_TARGET_V1)) + (diff_v2 / (24 * 60 * 60 / DIFFICULTY_TARGET_V2)) << " days) "
|
||||
@@ -2037,9 +2037,11 @@ skip:
|
||||
if(m_synchronized.compare_exchange_strong(val_expected, true))
|
||||
{
|
||||
MGINFO_YELLOW(ENDL << "**********************************************************************" << ENDL
|
||||
<< "You are now synchronized with the network. You may now start monero-wallet-cli." << ENDL
|
||||
<< "You are now synchronized with the network. You may now start wownero-wallet-cli." << ENDL
|
||||
<< ENDL
|
||||
<< "Use the \"help\" command to see the list of available commands." << ENDL
|
||||
<< "Use the \"help\" command to see a simplified list of available commands." << ENDL
|
||||
<< "Use the \"help_advanced\" command to see an advanced list of available commands." << ENDL
|
||||
<< "Use \"help_advanced <command>\" to see a command's documentation." << ENDL
|
||||
<< "**********************************************************************");
|
||||
m_sync_timer.pause();
|
||||
if (ELPP->vRegistry()->allowed(el::Level::Info, "sync-info"))
|
||||
|
||||
@@ -94,5 +94,5 @@ target_link_libraries(daemon
|
||||
${Blocks})
|
||||
set_property(TARGET daemon
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monerod")
|
||||
OUTPUT_NAME "wownerod")
|
||||
install(TARGETS daemon DESTINATION bin)
|
||||
|
||||
@@ -40,10 +40,11 @@ t_command_parser_executor::t_command_parser_executor(
|
||||
uint32_t ip
|
||||
, uint16_t port
|
||||
, const boost::optional<tools::login>& login
|
||||
, const epee::net_utils::ssl_options_t& ssl_options
|
||||
, bool is_rpc
|
||||
, cryptonote::core_rpc_server* rpc_server
|
||||
)
|
||||
: m_executor(ip, port, login, is_rpc, rpc_server)
|
||||
: m_executor(ip, port, login, ssl_options, is_rpc, rpc_server)
|
||||
{}
|
||||
|
||||
bool t_command_parser_executor::print_peer_list(const std::vector<std::string>& args)
|
||||
@@ -757,7 +758,7 @@ bool t_command_parser_executor::pop_blocks(const std::vector<std::string>& args)
|
||||
|
||||
bool t_command_parser_executor::version(const std::vector<std::string>& args)
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << std::endl;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << std::endl;
|
||||
return true;
|
||||
}
|
||||
|
||||
@@ -767,10 +768,10 @@ bool t_command_parser_executor::prune_blockchain(const std::vector<std::string>&
|
||||
|
||||
if (args.empty() || args[0] != "confirm")
|
||||
{
|
||||
std::cout << "Warning: pruning from within monerod will not shrink the database file size." << std::endl;
|
||||
std::cout << "Warning: pruning from within wownerod will not shrink the database file size." << std::endl;
|
||||
std::cout << "Instead, parts of the file will be marked as free, so the file will not grow" << std::endl;
|
||||
std::cout << "until that newly free space is used up. If you want a smaller file size now," << std::endl;
|
||||
std::cout << "exit monerod and run monero-blockchain-prune (you will temporarily need more" << std::endl;
|
||||
std::cout << "exit wownerod and run wownero-blockchain-prune (you will temporarily need more" << std::endl;
|
||||
std::cout << "disk space for the database conversion though). If you are OK with the database" << std::endl;
|
||||
std::cout << "file keeping the same size, re-run this command with the \"confirm\" parameter." << std::endl;
|
||||
return true;
|
||||
|
||||
@@ -40,6 +40,7 @@
|
||||
|
||||
#include "daemon/rpc_command_executor.h"
|
||||
#include "common/common_fwd.h"
|
||||
#include "net/net_fwd.h"
|
||||
#include "rpc/core_rpc_server.h"
|
||||
|
||||
namespace daemonize {
|
||||
@@ -53,6 +54,7 @@ public:
|
||||
uint32_t ip
|
||||
, uint16_t port
|
||||
, const boost::optional<tools::login>& login
|
||||
, const epee::net_utils::ssl_options_t& ssl_options
|
||||
, bool is_rpc
|
||||
, cryptonote::core_rpc_server* rpc_server = NULL
|
||||
);
|
||||
|
||||
@@ -43,10 +43,11 @@ t_command_server::t_command_server(
|
||||
uint32_t ip
|
||||
, uint16_t port
|
||||
, const boost::optional<tools::login>& login
|
||||
, const epee::net_utils::ssl_options_t& ssl_options
|
||||
, bool is_rpc
|
||||
, cryptonote::core_rpc_server* rpc_server
|
||||
)
|
||||
: m_parser(ip, port, login, is_rpc, rpc_server)
|
||||
: m_parser(ip, port, login, ssl_options, is_rpc, rpc_server)
|
||||
, m_command_lookup()
|
||||
, m_is_rpc(is_rpc)
|
||||
{
|
||||
@@ -362,7 +363,7 @@ bool t_command_server::help(const std::vector<std::string>& args)
|
||||
std::string t_command_server::get_commands_str()
|
||||
{
|
||||
std::stringstream ss;
|
||||
ss << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << std::endl;
|
||||
ss << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << std::endl;
|
||||
ss << "Commands: " << std::endl;
|
||||
std::string usage = m_command_lookup.get_usage();
|
||||
boost::replace_all(usage, "\n", "\n ");
|
||||
|
||||
@@ -43,6 +43,7 @@ Passing RPC commands:
|
||||
#include "common/common_fwd.h"
|
||||
#include "console_handler.h"
|
||||
#include "daemon/command_parser_executor.h"
|
||||
#include "net/net_fwd.h"
|
||||
|
||||
namespace daemonize {
|
||||
|
||||
@@ -57,6 +58,7 @@ public:
|
||||
uint32_t ip
|
||||
, uint16_t port
|
||||
, const boost::optional<tools::login>& login
|
||||
, const epee::net_utils::ssl_options_t& ssl_options
|
||||
, bool is_rpc = true
|
||||
, cryptonote::core_rpc_server* rpc_server = NULL
|
||||
);
|
||||
|
||||
@@ -45,6 +45,7 @@
|
||||
#include "daemon/command_server.h"
|
||||
#include "daemon/command_server.h"
|
||||
#include "daemon/command_line_args.h"
|
||||
#include "net/net_ssl.h"
|
||||
#include "version.h"
|
||||
|
||||
using namespace epee;
|
||||
@@ -163,7 +164,7 @@ bool t_daemon::run(bool interactive)
|
||||
if (interactive && mp_internals->rpcs.size())
|
||||
{
|
||||
// The first three variables are not used when the fourth is false
|
||||
rpc_commands.reset(new daemonize::t_command_server(0, 0, boost::none, false, mp_internals->rpcs.front()->get_server()));
|
||||
rpc_commands.reset(new daemonize::t_command_server(0, 0, boost::none, epee::net_utils::ssl_support_t::e_ssl_support_disabled, false, mp_internals->rpcs.front()->get_server()));
|
||||
rpc_commands->start_handling(std::bind(&daemonize::t_daemon::stop_p2p, this));
|
||||
}
|
||||
|
||||
|
||||
@@ -40,7 +40,7 @@
|
||||
|
||||
namespace daemonize
|
||||
{
|
||||
std::string const t_executor::NAME = "Monero Daemon";
|
||||
std::string const t_executor::NAME = "Wownero Daemon";
|
||||
|
||||
void t_executor::init_options(
|
||||
boost::program_options::options_description & configurable_options
|
||||
@@ -58,7 +58,7 @@ namespace daemonize
|
||||
boost::program_options::variables_map const & vm
|
||||
)
|
||||
{
|
||||
LOG_PRINT_L0("Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ") Daemonised");
|
||||
LOG_PRINT_L0("Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ") Daemonised");
|
||||
return t_daemon{vm, public_rpc_port};
|
||||
}
|
||||
|
||||
|
||||
@@ -172,7 +172,7 @@ int main(int argc, char const * argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Usage: " + std::string{argv[0]} + " [options|settings] [daemon_command...]" << std::endl << std::endl;
|
||||
std::cout << visible_options << std::endl;
|
||||
return 0;
|
||||
@@ -181,7 +181,7 @@ int main(int argc, char const * argv[])
|
||||
// Monero Version
|
||||
if (command_line::get_arg(vm, command_line::arg_version))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL;
|
||||
return 0;
|
||||
}
|
||||
|
||||
@@ -278,7 +278,7 @@ int main(int argc, char const * argv[])
|
||||
tools::set_max_concurrency(command_line::get_arg(vm, daemon_args::arg_max_concurrency));
|
||||
|
||||
// logging is now set up
|
||||
MGINFO("Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")");
|
||||
MGINFO("Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")");
|
||||
|
||||
// If there are positional options, we're running a daemon command
|
||||
{
|
||||
@@ -324,7 +324,11 @@ int main(int argc, char const * argv[])
|
||||
}
|
||||
}
|
||||
|
||||
daemonize::t_command_server rpc_commands{rpc_ip, rpc_port, std::move(login)};
|
||||
auto ssl_options = cryptonote::rpc_args::process_ssl(vm, true);
|
||||
if (!ssl_options)
|
||||
return 1;
|
||||
|
||||
daemonize::t_command_server rpc_commands{rpc_ip, rpc_port, std::move(login), std::move(*ssl_options)};
|
||||
if (rpc_commands.process_command_vec(command))
|
||||
{
|
||||
return 0;
|
||||
|
||||
@@ -127,6 +127,7 @@ t_rpc_command_executor::t_rpc_command_executor(
|
||||
uint32_t ip
|
||||
, uint16_t port
|
||||
, const boost::optional<tools::login>& login
|
||||
, const epee::net_utils::ssl_options_t& ssl_options
|
||||
, bool is_rpc
|
||||
, cryptonote::core_rpc_server* rpc_server
|
||||
)
|
||||
@@ -137,7 +138,7 @@ t_rpc_command_executor::t_rpc_command_executor(
|
||||
boost::optional<epee::net_utils::http::login> http_login{};
|
||||
if (login)
|
||||
http_login.emplace(login->username, login->password.password());
|
||||
m_rpc_client = new tools::t_rpc_client(ip, port, std::move(http_login));
|
||||
m_rpc_client = new tools::t_rpc_client(ip, port, std::move(http_login), ssl_options);
|
||||
}
|
||||
else
|
||||
{
|
||||
@@ -337,6 +338,7 @@ bool t_rpc_command_executor::show_difficulty() {
|
||||
tools::success_msg_writer() << "BH: " << res.height
|
||||
<< ", TH: " << res.top_block_hash
|
||||
<< ", DIFF: " << res.difficulty
|
||||
<< ", CUM_DIFF: " << res.cumulative_difficulty
|
||||
<< ", HR: " << res.difficulty / res.target << " H/s";
|
||||
|
||||
return true;
|
||||
@@ -1343,10 +1345,10 @@ bool t_rpc_command_executor::print_status()
|
||||
bool daemon_is_alive = m_rpc_client->check_connection();
|
||||
|
||||
if(daemon_is_alive) {
|
||||
tools::success_msg_writer() << "monerod is running";
|
||||
tools::success_msg_writer() << "wownerod is running";
|
||||
}
|
||||
else {
|
||||
tools::fail_msg_writer() << "monerod is NOT running";
|
||||
tools::fail_msg_writer() << "wownerod is NOT running";
|
||||
}
|
||||
|
||||
return true;
|
||||
|
||||
@@ -43,6 +43,7 @@
|
||||
#include "common/common_fwd.h"
|
||||
#include "common/rpc_client.h"
|
||||
#include "cryptonote_basic/cryptonote_basic.h"
|
||||
#include "net/net_fwd.h"
|
||||
#include "rpc/core_rpc_server.h"
|
||||
|
||||
#undef MONERO_DEFAULT_LOG_CATEGORY
|
||||
@@ -61,6 +62,7 @@ public:
|
||||
uint32_t ip
|
||||
, uint16_t port
|
||||
, const boost::optional<tools::login>& user
|
||||
, const epee::net_utils::ssl_options_t& ssl_options
|
||||
, bool is_rpc = true
|
||||
, cryptonote::core_rpc_server* rpc_server = NULL
|
||||
);
|
||||
|
||||
@@ -46,7 +46,7 @@ target_link_libraries(cn_deserialize
|
||||
|
||||
set_property(TARGET cn_deserialize
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-utils-deserialize")
|
||||
OUTPUT_NAME "wownero-utils-deserialize")
|
||||
|
||||
|
||||
set(object_sizes_sources
|
||||
@@ -67,5 +67,5 @@ target_link_libraries(object_sizes
|
||||
|
||||
set_property(TARGET object_sizes
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-utils-object-sizes")
|
||||
OUTPUT_NAME "wownero-utils-object-sizes")
|
||||
|
||||
|
||||
@@ -103,7 +103,7 @@ int main(int argc, char* argv[])
|
||||
|
||||
if (command_line::get_arg(vm, command_line::arg_help))
|
||||
{
|
||||
std::cout << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")" << ENDL << ENDL;
|
||||
std::cout << desc_options << std::endl;
|
||||
return 1;
|
||||
}
|
||||
|
||||
@@ -90,6 +90,20 @@ namespace hw {
|
||||
AKout = keys.AKout;
|
||||
}
|
||||
|
||||
ABPkeys &ABPkeys::operator=(const ABPkeys& keys) {
|
||||
if (&keys == this)
|
||||
return *this;
|
||||
Aout = keys.Aout;
|
||||
Bout = keys.Bout;
|
||||
is_subaddress = keys.is_subaddress;
|
||||
is_change_address = keys.is_change_address;
|
||||
additional_key = keys.additional_key;
|
||||
index = keys.index;
|
||||
Pout = keys.Pout;
|
||||
AKout = keys.AKout;
|
||||
return *this;
|
||||
}
|
||||
|
||||
bool Keymap::find(const rct::key& P, ABPkeys& keys) const {
|
||||
size_t sz = ABP.size();
|
||||
for (size_t i=0; i<sz; i++) {
|
||||
|
||||
@@ -77,6 +77,7 @@ namespace hw {
|
||||
ABPkeys(const rct::key& A, const rct::key& B, const bool is_subaddr, bool is_subaddress, bool is_change_address, size_t index, const rct::key& P,const rct::key& AK);
|
||||
ABPkeys(const ABPkeys& keys) ;
|
||||
ABPkeys() {index=0;is_subaddress=false;is_subaddress=false;is_change_address=false;}
|
||||
ABPkeys &operator=(const ABPkeys &keys);
|
||||
};
|
||||
|
||||
class Keymap {
|
||||
|
||||
@@ -50,5 +50,5 @@ add_dependencies(gen_multisig
|
||||
version)
|
||||
set_property(TARGET gen_multisig
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-gen-trusted-multisig")
|
||||
OUTPUT_NAME "wownero-gen-trusted-multisig")
|
||||
install(TARGETS gen_multisig DESTINATION bin)
|
||||
|
||||
@@ -256,10 +256,7 @@ namespace nodetool
|
||||
|
||||
private:
|
||||
const std::vector<std::string> m_seed_nodes_list =
|
||||
{ "seeds.moneroseeds.se"
|
||||
, "seeds.moneroseeds.ae.org"
|
||||
, "seeds.moneroseeds.ch"
|
||||
, "seeds.moneroseeds.li"
|
||||
{
|
||||
};
|
||||
|
||||
bool islimitup=false;
|
||||
|
||||
@@ -60,9 +60,16 @@
|
||||
#include "cryptonote_core/cryptonote_core.h"
|
||||
#include "net/parse.h"
|
||||
|
||||
#include <miniupnp/miniupnpc/miniupnpc.h>
|
||||
#include <miniupnp/miniupnpc/upnpcommands.h>
|
||||
#include <miniupnp/miniupnpc/upnperrors.h>
|
||||
// We have to look for miniupnpc headers in different places, dependent on if its compiled or external
|
||||
#ifdef UPNP_STATIC
|
||||
#include <miniupnp/miniupnpc/miniupnpc.h>
|
||||
#include <miniupnp/miniupnpc/upnpcommands.h>
|
||||
#include <miniupnp/miniupnpc/upnperrors.h>
|
||||
#else
|
||||
#include "miniupnpc.h"
|
||||
#include "upnpcommands.h"
|
||||
#include "upnperrors.h"
|
||||
#endif
|
||||
|
||||
#undef MONERO_DEFAULT_LOG_CATEGORY
|
||||
#define MONERO_DEFAULT_LOG_CATEGORY "net.p2p"
|
||||
@@ -448,30 +455,21 @@ namespace nodetool
|
||||
std::set<std::string> full_addrs;
|
||||
if (nettype == cryptonote::TESTNET)
|
||||
{
|
||||
full_addrs.insert("212.83.175.67:28080");
|
||||
full_addrs.insert("5.9.100.248:28080");
|
||||
full_addrs.insert("163.172.182.165:28080");
|
||||
full_addrs.insert("195.154.123.123:28080");
|
||||
full_addrs.insert("212.83.172.165:28080");
|
||||
full_addrs.insert("206.189.166.14:11180");
|
||||
full_addrs.insert("104.236.48.55:11180");
|
||||
}
|
||||
else if (nettype == cryptonote::STAGENET)
|
||||
{
|
||||
full_addrs.insert("162.210.173.150:38080");
|
||||
full_addrs.insert("162.210.173.151:38080");
|
||||
}
|
||||
else if (nettype == cryptonote::FAKECHAIN)
|
||||
{
|
||||
}
|
||||
else
|
||||
{
|
||||
full_addrs.insert("107.152.130.98:18080");
|
||||
full_addrs.insert("212.83.175.67:18080");
|
||||
full_addrs.insert("5.9.100.248:18080");
|
||||
full_addrs.insert("163.172.182.165:18080");
|
||||
full_addrs.insert("161.67.132.39:18080");
|
||||
full_addrs.insert("198.74.231.92:18080");
|
||||
full_addrs.insert("195.154.123.123:18080");
|
||||
full_addrs.insert("212.83.172.165:18080");
|
||||
full_addrs.insert("66.70.218.230:34567");
|
||||
full_addrs.insert("34.209.48.213:34567");
|
||||
full_addrs.insert("159.65.91.59:34567");
|
||||
full_addrs.insert("138.197.31.246:34567");
|
||||
}
|
||||
return full_addrs;
|
||||
}
|
||||
|
||||
@@ -134,10 +134,11 @@ namespace boost
|
||||
a & port;
|
||||
a & length;
|
||||
|
||||
if (length > net::tor_address::buffer_size())
|
||||
const size_t buffer_size = net::tor_address::buffer_size();
|
||||
if (length > buffer_size)
|
||||
MONERO_THROW(net::error::invalid_tor_address, "Tor address too long");
|
||||
|
||||
char host[net::tor_address::buffer_size()] = {0};
|
||||
char host[buffer_size] = {0};
|
||||
a.load_binary(host, length);
|
||||
host[sizeof(host) - 1] = 0;
|
||||
|
||||
@@ -155,10 +156,11 @@ namespace boost
|
||||
a & port;
|
||||
a & length;
|
||||
|
||||
if (length > net::i2p_address::buffer_size())
|
||||
const size_t buffer_size = net::i2p_address::buffer_size();
|
||||
if (length > buffer_size)
|
||||
MONERO_THROW(net::error::invalid_i2p_address, "i2p address too long");
|
||||
|
||||
char host[net::i2p_address::buffer_size()] = {0};
|
||||
char host[buffer_size] = {0};
|
||||
a.load_binary(host, length);
|
||||
host[sizeof(host) - 1] = 0;
|
||||
|
||||
|
||||
@@ -31,7 +31,8 @@ set(ringct_basic_sources
|
||||
rctTypes.cpp
|
||||
rctCryptoOps.c
|
||||
multiexp.cc
|
||||
bulletproofs.cc)
|
||||
bulletproofs.cc
|
||||
bulletproofs2.cc)
|
||||
|
||||
set(ringct_basic_private_headers
|
||||
rctOps.h
|
||||
|
||||
@@ -42,9 +42,16 @@ Bulletproof bulletproof_PROVE(const rct::key &v, const rct::key &gamma);
|
||||
Bulletproof bulletproof_PROVE(uint64_t v, const rct::key &gamma);
|
||||
Bulletproof bulletproof_PROVE(const rct::keyV &v, const rct::keyV &gamma);
|
||||
Bulletproof bulletproof_PROVE(const std::vector<uint64_t> &v, const rct::keyV &gamma);
|
||||
Bulletproof bulletproof_PROVE_old(const rct::key &v, const rct::key &gamma);
|
||||
Bulletproof bulletproof_PROVE_old(uint64_t v, const rct::key &gamma);
|
||||
Bulletproof bulletproof_PROVE_old(const rct::keyV &v, const rct::keyV &gamma);
|
||||
Bulletproof bulletproof_PROVE_old(const std::vector<uint64_t> &v, const rct::keyV &gamma);
|
||||
bool bulletproof_VERIFY(const Bulletproof &proof);
|
||||
bool bulletproof_VERIFY(const std::vector<const Bulletproof*> &proofs);
|
||||
bool bulletproof_VERIFY(const std::vector<Bulletproof> &proofs);
|
||||
bool bulletproof_VERIFY_old(const Bulletproof &proof);
|
||||
bool bulletproof_VERIFY_old(const std::vector<const Bulletproof*> &proofs);
|
||||
bool bulletproof_VERIFY_old(const std::vector<Bulletproof> &proofs);
|
||||
|
||||
}
|
||||
|
||||
|
||||
1160
src/ringct/bulletproofs2.cc
Normal file
1160
src/ringct/bulletproofs2.cc
Normal file
File diff suppressed because it is too large
Load Diff
@@ -91,6 +91,23 @@ namespace rct {
|
||||
return proof;
|
||||
}
|
||||
|
||||
Bulletproof proveRangeBulletproof_old(key &C, key &mask, uint64_t amount)
|
||||
{
|
||||
mask = rct::skGen();
|
||||
Bulletproof proof = bulletproof_PROVE_old(amount, mask);
|
||||
CHECK_AND_ASSERT_THROW_MES(proof.V.size() == 1, "V has not exactly one element");
|
||||
C = proof.V[0];
|
||||
return proof;
|
||||
}
|
||||
|
||||
Bulletproof proveRangeBulletproof_old(keyV &C, keyV &masks, const std::vector<uint64_t> &amounts)
|
||||
{
|
||||
masks = rct::skvGen(amounts.size());
|
||||
Bulletproof proof = bulletproof_PROVE_old(amounts, masks);
|
||||
CHECK_AND_ASSERT_THROW_MES(proof.V.size() == amounts.size(), "V does not have the expected size");
|
||||
C = proof.V;
|
||||
return proof;
|
||||
}
|
||||
bool verBulletproof(const Bulletproof &proof)
|
||||
{
|
||||
try { return bulletproof_VERIFY(proof); }
|
||||
@@ -105,6 +122,19 @@ namespace rct {
|
||||
catch (...) { return false; }
|
||||
}
|
||||
|
||||
bool verBulletproof_old(const Bulletproof &proof)
|
||||
{
|
||||
try { return bulletproof_VERIFY_old(proof); }
|
||||
// we can get deep throws from ge_frombytes_vartime if input isn't valid
|
||||
catch (...) { return false; }
|
||||
}
|
||||
|
||||
bool verBulletproof_old(const std::vector<const Bulletproof*> &proofs)
|
||||
{
|
||||
try { return bulletproof_VERIFY_old(proofs); }
|
||||
// we can get deep throws from ge_frombytes_vartime if input isn't valid
|
||||
catch (...) { return false; }
|
||||
}
|
||||
//Borromean (c.f. gmax/andytoshi's paper)
|
||||
boroSig genBorromean(const key64 x, const key64 P1, const key64 P2, const bits indices) {
|
||||
key64 L[2], alpha;
|
||||
@@ -419,7 +449,7 @@ namespace rct {
|
||||
hashes.push_back(hash2rct(h));
|
||||
|
||||
keyV kv;
|
||||
if (rv.type == RCTTypeBulletproof || rv.type == RCTTypeBulletproof2)
|
||||
if (rv.type == RCTTypeBulletproof || rv.type == RCTTypeBulletproof2 || rv.type == RCTTypeSimpleBulletproof || rv.type == RCTTypeFullBulletproof)
|
||||
{
|
||||
kv.reserve((6*2+9) * rv.p.bulletproofs.size());
|
||||
for (const auto &p: rv.p.bulletproofs)
|
||||
@@ -688,6 +718,7 @@ namespace rct {
|
||||
// Note: For txn fees, the last index in the amounts vector should contain that
|
||||
// Thus the amounts vector will be "one" longer than the destinations vectort
|
||||
rctSig genRct(const key &message, const ctkeyV & inSk, const keyV & destinations, const vector<xmr_amount> & amounts, const ctkeyM &mixRing, const keyV &amount_keys, const multisig_kLRki *kLRki, multisig_out *msout, unsigned int index, ctkeyV &outSk, const RCTConfig &rct_config, hw::device &hwdev) {
|
||||
const bool bulletproof = rct_config.range_proof_type != RangeProofBorromean;
|
||||
CHECK_AND_ASSERT_THROW_MES(amounts.size() == destinations.size() || amounts.size() == destinations.size() + 1, "Different number of amounts/destinations");
|
||||
CHECK_AND_ASSERT_THROW_MES(amount_keys.size() == destinations.size(), "Different number of amount_keys/destinations");
|
||||
CHECK_AND_ASSERT_THROW_MES(index < mixRing.size(), "Bad index into mixRing");
|
||||
@@ -698,10 +729,11 @@ namespace rct {
|
||||
CHECK_AND_ASSERT_THROW_MES(inSk.size() < 2, "genRct is not suitable for 2+ rings");
|
||||
|
||||
rctSig rv;
|
||||
rv.type = RCTTypeFull;
|
||||
rv.type = bulletproof ? RCTTypeFullBulletproof : RCTTypeFull;
|
||||
rv.message = message;
|
||||
rv.outPk.resize(destinations.size());
|
||||
rv.p.rangeSigs.resize(destinations.size());
|
||||
if (!bulletproof)
|
||||
rv.p.rangeSigs.resize(destinations.size());
|
||||
rv.ecdhInfo.resize(destinations.size());
|
||||
|
||||
size_t i = 0;
|
||||
@@ -711,10 +743,45 @@ namespace rct {
|
||||
//add destination to sig
|
||||
rv.outPk[i].dest = copy(destinations[i]);
|
||||
//compute range proof
|
||||
rv.p.rangeSigs[i] = proveRange(rv.outPk[i].mask, outSk[i].mask, amounts[i]);
|
||||
if (!bulletproof)
|
||||
{
|
||||
rv.p.rangeSigs[i] = proveRange(rv.outPk[i].mask, outSk[i].mask, amounts[i]);
|
||||
|
||||
#ifdef DBG
|
||||
CHECK_AND_ASSERT_THROW_MES(verRange(rv.outPk[i].mask, rv.p.rangeSigs[i]), "verRange failed on newly created proof");
|
||||
#endif
|
||||
}
|
||||
}
|
||||
rv.p.bulletproofs.clear();
|
||||
if (bulletproof)
|
||||
{
|
||||
std::vector<uint64_t> proof_amounts;
|
||||
size_t amounts_proved = 0;
|
||||
while (amounts_proved < amounts.size())
|
||||
{
|
||||
size_t batch_size = 1;
|
||||
if (rct_config.range_proof_type == RangeProofMultiOutputBulletproof)
|
||||
while (batch_size * 2 + amounts_proved <= amounts.size())
|
||||
batch_size *= 2;
|
||||
rct::keyV C, masks;
|
||||
std::vector<uint64_t> batch_amounts(batch_size);
|
||||
for (i = 0; i < batch_size; ++i)
|
||||
batch_amounts[i] = amounts[i + amounts_proved];
|
||||
rv.p.bulletproofs.push_back(proveRangeBulletproof_old(C, masks, batch_amounts));
|
||||
#ifdef DBG
|
||||
CHECK_AND_ASSERT_THROW_MES(verBulletproof_old(rv.p.bulletproofs.back()), "verBulletproof failed on newly created proof");
|
||||
#endif
|
||||
for (i = 0; i < batch_size; ++i)
|
||||
{
|
||||
rv.outPk[i + amounts_proved].mask = C[i];
|
||||
outSk[i + amounts_proved].mask = masks[i];
|
||||
}
|
||||
amounts_proved += batch_size;
|
||||
}
|
||||
}
|
||||
|
||||
for (i = 0; i < outSk.size(); ++i)
|
||||
{
|
||||
//mask amount and mask
|
||||
rv.ecdhInfo[i].mask = copy(outSk[i].mask);
|
||||
rv.ecdhInfo[i].amount = d2h(amounts[i]);
|
||||
@@ -899,6 +966,103 @@ namespace rct {
|
||||
}
|
||||
return genRctSimple(message, inSk, destinations, inamounts, outamounts, txnFee, mixRing, amount_keys, kLRki, msout, index, outSk, rct_config, hwdev);
|
||||
}
|
||||
//RCT simple
|
||||
//for post-rct only
|
||||
rctSig genRctSimple_old(const key &message, const ctkeyV & inSk, const keyV & destinations, const vector<xmr_amount> &inamounts, const vector<xmr_amount> &outamounts, xmr_amount txnFee, const ctkeyM & mixRing, const keyV &amount_keys, const std::vector<multisig_kLRki> *kLRki, multisig_out *msout, const std::vector<unsigned int> & index, ctkeyV &outSk, const RCTConfig &rct_config, hw::device &hwdev) {
|
||||
const bool bulletproof = rct_config.range_proof_type != RangeProofBorromean;
|
||||
CHECK_AND_ASSERT_THROW_MES(inamounts.size() > 0, "Empty inamounts");
|
||||
CHECK_AND_ASSERT_THROW_MES(inamounts.size() == inSk.size(), "Different number of inamounts/inSk");
|
||||
CHECK_AND_ASSERT_THROW_MES(outamounts.size() == destinations.size(), "Different number of amounts/destinations");
|
||||
CHECK_AND_ASSERT_THROW_MES(amount_keys.size() == destinations.size(), "Different number of amount_keys/destinations");
|
||||
CHECK_AND_ASSERT_THROW_MES(index.size() == inSk.size(), "Different number of index/inSk");
|
||||
CHECK_AND_ASSERT_THROW_MES(mixRing.size() == inSk.size(), "Different number of mixRing/inSk");
|
||||
for (size_t n = 0; n < mixRing.size(); ++n) {
|
||||
CHECK_AND_ASSERT_THROW_MES(index[n] < mixRing[n].size(), "Bad index into mixRing");
|
||||
}
|
||||
CHECK_AND_ASSERT_THROW_MES((kLRki && msout) || (!kLRki && !msout), "Only one of kLRki/msout is present");
|
||||
if (kLRki && msout) {
|
||||
CHECK_AND_ASSERT_THROW_MES(kLRki->size() == inamounts.size(), "Mismatched kLRki/inamounts sizes");
|
||||
}
|
||||
|
||||
rctSig rv;
|
||||
rv.type = bulletproof ? RCTTypeSimpleBulletproof : RCTTypeSimple;
|
||||
rv.message = message;
|
||||
rv.outPk.resize(destinations.size());
|
||||
if (bulletproof)
|
||||
rv.p.bulletproofs.resize(destinations.size());
|
||||
else
|
||||
rv.p.rangeSigs.resize(destinations.size());
|
||||
rv.ecdhInfo.resize(destinations.size());
|
||||
|
||||
size_t i;
|
||||
keyV masks(destinations.size()); //sk mask..
|
||||
outSk.resize(destinations.size());
|
||||
key sumout = zero();
|
||||
for (i = 0; i < destinations.size(); i++) {
|
||||
|
||||
//add destination to sig
|
||||
rv.outPk[i].dest = copy(destinations[i]);
|
||||
//compute range proof
|
||||
if (bulletproof)
|
||||
rv.p.bulletproofs[i] = proveRangeBulletproof_old(rv.outPk[i].mask, outSk[i].mask, outamounts[i]);
|
||||
else
|
||||
rv.p.rangeSigs[i] = proveRange(rv.outPk[i].mask, outSk[i].mask, outamounts[i]);
|
||||
#ifdef DBG
|
||||
if (bulletproof)
|
||||
CHECK_AND_ASSERT_THROW_MES(verBulletproof_old(rv.p.bulletproofs[i]), "verBulletproof failed on newly created proof");
|
||||
else
|
||||
CHECK_AND_ASSERT_THROW_MES(verRange(rv.outPk[i].mask, rv.p.rangeSigs[i]), "verRange failed on newly created proof");
|
||||
#endif
|
||||
|
||||
sc_add(sumout.bytes, outSk[i].mask.bytes, sumout.bytes);
|
||||
|
||||
//mask amount and mask
|
||||
rv.ecdhInfo[i].mask = copy(outSk[i].mask);
|
||||
rv.ecdhInfo[i].amount = d2h(outamounts[i]);
|
||||
hwdev.ecdhEncode(rv.ecdhInfo[i], amount_keys[i], rv.type == RCTTypeSimpleBulletproof);
|
||||
}
|
||||
|
||||
//set txn fee
|
||||
rv.txnFee = txnFee;
|
||||
// TODO: unused ??
|
||||
// key txnFeeKey = scalarmultH(d2h(rv.txnFee));
|
||||
rv.mixRing = mixRing;
|
||||
keyV &pseudoOuts = bulletproof ? rv.p.pseudoOuts : rv.pseudoOuts;
|
||||
pseudoOuts.resize(inamounts.size());
|
||||
rv.p.MGs.resize(inamounts.size());
|
||||
key sumpouts = zero(); //sum pseudoOut masks
|
||||
keyV a(inamounts.size());
|
||||
for (i = 0 ; i < inamounts.size() - 1; i++) {
|
||||
skGen(a[i]);
|
||||
sc_add(sumpouts.bytes, a[i].bytes, sumpouts.bytes);
|
||||
genC(pseudoOuts[i], a[i], inamounts[i]);
|
||||
}
|
||||
rv.mixRing = mixRing;
|
||||
sc_sub(a[i].bytes, sumout.bytes, sumpouts.bytes);
|
||||
genC(pseudoOuts[i], a[i], inamounts[i]);
|
||||
DP(pseudoOuts[i]);
|
||||
|
||||
key full_message = get_pre_mlsag_hash(rv,hwdev);
|
||||
if (msout)
|
||||
msout->c.resize(inamounts.size());
|
||||
for (i = 0 ; i < inamounts.size(); i++) {
|
||||
rv.p.MGs[i] = proveRctMGSimple(full_message, rv.mixRing[i], inSk[i], a[i], pseudoOuts[i], kLRki ? &(*kLRki)[i]: NULL, msout ? &msout->c[i] : NULL, index[i], hwdev);
|
||||
}
|
||||
return rv;
|
||||
}
|
||||
|
||||
rctSig genRctSimple_old(const key &message, const ctkeyV & inSk, const ctkeyV & inPk, const keyV & destinations, const vector<xmr_amount> &inamounts, const vector<xmr_amount> &outamounts, const keyV &amount_keys, const std::vector<multisig_kLRki> *kLRki, multisig_out *msout, xmr_amount txnFee, unsigned int mixin, const RCTConfig &rct_config, hw::device &hwdev) {
|
||||
std::vector<unsigned int> index;
|
||||
index.resize(inPk.size());
|
||||
ctkeyM mixRing;
|
||||
ctkeyV outSk;
|
||||
mixRing.resize(inPk.size());
|
||||
for (size_t i = 0; i < inPk.size(); ++i) {
|
||||
mixRing[i].resize(mixin+1);
|
||||
index[i] = populateFromBlockchainSimple(mixRing[i], inPk[i], mixin);
|
||||
}
|
||||
return genRctSimple_old(message, inSk, destinations, inamounts, outamounts, txnFee, mixRing, amount_keys, kLRki, msout, index, outSk, rct_config, hwdev);
|
||||
}
|
||||
|
||||
//RingCT protocol
|
||||
//genRct:
|
||||
@@ -912,10 +1076,13 @@ namespace rct {
|
||||
// must know the destination private key to find the correct amount, else will return a random number
|
||||
bool verRct(const rctSig & rv, bool semantics) {
|
||||
PERF_TIMER(verRct);
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeFull, false, "verRct called on non-full rctSig");
|
||||
const bool bulletproof = is_rct_bulletproof(rv.type);
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeFull || rv.type == RCTTypeFullBulletproof, false, "verRct called on non-full rctSig");
|
||||
if (semantics)
|
||||
{
|
||||
if (rv.type == RCTTypeBulletproof)
|
||||
CHECK_AND_ASSERT_MES(rv.outPk.size() == rv.p.rangeSigs.size(), false, "Mismatched sizes of outPk and rv.p.rangeSigs");
|
||||
else
|
||||
CHECK_AND_ASSERT_MES(rv.outPk.size() == rv.ecdhInfo.size(), false, "Mismatched sizes of outPk and rv.ecdhInfo");
|
||||
CHECK_AND_ASSERT_MES(rv.p.MGs.size() == 1, false, "full rctSig has not one MG");
|
||||
}
|
||||
@@ -930,10 +1097,23 @@ namespace rct {
|
||||
if (semantics) {
|
||||
tools::threadpool& tpool = tools::threadpool::getInstance();
|
||||
tools::threadpool::waiter waiter;
|
||||
std::deque<bool> results(rv.outPk.size(), false);
|
||||
std::deque<bool> results(bulletproof ? rv.p.bulletproofs.size() : rv.outPk.size(), false);
|
||||
DP("range proofs verified?");
|
||||
for (size_t i = 0; i < rv.outPk.size(); i++)
|
||||
tpool.submit(&waiter, [&, i] { results[i] = verRange(rv.outPk[i].mask, rv.p.rangeSigs[i]); });
|
||||
if (rct::is_rct_new_bulletproof(rv.type))
|
||||
{
|
||||
for (size_t i = 0; i < rv.p.bulletproofs.size(); i++)
|
||||
tpool.submit(&waiter, [&, i] { results[i] = verBulletproof(rv.p.bulletproofs[i]); });
|
||||
}
|
||||
else if (bulletproof)
|
||||
{
|
||||
for (size_t i = 0; i < rv.p.bulletproofs.size(); i++)
|
||||
tpool.submit(&waiter, [&, i] { results[i] = verBulletproof_old(rv.p.bulletproofs[i]); });
|
||||
}
|
||||
else
|
||||
{
|
||||
for (size_t i = 0; i < rv.outPk.size(); i++)
|
||||
tpool.submit(&waiter, [&, i] { results[i] = verRange(rv.outPk[i].mask, rv.p.rangeSigs[i]); });
|
||||
}
|
||||
waiter.wait(&tpool);
|
||||
|
||||
for (size_t i = 0; i < results.size(); ++i) {
|
||||
@@ -987,12 +1167,15 @@ namespace rct {
|
||||
{
|
||||
CHECK_AND_ASSERT_MES(rvp, false, "rctSig pointer is NULL");
|
||||
const rctSig &rv = *rvp;
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeSimple || rv.type == RCTTypeBulletproof || rv.type == RCTTypeBulletproof2,
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeSimple || rv.type == RCTTypeBulletproof || rv.type == RCTTypeBulletproof2 || rv.type == RCTTypeSimpleBulletproof,
|
||||
false, "verRctSemanticsSimple called on non simple rctSig");
|
||||
const bool bulletproof = is_rct_bulletproof(rv.type);
|
||||
if (bulletproof)
|
||||
if (rv.type == RCTTypeBulletproof)
|
||||
{
|
||||
CHECK_AND_ASSERT_MES(rv.outPk.size() == n_bulletproof_amounts(rv.p.bulletproofs), false, "Mismatched sizes of outPk and bulletproofs");
|
||||
}
|
||||
else if (bulletproof)
|
||||
{
|
||||
CHECK_AND_ASSERT_MES(rv.p.pseudoOuts.size() == rv.p.MGs.size(), false, "Mismatched sizes of rv.p.pseudoOuts and rv.p.MGs");
|
||||
CHECK_AND_ASSERT_MES(rv.pseudoOuts.empty(), false, "rv.pseudoOuts is not empty");
|
||||
}
|
||||
@@ -1046,12 +1229,23 @@ namespace rct {
|
||||
offset += rv.p.rangeSigs.size();
|
||||
}
|
||||
}
|
||||
for (const rctSig *rvp: rvv)
|
||||
{
|
||||
const rctSig &rv = *rvp;
|
||||
if (!rct::is_rct_new_bulletproof(rv.type)){
|
||||
if (!proofs.empty() && !verBulletproof_old(proofs))
|
||||
{
|
||||
LOG_PRINT_L1("Aggregate range proof verified failed");
|
||||
return false;
|
||||
}
|
||||
} else {
|
||||
if (!proofs.empty() && !verBulletproof(proofs))
|
||||
{
|
||||
LOG_PRINT_L1("Aggregate range proof verified failed");
|
||||
return false;
|
||||
}
|
||||
|
||||
}
|
||||
}
|
||||
waiter.wait(&tpool);
|
||||
for (size_t i = 0; i < results.size(); ++i) {
|
||||
if (!results[i]) {
|
||||
@@ -1087,7 +1281,7 @@ namespace rct {
|
||||
{
|
||||
PERF_TIMER(verRctNonSemanticsSimple);
|
||||
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeSimple || rv.type == RCTTypeBulletproof || rv.type == RCTTypeBulletproof2,
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeSimple || rv.type == RCTTypeBulletproof || rv.type == RCTTypeBulletproof2 || rv.type == RCTTypeSimpleBulletproof,
|
||||
false, "verRctNonSemanticsSimple called on non simple rctSig");
|
||||
const bool bulletproof = is_rct_bulletproof(rv.type);
|
||||
// semantics check is early, and mixRing/MGs aren't resolved yet
|
||||
@@ -1148,7 +1342,7 @@ namespace rct {
|
||||
// uses the attached ecdh info to find the amounts represented by each output commitment
|
||||
// must know the destination private key to find the correct amount, else will return a random number
|
||||
xmr_amount decodeRct(const rctSig & rv, const key & sk, unsigned int i, key & mask, hw::device &hwdev) {
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeFull, false, "decodeRct called on non-full rctSig");
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeFull || rv.type == RCTTypeFullBulletproof, false, "decodeRct called on non-full rctSig");
|
||||
CHECK_AND_ASSERT_THROW_MES(i < rv.ecdhInfo.size(), "Bad index");
|
||||
CHECK_AND_ASSERT_THROW_MES(rv.outPk.size() == rv.ecdhInfo.size(), "Mismatched sizes of rv.outPk and rv.ecdhInfo");
|
||||
|
||||
@@ -1178,7 +1372,7 @@ namespace rct {
|
||||
}
|
||||
|
||||
xmr_amount decodeRctSimple(const rctSig & rv, const key & sk, unsigned int i, key &mask, hw::device &hwdev) {
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeSimple || rv.type == RCTTypeBulletproof || rv.type == RCTTypeBulletproof2, false, "decodeRct called on non simple rctSig");
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeSimple || rv.type == RCTTypeBulletproof || rv.type == RCTTypeBulletproof2 || rv.type == RCTTypeSimpleBulletproof, false, "decodeRct called on non simple rctSig");
|
||||
CHECK_AND_ASSERT_THROW_MES(i < rv.ecdhInfo.size(), "Bad index");
|
||||
CHECK_AND_ASSERT_THROW_MES(rv.outPk.size() == rv.ecdhInfo.size(), "Mismatched sizes of rv.outPk and rv.ecdhInfo");
|
||||
|
||||
@@ -1208,12 +1402,12 @@ namespace rct {
|
||||
}
|
||||
|
||||
bool signMultisig(rctSig &rv, const std::vector<unsigned int> &indices, const keyV &k, const multisig_out &msout, const key &secret_key) {
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeFull || rv.type == RCTTypeSimple || rv.type == RCTTypeBulletproof || rv.type == RCTTypeBulletproof2,
|
||||
CHECK_AND_ASSERT_MES(rv.type == RCTTypeFull || rv.type == RCTTypeSimple || rv.type == RCTTypeBulletproof || rv.type == RCTTypeBulletproof2 || rv.type == RCTTypeFullBulletproof || rv.type == RCTTypeSimpleBulletproof,
|
||||
false, "unsupported rct type");
|
||||
CHECK_AND_ASSERT_MES(indices.size() == k.size(), false, "Mismatched k/indices sizes");
|
||||
CHECK_AND_ASSERT_MES(k.size() == rv.p.MGs.size(), false, "Mismatched k/MGs size");
|
||||
CHECK_AND_ASSERT_MES(k.size() == msout.c.size(), false, "Mismatched k/msout.c size");
|
||||
if (rv.type == RCTTypeFull)
|
||||
if (rv.type == RCTTypeFull || rv.type == RCTTypeFullBulletproof)
|
||||
{
|
||||
CHECK_AND_ASSERT_MES(rv.p.MGs.size() == 1, false, "MGs not a single element");
|
||||
}
|
||||
|
||||
@@ -123,6 +123,8 @@ namespace rct {
|
||||
rctSig genRct(const key &message, const ctkeyV & inSk, const ctkeyV & inPk, const keyV & destinations, const std::vector<xmr_amount> & amounts, const keyV &amount_keys, const multisig_kLRki *kLRki, multisig_out *msout, const int mixin, const RCTConfig &rct_config, hw::device &hwdev);
|
||||
rctSig genRctSimple(const key & message, const ctkeyV & inSk, const ctkeyV & inPk, const keyV & destinations, const std::vector<xmr_amount> & inamounts, const std::vector<xmr_amount> & outamounts, const keyV &amount_keys, const std::vector<multisig_kLRki> *kLRki, multisig_out *msout, xmr_amount txnFee, unsigned int mixin, const RCTConfig &rct_config, hw::device &hwdev);
|
||||
rctSig genRctSimple(const key & message, const ctkeyV & inSk, const keyV & destinations, const std::vector<xmr_amount> & inamounts, const std::vector<xmr_amount> & outamounts, xmr_amount txnFee, const ctkeyM & mixRing, const keyV &amount_keys, const std::vector<multisig_kLRki> *kLRki, multisig_out *msout, const std::vector<unsigned int> & index, ctkeyV &outSk, const RCTConfig &rct_config, hw::device &hwdev);
|
||||
rctSig genRctSimple_old(const key & message, const ctkeyV & inSk, const ctkeyV & inPk, const keyV & destinations, const std::vector<xmr_amount> & inamounts, const std::vector<xmr_amount> & outamounts, const keyV &amount_keys, const std::vector<multisig_kLRki> *kLRki, multisig_out *msout, xmr_amount txnFee, unsigned int mixin, const RCTConfig &rct_config, hw::device &hwdev);
|
||||
rctSig genRctSimple_old(const key & message, const ctkeyV & inSk, const keyV & destinations, const std::vector<xmr_amount> & inamounts, const std::vector<xmr_amount> & outamounts, xmr_amount txnFee, const ctkeyM & mixRing, const keyV &amount_keys, const std::vector<multisig_kLRki> *kLRki, multisig_out *msout, const std::vector<unsigned int> & index, ctkeyV &outSk, const RCTConfig &rct_config, hw::device &hwdev);
|
||||
bool verRct(const rctSig & rv, bool semantics);
|
||||
static inline bool verRct(const rctSig & rv) { return verRct(rv, true) && verRct(rv, false); }
|
||||
bool verRctSemanticsSimple(const rctSig & rv);
|
||||
|
||||
@@ -216,6 +216,7 @@ namespace rct {
|
||||
switch (type)
|
||||
{
|
||||
case RCTTypeSimple:
|
||||
case RCTTypeSimpleBulletproof:
|
||||
case RCTTypeBulletproof:
|
||||
case RCTTypeBulletproof2:
|
||||
return true;
|
||||
@@ -228,6 +229,8 @@ namespace rct {
|
||||
{
|
||||
switch (type)
|
||||
{
|
||||
case RCTTypeSimpleBulletproof:
|
||||
case RCTTypeFullBulletproof:
|
||||
case RCTTypeBulletproof:
|
||||
case RCTTypeBulletproof2:
|
||||
return true;
|
||||
@@ -236,6 +239,23 @@ namespace rct {
|
||||
}
|
||||
}
|
||||
|
||||
bool is_rct_old_bulletproof(int type)
|
||||
{
|
||||
switch (type)
|
||||
{
|
||||
case RCTTypeSimpleBulletproof:
|
||||
case RCTTypeFullBulletproof:
|
||||
return true;
|
||||
default:
|
||||
return false;
|
||||
}
|
||||
}
|
||||
|
||||
bool is_rct_new_bulletproof(int type)
|
||||
{
|
||||
return is_rct_bulletproof(type) && !is_rct_old_bulletproof(type);
|
||||
}
|
||||
|
||||
bool is_rct_borromean(int type)
|
||||
{
|
||||
switch (type)
|
||||
@@ -248,6 +268,25 @@ namespace rct {
|
||||
}
|
||||
}
|
||||
|
||||
size_t n_bulletproof_v1_amounts(const Bulletproof &proof)
|
||||
{
|
||||
CHECK_AND_ASSERT_MES(proof.L.size() >= 6, 0, "Invalid bulletproof L size");
|
||||
CHECK_AND_ASSERT_MES(proof.L.size() <= 31, 0, "Insane bulletproof L size");
|
||||
return 1 << (proof.L.size() - 6);
|
||||
}
|
||||
size_t n_bulletproof_v1_amounts(const std::vector<Bulletproof> &proofs)
|
||||
{
|
||||
size_t n = 0;
|
||||
for (const Bulletproof &proof: proofs)
|
||||
{
|
||||
size_t n2 = n_bulletproof_v1_amounts(proof);
|
||||
CHECK_AND_ASSERT_MES(n2 < std::numeric_limits<uint32_t>::max() - n, 0, "Invalid number of bulletproofs");
|
||||
if (n2 == 0)
|
||||
return 0;
|
||||
n += n2;
|
||||
}
|
||||
return n;
|
||||
}
|
||||
size_t n_bulletproof_amounts(const Bulletproof &proof)
|
||||
{
|
||||
CHECK_AND_ASSERT_MES(proof.L.size() >= 6, 0, "Invalid bulletproof L size");
|
||||
|
||||
@@ -214,8 +214,10 @@ namespace rct {
|
||||
};
|
||||
|
||||
size_t n_bulletproof_amounts(const Bulletproof &proof);
|
||||
size_t n_bulletproof_v1_amounts(const Bulletproof &proof);
|
||||
size_t n_bulletproof_max_amounts(const Bulletproof &proof);
|
||||
size_t n_bulletproof_amounts(const std::vector<Bulletproof> &proofs);
|
||||
size_t n_bulletproof_v1_amounts(const std::vector<Bulletproof> &proofs);
|
||||
size_t n_bulletproof_max_amounts(const std::vector<Bulletproof> &proofs);
|
||||
|
||||
//A container to hold all signatures necessary for RingCT
|
||||
@@ -229,8 +231,10 @@ namespace rct {
|
||||
RCTTypeNull = 0,
|
||||
RCTTypeFull = 1,
|
||||
RCTTypeSimple = 2,
|
||||
RCTTypeBulletproof = 3,
|
||||
RCTTypeBulletproof2 = 4,
|
||||
RCTTypeFullBulletproof = 3,
|
||||
RCTTypeSimpleBulletproof = 4,
|
||||
RCTTypeBulletproof = 5,
|
||||
RCTTypeBulletproof2 = 6,
|
||||
};
|
||||
enum RangeProofType { RangeProofBorromean, RangeProofBulletproof, RangeProofMultiOutputBulletproof, RangeProofPaddedBulletproof };
|
||||
struct RCTConfig {
|
||||
@@ -253,7 +257,7 @@ namespace rct {
|
||||
FIELD(type)
|
||||
if (type == RCTTypeNull)
|
||||
return true;
|
||||
if (type != RCTTypeFull && type != RCTTypeSimple && type != RCTTypeBulletproof && type != RCTTypeBulletproof2)
|
||||
if (type != RCTTypeFull && type != RCTTypeSimple && type != RCTTypeBulletproof && type != RCTTypeBulletproof2 && type != RCTTypeFullBulletproof && type != RCTTypeSimpleBulletproof)
|
||||
return false;
|
||||
VARINT_FIELD(txnFee)
|
||||
// inputs/outputs not saved, only here for serialization help
|
||||
@@ -326,9 +330,24 @@ namespace rct {
|
||||
{
|
||||
if (type == RCTTypeNull)
|
||||
return true;
|
||||
if (type != RCTTypeFull && type != RCTTypeSimple && type != RCTTypeBulletproof && type != RCTTypeBulletproof2)
|
||||
if (type != RCTTypeFull && type != RCTTypeSimple && type != RCTTypeBulletproof && type != RCTTypeBulletproof2 && type != RCTTypeFullBulletproof && type != RCTTypeSimpleBulletproof)
|
||||
return false;
|
||||
if (type == RCTTypeBulletproof || type == RCTTypeBulletproof2)
|
||||
if (type == RCTTypeSimpleBulletproof || type == RCTTypeFullBulletproof)
|
||||
{
|
||||
ar.tag("bp");
|
||||
ar.begin_array();
|
||||
PREPARE_CUSTOM_VECTOR_SERIALIZATION(outputs, bulletproofs);
|
||||
if (bulletproofs.size() != outputs)
|
||||
return false;
|
||||
for (size_t i = 0; i < outputs; ++i)
|
||||
{
|
||||
FIELDS(bulletproofs[i])
|
||||
if (outputs - i > 1)
|
||||
ar.delimit_array();
|
||||
}
|
||||
ar.end_array();
|
||||
}
|
||||
else if (type == RCTTypeBulletproof || type == RCTTypeBulletproof2)
|
||||
{
|
||||
uint32_t nbp = bulletproofs.size();
|
||||
if (type == RCTTypeBulletproof2)
|
||||
@@ -370,7 +389,7 @@ namespace rct {
|
||||
ar.begin_array();
|
||||
// we keep a byte for size of MGs, because we don't know whether this is
|
||||
// a simple or full rct signature, and it's starting to annoy the hell out of me
|
||||
size_t mg_elements = (type == RCTTypeSimple || type == RCTTypeBulletproof || type == RCTTypeBulletproof2) ? inputs : 1;
|
||||
size_t mg_elements = (type == RCTTypeSimple || type == RCTTypeBulletproof || type == RCTTypeBulletproof2 || type == RCTTypeSimpleBulletproof) ? inputs : 1;
|
||||
PREPARE_CUSTOM_VECTOR_SERIALIZATION(mg_elements, MGs);
|
||||
if (MGs.size() != mg_elements)
|
||||
return false;
|
||||
@@ -388,7 +407,7 @@ namespace rct {
|
||||
for (size_t j = 0; j < mixin + 1; ++j)
|
||||
{
|
||||
ar.begin_array();
|
||||
size_t mg_ss2_elements = ((type == RCTTypeSimple || type == RCTTypeBulletproof || type == RCTTypeBulletproof2) ? 1 : inputs) + 1;
|
||||
size_t mg_ss2_elements = ((type == RCTTypeSimple || type == RCTTypeBulletproof || type == RCTTypeBulletproof2 || type == RCTTypeSimpleBulletproof) ? 1 : inputs) + 1;
|
||||
PREPARE_CUSTOM_VECTOR_SERIALIZATION(mg_ss2_elements, MGs[i].ss[j]);
|
||||
if (MGs[i].ss[j].size() != mg_ss2_elements)
|
||||
return false;
|
||||
@@ -414,7 +433,7 @@ namespace rct {
|
||||
ar.delimit_array();
|
||||
}
|
||||
ar.end_array();
|
||||
if (type == RCTTypeBulletproof || type == RCTTypeBulletproof2)
|
||||
if (type == RCTTypeBulletproof || type == RCTTypeBulletproof2 || type == RCTTypeSimpleBulletproof)
|
||||
{
|
||||
ar.tag("pseudoOuts");
|
||||
ar.begin_array();
|
||||
@@ -438,12 +457,16 @@ namespace rct {
|
||||
|
||||
keyV& get_pseudo_outs()
|
||||
{
|
||||
return type == RCTTypeBulletproof || type == RCTTypeBulletproof2 ? p.pseudoOuts : pseudoOuts;
|
||||
if (type == RCTTypeBulletproof)
|
||||
return type == RCTTypeBulletproof || type == RCTTypeBulletproof2 ? p.pseudoOuts : pseudoOuts;
|
||||
return type == RCTTypeSimpleBulletproof ? p.pseudoOuts : pseudoOuts;
|
||||
}
|
||||
|
||||
keyV const& get_pseudo_outs() const
|
||||
{
|
||||
return type == RCTTypeBulletproof || type == RCTTypeBulletproof2 ? p.pseudoOuts : pseudoOuts;
|
||||
if (type == RCTTypeBulletproof)
|
||||
return type == RCTTypeBulletproof || type == RCTTypeBulletproof2 ? p.pseudoOuts : pseudoOuts;
|
||||
return type == RCTTypeSimpleBulletproof ? p.pseudoOuts : pseudoOuts;
|
||||
}
|
||||
};
|
||||
|
||||
@@ -550,6 +573,8 @@ namespace rct {
|
||||
|
||||
bool is_rct_simple(int type);
|
||||
bool is_rct_bulletproof(int type);
|
||||
bool is_rct_old_bulletproof(int type);
|
||||
bool is_rct_new_bulletproof(int type);
|
||||
bool is_rct_borromean(int type);
|
||||
|
||||
static inline const rct::key &pk2rct(const crypto::public_key &pk) { return (const rct::key&)pk; }
|
||||
|
||||
@@ -90,15 +90,9 @@ namespace cryptonote
|
||||
command_line::add_arg(desc, arg_rpc_bind_port);
|
||||
command_line::add_arg(desc, arg_rpc_restricted_bind_port);
|
||||
command_line::add_arg(desc, arg_restricted_rpc);
|
||||
command_line::add_arg(desc, arg_rpc_ssl);
|
||||
command_line::add_arg(desc, arg_rpc_ssl_private_key);
|
||||
command_line::add_arg(desc, arg_rpc_ssl_certificate);
|
||||
command_line::add_arg(desc, arg_rpc_ssl_ca_certificates);
|
||||
command_line::add_arg(desc, arg_rpc_ssl_allowed_fingerprints);
|
||||
command_line::add_arg(desc, arg_rpc_ssl_allow_any_cert);
|
||||
command_line::add_arg(desc, arg_bootstrap_daemon_address);
|
||||
command_line::add_arg(desc, arg_bootstrap_daemon_login);
|
||||
cryptonote::rpc_args::init_options(desc);
|
||||
cryptonote::rpc_args::init_options(desc, true);
|
||||
}
|
||||
//------------------------------------------------------------------------------------------------------------------------------
|
||||
core_rpc_server::core_rpc_server(
|
||||
@@ -118,7 +112,7 @@ namespace cryptonote
|
||||
m_restricted = restricted;
|
||||
m_net_server.set_threads_prefix("RPC");
|
||||
|
||||
auto rpc_config = cryptonote::rpc_args::process(vm);
|
||||
auto rpc_config = cryptonote::rpc_args::process(vm, true);
|
||||
if (!rpc_config)
|
||||
return false;
|
||||
|
||||
@@ -151,46 +145,9 @@ namespace cryptonote
|
||||
if (rpc_config->login)
|
||||
http_login.emplace(std::move(rpc_config->login->username), std::move(rpc_config->login->password).password());
|
||||
|
||||
epee::net_utils::ssl_options_t ssl_options = epee::net_utils::ssl_support_t::e_ssl_support_autodetect;
|
||||
if (command_line::get_arg(vm, arg_rpc_ssl_allow_any_cert))
|
||||
ssl_options.verification = epee::net_utils::ssl_verification_t::none;
|
||||
else
|
||||
{
|
||||
std::string ssl_ca_path = command_line::get_arg(vm, arg_rpc_ssl_ca_certificates);
|
||||
const std::vector<std::string> ssl_allowed_fingerprint_strings = command_line::get_arg(vm, arg_rpc_ssl_allowed_fingerprints);
|
||||
std::vector<std::vector<uint8_t>> ssl_allowed_fingerprints{ ssl_allowed_fingerprint_strings.size() };
|
||||
std::transform(ssl_allowed_fingerprint_strings.begin(), ssl_allowed_fingerprint_strings.end(), ssl_allowed_fingerprints.begin(), epee::from_hex::vector);
|
||||
for (const auto &fpr: ssl_allowed_fingerprints)
|
||||
{
|
||||
if (fpr.size() != SSL_FINGERPRINT_SIZE)
|
||||
{
|
||||
MERROR("SHA-256 fingerprint should be " BOOST_PP_STRINGIZE(SSL_FINGERPRINT_SIZE) " bytes long.");
|
||||
return false;
|
||||
}
|
||||
}
|
||||
|
||||
if (!ssl_ca_path.empty() || !ssl_allowed_fingerprints.empty())
|
||||
ssl_options = epee::net_utils::ssl_options_t{std::move(ssl_allowed_fingerprints), std::move(ssl_ca_path)};
|
||||
}
|
||||
|
||||
ssl_options.auth = epee::net_utils::ssl_authentication_t{
|
||||
command_line::get_arg(vm, arg_rpc_ssl_private_key), command_line::get_arg(vm, arg_rpc_ssl_certificate)
|
||||
};
|
||||
|
||||
// user specified CA file or fingeprints implies enabled SSL by default
|
||||
if (ssl_options.verification != epee::net_utils::ssl_verification_t::user_certificates || !command_line::is_arg_defaulted(vm, arg_rpc_ssl))
|
||||
{
|
||||
const std::string ssl = command_line::get_arg(vm, arg_rpc_ssl);
|
||||
if (!epee::net_utils::ssl_support_from_string(ssl_options.support, ssl))
|
||||
{
|
||||
MFATAL("Invalid RPC SSL support: " << ssl);
|
||||
return false;
|
||||
}
|
||||
}
|
||||
|
||||
auto rng = [](size_t len, uint8_t *ptr){ return crypto::rand(len, ptr); };
|
||||
return epee::http_server_impl_base<core_rpc_server, connection_context>::init(
|
||||
rng, std::move(port), std::move(rpc_config->bind_ip), std::move(rpc_config->access_control_origins), std::move(http_login), std::move(ssl_options)
|
||||
rng, std::move(port), std::move(rpc_config->bind_ip), std::move(rpc_config->access_control_origins), std::move(http_login), std::move(rpc_config->ssl_options)
|
||||
);
|
||||
}
|
||||
//------------------------------------------------------------------------------------------------------------------------------
|
||||
@@ -858,7 +815,7 @@ namespace cryptonote
|
||||
{
|
||||
res.status = "Failed";
|
||||
res.reason = "Sanity check failed";
|
||||
res.sanity_check_failed = true;
|
||||
res.sanity_check_failed = false;
|
||||
return true;
|
||||
}
|
||||
|
||||
@@ -948,16 +905,13 @@ namespace cryptonote
|
||||
return true;
|
||||
}
|
||||
|
||||
boost::thread::attributes attrs;
|
||||
attrs.set_stack_size(THREAD_STACK_SIZE);
|
||||
|
||||
cryptonote::miner &miner= m_core.get_miner();
|
||||
if (miner.is_mining())
|
||||
{
|
||||
res.status = "Already mining";
|
||||
return true;
|
||||
}
|
||||
if(!miner.start(info.address, static_cast<size_t>(req.threads_count), attrs, req.do_background_mining, req.ignore_battery))
|
||||
if(!miner.start(info.address, static_cast<size_t>(req.threads_count), req.do_background_mining, req.ignore_battery))
|
||||
{
|
||||
res.status = "Failed, mining not started";
|
||||
LOG_PRINT_L0(res.status);
|
||||
@@ -1005,13 +959,14 @@ namespace cryptonote
|
||||
const account_public_address& lMiningAdr = lMiner.get_mining_address();
|
||||
res.address = get_account_address_as_str(nettype(), false, lMiningAdr);
|
||||
const uint8_t major_version = m_core.get_blockchain_storage().get_current_hard_fork_version();
|
||||
const unsigned variant = major_version >= 7 ? major_version - 6 : 0;
|
||||
const unsigned variant = major_version >= 13 ? 6 : major_version >= 11 && major_version <= 12 ? 4 : 2;
|
||||
switch (variant)
|
||||
{
|
||||
case 0: res.pow_algorithm = "Cryptonight"; break;
|
||||
case 1: res.pow_algorithm = "CNv1 (Cryptonight variant 1)"; break;
|
||||
case 2: case 3: res.pow_algorithm = "CNv2 (Cryptonight variant 2)"; break;
|
||||
case 4: case 5: res.pow_algorithm = "CNv4 (Cryptonight variant 4)"; break;
|
||||
case 4: case 5: res.pow_algorithm = "CN/WOW"; break;
|
||||
case 6: res.pow_algorithm = "RandomWOW"; break;
|
||||
default: res.pow_algorithm = "I'm not sure actually"; break;
|
||||
}
|
||||
if (res.is_background_mining_enabled)
|
||||
@@ -1295,6 +1250,18 @@ namespace cryptonote
|
||||
LOG_ERROR("Failed to create block template");
|
||||
return false;
|
||||
}
|
||||
if (b.major_version >= RX_BLOCK_VERSION)
|
||||
{
|
||||
uint64_t seed_height, next_height;
|
||||
crypto::hash seed_hash;
|
||||
crypto::rx_seedheights(res.height, &seed_height, &next_height);
|
||||
seed_hash = m_core.get_block_id_by_height(seed_height);
|
||||
res.seed_hash = string_tools::pod_to_hex(seed_hash);
|
||||
if (next_height != seed_height) {
|
||||
seed_hash = m_core.get_block_id_by_height(next_height);
|
||||
res.next_seed_hash = string_tools::pod_to_hex(seed_hash);
|
||||
}
|
||||
}
|
||||
store_difficulty(wdiff, res.difficulty, res.wide_difficulty, res.difficulty_top64);
|
||||
blobdata block_blob = t_serializable_object_to_blob(b);
|
||||
crypto::public_key tx_pub_key = cryptonote::get_tx_pub_key_from_extra(b.miner_tx);
|
||||
@@ -1437,7 +1404,7 @@ namespace cryptonote
|
||||
return false;
|
||||
}
|
||||
b.nonce = req.starting_nonce;
|
||||
miner::find_nonce_for_given_block(b, template_res.difficulty, template_res.height);
|
||||
miner::find_nonce_for_given_block(&(m_core.get_blockchain_storage()), b, template_res.difficulty, template_res.height);
|
||||
|
||||
submit_req.front() = string_tools::buff_to_hex_nodelimer(block_to_blob(b));
|
||||
r = on_submitblock(submit_req, submit_res, error_resp, ctx);
|
||||
@@ -1482,7 +1449,7 @@ namespace cryptonote
|
||||
response.reward = get_block_reward(blk);
|
||||
response.block_size = response.block_weight = m_core.get_blockchain_storage().get_db().get_block_weight(height);
|
||||
response.num_txes = blk.tx_hashes.size();
|
||||
response.pow_hash = fill_pow_hash ? string_tools::pod_to_hex(get_block_longhash(blk, height)) : "";
|
||||
response.pow_hash = fill_pow_hash ? string_tools::pod_to_hex(get_block_longhash(&(m_core.get_blockchain_storage()), blk, height, 0)) : "";
|
||||
response.long_term_weight = m_core.get_blockchain_storage().get_db().get_block_long_term_weight(height);
|
||||
response.miner_tx_hash = string_tools::pod_to_hex(cryptonote::get_transaction_hash(blk.miner_tx));
|
||||
return true;
|
||||
@@ -2439,40 +2406,6 @@ namespace cryptonote
|
||||
, false
|
||||
};
|
||||
|
||||
const command_line::arg_descriptor<std::string> core_rpc_server::arg_rpc_ssl = {
|
||||
"rpc-ssl"
|
||||
, "Enable SSL on RPC connections: enabled|disabled|autodetect"
|
||||
, "autodetect"
|
||||
};
|
||||
|
||||
const command_line::arg_descriptor<std::string> core_rpc_server::arg_rpc_ssl_private_key = {
|
||||
"rpc-ssl-private-key"
|
||||
, "Path to a PEM format private key"
|
||||
, ""
|
||||
};
|
||||
|
||||
const command_line::arg_descriptor<std::string> core_rpc_server::arg_rpc_ssl_certificate = {
|
||||
"rpc-ssl-certificate"
|
||||
, "Path to a PEM format certificate"
|
||||
, ""
|
||||
};
|
||||
|
||||
const command_line::arg_descriptor<std::string> core_rpc_server::arg_rpc_ssl_ca_certificates = {
|
||||
"rpc-ssl-ca-certificates"
|
||||
, "Path to file containing concatenated PEM format certificate(s) to replace system CA(s)."
|
||||
};
|
||||
|
||||
const command_line::arg_descriptor<std::vector<std::string>> core_rpc_server::arg_rpc_ssl_allowed_fingerprints = {
|
||||
"rpc-ssl-allowed-fingerprints"
|
||||
, "List of certificate fingerprints to allow"
|
||||
};
|
||||
|
||||
const command_line::arg_descriptor<bool> core_rpc_server::arg_rpc_ssl_allow_any_cert = {
|
||||
"rpc-ssl-allow-any-cert"
|
||||
, "Allow any peer certificate"
|
||||
, false
|
||||
};
|
||||
|
||||
const command_line::arg_descriptor<std::string> core_rpc_server::arg_bootstrap_daemon_address = {
|
||||
"bootstrap-daemon-address"
|
||||
, "URL of a 'bootstrap' remote daemon that the connected wallets can use while this daemon is still not fully synced"
|
||||
|
||||
@@ -84,7 +84,7 @@ namespace cryptonote
|
||||
// advance which version they will stop working with
|
||||
// Don't go over 32767 for any of these
|
||||
#define CORE_RPC_VERSION_MAJOR 2
|
||||
#define CORE_RPC_VERSION_MINOR 6
|
||||
#define CORE_RPC_VERSION_MINOR 7
|
||||
#define MAKE_CORE_RPC_VERSION(major,minor) (((major)<<16)|(minor))
|
||||
#define CORE_RPC_VERSION MAKE_CORE_RPC_VERSION(CORE_RPC_VERSION_MAJOR, CORE_RPC_VERSION_MINOR)
|
||||
|
||||
@@ -590,7 +590,7 @@ namespace cryptonote
|
||||
BEGIN_KV_SERIALIZE_MAP()
|
||||
KV_SERIALIZE(tx_as_hex)
|
||||
KV_SERIALIZE_OPT(do_not_relay, false)
|
||||
KV_SERIALIZE_OPT(do_sanity_checks, true)
|
||||
KV_SERIALIZE_OPT(do_sanity_checks, false)
|
||||
END_KV_SERIALIZE_MAP()
|
||||
};
|
||||
typedef epee::misc_utils::struct_init<request_t> request;
|
||||
@@ -937,6 +937,8 @@ namespace cryptonote
|
||||
uint64_t reserved_offset;
|
||||
uint64_t expected_reward;
|
||||
std::string prev_hash;
|
||||
std::string seed_hash;
|
||||
std::string next_seed_hash;
|
||||
blobdata blocktemplate_blob;
|
||||
blobdata blockhashing_blob;
|
||||
std::string status;
|
||||
@@ -954,6 +956,8 @@ namespace cryptonote
|
||||
KV_SERIALIZE(blockhashing_blob)
|
||||
KV_SERIALIZE(status)
|
||||
KV_SERIALIZE(untrusted)
|
||||
KV_SERIALIZE(seed_hash)
|
||||
KV_SERIALIZE(next_seed_hash)
|
||||
END_KV_SERIALIZE_MAP()
|
||||
};
|
||||
typedef epee::misc_utils::struct_init<response_t> response;
|
||||
|
||||
@@ -408,10 +408,7 @@ namespace rpc
|
||||
return;
|
||||
}
|
||||
|
||||
boost::thread::attributes attrs;
|
||||
attrs.set_stack_size(THREAD_STACK_SIZE);
|
||||
|
||||
if(!m_core.get_miner().start(info.address, static_cast<size_t>(req.threads_count), attrs, req.do_background_mining, req.ignore_battery))
|
||||
if(!m_core.get_miner().start(info.address, static_cast<size_t>(req.threads_count), req.do_background_mining, req.ignore_battery))
|
||||
{
|
||||
res.error_details = "Failed, mining not started";
|
||||
LOG_PRINT_L0(res.error_details);
|
||||
|
||||
@@ -33,28 +33,95 @@
|
||||
#include <boost/bind.hpp>
|
||||
#include "common/command_line.h"
|
||||
#include "common/i18n.h"
|
||||
#include "hex.h"
|
||||
|
||||
namespace cryptonote
|
||||
{
|
||||
namespace
|
||||
{
|
||||
boost::optional<epee::net_utils::ssl_options_t> do_process_ssl(const boost::program_options::variables_map& vm, const rpc_args::descriptors& arg, const bool any_cert_option)
|
||||
{
|
||||
bool ssl_required = false;
|
||||
epee::net_utils::ssl_options_t ssl_options = epee::net_utils::ssl_support_t::e_ssl_support_enabled;
|
||||
if (any_cert_option && command_line::get_arg(vm, arg.rpc_ssl_allow_any_cert))
|
||||
ssl_options.verification = epee::net_utils::ssl_verification_t::none;
|
||||
else
|
||||
{
|
||||
std::string ssl_ca_file = command_line::get_arg(vm, arg.rpc_ssl_ca_certificates);
|
||||
const std::vector<std::string> ssl_allowed_fingerprints = command_line::get_arg(vm, arg.rpc_ssl_allowed_fingerprints);
|
||||
|
||||
std::vector<std::vector<uint8_t>> allowed_fingerprints{ ssl_allowed_fingerprints.size() };
|
||||
std::transform(ssl_allowed_fingerprints.begin(), ssl_allowed_fingerprints.end(), allowed_fingerprints.begin(), epee::from_hex::vector);
|
||||
for (const auto &fpr: allowed_fingerprints)
|
||||
{
|
||||
if (fpr.size() != SSL_FINGERPRINT_SIZE)
|
||||
{
|
||||
MERROR("SHA-256 fingerprint should be " BOOST_PP_STRINGIZE(SSL_FINGERPRINT_SIZE) " bytes long.");
|
||||
return boost::none;
|
||||
}
|
||||
}
|
||||
|
||||
if (!allowed_fingerprints.empty() || !ssl_ca_file.empty())
|
||||
{
|
||||
ssl_required = true;
|
||||
ssl_options = epee::net_utils::ssl_options_t{
|
||||
std::move(allowed_fingerprints), std::move(ssl_ca_file)
|
||||
};
|
||||
|
||||
if (command_line::get_arg(vm, arg.rpc_ssl_allow_chained))
|
||||
ssl_options.verification = epee::net_utils::ssl_verification_t::user_ca;
|
||||
}
|
||||
}
|
||||
|
||||
// user specified CA file or fingeprints implies enabled SSL by default
|
||||
if (!ssl_required && !epee::net_utils::ssl_support_from_string(ssl_options.support, command_line::get_arg(vm, arg.rpc_ssl)))
|
||||
{
|
||||
MERROR("Invalid argument for " << std::string(arg.rpc_ssl.name));
|
||||
return boost::none;
|
||||
}
|
||||
|
||||
ssl_options.auth = epee::net_utils::ssl_authentication_t{
|
||||
command_line::get_arg(vm, arg.rpc_ssl_private_key), command_line::get_arg(vm, arg.rpc_ssl_certificate)
|
||||
};
|
||||
|
||||
return {std::move(ssl_options)};
|
||||
}
|
||||
} // anonymous
|
||||
|
||||
rpc_args::descriptors::descriptors()
|
||||
: rpc_bind_ip({"rpc-bind-ip", rpc_args::tr("Specify IP to bind RPC server"), "127.0.0.1"})
|
||||
, rpc_login({"rpc-login", rpc_args::tr("Specify username[:password] required for RPC server"), "", true})
|
||||
, confirm_external_bind({"confirm-external-bind", rpc_args::tr("Confirm rpc-bind-ip value is NOT a loopback (local) IP")})
|
||||
, rpc_access_control_origins({"rpc-access-control-origins", rpc_args::tr("Specify a comma separated list of origins to allow cross origin resource sharing"), ""})
|
||||
, rpc_ssl({"rpc-ssl", rpc_args::tr("Enable SSL on RPC connections: enabled|disabled|autodetect"), "autodetect"})
|
||||
, rpc_ssl_private_key({"rpc-ssl-private-key", rpc_args::tr("Path to a PEM format private key"), ""})
|
||||
, rpc_ssl_certificate({"rpc-ssl-certificate", rpc_args::tr("Path to a PEM format certificate"), ""})
|
||||
, rpc_ssl_ca_certificates({"rpc-ssl-ca-certificates", rpc_args::tr("Path to file containing concatenated PEM format certificate(s) to replace system CA(s)."), ""})
|
||||
, rpc_ssl_allowed_fingerprints({"rpc-ssl-allowed-fingerprints", rpc_args::tr("List of certificate fingerprints to allow")})
|
||||
, rpc_ssl_allow_chained({"rpc-ssl-allow-chained", rpc_args::tr("Allow user (via --rpc-ssl-certificates) chain certificates"), false})
|
||||
, rpc_ssl_allow_any_cert({"rpc-ssl-allow-any-cert", rpc_args::tr("Allow any peer certificate"), false})
|
||||
{}
|
||||
|
||||
const char* rpc_args::tr(const char* str) { return i18n_translate(str, "cryptonote::rpc_args"); }
|
||||
|
||||
void rpc_args::init_options(boost::program_options::options_description& desc)
|
||||
void rpc_args::init_options(boost::program_options::options_description& desc, const bool any_cert_option)
|
||||
{
|
||||
const descriptors arg{};
|
||||
command_line::add_arg(desc, arg.rpc_bind_ip);
|
||||
command_line::add_arg(desc, arg.rpc_login);
|
||||
command_line::add_arg(desc, arg.confirm_external_bind);
|
||||
command_line::add_arg(desc, arg.rpc_access_control_origins);
|
||||
command_line::add_arg(desc, arg.rpc_ssl);
|
||||
command_line::add_arg(desc, arg.rpc_ssl_private_key);
|
||||
command_line::add_arg(desc, arg.rpc_ssl_certificate);
|
||||
command_line::add_arg(desc, arg.rpc_ssl_ca_certificates);
|
||||
command_line::add_arg(desc, arg.rpc_ssl_allowed_fingerprints);
|
||||
command_line::add_arg(desc, arg.rpc_ssl_allow_chained);
|
||||
if (any_cert_option)
|
||||
command_line::add_arg(desc, arg.rpc_ssl_allow_any_cert);
|
||||
}
|
||||
|
||||
boost::optional<rpc_args> rpc_args::process(const boost::program_options::variables_map& vm)
|
||||
boost::optional<rpc_args> rpc_args::process(const boost::program_options::variables_map& vm, const bool any_cert_option)
|
||||
{
|
||||
const descriptors arg{};
|
||||
rpc_args config{};
|
||||
@@ -118,6 +185,17 @@ namespace cryptonote
|
||||
config.access_control_origins = std::move(access_control_origins);
|
||||
}
|
||||
|
||||
auto ssl_options = do_process_ssl(vm, arg, any_cert_option);
|
||||
if (!ssl_options)
|
||||
return boost::none;
|
||||
config.ssl_options = std::move(*ssl_options);
|
||||
|
||||
return {std::move(config)};
|
||||
}
|
||||
|
||||
boost::optional<epee::net_utils::ssl_options_t> rpc_args::process_ssl(const boost::program_options::variables_map& vm, const bool any_cert_option)
|
||||
{
|
||||
const descriptors arg{};
|
||||
return do_process_ssl(vm, arg, any_cert_option);
|
||||
}
|
||||
}
|
||||
|
||||
@@ -35,6 +35,7 @@
|
||||
|
||||
#include "common/command_line.h"
|
||||
#include "common/password.h"
|
||||
#include "net/net_ssl.h"
|
||||
|
||||
namespace cryptonote
|
||||
{
|
||||
@@ -54,16 +55,29 @@ namespace cryptonote
|
||||
const command_line::arg_descriptor<std::string> rpc_login;
|
||||
const command_line::arg_descriptor<bool> confirm_external_bind;
|
||||
const command_line::arg_descriptor<std::string> rpc_access_control_origins;
|
||||
const command_line::arg_descriptor<std::string> rpc_ssl;
|
||||
const command_line::arg_descriptor<std::string> rpc_ssl_private_key;
|
||||
const command_line::arg_descriptor<std::string> rpc_ssl_certificate;
|
||||
const command_line::arg_descriptor<std::string> rpc_ssl_ca_certificates;
|
||||
const command_line::arg_descriptor<std::vector<std::string>> rpc_ssl_allowed_fingerprints;
|
||||
const command_line::arg_descriptor<bool> rpc_ssl_allow_chained;
|
||||
const command_line::arg_descriptor<bool> rpc_ssl_allow_any_cert;
|
||||
};
|
||||
|
||||
// `allow_any_cert` bool toggles `--rpc-ssl-allow-any-cert` configuration
|
||||
|
||||
static const char* tr(const char* str);
|
||||
static void init_options(boost::program_options::options_description& desc);
|
||||
static void init_options(boost::program_options::options_description& desc, const bool any_cert_option = false);
|
||||
|
||||
//! \return Arguments specified by user, or `boost::none` if error
|
||||
static boost::optional<rpc_args> process(const boost::program_options::variables_map& vm);
|
||||
static boost::optional<rpc_args> process(const boost::program_options::variables_map& vm, const bool any_cert_option = false);
|
||||
|
||||
//! \return SSL arguments specified by user, or `boost::none` if error
|
||||
static boost::optional<epee::net_utils::ssl_options_t> process_ssl(const boost::program_options::variables_map& vm, const bool any_cert_option = false);
|
||||
|
||||
std::string bind_ip;
|
||||
std::vector<std::string> access_control_origins;
|
||||
boost::optional<tools::login> login; // currently `boost::none` if unspecified by user
|
||||
epee::net_utils::ssl_options_t ssl_options = epee::net_utils::ssl_support_t::e_ssl_support_enabled;
|
||||
};
|
||||
}
|
||||
|
||||
@@ -61,5 +61,5 @@ target_link_libraries(simplewallet
|
||||
${EXTRA_LIBRARIES})
|
||||
set_property(TARGET simplewallet
|
||||
PROPERTY
|
||||
OUTPUT_NAME "monero-wallet-cli")
|
||||
OUTPUT_NAME "wownero-wallet-cli")
|
||||
install(TARGETS simplewallet DESTINATION bin)
|
||||
|
||||
@@ -66,6 +66,9 @@
|
||||
#include "version.h"
|
||||
#include <stdexcept>
|
||||
#include "wallet/message_store.h"
|
||||
#include <unistd.h>
|
||||
#include <stdlib.h>
|
||||
#include <time.h>
|
||||
|
||||
#ifdef WIN32
|
||||
#include <boost/locale.hpp>
|
||||
@@ -88,9 +91,9 @@ typedef cryptonote::simple_wallet sw;
|
||||
|
||||
#define EXTENDED_LOGS_FILE "wallet_details.log"
|
||||
|
||||
#define DEFAULT_MIX 10
|
||||
#define DEFAULT_MIX 21
|
||||
|
||||
#define MIN_RING_SIZE 11 // Used to inform user about min ring size -- does not track actual protocol
|
||||
#define MIN_RING_SIZE 22 // Used to inform user about min ring size -- does not track actual protocol
|
||||
|
||||
#define LOCK_IDLE_SCOPE() \
|
||||
bool auto_refresh_enabled = m_auto_refresh_enabled.load(std::memory_order_relaxed); \
|
||||
@@ -147,7 +150,7 @@ namespace
|
||||
const command_line::arg_descriptor<bool> arg_allow_mismatched_daemon_version = {"allow-mismatched-daemon-version", sw::tr("Allow communicating with a daemon that uses a different RPC version"), false};
|
||||
const command_line::arg_descriptor<uint64_t> arg_restore_height = {"restore-height", sw::tr("Restore from specific blockchain height"), 0};
|
||||
const command_line::arg_descriptor<std::string> arg_restore_date = {"restore-date", sw::tr("Restore from estimated blockchain height on specified date"), ""};
|
||||
const command_line::arg_descriptor<bool> arg_do_not_relay = {"do-not-relay", sw::tr("The newly created transaction will not be relayed to the monero network"), false};
|
||||
const command_line::arg_descriptor<bool> arg_do_not_relay = {"do-not-relay", sw::tr("The newly created transaction will not be relayed to the wownero network"), false};
|
||||
const command_line::arg_descriptor<bool> arg_create_address_file = {"create-address-file", sw::tr("Create an address file for new wallets"), false};
|
||||
const command_line::arg_descriptor<std::string> arg_subaddress_lookahead = {"subaddress-lookahead", tools::wallet2::tr("Set subaddress lookahead sizes to <major>:<minor>"), ""};
|
||||
const command_line::arg_descriptor<bool> arg_use_english_language_names = {"use-english-language-names", sw::tr("Display English language names"), false};
|
||||
@@ -217,7 +220,7 @@ namespace
|
||||
const char* USAGE_MMS("mms [<subcommand> [<subcommand_parameters>]]");
|
||||
const char* USAGE_MMS_INIT("mms init <required_signers>/<authorized_signers> <own_label> <own_transport_address>");
|
||||
const char* USAGE_MMS_INFO("mms info");
|
||||
const char* USAGE_MMS_SIGNER("mms signer [<number> <label> [<transport_address> [<monero_address>]]]");
|
||||
const char* USAGE_MMS_SIGNER("mms signer [<number> <label> [<transport_address> [<wownero_address>]]]");
|
||||
const char* USAGE_MMS_LIST("mms list");
|
||||
const char* USAGE_MMS_NEXT("mms next [sync]");
|
||||
const char* USAGE_MMS_SYNC("mms sync");
|
||||
@@ -444,7 +447,7 @@ namespace
|
||||
std::stringstream prompt;
|
||||
prompt << sw::tr("For URL: ") << url
|
||||
<< ", " << dnssec_str << std::endl
|
||||
<< sw::tr(" Monero Address = ") << addresses[0]
|
||||
<< sw::tr(" Wownero Address = ") << addresses[0]
|
||||
<< std::endl
|
||||
<< sw::tr("Is this OK?")
|
||||
;
|
||||
@@ -1614,7 +1617,7 @@ bool simple_wallet::export_raw_multisig(const std::vector<std::string> &args)
|
||||
for (auto &ptx: txs.m_ptx)
|
||||
{
|
||||
const crypto::hash txid = cryptonote::get_transaction_hash(ptx.tx);
|
||||
const std::string filename = std::string("raw_multisig_monero_tx_") + epee::string_tools::pod_to_hex(txid);
|
||||
const std::string filename = std::string("raw_multisig_wownero_tx_") + epee::string_tools::pod_to_hex(txid);
|
||||
if (!filenames.empty())
|
||||
filenames += ", ";
|
||||
filenames += filename;
|
||||
@@ -2142,25 +2145,25 @@ bool simple_wallet::net_stats(const std::vector<std::string> &args)
|
||||
|
||||
bool simple_wallet::welcome(const std::vector<std::string> &args)
|
||||
{
|
||||
message_writer() << tr("Welcome to Monero, the private cryptocurrency.");
|
||||
message_writer() << tr("Welcome to Wownero, a private meme cryptocurrency.");
|
||||
message_writer() << "";
|
||||
message_writer() << tr("Monero, like Bitcoin, is a cryptocurrency. That is, it is digital money.");
|
||||
message_writer() << tr("Unlike Bitcoin, your Monero transactions and balance stay private, and not visible to the world by default.");
|
||||
message_writer() << tr("Wownero, like Monero, is a bad ass cryptocurrency. That is, it is magic internet money.");
|
||||
message_writer() << tr("Unlike Bitcoin, your Wownero transactions and balance stay private, and not visible to the world by default.");
|
||||
message_writer() << tr("However, you have the option of making those available to select parties, if you choose to.");
|
||||
message_writer() << "";
|
||||
message_writer() << tr("Monero protects your privacy on the blockchain, and while Monero strives to improve all the time,");
|
||||
message_writer() << tr("Wownero protects your questionable purchasing habits on the blockchain, and while Wownero strives to copy Monero as much as we can,");
|
||||
message_writer() << tr("no privacy technology can be 100% perfect, Monero included.");
|
||||
message_writer() << tr("Monero cannot protect you from malware, and it may not be as effective as we hope against powerful adversaries.");
|
||||
message_writer() << tr("Flaws in Monero may be discovered in the future, and attacks may be developed to peek under some");
|
||||
message_writer() << tr("of the layers of privacy Monero provides. Be safe and practice defense in depth.");
|
||||
message_writer() << tr("No one can protect you from anything!!!");
|
||||
message_writer() << tr("Flaws in Wownero are likely, and script kiddies are dumb enough to attack the network.");
|
||||
message_writer() << tr("Be safe and practice defense in depth.");
|
||||
message_writer() << "";
|
||||
message_writer() << tr("Welcome to Monero and financial privacy. For more information, see https://getmonero.org/");
|
||||
message_writer() << tr("Welcome to Wownero and enterprise level trolling. For more information, see http://wownero.org/");
|
||||
return true;
|
||||
}
|
||||
|
||||
bool simple_wallet::version(const std::vector<std::string> &args)
|
||||
{
|
||||
message_writer() << "Monero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")";
|
||||
message_writer() << "Wownero '" << MONERO_RELEASE_NAME << "' (v" << MONERO_VERSION_FULL << ")";
|
||||
return true;
|
||||
}
|
||||
|
||||
@@ -2420,7 +2423,7 @@ bool simple_wallet::set_unit(const std::vector<std::string> &args/* = std::vecto
|
||||
const std::string &unit = args[1];
|
||||
unsigned int decimal_point = CRYPTONOTE_DISPLAY_DECIMAL_POINT;
|
||||
|
||||
if (unit == "monero")
|
||||
if (unit == "wownero")
|
||||
decimal_point = CRYPTONOTE_DISPLAY_DECIMAL_POINT;
|
||||
else if (unit == "millinero")
|
||||
decimal_point = CRYPTONOTE_DISPLAY_DECIMAL_POINT - 3;
|
||||
@@ -2705,6 +2708,27 @@ bool simple_wallet::set_device_name(const std::vector<std::string> &args/* = std
|
||||
}
|
||||
|
||||
bool simple_wallet::help(const std::vector<std::string> &args/* = std::vector<std::string>()*/)
|
||||
{
|
||||
success_msg_writer() <<
|
||||
"Commands:\n" <<
|
||||
tr(" \"balance\" - Show balance.\n") <<
|
||||
tr(" \"address new\" - Create new subaddress.\n") <<
|
||||
tr(" \"address all\" - Show all addresses.\n") <<
|
||||
tr(" \"transfer [address] [amount]\" - Send WOW to an address.\n") <<
|
||||
tr(" \"show_transfers [in|out|pending|failed|pool]\" - Show transactions.\n") <<
|
||||
tr(" \"sweep_all [address]\" - Send whole balance to another wallet.\n") <<
|
||||
tr(" \"seed\" - Show secret 25 words that can be used to recover this wallet.\n") <<
|
||||
tr(" \"refresh\" - Synchronize wallet with the Wownero network.\n") <<
|
||||
tr(" \"status\" - Check current status of wallet.\n") <<
|
||||
tr(" \"version\" - Check software version.\n") <<
|
||||
tr(" \"help\" - Show simplified help section.\n") <<
|
||||
tr(" \"help_advanced\" - Show advanced help section.\n") <<
|
||||
tr(" \"save\" - Save wallet.\n") <<
|
||||
" \"exit\" - Exit wallet.\n\n";
|
||||
return true;
|
||||
}
|
||||
|
||||
bool simple_wallet::help_advanced(const std::vector<std::string> &args/* = std::vector<std::string>()*/)
|
||||
{
|
||||
if(args.empty())
|
||||
{
|
||||
@@ -2794,7 +2818,7 @@ simple_wallet::simple_wallet()
|
||||
m_cmd_binder.set_handler("donate",
|
||||
boost::bind(&simple_wallet::donate, this, _1),
|
||||
tr(USAGE_DONATE),
|
||||
tr("Donate <amount> to the development team (donate.getmonero.org)."));
|
||||
tr("Donate <amount> to the development team."));
|
||||
m_cmd_binder.set_handler("sign_transfer",
|
||||
boost::bind(&simple_wallet::sign_transfer, this, _1),
|
||||
tr(USAGE_SIGN_TRANSFER),
|
||||
@@ -2867,8 +2891,8 @@ simple_wallet::simple_wallet()
|
||||
"ask-password <0|1|2 (or never|action|decrypt)>\n "
|
||||
" action: ask the password before many actions such as transfer, etc\n "
|
||||
" decrypt: same as action, but keeps the spend key encrypted in memory when not needed\n "
|
||||
"unit <monero|millinero|micronero|nanonero|piconero>\n "
|
||||
" Set the default monero (sub-)unit.\n "
|
||||
"unit <wownero|millinero|micronero|nanonero|piconero>\n "
|
||||
" Set the default wownero (sub-)unit.\n "
|
||||
"min-outputs-count [n]\n "
|
||||
" Try to keep at least that many outputs of value at least min-outputs-value.\n "
|
||||
"min-outputs-value [n]\n "
|
||||
@@ -2884,12 +2908,12 @@ simple_wallet::simple_wallet()
|
||||
"auto-low-priority <1|0>\n "
|
||||
" Whether to automatically use the low priority fee level when it's safe to do so.\n "
|
||||
"segregate-pre-fork-outputs <1|0>\n "
|
||||
" Set this if you intend to spend outputs on both Monero AND a key reusing fork.\n "
|
||||
" Set this if you intend to spend outputs on both Wownero AND a key reusing fork.\n "
|
||||
"key-reuse-mitigation2 <1|0>\n "
|
||||
" Set this if you are not sure whether you will spend on a key reusing Monero fork later.\n"
|
||||
" Set this if you are not sure whether you will spend on a key reusing Wownero fork later.\n"
|
||||
"subaddress-lookahead <major>:<minor>\n "
|
||||
" Set the lookahead sizes for the subaddress hash table.\n "
|
||||
" Set this if you are not sure whether you will spend on a key reusing Monero fork later.\n "
|
||||
" Set this if you are not sure whether you will spend on a key reusing Wownero fork later.\n "
|
||||
"segregation-height <n>\n "
|
||||
" Set to the height of a key reusing fork you want to use, 0 to use default."));
|
||||
m_cmd_binder.set_handler("encrypted_seed",
|
||||
@@ -3080,7 +3104,7 @@ simple_wallet::simple_wallet()
|
||||
m_cmd_binder.set_handler("mms signer",
|
||||
boost::bind(&simple_wallet::mms, this, _1),
|
||||
tr(USAGE_MMS_SIGNER),
|
||||
tr("Set or modify authorized signer info (single-word label, transport address, Monero address), or list all signers"));
|
||||
tr("Set or modify authorized signer info (single-word label, transport address, Wownero address), or list all signers"));
|
||||
m_cmd_binder.set_handler("mms list",
|
||||
boost::bind(&simple_wallet::mms, this, _1),
|
||||
tr(USAGE_MMS_LIST),
|
||||
@@ -3193,7 +3217,7 @@ simple_wallet::simple_wallet()
|
||||
m_cmd_binder.set_handler("welcome",
|
||||
boost::bind(&simple_wallet::welcome, this, _1),
|
||||
tr(USAGE_WELCOME),
|
||||
tr("Prints basic info about Monero for first time users"));
|
||||
tr("Prints basic info about Wownero for first time users"));
|
||||
m_cmd_binder.set_handler("version",
|
||||
boost::bind(&simple_wallet::version, this, _1),
|
||||
tr(USAGE_VERSION),
|
||||
@@ -3201,7 +3225,17 @@ simple_wallet::simple_wallet()
|
||||
m_cmd_binder.set_handler("help",
|
||||
boost::bind(&simple_wallet::help, this, _1),
|
||||
tr(USAGE_HELP),
|
||||
tr("Show simplified help section."));
|
||||
m_cmd_binder.set_handler("help_advanced",
|
||||
boost::bind(&simple_wallet::help_advanced, this, _1),
|
||||
tr("help_advanced"),
|
||||
tr("Show the help section or the documentation about a <command>."));
|
||||
m_cmd_binder.set_handler("churn",
|
||||
boost::bind(&simple_wallet::churn, this, _1),
|
||||
tr("churn"),
|
||||
tr("Churning can enhance privacy by increasing the distance of your funds from the source. This is especially\n"
|
||||
"important if your funds come from an exchange or a pool that shares public mining data. Each churn also helps\n"
|
||||
"create more decoy outputs, which is good for constructing stronger ring signatures."));
|
||||
}
|
||||
//----------------------------------------------------------------------------------------------------
|
||||
bool simple_wallet::set_variable(const std::vector<std::string> &args)
|
||||
@@ -3255,7 +3289,7 @@ bool simple_wallet::set_variable(const std::vector<std::string> &args)
|
||||
success_msg_writer() << "segregation-height = " << m_wallet->segregation_height();
|
||||
success_msg_writer() << "ignore-fractional-outputs = " << m_wallet->ignore_fractional_outputs();
|
||||
success_msg_writer() << "track-uses = " << m_wallet->track_uses();
|
||||
success_msg_writer() << "setup-background-mining = " << setup_background_mining_string + tr(" (set this to support the network and to get a chance to receive new monero)");
|
||||
success_msg_writer() << "setup-background-mining = " << setup_background_mining_string + tr(" (set this to support the network and to get a chance to receive new wownero)");
|
||||
success_msg_writer() << "device_name = " << m_wallet->device_name();
|
||||
return true;
|
||||
}
|
||||
@@ -3298,7 +3332,7 @@ bool simple_wallet::set_variable(const std::vector<std::string> &args)
|
||||
CHECK_SIMPLE_VARIABLE("priority", set_default_priority, tr("0, 1, 2, 3, or 4, or one of ") << join_priority_strings(", "));
|
||||
CHECK_SIMPLE_VARIABLE("confirm-missing-payment-id", set_confirm_missing_payment_id, tr("0 or 1"));
|
||||
CHECK_SIMPLE_VARIABLE("ask-password", set_ask_password, tr("0|1|2 (or never|action|decrypt)"));
|
||||
CHECK_SIMPLE_VARIABLE("unit", set_unit, tr("monero, millinero, micronero, nanonero, piconero"));
|
||||
CHECK_SIMPLE_VARIABLE("unit", set_unit, tr("wownero, millinero, micronero, nanonero, piconero"));
|
||||
CHECK_SIMPLE_VARIABLE("min-outputs-count", set_min_output_count, tr("unsigned integer"));
|
||||
CHECK_SIMPLE_VARIABLE("min-outputs-value", set_min_output_value, tr("amount"));
|
||||
CHECK_SIMPLE_VARIABLE("merge-destinations", set_merge_destinations, tr("0 or 1"));
|
||||
@@ -4090,7 +4124,7 @@ bool simple_wallet::init(const boost::program_options::variables_map& vm)
|
||||
check_background_mining(password);
|
||||
|
||||
if (welcome)
|
||||
message_writer(console_color_yellow, true) << tr("If you are new to Monero, type \"welcome\" for a brief overview.");
|
||||
message_writer(console_color_yellow, true) << tr("If you are new to Wownero, type \"welcome\" for a brief overview.");
|
||||
|
||||
if (m_long_payment_id_support)
|
||||
{
|
||||
@@ -4312,9 +4346,10 @@ boost::optional<epee::wipeable_string> simple_wallet::new_wallet(const boost::pr
|
||||
"**********************************************************************\n" <<
|
||||
tr("Your wallet has been generated!\n"
|
||||
"To start synchronizing with the daemon, use the \"refresh\" command.\n"
|
||||
"Use the \"help\" command to see the list of available commands.\n"
|
||||
"Use \"help <command>\" to see a command's documentation.\n"
|
||||
"Always use the \"exit\" command when closing monero-wallet-cli to save \n"
|
||||
"Use the \"help\" command to see a simplified list of available commands.\n"
|
||||
"Use the \"help_advanced\" command to see an advanced list of available commands.\n"
|
||||
"Use \"help_advanced <command>\" to see a command's documentation.\n"
|
||||
"Always use the \"exit\" command when closing wownero-wallet-cli to save \n"
|
||||
"your current session's state. Otherwise, you might need to synchronize \n"
|
||||
"your wallet again (your wallet keys are NOT at risk in any case).\n")
|
||||
;
|
||||
@@ -4566,8 +4601,9 @@ boost::optional<epee::wipeable_string> simple_wallet::open_wallet(const boost::p
|
||||
}
|
||||
success_msg_writer() <<
|
||||
"**********************************************************************\n" <<
|
||||
tr("Use the \"help\" command to see the list of available commands.\n") <<
|
||||
tr("Use \"help <command>\" to see a command's documentation.\n") <<
|
||||
tr("Use the \"help\" command to see a simplified list of available commands.\n") <<
|
||||
tr("Use the \"help_advanced\" command to see an advanced list of available commands.\n") <<
|
||||
tr("Use \"help_advanced <command>\" to see a command's documentation.\n") <<
|
||||
"**********************************************************************";
|
||||
return std::move(password);
|
||||
}
|
||||
@@ -4680,7 +4716,7 @@ void simple_wallet::start_background_mining()
|
||||
return;
|
||||
}
|
||||
}
|
||||
success_msg_writer() << tr("Background mining enabled. Thank you for supporting the Monero network.");
|
||||
success_msg_writer() << tr("Background mining enabled. Thank you for supporting the Wownero network.");
|
||||
}
|
||||
//----------------------------------------------------------------------------------------------------
|
||||
void simple_wallet::stop_background_mining()
|
||||
@@ -4749,7 +4785,7 @@ void simple_wallet::check_background_mining(const epee::wipeable_string &passwor
|
||||
{
|
||||
message_writer() << tr("The daemon is not set up to background mine.");
|
||||
message_writer() << tr("With background mining enabled, the daemon will mine when idle and not on batttery.");
|
||||
message_writer() << tr("Enabling this supports the network you are using, and makes you eligible for receiving new monero");
|
||||
message_writer() << tr("Enabling this supports the network you are using, and makes you eligible for receiving new wownero");
|
||||
std::string accepted = input_line(tr("Do you want to do it now? (Y/Yes/N/No): "));
|
||||
if (std::cin.eof() || !command_line::is_yes(accepted)) {
|
||||
m_wallet->setup_background_mining(tools::wallet2::BackgroundMiningNo);
|
||||
@@ -4934,7 +4970,7 @@ void simple_wallet::on_new_block(uint64_t height, const cryptonote::block& block
|
||||
m_refresh_progress_reporter.update(height, false);
|
||||
}
|
||||
//----------------------------------------------------------------------------------------------------
|
||||
void simple_wallet::on_money_received(uint64_t height, const crypto::hash &txid, const cryptonote::transaction& tx, uint64_t amount, const cryptonote::subaddress_index& subaddr_index)
|
||||
void simple_wallet::on_money_received(uint64_t height, const crypto::hash &txid, const cryptonote::transaction& tx, uint64_t amount, const cryptonote::subaddress_index& subaddr_index, uint64_t unlock_time)
|
||||
{
|
||||
message_writer(console_color_green, false) << "\r" <<
|
||||
tr("Height ") << height << ", " <<
|
||||
@@ -4956,10 +4992,14 @@ void simple_wallet::on_money_received(uint64_t height, const crypto::hash &txid,
|
||||
(m_long_payment_id_support ? tr("WARNING: this transaction uses an unencrypted payment ID: consider using subaddresses instead.") : tr("WARNING: this transaction uses an unencrypted payment ID: these are obsolete. Support will be withdrawn in the future. Use subaddresses instead."));
|
||||
}
|
||||
}
|
||||
if (m_wallet->auto_confirm_churn() == 0) {
|
||||
if (unlock_time)
|
||||
message_writer() << tr("NOTE: This transaction is locked, see details with: show_transfer ") + epee::string_tools::pod_to_hex(txid);
|
||||
if (m_auto_refresh_refreshing)
|
||||
m_cmd_binder.print_prompt();
|
||||
else
|
||||
m_refresh_progress_reporter.update(height, true);
|
||||
}
|
||||
}
|
||||
//----------------------------------------------------------------------------------------------------
|
||||
void simple_wallet::on_unconfirmed_money_received(uint64_t height, const crypto::hash &txid, const cryptonote::transaction& tx, uint64_t amount, const cryptonote::subaddress_index& subaddr_index)
|
||||
@@ -4969,15 +5009,18 @@ void simple_wallet::on_unconfirmed_money_received(uint64_t height, const crypto:
|
||||
//----------------------------------------------------------------------------------------------------
|
||||
void simple_wallet::on_money_spent(uint64_t height, const crypto::hash &txid, const cryptonote::transaction& in_tx, uint64_t amount, const cryptonote::transaction& spend_tx, const cryptonote::subaddress_index& subaddr_index)
|
||||
{
|
||||
|
||||
message_writer(console_color_magenta, false) << "\r" <<
|
||||
tr("Height ") << height << ", " <<
|
||||
tr("txid ") << txid << ", " <<
|
||||
tr("spent ") << print_money(amount) << ", " <<
|
||||
tr("idx ") << subaddr_index;
|
||||
if (m_wallet->auto_confirm_churn() == 0) {
|
||||
if (m_auto_refresh_refreshing)
|
||||
m_cmd_binder.print_prompt();
|
||||
else
|
||||
m_refresh_progress_reporter.update(height, true);
|
||||
}
|
||||
}
|
||||
//----------------------------------------------------------------------------------------------------
|
||||
void simple_wallet::on_skip_transaction(uint64_t height, const crypto::hash &txid, const cryptonote::transaction& tx)
|
||||
@@ -5183,6 +5226,7 @@ bool simple_wallet::show_balance_unlocked(bool detailed)
|
||||
extra = tr(" (Some owned outputs have partial key images - import_multisig_info needed)");
|
||||
else if (m_wallet->has_unknown_key_images())
|
||||
extra += tr(" (Some owned outputs have missing key images - import_key_images needed)");
|
||||
if (m_wallet->auto_confirm_churn() == 0) {
|
||||
success_msg_writer() << tr("Currently selected account: [") << m_current_subaddress_account << tr("] ") << m_wallet->get_subaddress_label({m_current_subaddress_account, 0});
|
||||
const std::string tag = m_wallet->get_account_tags().second[m_current_subaddress_account];
|
||||
success_msg_writer() << tr("Tag: ") << (tag.empty() ? std::string{tr("(No tag assigned)")} : tag);
|
||||
@@ -5192,7 +5236,7 @@ bool simple_wallet::show_balance_unlocked(bool detailed)
|
||||
if (blocks_to_unlock > 0)
|
||||
unlock_time_message = (boost::format(" (%lu block(s) to unlock)") % blocks_to_unlock).str();
|
||||
success_msg_writer() << tr("Balance: ") << print_money(m_wallet->balance(m_current_subaddress_account)) << ", "
|
||||
<< tr("unlocked balance: ") << print_money(unlocked_balance) << unlock_time_message << extra;
|
||||
<< tr("unlocked balance: ") << print_money(unlocked_balance) << unlock_time_message << extra;}
|
||||
std::map<uint32_t, uint64_t> balance_per_subaddress = m_wallet->balance_per_subaddress(m_current_subaddress_account);
|
||||
std::map<uint32_t, std::pair<uint64_t, uint64_t>> unlocked_balance_per_subaddress = m_wallet->unlocked_balance_per_subaddress(m_current_subaddress_account);
|
||||
if (!detailed || balance_per_subaddress.empty())
|
||||
@@ -5758,7 +5802,7 @@ bool simple_wallet::transfer_main(int transfer_type, const std::vector<std::stri
|
||||
}
|
||||
else
|
||||
{
|
||||
if (boost::starts_with(local_args[i], "monero:"))
|
||||
if (boost::starts_with(local_args[i], "wownero:"))
|
||||
fail_msg_writer() << tr("Invalid last argument: ") << local_args.back() << ": " << error;
|
||||
else
|
||||
fail_msg_writer() << tr("Invalid last argument: ") << local_args.back();
|
||||
@@ -6008,7 +6052,7 @@ bool simple_wallet::transfer_main(int transfer_type, const std::vector<std::stri
|
||||
}
|
||||
else if (m_wallet->multisig())
|
||||
{
|
||||
bool r = m_wallet->save_multisig_tx(ptx_vector, "multisig_monero_tx");
|
||||
bool r = m_wallet->save_multisig_tx(ptx_vector, "multisig_wownero_tx");
|
||||
if (!r)
|
||||
{
|
||||
fail_msg_writer() << tr("Failed to write transaction(s) to file");
|
||||
@@ -6016,7 +6060,7 @@ bool simple_wallet::transfer_main(int transfer_type, const std::vector<std::stri
|
||||
}
|
||||
else
|
||||
{
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "multisig_monero_tx";
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "multisig_wownero_tx";
|
||||
}
|
||||
}
|
||||
else if (m_wallet->get_account().get_device().has_tx_cold_sign())
|
||||
@@ -6045,7 +6089,7 @@ bool simple_wallet::transfer_main(int transfer_type, const std::vector<std::stri
|
||||
}
|
||||
else if (m_wallet->watch_only())
|
||||
{
|
||||
bool r = m_wallet->save_tx(ptx_vector, "unsigned_monero_tx");
|
||||
bool r = m_wallet->save_tx(ptx_vector, "unsigned_wownero_tx");
|
||||
if (!r)
|
||||
{
|
||||
fail_msg_writer() << tr("Failed to write transaction(s) to file");
|
||||
@@ -6053,7 +6097,7 @@ bool simple_wallet::transfer_main(int transfer_type, const std::vector<std::stri
|
||||
}
|
||||
else
|
||||
{
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "unsigned_monero_tx";
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "unsigned_wownero_tx";
|
||||
}
|
||||
}
|
||||
else
|
||||
@@ -6146,26 +6190,26 @@ bool simple_wallet::sweep_unmixable(const std::vector<std::string> &args_)
|
||||
// actually commit the transactions
|
||||
if (m_wallet->multisig())
|
||||
{
|
||||
bool r = m_wallet->save_multisig_tx(ptx_vector, "multisig_monero_tx");
|
||||
bool r = m_wallet->save_multisig_tx(ptx_vector, "multisig_wownero_tx");
|
||||
if (!r)
|
||||
{
|
||||
fail_msg_writer() << tr("Failed to write transaction(s) to file");
|
||||
}
|
||||
else
|
||||
{
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "multisig_monero_tx";
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "multisig_wownero_tx";
|
||||
}
|
||||
}
|
||||
else if (m_wallet->watch_only())
|
||||
{
|
||||
bool r = m_wallet->save_tx(ptx_vector, "unsigned_monero_tx");
|
||||
bool r = m_wallet->save_tx(ptx_vector, "unsigned_wownero_tx");
|
||||
if (!r)
|
||||
{
|
||||
fail_msg_writer() << tr("Failed to write transaction(s) to file");
|
||||
}
|
||||
else
|
||||
{
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "unsigned_monero_tx";
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "unsigned_wownero_tx";
|
||||
}
|
||||
}
|
||||
else
|
||||
@@ -6383,8 +6427,10 @@ bool simple_wallet::sweep_main(uint64_t below, bool locked, const std::vector<st
|
||||
payment_id_seen = true;
|
||||
}
|
||||
|
||||
const bool is_wallet_address = m_wallet->get_address() == info.address;
|
||||
|
||||
// prompt is there is no payment id and confirmation is required
|
||||
if (m_long_payment_id_support && !payment_id_seen && m_wallet->confirm_missing_payment_id() && !info.is_subaddress)
|
||||
if (m_long_payment_id_support && !payment_id_seen && m_wallet->confirm_missing_payment_id() && !info.is_subaddress && !is_wallet_address)
|
||||
{
|
||||
std::string accepted = input_line(tr("No payment id is included with this transaction. Is this okay?"), true);
|
||||
if (std::cin.eof())
|
||||
@@ -6411,6 +6457,9 @@ bool simple_wallet::sweep_main(uint64_t below, bool locked, const std::vector<st
|
||||
}
|
||||
|
||||
// give user total and fee, and prompt to confirm
|
||||
|
||||
if (m_wallet->auto_confirm_churn() == 0)
|
||||
{
|
||||
uint64_t total_fee = 0, total_sent = 0;
|
||||
for (size_t n = 0; n < ptx_vector.size(); ++n)
|
||||
{
|
||||
@@ -6453,18 +6502,19 @@ bool simple_wallet::sweep_main(uint64_t below, bool locked, const std::vector<st
|
||||
|
||||
return true;
|
||||
}
|
||||
}
|
||||
|
||||
// actually commit the transactions
|
||||
if (m_wallet->multisig())
|
||||
{
|
||||
bool r = m_wallet->save_multisig_tx(ptx_vector, "multisig_monero_tx");
|
||||
bool r = m_wallet->save_multisig_tx(ptx_vector, "multisig_wownero_tx");
|
||||
if (!r)
|
||||
{
|
||||
fail_msg_writer() << tr("Failed to write transaction(s) to file");
|
||||
}
|
||||
else
|
||||
{
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "multisig_monero_tx";
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "multisig_wownero_tx";
|
||||
}
|
||||
}
|
||||
else if (m_wallet->get_account().get_device().has_tx_cold_sign())
|
||||
@@ -6494,14 +6544,14 @@ bool simple_wallet::sweep_main(uint64_t below, bool locked, const std::vector<st
|
||||
}
|
||||
else if (m_wallet->watch_only())
|
||||
{
|
||||
bool r = m_wallet->save_tx(ptx_vector, "unsigned_monero_tx");
|
||||
bool r = m_wallet->save_tx(ptx_vector, "unsigned_wownero_tx");
|
||||
if (!r)
|
||||
{
|
||||
fail_msg_writer() << tr("Failed to write transaction(s) to file");
|
||||
}
|
||||
else
|
||||
{
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "unsigned_monero_tx";
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "unsigned_wownero_tx";
|
||||
}
|
||||
}
|
||||
else
|
||||
@@ -6712,26 +6762,26 @@ bool simple_wallet::sweep_single(const std::vector<std::string> &args_)
|
||||
// actually commit the transactions
|
||||
if (m_wallet->multisig())
|
||||
{
|
||||
bool r = m_wallet->save_multisig_tx(ptx_vector, "multisig_monero_tx");
|
||||
bool r = m_wallet->save_multisig_tx(ptx_vector, "multisig_wownero_tx");
|
||||
if (!r)
|
||||
{
|
||||
fail_msg_writer() << tr("Failed to write transaction(s) to file");
|
||||
}
|
||||
else
|
||||
{
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "multisig_monero_tx";
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "multisig_wownero_tx";
|
||||
}
|
||||
}
|
||||
else if (m_wallet->watch_only())
|
||||
{
|
||||
bool r = m_wallet->save_tx(ptx_vector, "unsigned_monero_tx");
|
||||
bool r = m_wallet->save_tx(ptx_vector, "unsigned_wownero_tx");
|
||||
if (!r)
|
||||
{
|
||||
fail_msg_writer() << tr("Failed to write transaction(s) to file");
|
||||
}
|
||||
else
|
||||
{
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "unsigned_monero_tx";
|
||||
success_msg_writer(true) << tr("Unsigned transaction(s) successfully written to file: ") << "unsigned_wownero_tx";
|
||||
}
|
||||
}
|
||||
else
|
||||
@@ -7028,7 +7078,7 @@ bool simple_wallet::sign_transfer(const std::vector<std::string> &args_)
|
||||
std::vector<tools::wallet2::pending_tx> ptx;
|
||||
try
|
||||
{
|
||||
bool r = m_wallet->sign_tx("unsigned_monero_tx", "signed_monero_tx", ptx, [&](const tools::wallet2::unsigned_tx_set &tx){ return accept_loaded_tx(tx); }, export_raw);
|
||||
bool r = m_wallet->sign_tx("unsigned_wownero_tx", "signed_wownero_tx", ptx, [&](const tools::wallet2::unsigned_tx_set &tx){ return accept_loaded_tx(tx); }, export_raw);
|
||||
if (!r)
|
||||
{
|
||||
fail_msg_writer() << tr("Failed to sign transaction");
|
||||
@@ -7048,7 +7098,7 @@ bool simple_wallet::sign_transfer(const std::vector<std::string> &args_)
|
||||
txids_as_text += (", ");
|
||||
txids_as_text += epee::string_tools::pod_to_hex(get_transaction_hash(t.tx));
|
||||
}
|
||||
success_msg_writer(true) << tr("Transaction successfully signed to file ") << "signed_monero_tx" << ", txid " << txids_as_text;
|
||||
success_msg_writer(true) << tr("Transaction successfully signed to file ") << "signed_wownero_tx" << ", txid " << txids_as_text;
|
||||
if (export_raw)
|
||||
{
|
||||
std::string rawfiles_as_text;
|
||||
@@ -7056,7 +7106,7 @@ bool simple_wallet::sign_transfer(const std::vector<std::string> &args_)
|
||||
{
|
||||
if (i > 0)
|
||||
rawfiles_as_text += ", ";
|
||||
rawfiles_as_text += "signed_monero_tx_raw" + (ptx.size() == 1 ? "" : ("_" + std::to_string(i)));
|
||||
rawfiles_as_text += "signed_wownero_tx_raw" + (ptx.size() == 1 ? "" : ("_" + std::to_string(i)));
|
||||
}
|
||||
success_msg_writer(true) << tr("Transaction raw hex data exported to ") << rawfiles_as_text;
|
||||
}
|
||||
@@ -7076,7 +7126,7 @@ bool simple_wallet::submit_transfer(const std::vector<std::string> &args_)
|
||||
try
|
||||
{
|
||||
std::vector<tools::wallet2::pending_tx> ptx_vector;
|
||||
bool r = m_wallet->load_tx("signed_monero_tx", ptx_vector, [&](const tools::wallet2::signed_tx_set &tx){ return accept_loaded_tx(tx); });
|
||||
bool r = m_wallet->load_tx("signed_wownero_tx", ptx_vector, [&](const tools::wallet2::signed_tx_set &tx){ return accept_loaded_tx(tx); });
|
||||
if (!r)
|
||||
{
|
||||
fail_msg_writer() << tr("Failed to load transaction from file");
|
||||
@@ -7226,7 +7276,7 @@ bool simple_wallet::get_tx_proof(const std::vector<std::string> &args)
|
||||
try
|
||||
{
|
||||
std::string sig_str = m_wallet->get_tx_proof(txid, info.address, info.is_subaddress, args.size() == 3 ? args[2] : "");
|
||||
const std::string filename = "monero_tx_proof";
|
||||
const std::string filename = "wownero_tx_proof";
|
||||
if (epee::file_io_utils::save_string_to_file(filename, sig_str))
|
||||
success_msg_writer() << tr("signature file saved to: ") << filename;
|
||||
else
|
||||
@@ -7438,7 +7488,7 @@ bool simple_wallet::get_spend_proof(const std::vector<std::string> &args)
|
||||
try
|
||||
{
|
||||
const std::string sig_str = m_wallet->get_spend_proof(txid, args.size() == 2 ? args[1] : "");
|
||||
const std::string filename = "monero_spend_proof";
|
||||
const std::string filename = "wownero_spend_proof";
|
||||
if (epee::file_io_utils::save_string_to_file(filename, sig_str))
|
||||
success_msg_writer() << tr("signature file saved to: ") << filename;
|
||||
else
|
||||
@@ -7527,7 +7577,7 @@ bool simple_wallet::get_reserve_proof(const std::vector<std::string> &args)
|
||||
try
|
||||
{
|
||||
const std::string sig_str = m_wallet->get_reserve_proof(account_minreserve, args.size() == 2 ? args[1] : "");
|
||||
const std::string filename = "monero_reserve_proof";
|
||||
const std::string filename = "wownero_reserve_proof";
|
||||
if (epee::file_io_utils::save_string_to_file(filename, sig_str))
|
||||
success_msg_writer() << tr("signature file saved to: ") << filename;
|
||||
else
|
||||
@@ -7683,6 +7733,8 @@ bool simple_wallet::get_transfers(std::vector<std::string>& local_args, std::vec
|
||||
local_args.erase(local_args.begin());
|
||||
}
|
||||
|
||||
const uint64_t last_block_height = m_wallet->get_blockchain_current_height();
|
||||
|
||||
if (in || coinbase) {
|
||||
std::list<std::pair<crypto::hash, tools::wallet2::payment_details>> payments;
|
||||
m_wallet->get_payments(payments, min_height, max_height, m_current_subaddress_account, subaddr_indices);
|
||||
@@ -7697,6 +7749,25 @@ bool simple_wallet::get_transfers(std::vector<std::string>& local_args, std::vec
|
||||
std::string destination = m_wallet->get_subaddress_as_str({m_current_subaddress_account, pd.m_subaddr_index.minor});
|
||||
const std::string type = pd.m_coinbase ? tr("block") : tr("in");
|
||||
const bool unlocked = m_wallet->is_transfer_unlocked(pd.m_unlock_time, pd.m_block_height);
|
||||
std::string locked_msg = "unlocked";
|
||||
if (!unlocked)
|
||||
{
|
||||
locked_msg = "locked";
|
||||
const uint64_t unlock_time = pd.m_unlock_time;
|
||||
if (pd.m_unlock_time < CRYPTONOTE_MAX_BLOCK_NUMBER)
|
||||
{
|
||||
uint64_t bh = std::max(pd.m_unlock_time, pd.m_block_height + CRYPTONOTE_DEFAULT_TX_SPENDABLE_AGE);
|
||||
if (bh >= last_block_height)
|
||||
locked_msg = std::to_string(bh - last_block_height) + " blks";
|
||||
}
|
||||
else
|
||||
{
|
||||
uint64_t current_time = static_cast<uint64_t>(time(NULL));
|
||||
uint64_t threshold = current_time + (m_wallet->use_fork_rules(2, 0) ? CRYPTONOTE_LOCKED_TX_ALLOWED_DELTA_SECONDS_V2 : CRYPTONOTE_LOCKED_TX_ALLOWED_DELTA_SECONDS_V1);
|
||||
if (threshold < pd.m_unlock_time)
|
||||
locked_msg = get_human_readable_timespan(std::chrono::seconds(pd.m_unlock_time - threshold));
|
||||
}
|
||||
}
|
||||
transfers.push_back({
|
||||
type,
|
||||
pd.m_block_height,
|
||||
@@ -7710,7 +7781,7 @@ bool simple_wallet::get_transfers(std::vector<std::string>& local_args, std::vec
|
||||
{{destination, pd.m_amount}},
|
||||
{pd.m_subaddr_index.minor},
|
||||
note,
|
||||
(unlocked) ? "unlocked" : "locked"
|
||||
locked_msg
|
||||
});
|
||||
}
|
||||
}
|
||||
@@ -9296,6 +9367,97 @@ bool simple_wallet::process_command(const std::vector<std::string> &args)
|
||||
return m_cmd_binder.process_command_vec(args);
|
||||
}
|
||||
//----------------------------------------------------------------------------------------------------
|
||||
bool simple_wallet::churn(const std::vector<std::string> &args_)
|
||||
{
|
||||
// Check if wallet is on MAINNET
|
||||
if (m_wallet->nettype() != cryptonote::MAINNET)
|
||||
{
|
||||
fail_msg_writer() << tr("Churning is only possible on Mainnet, operation cancelled.");
|
||||
return true;
|
||||
}
|
||||
|
||||
// Check balance
|
||||
if (m_wallet->unlocked_balance(m_current_subaddress_account) < 2)
|
||||
{
|
||||
fail_msg_writer() << tr("You need to have an unlocked balance of more than 2 WOW, operation cancelled.");
|
||||
return true;
|
||||
}
|
||||
|
||||
// Warning
|
||||
std::string warning = input_line(tr("Warning: Churning requires your wallet to be open for a few hours. If wallet is left unattended, make sure your computer is in a secure location. Continue?"));
|
||||
if (std::cin.eof() || !command_line::is_yes(warning))
|
||||
{
|
||||
message_writer() << tr("Operation cancelled.");
|
||||
return true;
|
||||
}
|
||||
|
||||
// Generate pseudo-random integers for the number of churns and interval pause
|
||||
int churn_number, pause_time, i;
|
||||
srand (time(NULL)); // seed RNG with current time
|
||||
churn_number = rand()%(8 + 1 - 2) + 2; // churn between 2 to 8 times
|
||||
|
||||
std::stack<int> pauses;
|
||||
float total_time = 0;
|
||||
// no pause for the last churn
|
||||
for (i = 1; i <= churn_number - 1; ++i) {
|
||||
pause_time = rand()%(120 + 1 - 60) + 60; // wait between 1 to 2 hours per interval
|
||||
pauses.push(pause_time);
|
||||
total_time += static_cast<float>(pause_time)/60; // calculate how long churning will take in hours
|
||||
}
|
||||
|
||||
// Calculate fee
|
||||
float churn_fee = m_wallet->use_fork_rules(HF_VERSION_PER_BYTE_FEE) ? static_cast<float>(churn_number * 0.015) : static_cast<float>(churn_number * 0.032654); // usual 2/2 tx fee
|
||||
|
||||
// Prompt confirmation
|
||||
printf ("----------------\nNumber of churns: %d\nTotal duration: %.2f hours\nEstimated cost: %.2f WOW\n----------------\n", churn_number, total_time, churn_fee);
|
||||
std::string confirm_churn = input_line(tr("Continue?"));
|
||||
if (std::cin.eof() || !command_line::is_yes(confirm_churn))
|
||||
{
|
||||
message_writer() << tr("Operation cancelled.");
|
||||
return true;
|
||||
}
|
||||
|
||||
// Get main address
|
||||
std::vector<std::string> local_args = args_;
|
||||
std::string address_str;
|
||||
address_str = m_wallet->get_account().get_public_address_str(m_wallet->nettype());
|
||||
local_args.push_back(address_str);
|
||||
message_writer() << tr("Sweeping entire wallet balance to your main address:");
|
||||
message_writer(console_color_white, true) << address_str;
|
||||
|
||||
// Disable wallet confirmations to allow for automation
|
||||
m_wallet->auto_confirm_churn(1);
|
||||
m_wallet->ask_password(tools::wallet2::AskPasswordNever);
|
||||
m_wallet->always_confirm_transfers(0);
|
||||
m_wallet->auto_refresh(0);
|
||||
|
||||
// Loop sweep_all to main address for churn_number times with pause_time each interval
|
||||
for (i = 1; i <= churn_number; ++i) {
|
||||
refresh(local_args);
|
||||
sweep_all(local_args);
|
||||
message_writer(console_color_magenta, true) << tr("\n---------------- ") << i << tr(" out of ") << churn_number << tr(" churns ----------------");
|
||||
|
||||
if (i == churn_number)
|
||||
{
|
||||
success_msg_writer() << tr("\nChurning compete.");
|
||||
|
||||
// Re-enable confirmations
|
||||
m_wallet->auto_confirm_churn(0);
|
||||
m_wallet->ask_password(tools::wallet2::AskPasswordOnAction);
|
||||
m_wallet->always_confirm_transfers(1);
|
||||
m_wallet->auto_refresh(1);
|
||||
}
|
||||
else
|
||||
{
|
||||
message_writer() << tr("\nInterval pause, please wait...\n");
|
||||
sleep(pauses.top()*60);
|
||||
pauses.pop();
|
||||
}
|
||||
}
|
||||
|
||||
return true;
|
||||
}
|
||||
//----------------------------------------------------------------------------------------------------
|
||||
void simple_wallet::interrupt()
|
||||
{
|
||||
if (m_in_manual_refresh.load(std::memory_order_relaxed))
|
||||
@@ -9320,7 +9482,7 @@ void simple_wallet::commit_or_save(std::vector<tools::wallet2::pending_tx>& ptx_
|
||||
cryptonote::blobdata blob;
|
||||
tx_to_blob(ptx.tx, blob);
|
||||
const std::string blob_hex = epee::string_tools::buff_to_hex_nodelimer(blob);
|
||||
const std::string filename = "raw_monero_tx" + (ptx_vector.size() == 1 ? "" : ("_" + std::to_string(i++)));
|
||||
const std::string filename = "raw_wownero_tx" + (ptx_vector.size() == 1 ? "" : ("_" + std::to_string(i++)));
|
||||
if (epee::file_io_utils::save_string_to_file(filename, blob_hex))
|
||||
success_msg_writer(true) << tr("Transaction successfully saved to ") << filename << tr(", txid ") << txid;
|
||||
else
|
||||
@@ -9328,9 +9490,14 @@ void simple_wallet::commit_or_save(std::vector<tools::wallet2::pending_tx>& ptx_
|
||||
}
|
||||
else
|
||||
{
|
||||
if (m_wallet->auto_confirm_churn() == 0) {
|
||||
m_wallet->commit_tx(ptx);
|
||||
success_msg_writer(true) << tr("Transaction successfully submitted, transaction ") << txid << ENDL
|
||||
<< tr("You can check its status by using the `show_transfers` command.");
|
||||
} else {
|
||||
m_wallet->commit_tx(ptx);
|
||||
success_msg_writer(true) << tr("Churn successfully executed, transaction ") << txid;
|
||||
}
|
||||
}
|
||||
// if no exception, remove element from vector
|
||||
ptx_vector.pop_back();
|
||||
@@ -9380,12 +9547,12 @@ int main(int argc, char* argv[])
|
||||
bool should_terminate = false;
|
||||
std::tie(vm, should_terminate) = wallet_args::main(
|
||||
argc, argv,
|
||||
"monero-wallet-cli [--wallet-file=<filename>|--generate-new-wallet=<filename>] [<COMMAND>]",
|
||||
sw::tr("This is the command line monero wallet. It needs to connect to a monero\ndaemon to work correctly.\nWARNING: Do not reuse your Monero keys on another fork, UNLESS this fork has key reuse mitigations built in. Doing so will harm your privacy."),
|
||||
"wownero-wallet-cli [--wallet-file=<filename>|--generate-new-wallet=<filename>] [<COMMAND>]",
|
||||
sw::tr("This is the command line wownero wallet. It needs to connect to a wownero\ndaemon to work correctly."),
|
||||
desc_params,
|
||||
positional_options,
|
||||
[](const std::string &s, bool emphasis){ tools::scoped_message_writer(emphasis ? epee::console_color_white : epee::console_color_default, true) << s; },
|
||||
"monero-wallet-cli.log"
|
||||
"wownero-wallet-cli.log"
|
||||
);
|
||||
|
||||
if (!vm)
|
||||
@@ -9564,7 +9731,7 @@ void simple_wallet::list_mms_messages(const std::vector<mms::message> &messages)
|
||||
void simple_wallet::list_signers(const std::vector<mms::authorized_signer> &signers)
|
||||
{
|
||||
message_writer() << boost::format("%2s %-20s %-s") % tr("#") % tr("Label") % tr("Transport Address");
|
||||
message_writer() << boost::format("%2s %-20s %-s") % "" % tr("Auto-Config Token") % tr("Monero Address");
|
||||
message_writer() << boost::format("%2s %-20s %-s") % "" % tr("Auto-Config Token") % tr("Wownero Address");
|
||||
for (size_t i = 0; i < signers.size(); ++i)
|
||||
{
|
||||
const mms::authorized_signer &signer = signers[i];
|
||||
@@ -9770,7 +9937,7 @@ void simple_wallet::mms_signer(const std::vector<std::string> &args)
|
||||
}
|
||||
if ((args.size() < 2) || (args.size() > 4))
|
||||
{
|
||||
fail_msg_writer() << tr("mms signer [<number> <label> [<transport_address> [<monero_address>]]]");
|
||||
fail_msg_writer() << tr("mms signer [<number> <label> [<transport_address> [<wownero_address>]]]");
|
||||
return;
|
||||
}
|
||||
|
||||
@@ -9789,14 +9956,14 @@ void simple_wallet::mms_signer(const std::vector<std::string> &args)
|
||||
bool ok = cryptonote::get_account_address_from_str_or_url(info, m_wallet->nettype(), args[3], oa_prompter);
|
||||
if (!ok)
|
||||
{
|
||||
fail_msg_writer() << tr("Invalid Monero address");
|
||||
fail_msg_writer() << tr("Invalid Wownero address");
|
||||
return;
|
||||
}
|
||||
monero_address = info.address;
|
||||
const std::vector<mms::message> &messages = ms.get_all_messages();
|
||||
if ((messages.size() > 0) || state.multisig)
|
||||
{
|
||||
fail_msg_writer() << tr("Wallet state does not allow changing Monero addresses anymore");
|
||||
fail_msg_writer() << tr("Wallet state does not allow changing Wownero addresses anymore");
|
||||
return;
|
||||
}
|
||||
}
|
||||
|
||||
@@ -146,6 +146,8 @@ namespace cryptonote
|
||||
bool set_setup_background_mining(const std::vector<std::string> &args = std::vector<std::string>());
|
||||
bool set_device_name(const std::vector<std::string> &args = std::vector<std::string>());
|
||||
bool help(const std::vector<std::string> &args = std::vector<std::string>());
|
||||
bool help_advanced(const std::vector<std::string> &args = std::vector<std::string>());
|
||||
bool churn(const std::vector<std::string> &args);
|
||||
bool start_mining(const std::vector<std::string> &args);
|
||||
bool stop_mining(const std::vector<std::string> &args);
|
||||
bool set_daemon(const std::vector<std::string> &args);
|
||||
@@ -310,7 +312,7 @@ namespace cryptonote
|
||||
|
||||
//----------------- i_wallet2_callback ---------------------
|
||||
virtual void on_new_block(uint64_t height, const cryptonote::block& block);
|
||||
virtual void on_money_received(uint64_t height, const crypto::hash &txid, const cryptonote::transaction& tx, uint64_t amount, const cryptonote::subaddress_index& subaddr_index);
|
||||
virtual void on_money_received(uint64_t height, const crypto::hash &txid, const cryptonote::transaction& tx, uint64_t amount, const cryptonote::subaddress_index& subaddr_index, uint64_t unlock_time);
|
||||
virtual void on_unconfirmed_money_received(uint64_t height, const crypto::hash &txid, const cryptonote::transaction& tx, uint64_t amount, const cryptonote::subaddress_index& subaddr_index);
|
||||
virtual void on_money_spent(uint64_t height, const crypto::hash &txid, const cryptonote::transaction& in_tx, uint64_t amount, const cryptonote::transaction& spend_tx, const cryptonote::subaddress_index& subaddr_index);
|
||||
virtual void on_skip_transaction(uint64_t height, const crypto::hash &txid, const cryptonote::transaction& tx);
|
||||
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user